目录
1.Apache的作用
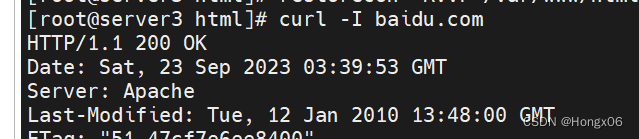
在
web
被访问时通常使用
http
://
的方式
http
://
##
超文本传输协议
http
://
超文本传输协议提供软件
:
Apache
nginx
stgw
jfe
Tengine
如:
2.Apache的安装
dnf install httpd.x86_64 - y
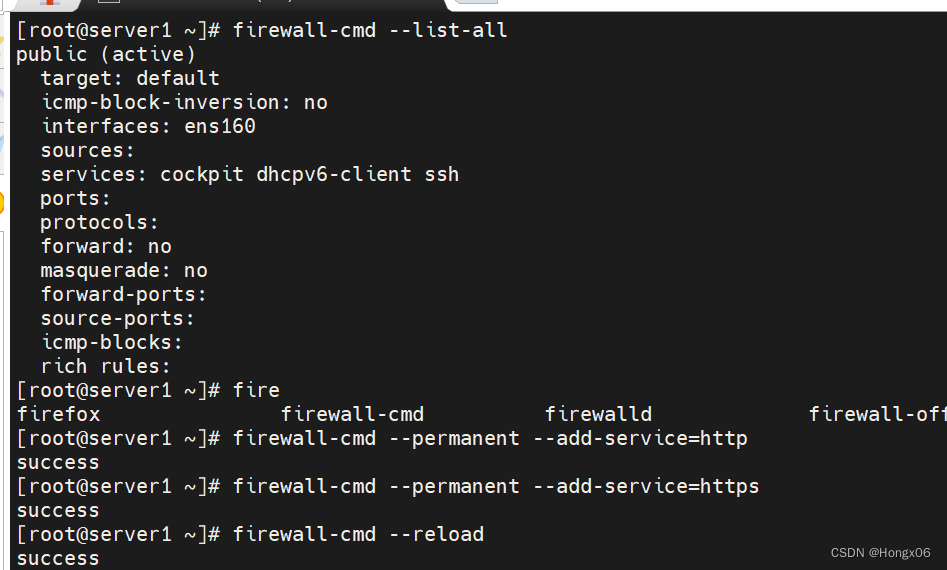
3.Apache的启用
systemctl enable -- now httpd ##开启服务并设定服务位开机启动firewall - cmd -- list - all ##查看火墙信息firewall - cmd -- permanent -- add - service = http ##在火墙中永久开启 http 访问firewall - cmd -- permanent -- add - service = https ##在火墙中永久开启 https 访问firewall - cmd -- reload ##刷新火墙使设定生效
4.Apache的基本信息
服务名称
:
httpd
配置文件
:
/ etc / httpd / conf / httpd.conf ##主配置文件/ etc / httpd / conf.d /* .conf ##子配置文件
默认发布目录
:
/ var / www / html
默认发布文件
:
index.html
默认端口
:
80 #http443 #https
用户
:
apache
日志
:
/ etc / httpd / logs
5.Apache的基本配置
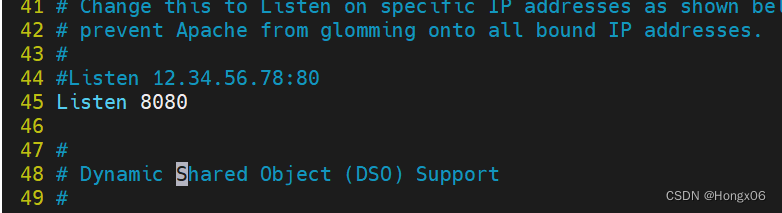
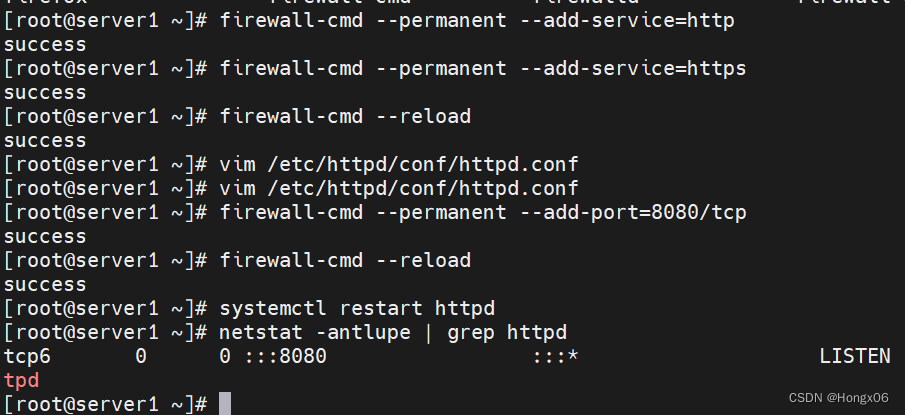
1.Apache端口修改
vim / etc / httpd / conf / httpd.conf45 Listen 8080
