摘要:长安“战疫”网络安全卫士守护赛部分wp
然后就是朴实无华的取证那个题 不知道是大小写的原因还是啥交不上,无字天书卡到最后那个长得好像摩斯密码的地方,收获满满,继续努力。
misc:
八卦迷宫
走迷宫,路线即是答案,但是要把中文转化成拼音才能交上flag,哈哈哈,当时还在那疑惑了:

cazy{zhanchangyangchangzhanyanghechangshanshananzhanyiyizhanyianyichanganyang}
西安加油
打开流量包,然后导出http到文件夹:

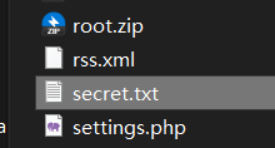
然后里面有一个secret.txt:
打开:

很明显base64
解密:

是一个压缩包,导出:


都是照片,一张一张看发现每一张都有涂鸦,拼一块就行:

cazy{make_XiAN_great_Again}
binary
给了个234的未知文件,看题目是说是二进制,用ida打开看看:

Javavm,Java逆向,用jadx-gui打开:

只有一个主函数,里面是一个数组
思来想去的说是二进制,那么把这一些数都转换成二进制数据流得到
"0000000101110000000011111101110000000011111010110101011111000111011011111001000101000011110001110101101101000100100010110000011000111000001010100010010001011101101100110110101111010001001111101011101000000010010000101111100000000101010101010101010101010000000111111110010000000010011001111111111111000101010100001011111101000000110000101101000110010010000100110101011101101100000100111100110001101000001001011101111111100101011010001101010111001010110001110000000110100000000000010011010100100010001101110101110111110100101001001111111011100001100101000100010001101110110110011001100110011101111010011000111111101101001100000001000001110101000111000001011011111101111101100110101101001100010100110000100010100100111100100000100111001001011101010100110001110001100100000101010001001101111101110110010011111101011101110110001011100000010111011000101101000110010001111011000111101001001111010101000001110101110110101111110100010010101101100100100000011010001001111101101000100011100101100110111110011000111001111100000010110110111001111100010011001011001010001011101100000000011111111010110011100111001010111010110000000111000111011010110001010100100011111011100110101011010110001110111101000101001100001100110100000000000100100010101111101100011111111110100111010001010110111111110000001010101011001111101111110001011010011110001101100000000111111011110110000000100011000"然后试了好多种方法最后在网上找资料的时候找到大佬的二进制数据流转化成二维码的脚本:
还得是大佬哈哈哈
mport PIL
from PIL import Image
MAX = 37
img = Image.new("RGB",(MAX,MAX))
i = 0
str = "0000000101110000000011111101110000000011111010110101011111000111011011111001000101000011110001110101101101000100100010110000011000111000001010100010010001011101101100110110101111010001001111101011101000000010010000101111100000000101010101010101010101010000000111111110010000000010011001111111111111000101010100001011111101000000110000101101000110010010000100110101011101101100000100111100110001101000001001011101111111100101011010001101010111001010110001110000000110100000000000010011010100100010001101110101110111110100101001001111111011100001100101000100010001101110110110011001100110011101111010011000111111101101001100000001000001110101000111000001011011111101111101100110101101001100010100110000100010100100111100100000100111001001011101010100110001110001100100000101010001001101111101110110010011111101011101110110001011100000010111011000101101000110010001111011000111101001001111010101000001110101110110101111110100010010101101100100100000011010001001111101101000100011100101100110111110011000111001111100000010110110111001111100010011001011001010001011101100000000011111111010110011100111001010111010110000000111000111011010110001010100100011111011100110101011010110001110111101000101001100001100110100000000000100100010101111101100011111111110100111010001010110111111110000001010101011001111101111110001011010011110001101100000000111111011110110000000100011000"
for x in range(MAX):
for y in range(MAX):
if(str[i] == '1'):
img.putpixel([x,y],(0,0,0))
else:
img.putpixel([x,y],(255,255,255))
i = i+1
img.show()
img.save("3.png")得到图片:

