本人实力有限只做出3题RE望各位大佬指点
REVERSE:
Prese
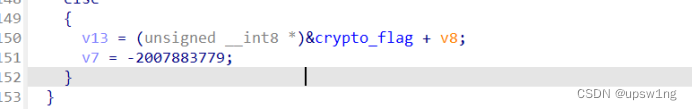
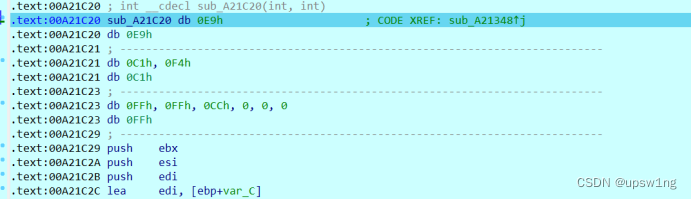
1.有一个平坦化流程控制脚本去不掉不过逻辑简单,main函数就是输入字符串进入main_crypto进行加密将如何的结果和crypto_flag比较
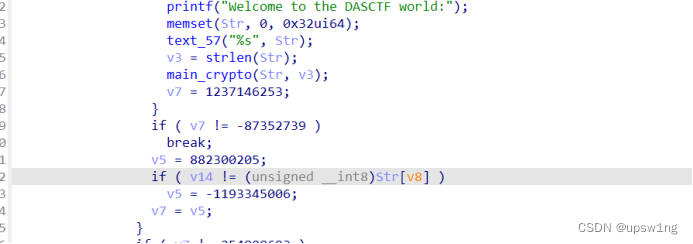
2.进入main_crypto分析一下通过调试可以分析这个函数的作用就是使用输入的字符串长度和i进行xor 取反存入到temp数组中,然后将我们的输入作为下标在temp中取值得出值和crypto_flag进行比较
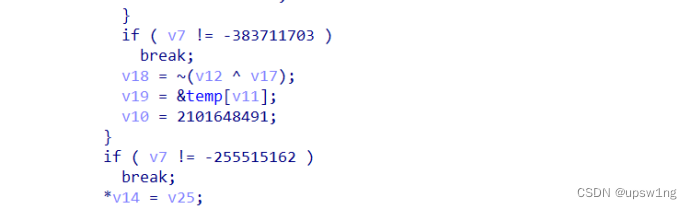
3.在对和crypto_flag交叉引用的时候发现有别的函数调用了它跟进发现在进入main函数之前会有一个函数在对crypto_flag进行修改,IAT_start跟进是一个反调试如果检测到调试就不xor否则就xor
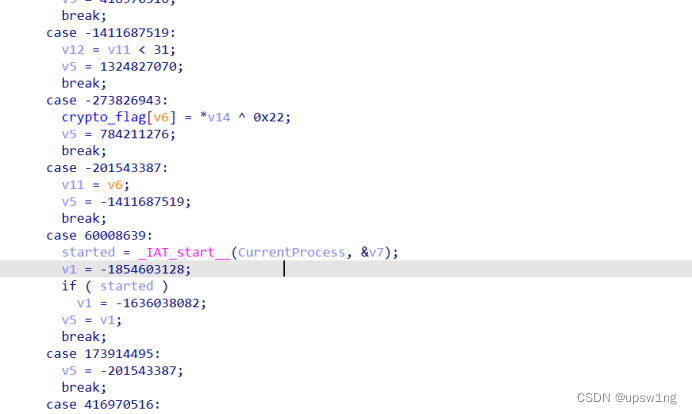
4.根据密文可以知道flag正确的长度是31,提取出temp写出exp
table = [0xE0, 0xE1, 0xE2, 0xE3, 0xE4, 0xE5, 0xE6, 0xE7, 0xE8, 0xE9,
0xEA, 0xEB, 0xEC, 0xED, 0xEE, 0xEF, 0xF0, 0xF1, 0xF2, 0xF3,
0xF4, 0xF5, 0xF6, 0xF7, 0xF8, 0xF9, 0xFA, 0xFB, 0xFC, 0xFD,
0xFE, 0xFF, 0xC0, 0xC1, 0xC2, 0xC3, 0xC4, 0xC5, 0xC6, 0xC7,
0xC8, 0xC9, 0xCA, 0xCB, 0xCC, 0xCD, 0xCE, 0xCF, 0xD0, 0xD1,
0xD2, 0xD3, 0xD4, 0xD5, 0xD6, 0xD7, 0xD8, 0xD9, 0xDA, 0xDB,
0xDC, 0xDD, 0xDE, 0xDF, 0xA0, 0xA1, 0xA2, 0xA3, 0xA4, 0xA5,
0xA6, 0xA7, 0xA8, 0xA9, 0xAA, 0xAB, 0xAC, 0xAD, 0xAE, 0xAF,
0xB0, 0xB1, 0xB2, 0xB3, 0xB4, 0xB5, 0xB6, 0xB7, 0xB8, 0xB9,
0xBA, 0xBB, 0xBC, 0xBD, 0xBE, 0xBF, 0x80, 0x81, 0x82, 0x83,
0x84, 0x85, 0x86, 0x87, 0x88, 0x89, 0x8A, 0x8B, 0x8C, 0x8D,
0x8E, 0x8F, 0x90, 0x91, 0x92, 0x93, 0x94, 0x95, 0x96, 0x97,