firewall - cmd -- permanent -- add - port = 8080 / tcpfirewall - cmd -- reloadsystemctl restart httpdhttp :// 172.25.254.100 : 8080
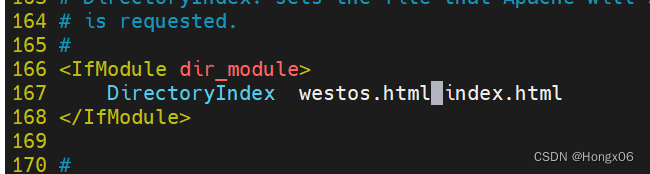
2.默认发布文件
vim / etc / httpd / conf / httpd.confDirectoryIndex westos.html index.htmlsystemctl restart httpd
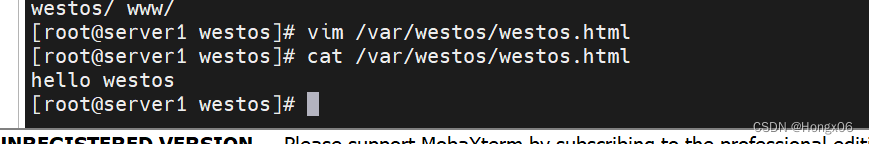
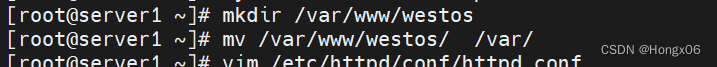
3.默认发布目录
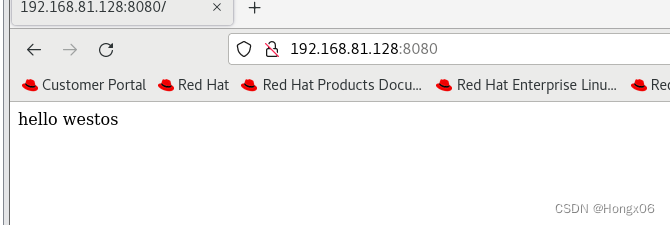
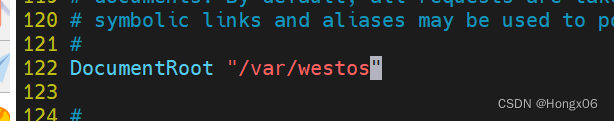
mkdir / var / www / westosmv / var / www / westos / varvim / etc / httpd / conf / httpd.conf
DocumentRoot " / var / westos"
< Directory " / var / westos" >Require all granted</ Directory >
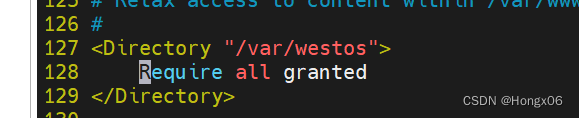
systemctl restart httpdfirefox http :// 192.168.0.11
6.Apache的访问控制
实验素材
mkdir / var / www / html / westosvim / var / www / html / westos / index.html< h1 > westosdir ' s page </ h1 >firefox http :// 192.168.0.11 / westos


1.基于客户端ip的访问控制
