4.在FW_C上配置IPSec策略。 a.定义被保护的数据流。
[FW_C] acl 3000
[FW_C-acl-adv-3000] rule 5 permit ip source 10.1.2.0 0.0.0.255 destination 10.1.1.0 0.0.0.255
b.配置IPSec安全提议tran1。采用默认参数。
[FW_C] ipsec proposal tran1
[FW_C-ipsec-proposal-tran1] esp authentication-algorithm sha2-256 //默认就有
[FW_C-ipsec-proposal-tran1] esp encryption-algorithm aes-256 //默认就有
[FW_C-ipsec-proposal-tran1] quit
c.配置IKE安全提议。采用默认参数。
[FW_C] ike proposal 10
[FW_C-ike-proposal-10] authentication-method pre-share //默认就有
[FW_C-ike-proposal-10] prf hmac-sha2-256 //默认就有
[FW_C-ike-proposal-10] encryption-algorithm aes-256 //默认就有
[FW_C-ike-proposal-10] dh group14 //默认就有
[FW_C-ike-proposal-10] integrity-algorithm hmac-sha2-256 //默认就有
[FW_C-ike-proposal-10] quit
d.配置IKE Peer。
[FW_C] ike peer a
[FW_C-ike-peer-a] ike-proposal 10
[FW_C-ike-peer-a] remote-address 1.1.2.1
[FW_C-ike-peer-a] pre-shared-key admin123
[FW_C-ike-peer-a] quit
e.配置IPSec策略map1。
[FW_C] ipsec policy map1 10 isakmp
[FW_C-ipsec-policy-isakmp-map1-10] security acl 3000
[FW_C-ipsec-policy-isakmp-map1-10] proposal tran1
[FW_C-ipsec-policy-isakmp-map1-10] ike-peer a
[FW_C-ipsec-policy-isakmp-map1-10] quit
f.在接口GigabitEthernet 1/0/2上应用IPSec策略组map1。
[FW_C] interface GigabitEthernet 1/0/2
[FW_C-GigabitEthernet1/0/2] ipsec policy map1
[FW_C-GigabitEthernet1/0/2] quit
c.出路路由器配置。
acl number 2000
rule 5 permit source 10.1.2.0 0.0.0.255
interface GigabitEthernet0/0/0
ip address 10.1.5.1 255.255.255.0
interface GigabitEthernet0/0/1
ip address 1.1.5.1 255.255.255.0
nat outbound 2000