然后扫码得到:

cazy{932b2c0070e4897ea7df0190dbf36ece}
密码 :
no_cry_no_can
下载下来打开是一个python脚本:

分析一下 就是key有五位 然后这个加密函数的功能就是 将flag里面的每一位与key按位进行异或5个一循环,那么要先求出来key,因为给出来flag的前五位cazy{ 和加密后的c
很容易求出来key,求出来key之后就可以写脚本了:
s='cazy{'
a='<pH\x86\x1a&"m\xce\x12\x00pm\x97U1uA\xcf\x0c:NP\xcf\x18~l'
print(len(a))
key=[]
for i in range(len(s)):
key.append(ord(s[i])^ord(a[i]))
print(key)
m=''
for i in range(len(a)):
m+=chr(ord(a[i])^key[i%5])
print(m)cazy{y3_1s_a_h4nds0me_b0y!}
no_can_no_bb
下载下来打开依旧是一个python脚本,很明显的AES加密

这个是多次(2**20)加密直接写脚本爆破:
前面不变后面把加密函数换成自己写的解密函数,结果如下:
mport random
from Crypto.Util.number import long_to_bytes
from Crypto.Cipher import AES
def pad(m):
tmp = 16-(len(m)%16)
return m + bytes([tmp for _ in range(tmp)])
c = b'\x9d\x18K\x84n\xb8b|\x18\xad4\xc6\xfc\xec\xfe\x14\x0b_T\xe3\x1b\x03Q\x96e\x9e\xb8MQ\xd5\xc3\x1c'
for i in range(1,2**20):
key = pad(long_to_bytes(i))
aes = AES.new(key,AES.MODE_ECB)
m = aes.decrypt(c)
if m[:5] ==b'cazy{':
print(m)cazy{n0_c4n,bb?n0p3!}
RE
hello_py
下载下来是一个.pyc的程序,在线反汇编一下
得到:

#!/usr/bin/env python
# visit https://tool.lu/pyc/ for more information
import threading
import time
def encode_1(n):
global num
if num >= 0:
flag[num] = flag[num] ^ num
num -= 1
time.sleep(1)
if num <= 0:
pass
def encode_2(n):
global num
if num >= 0:
flag[num] = flag[num] ^ flag[num + 1]
num -= 1
time.sleep(1)
if num < 0:
pass
Happy = [
44,
100,
3,
50,
106,
90,
5,
102,
10,
112]
num = 9
f = input('Please input your flag:')
if len(f) != 10:
print('Your input is illegal')
continue
flag = list(f)
j = 0
print("flag to 'ord':", flag)
t1 = threading.Thread(encode_1, (1,), **('target', 'args'))
t2 = threading.Thread(encode_2, (2,), **('target', 'args'))
t1.start()
time.sleep(0.5)
t2.start()
t1.join()
t2.join()
if flag == Happy:
print('Good job!')
continue
print('No no no!')
Continue然后分析一下这个python脚本的功能
就是对输入的flag进行异或 下标为奇数用自己异或下标,下标为偶数则用自己异或下一个,然后和Happy比较
逻辑很简单
逆向过来就行,脚本如下:
Happy = [
44, 100, 3, 50, 106, 90, 5, 102, 10, 112]
flag=''
for i in range(len(Happy)):
if i%2!=0:
flag+=chr(Happy[i]^i)
else:
flag+=chr(Happy[i+1]^Happy[i])
print(flag)flag{He110_cazy}
cute_dog
经典第一步查壳:

无壳64位,扔ida64:

主函数没啥东西,shitf f12看看:

可疑字符串,去它函数里面看看:

也没啥特殊函数,就猜测是加密之后的字符串,先试一下base64:

得到答案: flag{Ch1na_yyds_cazy}
























 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