vim /etc/httpd/conf.d/access.conf
#ip
白名单
#
< Directory " / var / www / html / westos" >Order Deny,AllowAllow from 192.168.0.10Deny from All</ Directory >

#ip
黑名单
#
< Directory " / var / www / html / westos" >Order Allow,DenyAllow from AllDeny from 192.168.0.10</ Directory >

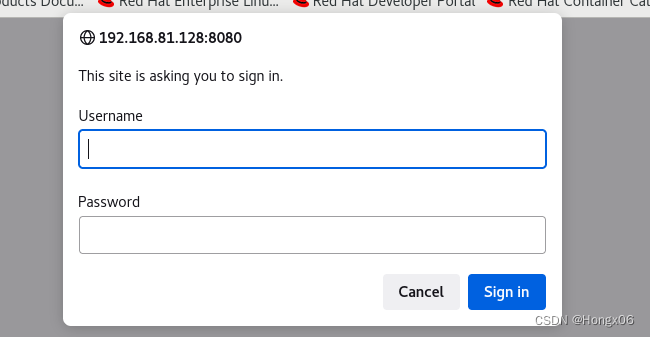
2.基于用户认证
vim / etc / httpd /conf.d/access.conf< Directory / var / www / html / westos >AuthUserfile / etc / httpd / htpasswdfile ##指定认证文件AuthName "Please input your name and password" ##认证提示语AuthType basic ##认证类型Require user admin ##允许通过的认证用户 2 选 1Require valid - user</ Directory >
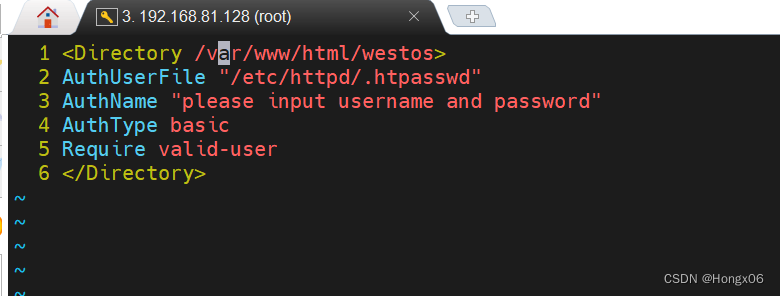
##
允许所有用户通过认证
2
选
1
htpasswd - cm / etc / httpd / htpasswdfile admin ##生成认证文件htpasswd - m / etc / httpd / htpasswdfile admin
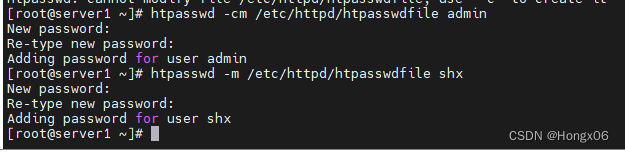
注意
:
当/etc/httpd/htpasswdfile存在那么在添加用户时不要加-c参数否则会覆盖源文件内容
7.Apache的虚拟主机