ip route-static 0.0.0.0 0.0.0.0 1.1.5.2
ip route-static 10.1.2.0 255.255.255.0 10.1.5.2
结果验证
1.配置完成后,PC2发起访问,之后PC1与PC2之间可以相互访问。PC2同时可以访问到公网。
2.PC2可以Ping通FW_A的1.1.2.1,同时在FW_B上可以查看NAT转换session表项。
<FW_B> display firewall session table
Current Total Sessions : 2
udp VPN:public --> public 10.1.5.2:500[1.1.5.1:2048]–>1.1.2.1:500
udp VPN:public --> public 10.1.5.2:4500[1.1.5.1:2048]–>1.1.2.1:4500
3.总部防火墙FW_A上可以查看到对应的IKE SA。 <FW_A> display ike sa IKE SA information : Conn-ID Peer VPN Flag(s) Phase RemoteType RemoteID
83887864 1.1.5.1:500 RD|A v2:2 IP 1.1.5.1
83887652 1.1.5.1:500 RD|A v2:1 IP 1.1.5.1
Number of IKE SA : 2
Flag Description:
RD–READY ST–STAYALIVE RL–REPLACED FD–FADING TO–TIMEOUT
HRT–HEARTBEAT LKG–LAST KNOWN GOOD SEQ NO. BCK–BACKED UP
M–ACTIVE S–STANDBY A–ALONE NEG–NEGOTIATING
4.分支上FW_C可以查看到对端为总部的IKE SA,FW_C是发起方,标志位为ST。 <FW_C> display ike sa IKE SA information : Conn-ID Peer VPN Flag(s) Phase RemoteType RemoteID
62887864 1.1.2.1:500 RD|ST|A v2:2 IP 1.1.2.1
62887652 1.1.2.1:500 RD|ST|A v2:1 IP 1.1.2.1
Number of IKE SA : 2
Flag Description:
RD–READY ST–STAYALIVE RL–REPLACED FD–FADING TO–TIMEOUT
HRT–HEARTBEAT LKG–LAST KNOWN GOOD SEQ NO. BCK–BACKED UP
M–ACTIVE S–STANDBY A–ALONE NEG–NEGOTIATING
5.总部防火墙FW_A上可以查看到一对双向的IPSec SA,对应分支FW_C。
<FW_A> display ipsec sa brief
Current ipsec sa num:2
Spu board slot 1, cpu 1 ipsec sa information: Number of SAs:2 Src address Dst address SPI VPN Protocol Algorithm
1.1.2.1 1.1.5.1 3923280450 ESP E:AES-256 A:SHA2_256_128
1.1.5.1 1.1.2.1 2676437093 ESP E:AES-256 A:SHA2_256_128
