Generally , This target seems really easy . It is like a personal PC pentest but unfortunately I had never to think about how to attack a personal PC . And the author likes set rabbit hole very much .
Scan
It opened three ports 22,80,111
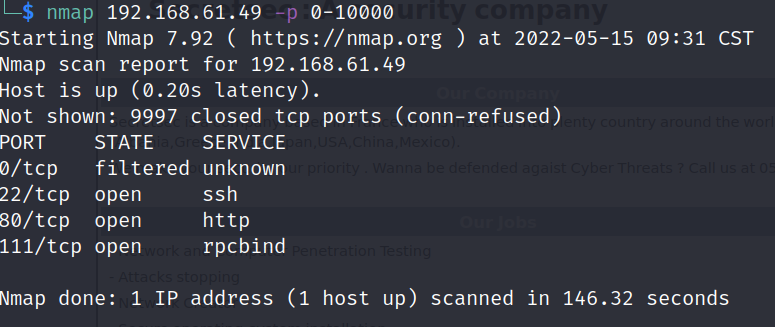
Without 111 , it might be finding secret in web and logged in from ssh .
80 port

The web index showed me three names . They were probably the users of the machine .
Dirsearch gave me some file directory . The robots was rabbit hole
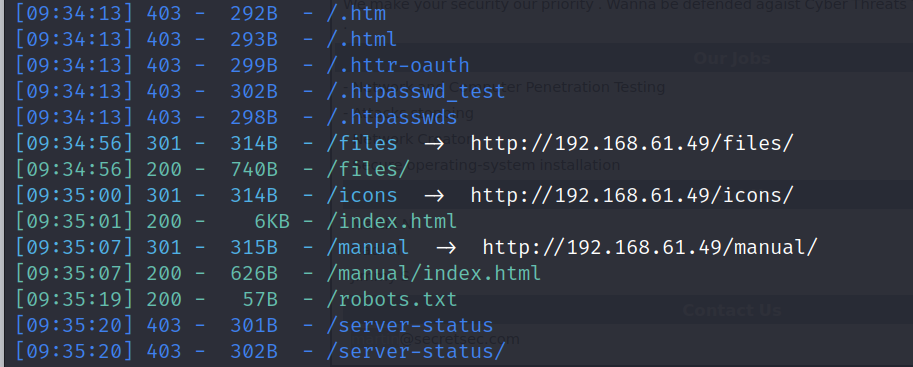
Open the icon dir . You will saw a suspicious file between many of icons named VDSoyouAXio.t








 本文详细记录了一次针对个人PC的渗透测试过程,从扫描开放端口开始,发现80端口的Web线索,通过SSH私钥获取Martin的shell,然后利用jimmy的定时任务反弹shell,再破解hadi的密码,最终以hadi的权限尝试提权到root。整个过程中揭示了个人PC安全的脆弱性和渗透测试的技巧。
本文详细记录了一次针对个人PC的渗透测试过程,从扫描开放端口开始,发现80端口的Web线索,通过SSH私钥获取Martin的shell,然后利用jimmy的定时任务反弹shell,再破解hadi的密码,最终以hadi的权限尝试提权到root。整个过程中揭示了个人PC安全的脆弱性和渗透测试的技巧。
 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 217
217











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