mkdir -p /var/www/virtual/shx.org/{news,bbs}/html/index.html
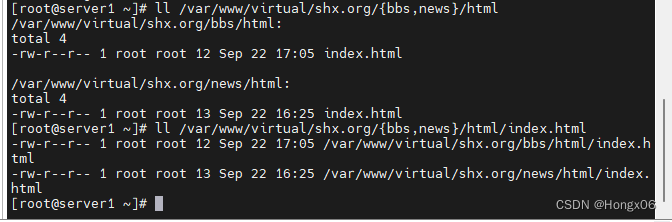
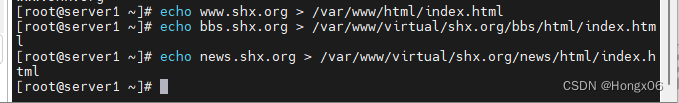
echo www.shx.org > / var / www /html/index.htmlecho bbs.shx.org > / var / www / virtual/shx.org/bbs/html/index.htmlecho news.shx.org > / var / www / virtual/shx.org/news/html/index.html
vim /etc/httpd/conf.d/Vhost.conf
1 <VirtualHost _default_:80>
2 DocumentRoot /var/www/html
3 CustomLog logs/default.log combined
4 </VirtualHost>
5
6 <VirtualHost *:80>
7 ServerName news.shx.org
8 DocumentRoot /var/www/virtual/shx.org/news/html/
9 CustomLog logs/news.log combined
10 </VirtualHost>
11
12 <VirtualHost *:80>
13 ServerName bbs.shx.org
14 DocumentRoot /var/www/virtual/shx.org/bbs/html/
15 CustomLog logs/bbs.log combined
16 </VirtualHost>

测试
:
在浏览器所在主机中
vim / etc / hosts192.168.81.128 server3 www.shx.org news.shx.org bbs.shx.org

firefox http :// www.shx.orgfirefox http :// bbs.shx.orgfirefox http :// news.shx.org