6.分支节点FW_C上可以查看到一对双向IPSec SA。<FW_C> display ipsec sa brief
Current ipsec sa num:2
Spu board slot 1, cpu 1 ipsec sa information: Number of SAs:4 Src address Dst address SPI VPN Protocol Algorithm
10.1.5.2 1.1.2.1 2179965693 ESP E:AES-256 A:SHA2_256_128
1.1.2.1 10.1.5.2 3813759530 ESP E:AES-256 A:SHA2_256_128
第二种方法,即做vpn又做nat,意思是电脑又和总部vpn通,又能上外网,都在一台防火墙设备上实现。
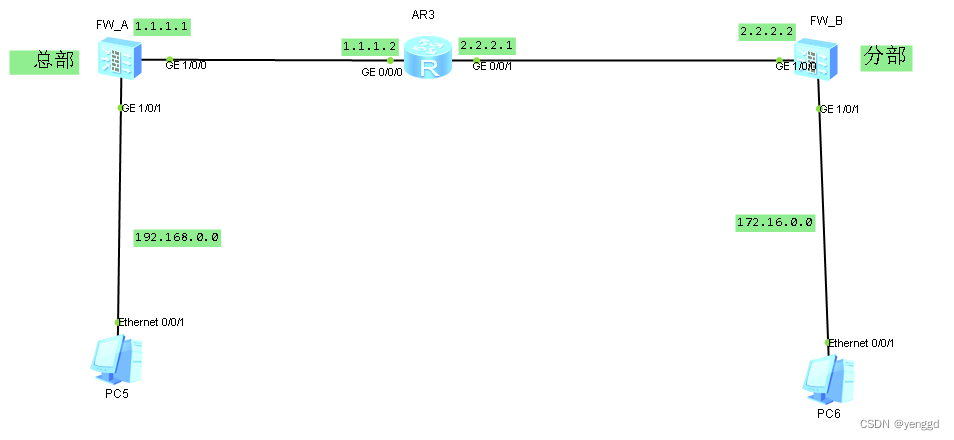
FW_A主要配置:
acl number 3000
rule 5 permit ip source 192.168.0.0 0.0.0.255 destination 172.16.0.0 0.0.0.255
ipsec proposal pro1
transfrom esp
ike proposal 10
ike peer fenbu_1
pre-shared-key admin
ike-proposal 10
nat traversal
ipsec policy-template temp1 1
security acl 3000
ike-peer fenbu_1
proposal pro1
ipsec policy policy1 1 isakmp template temp1
interface GigabitEthernet1/0/0
undo shutdown
ip address 1.1.1.1 255.255.255.0
service-manage ping permit
ipsec policy policy1
interface GigabitEthernet1/0/1
undo shutdown
ip address 192.168.0.1 255.255.255.0
service-manage ping permit
dhcp select interface
firewall zone trust
set priority 85
add interface GigabitEthernet0/0/0
add interface GigabitEthernet1/0/1
firewall zone untrust
set priority 5
add interface GigabitEthernet1/0/0
ip route-static 0.0.0.0 0.0.0.0 1.1.1.2
FW_B主要配置:
acl number 2000
rule 5 permit source 172.16.0.0 0.0.0.255
acl number 3000
rule 5 permit ip source 172.16.0.0 0.0.0.255 destination 192.168.0.0 0.0.0.255
ipsec proposal pro1
transfrom esp
ike proposal 10
ike peer zongbu
pre-shared-key admin