0x98, 0x99, 0x9A, 0x9B, 0x9C, 0x9D, 0x9E, 0x9F, 0x60, 0x61,
0x62, 0x63, 0x64, 0x65, 0x66, 0x67, 0x68, 0x69, 0x6A, 0x6B,
0x6C, 0x6D, 0x6E, 0x6F, 0x70, 0x71, 0x72, 0x73, 0x74, 0x75,
0x76, 0x77, 0x78, 0x79, 0x7A, 0x7B, 0x7C, 0x7D, 0x7E, 0x7F,
0x40, 0x41, 0x42, 0x43, 0x44, 0x45, 0x46, 0x47, 0x48, 0x49,
0x4A, 0x4B, 0x4C, 0x4D, 0x4E, 0x4F, 0x50, 0x51, 0x52, 0x53,
0x54, 0x55, 0x56, 0x57, 0x58, 0x59, 0x5A, 0x5B, 0x5C, 0x5D,
0x5E, 0x5F, 0x20, 0x21, 0x22, 0x23, 0x24, 0x25, 0x26, 0x27,
0x28, 0x29, 0x2A, 0x2B, 0x2C, 0x2D, 0x2E, 0x2F, 0x30, 0x31,
0x32, 0x33, 0x34, 0x35, 0x36, 0x37, 0x38, 0x39, 0x3A, 0x3B,
0x3C, 0x3D, 0x3E, 0x3F, 0x00, 0x01, 0x02, 0x03, 0x04, 0x05,
0x06, 0x07, 0x08, 0x09, 0x0A, 0x0B, 0x0C, 0x0D, 0x0E, 0x0F,
0x10, 0x11, 0x12, 0x13, 0x14, 0x15, 0x16, 0x17, 0x18, 0x19,
0x1A, 0x1B, 0x1C, 0x1D, 0x1E, 0x1F]
enc = [0x86, 0x83, 0x91, 0x81, 0x96, 0x84, 0xB9, 0xA5, 0xAD, 0xAD,
0xA6, 0x9D, 0xB6, 0xAA, 0xA7, 0x9D, 0xB0, 0xA7, 0x9D, 0xAB,
0xB1, 0x9D, 0xA7, 0xA3, 0xB1, 0xBB, 0xAA, 0xAA, 0xAA, 0xAA,
0xBF]
for i in range(len(enc)):
enc[i] ^= 0x22
for i in enc:
print(chr(table.index(i)),end='')EzVM
1.输入一个长度为16的字符串并且是0-9的字符串,然后将这个字符串每两位转为整数,调用sub_1400012D5函数去判断
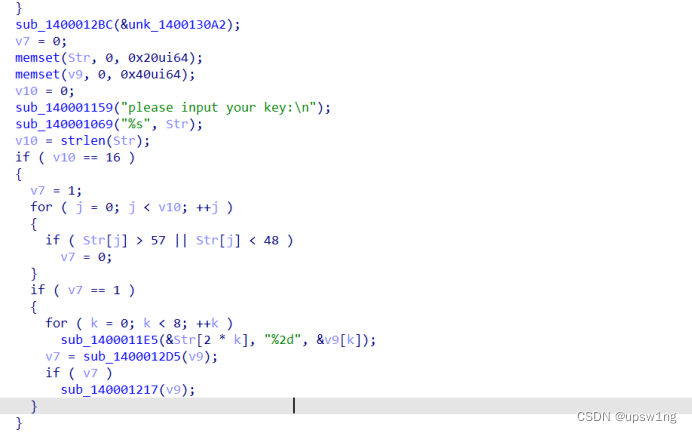
2.sub_1400012D5函数实现了一个VM对输入的加密