8.Apache的语言支持
#php#
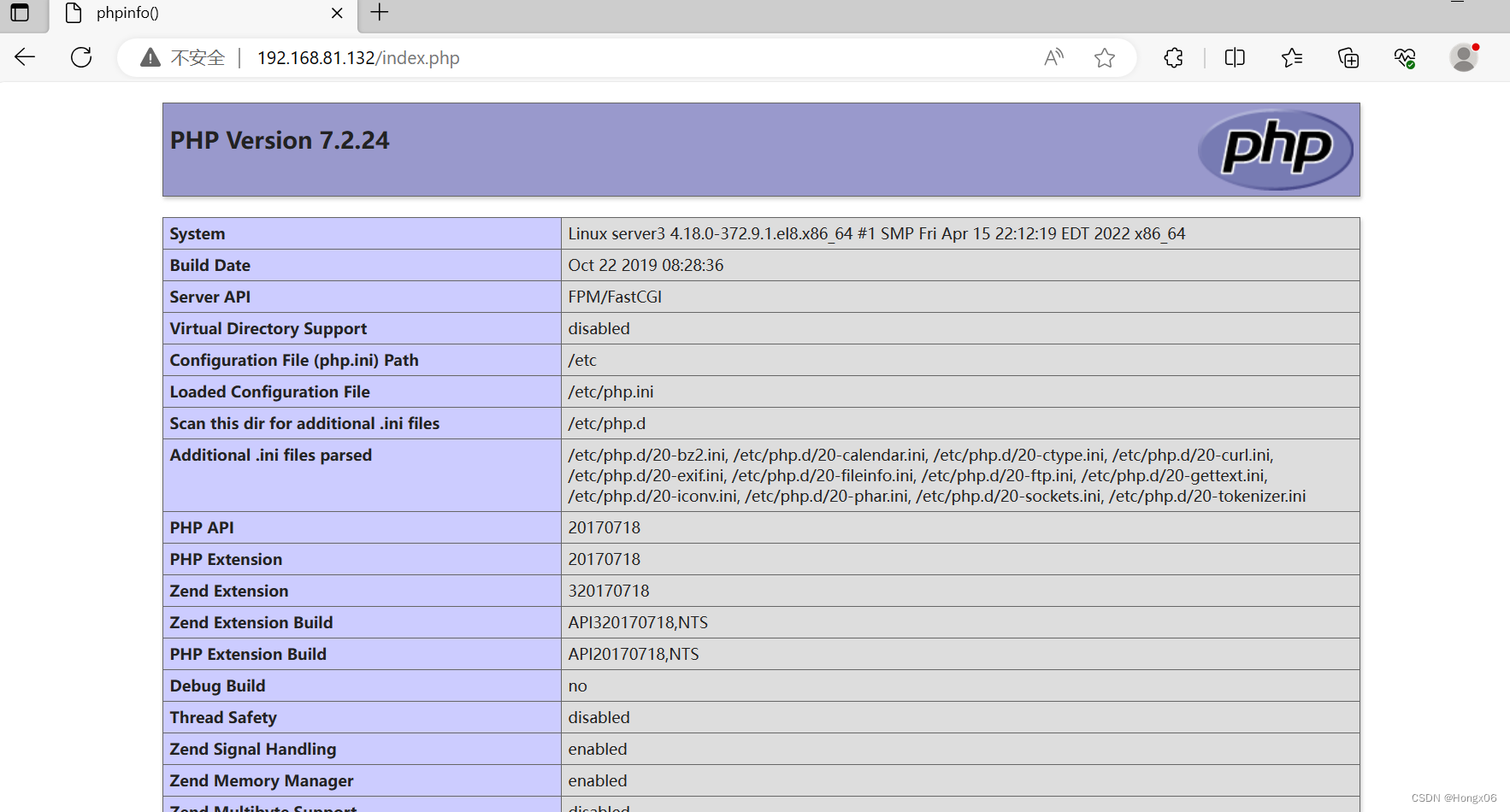
vim / var / www / html / index.php< ?phpphpinfo();? >
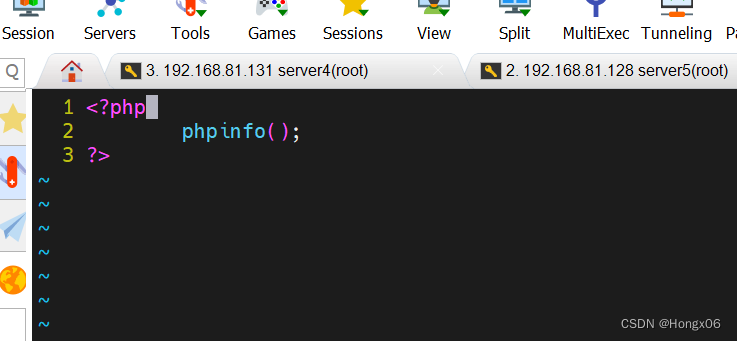
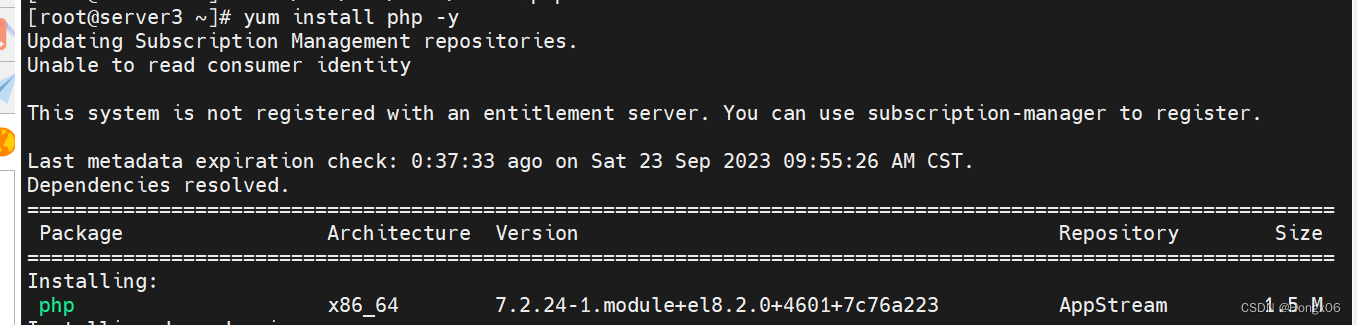
dnf install php - ysystemctl restart httpd
firefox http
://
192.168.81.132
/
index.php
#cgi#
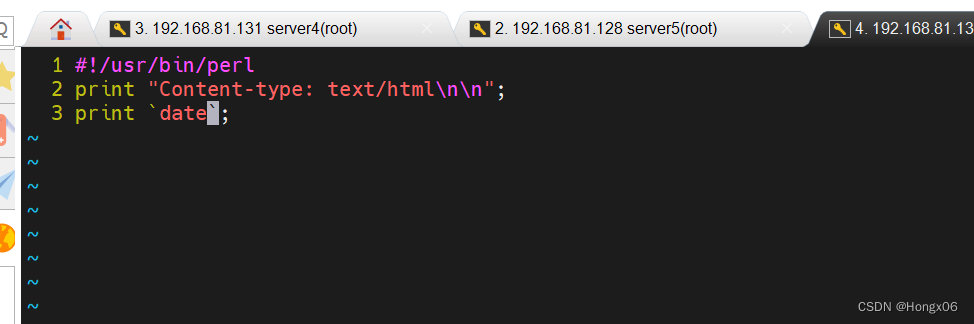
mkdir / var / www / html / cgidirvim / var / www / html / cgidir / index.cgi# !/ usr / bin / perlprint "Content - type : text / html \ n \ n";print `date`;
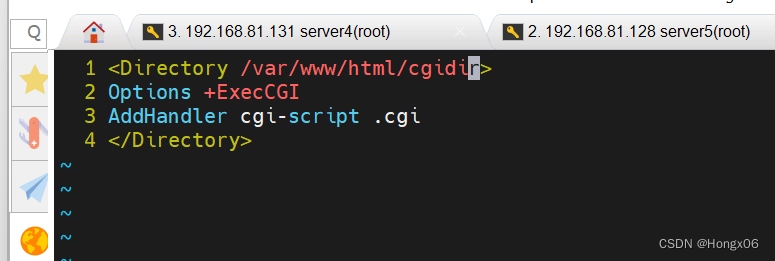
vim / etc / httpd / conf.d / cgi.conf< Directory " / var / www / html / cgidir" >Options + ExecCGIAddHandler cgi - script .cgi</ Directory >
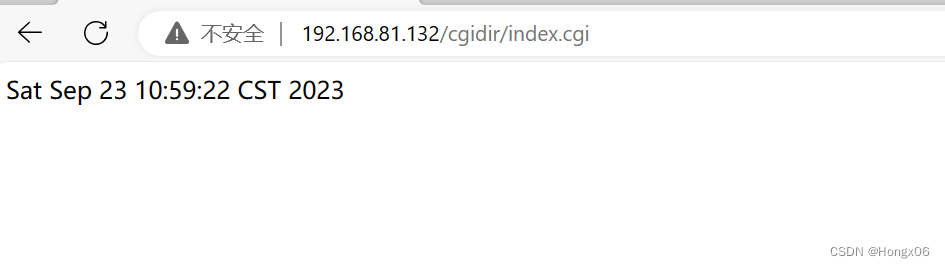
firefox http
://
192.168.0.11
/
cgidir
/
index.cgi
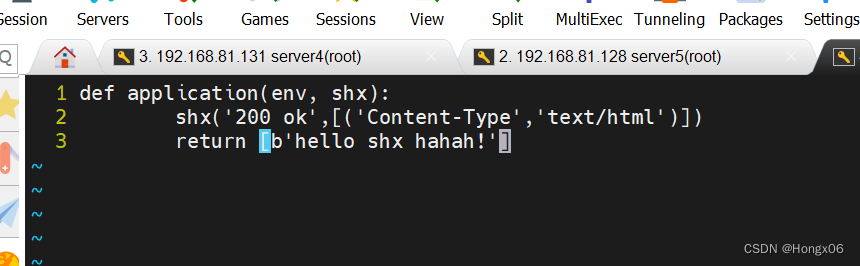
#wsgi#
书写
wsgi
的测试文件