ike-proposal 10
remote-address 1.1.1.1
nat traversal
ipsec policy policy1 1 isakmp
security acl 3000
ike-peer zongbu
proposal pro1
interface GigabitEthernet1/0/0
undo shutdown
ip address 1.1.1.1 255.255.255.0
service-manage ping permit
ipsec policy policy1
interface GigabitEthernet1/0/1
undo shutdown
ip address 172.16.0.1 255.255.255.0
service-manage ping permit
dhcp select interface
firewall zone trust
set priority 85
add interface GigabitEthernet0/0/0
add interface GigabitEthernet1/0/1
ip route-static 0.0.0.0 0.0.0.0 2.2.2.1
自我介绍一下,小编13年上海交大毕业,曾经在小公司待过,也去过华为、OPPO等大厂,18年进入阿里一直到现在。
深知大多数网络安全工程师,想要提升技能,往往是自己摸索成长,但自己不成体系的自学效果低效又漫长,而且极易碰到天花板技术停滞不前!
因此收集整理了一份《2024年网络安全全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友。



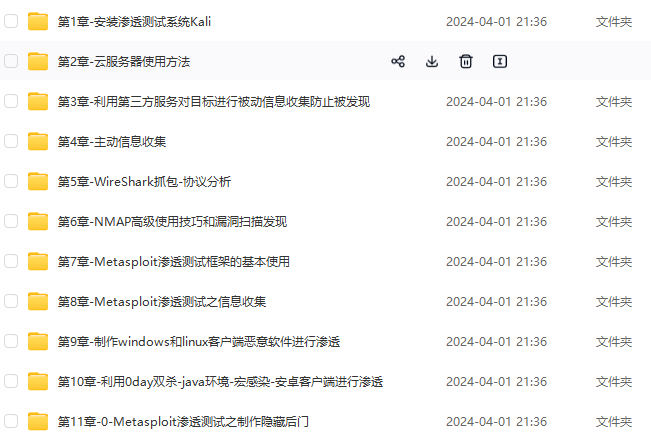
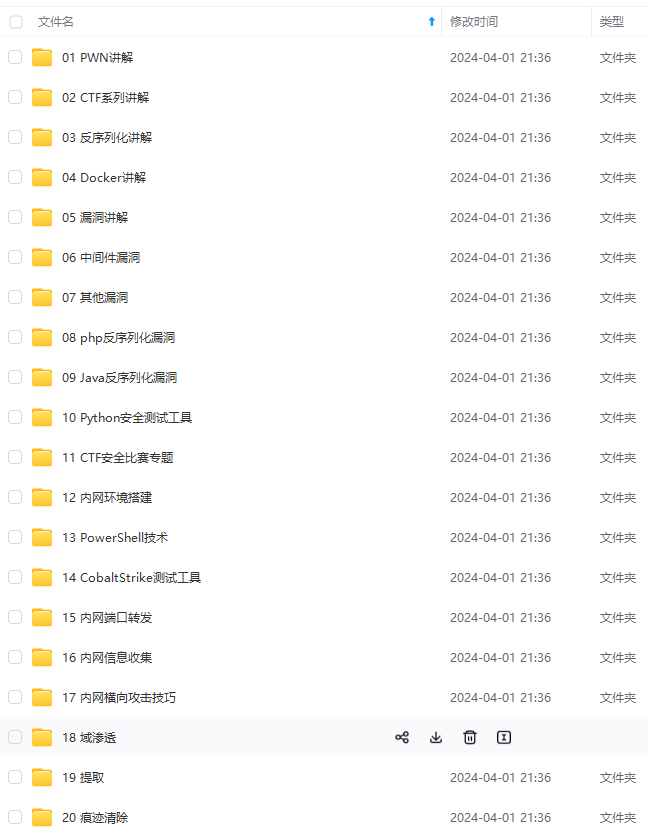
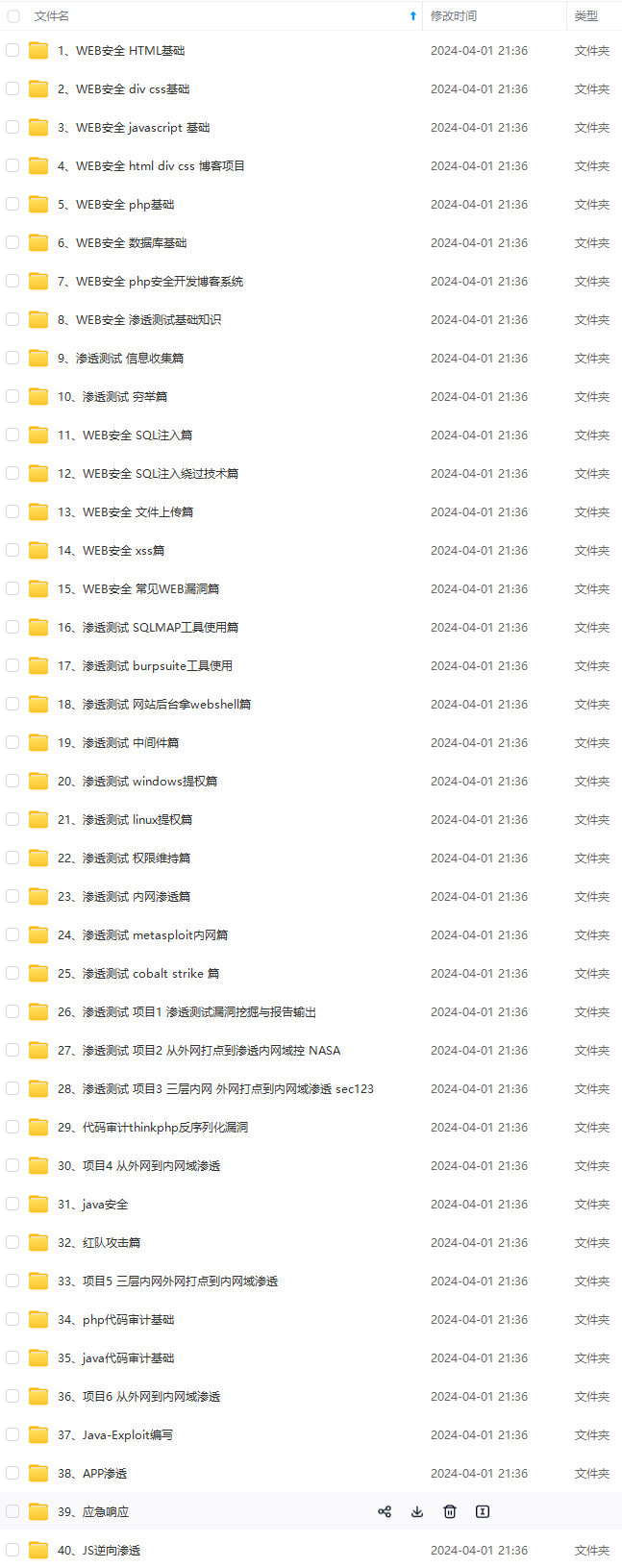
既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,基本涵盖了95%以上网络安全知识点,真正体系化!
由于文件比较大,这里只是将部分目录大纲截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且后续会持续更新
如果你觉得这些内容对你有帮助,可以添加VX:vip204888 (备注网络安全获取)

2VVN-1712893354547)]
[外链图片转存中…(img-JFxGSuq2-1712893354547)]
[外链图片转存中…(img-JwwRLDjm-1712893354547)]
既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,基本涵盖了95%以上网络安全知识点,真正体系化!
由于文件比较大,这里只是将部分目录大纲截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且后续会持续更新
如果你觉得这些内容对你有帮助,可以添加VX:vip204888 (备注网络安全获取)
[外链图片转存中…(img-3HNEvtMa-1712893354547)]






















 444
444











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