3.sub_140001217 函数,首先对.dll进行重命名,然后使用输入的key对data文件数据进行解密再写入到一个新的check.dll文件也就是说其实我们调用的是data文件解密后的dll文件,而不是现在给的这个
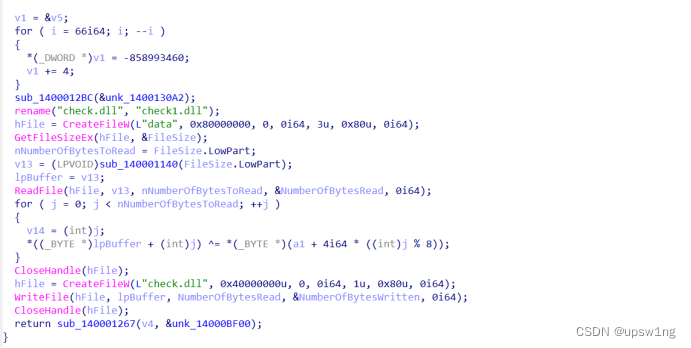
4.调用check.dll中的check加密比较我们现在要求出这个key是多少
5.可以通过对VM加密函数求解得出,不过因为xor的特性我们可以通过密文和明文得出key,因为我们知道解密出来肯定是一个dll文件,我们就可以拿dll前面几个字符和密文xor得出key,解密出真的dll后发现就是一个xor
#密文
# key1 = [0x2C,0x0D,0x89,0x2E,0x1D,0x0C,0x25,0x3B]
# #明文
# enc = [0x4D,0x5A,0x90,0x00,0x03,0x00,0x00,0x00]
# key = []
# for i in range(len(key1)):
# key.append(key1[i] ^ enc[i])
# #print(key)
# flag = []
# with open(r"C:\Users\34043\Desktop\题目\data",'rb') as f:
#
# data = f.read()
# for i in range(len(data)):
# flag.append(data[i] ^ key[i % 8])
# with open(r"C:\Users\34043\Desktop\题目\data1", 'wb') as f1:
# f1.write(bytes(flag))
enc = b"\r\b\x1A\x0A\x1D\x0F2x*{*{|}qdz,{}d(}q,dxx}zd(z}p\x7F(z+~}yy4"
for i in enc:
print(chr(i ^ 0x49),end='')Unwind
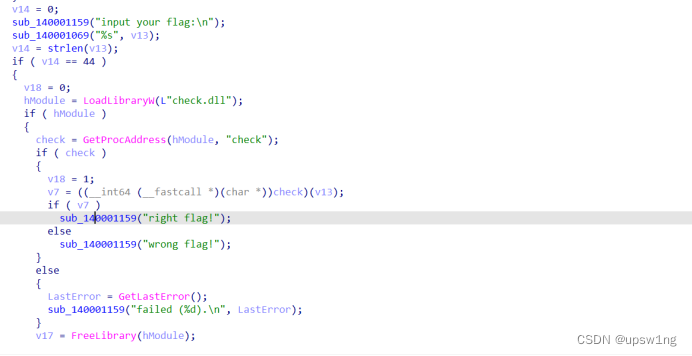
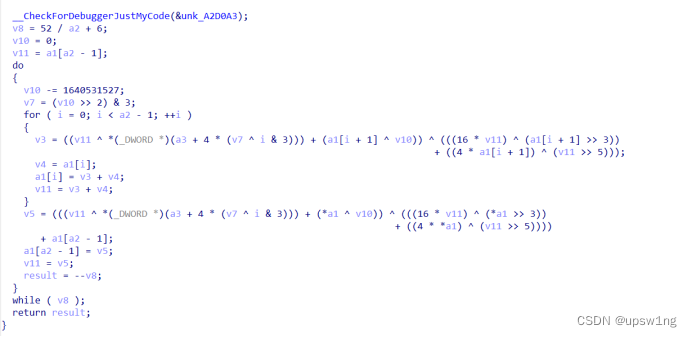
1.首先分析TLS函数,通过调试发现是一个HOOK操作将check函数HOOK成一个异常处理的函数
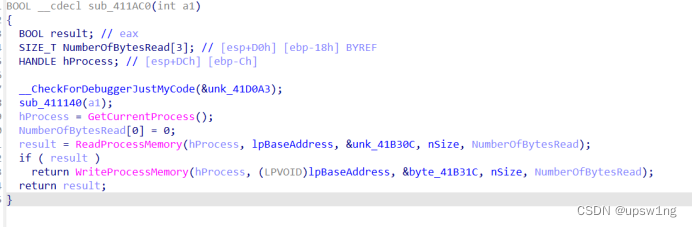
2.会执行到这个函数
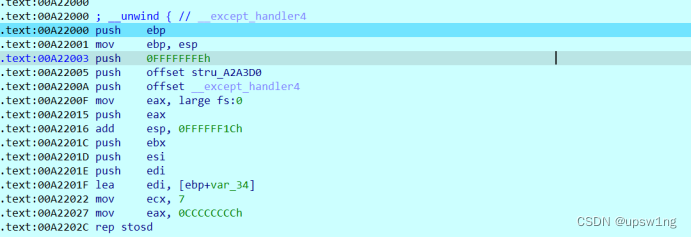
3.创建一个SEH的异常处理,异常处理的函数是sub_A21424函数也就是一个xtea加密函数 int 3会尝试异常触发异常处理函数 通过调试发现会执行两次xtea加密
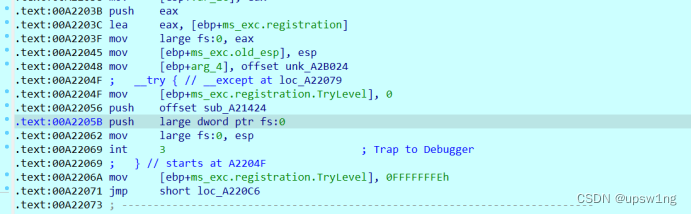
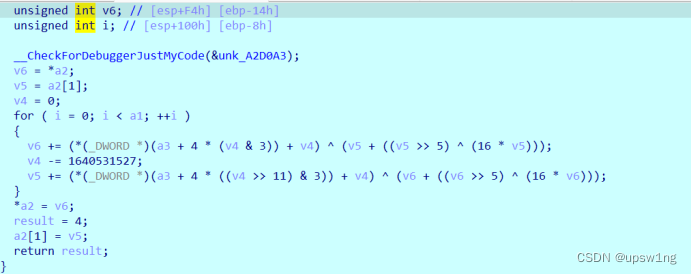
4.Main函数就是xxtea加密,程序流程: HOOK -> xxtea加密 -> 2次xtea加密 ->比较