vim / var / www / html / wsgi / index.wsgidef application(env, shx) :shx( '200 ok' ,[( 'Content-Type' , 'text/html' )])return [b ' hello shx ahhahahahah ! ']
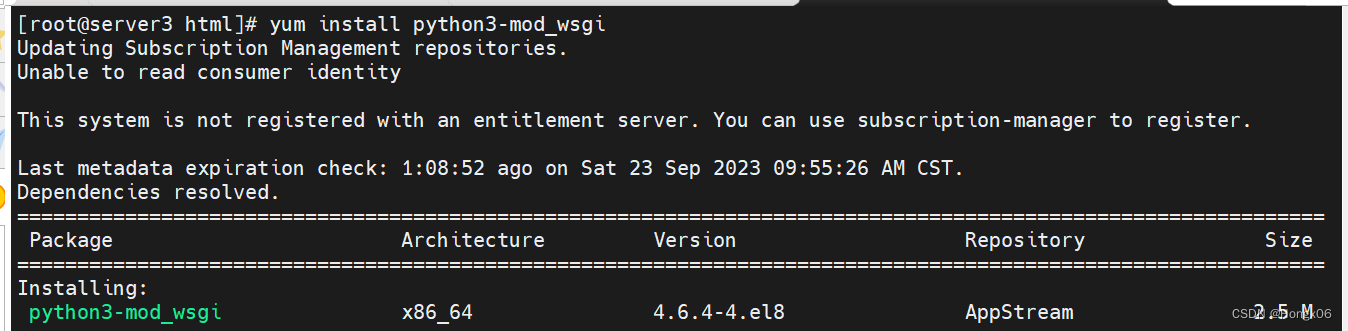
dnf install python3 - mod_wsgisystemctl restart httpd
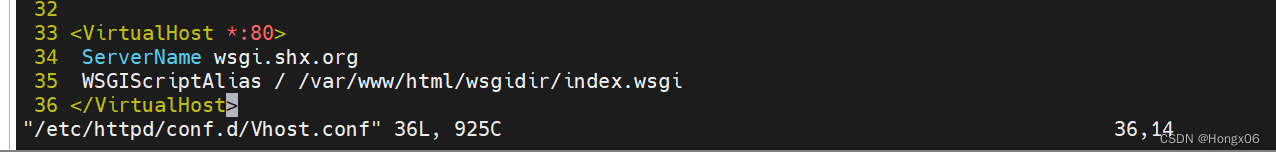
vim / etc / httpd / conf.d / vhost< VirtualHost *: 80 >ServerName wsgi.westos.orgWSGIScriptAlias / / var / www / html / wsgi / index.wsgi</ VirtualHost >



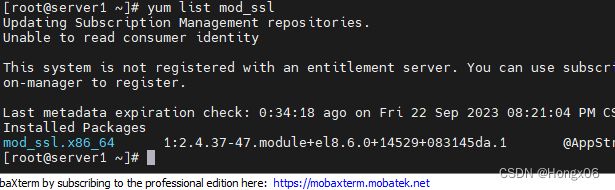
9.Apache的加密访问
安装加密插件
dnf install mod_ssl - y ## 生成证书
command
1
openssl genrsa - out / etc / pki / tls / private / www.westos.com.key 2048 生成私钥openssl req - new - key / etc / pki / tls / private / www.westos.com.key \- out / etc / pki / tls / certs / www.westos.com.csr 生成证书签名文件openssl x509 - req - days 365 - in / etc / pki / tls / certs / www.westos.com.csr signkey / etc / pki / tls / private / www.westos.com.key out / etc / pki / tls / certs / www.westos.com.crt #生成证书
