目录
Task 1: Deriving the Private Key
Task 6: Manually Verifying an X.509 Certificate
Step 1: Download a certificate from a real web server.
Step 2: Extract the public key (e, n) from the issuer’s certificate.
Step 3: Extract the signature from the server’s certificate.
Step 4: Extract the body of the server’s certificate.
测试示例
gcc bn_sample.c -lcrypto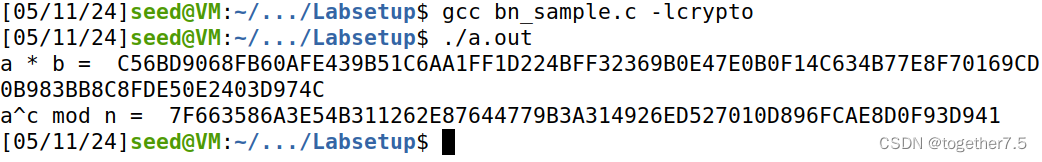
Task 1: Deriving the Private Key
代码如下
#include <stdio.h>
#include <openssl/bn.h>
#define NBITS 256
void printBN(char *msg, BIGNUM * a)
{
/* Use BN_bn2hex(a) for hex string
* Use BN_bn2dec(a) for decimal string */
char * number_str = BN_bn2hex(a);
printf("%s %s\n", msg, number_str);
OPENSSL_free(number_str);
}
int main ()
{
BN_CTX *ctx = BN_CTX_new();
BIGNUM *p = BN_new();
BIGNUM *q = BN_new();
BIGNUM *n = BN_new();
BIGNUM *p_ = BN_new();
BIGNUM 







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章


















 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