x509 证书格式- req 请求- in 加载签证名称- signkey / etc / pki / tls / private / www.westos.com.key
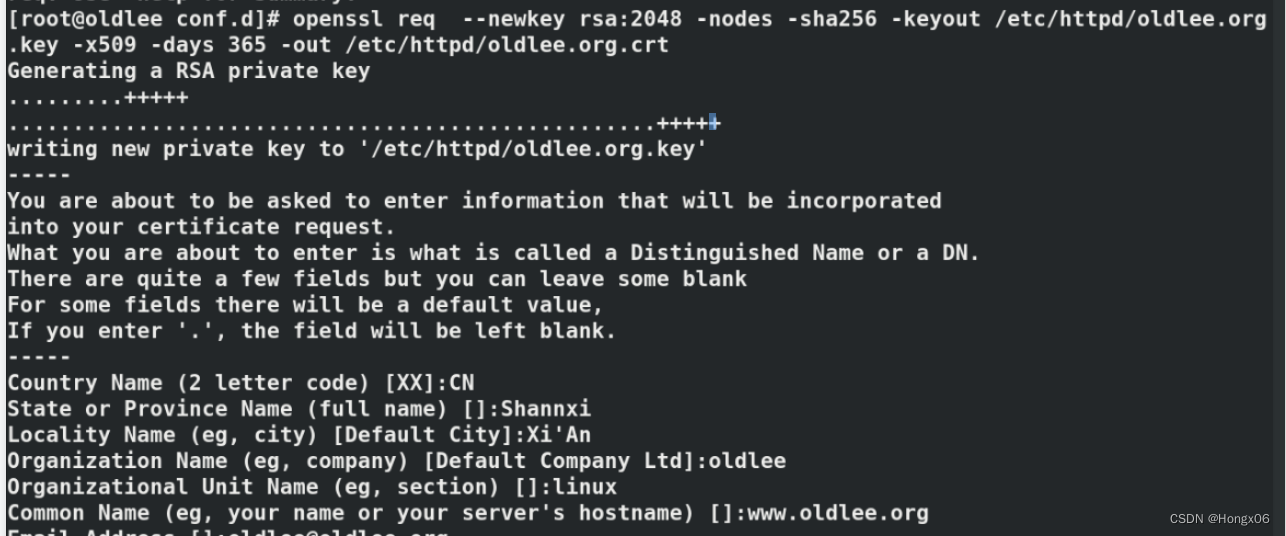
command
2
openssl req -- newkey rsa : 2048 \ - nodes - sha256 - keyout / etc / httpd / westos.org.key - x509 - days 365 - out / etc / httpd / shx.org.crt 生成密钥和证书签名文件
vim / etc / httpd / conf.d / Vh ost.conf18 <VirtualHost *:443>
19 Servername login.shx.org
20 DocumentRoot /var/www/virtual/shx.org/login/html
21 CustomLog logs/login.log combined
22 SSLEngine on
23 SSLCertificateFile /etc/httpd/shx.org.crt
24 SSLCertificateKeyFile /etc/httpd/shx.org.key
25 </VirtualHost>
26
27 <VirtualHost *:80>
28 ServerName login.shx.org
29 RewriteEngine on
30 RewriteRule ^(/.*)$ https://%{HTTP_HOST}$1
31 </VirtualHost>

systemctl restart httpd
^ ( /.* )$ ##客户地址栏中输入的地址%{HTTP_HOST} ##客户主机$ 1 ##RewriteRule后面跟的第一串字符的值


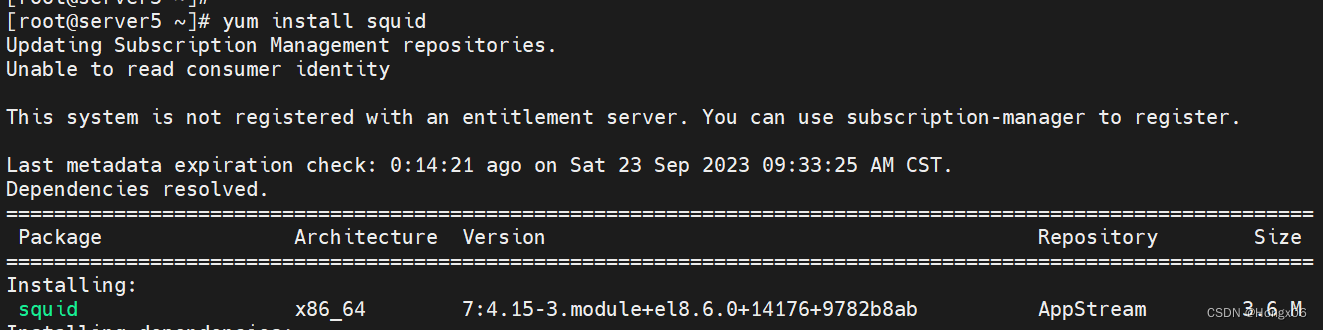
10.Squid+Apache
squid 反
向代理
实验环境
:
单网卡主机设定
ip
不能上网
双网卡主机设定
ip1
可以连接单网卡主机
,
设定
ip2
可以上网
实验效果
让单网卡主机不能上网但浏览器可以访问互联网页
操作
:
在双网卡主机中
dnf install squid - y
vim / etc / squid / squid.conf59 http_access allow all63 http_port 80 vhost vport ##vhost 支持虚拟域名 vport 支持虚拟端口64 cache_peer 172.25.254.20 parent 80 0 proxy - only65 cache_dir ufs / var / spool / squid 100 16 256systemctl restart squid

firewall - cmd -- permanent -- add - port = 3128 / tcpfirewall - cmd -- reload 在单网卡专辑中选择
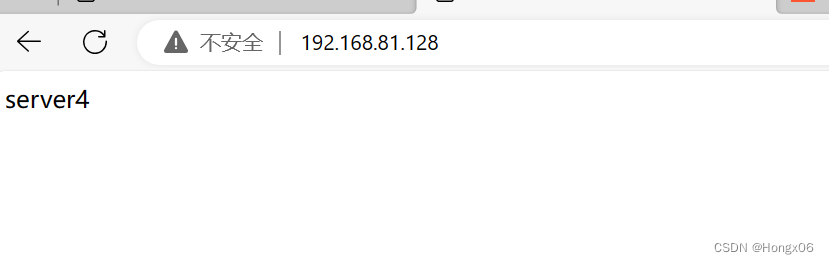
![]()
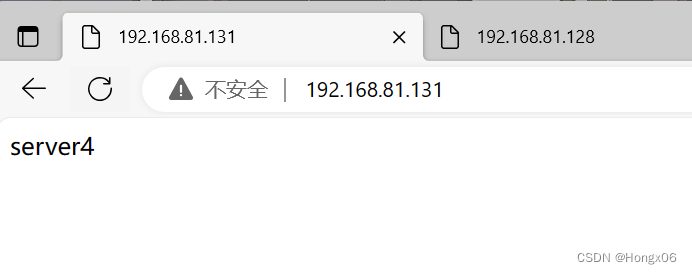
实验环境
:
192.168.81.131
##Apache服务器
192.168.81.128
##squid,没有数据负责缓存
vim / etc / squid / squid.conf
#
当
192.168.81.128
的
80
端口被访问会从
192.168.81.131
的
80
端口缓存数据
cache_peer 192.168.81.131 parent 80 0 proxy - onlysystemctl restart squid
测试
:
firefox http
:/
192.168.81.128
访问看到的是
192.168.81.131
上的数据





















 322
322

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