5.exp
#include <stdio.h>
#include <stdlib.h>
#include <stdint.h>
int delta = 0x61C88647;
#define MX (((z>>5^y<<2) + (y>>3^z<<4)) ^ ((sum^y) + (key[(p&3)^e] ^ z)))
void xteadecrypt(uint32_t* v, uint32_t* k) {
uint32_t v0 = v[0], v1 = v[1];
// uint32_t k0 = k[0], k1 = k[1], k2 = k[2], k3 = k[3];
uint32_t sum = -delta * 36;
for (size_t i = 0; i < 36; i++)
{
v1 -= (((v0 << 4) ^ (v0 >> 5)) + v0) ^ (sum + k[(sum >> 11) & 3]);
sum += 0x61C88647;
v0 -= (((v1 << 4) ^ (v1 >> 5)) + v1) ^ (sum + k[sum & 3]);
}
v[0] = v0; v[1] = v1;
}
void btea(uint32_t* v, int n, uint32_t const key[4])
{
uint32_t y, z, sum;
unsigned int p, rounds, e;
//加密
n = -n;
rounds = 6 + 52 / n;
sum = rounds * -delta;
y = v[0];
do
{
e = (sum >> 2) & 3;
for (p = n - 1; p > 0; p--)
{
z = v[p - 1];
y = v[p] -= MX;
}
z = v[n - 1];
y = v[0] -= MX;
sum += delta;
} while (--rounds);
}
int main()
{
uint8_t enc[32] = { 0xC1, 0xA7, 0xAA, 0x87, 0xB6, 0x21, 0x73, 0x85, 0x8C, 0xD2,
0x71, 0x0E, 0xF2, 0x39, 0xDF, 0xCA, 0x14, 0xCA, 0xEF, 0x58,
0xD8, 0xD9, 0xE7, 0xD7, 0x5D, 0x5C, 0x9F, 0xF2, 0x5E, 0xD4,
0x5E, 0x5F };
uint32_t temp[2] = { 0,0 };
uint32_t* p = (uint32_t*)enc;
uint32_t key[4] = { 0x44,0x41,0x53,0x21 };
for (int i = 0; i < 8; i += 2)
{
temp[0] = p[i];
temp[1] = p[i + 1];
xteadecrypt(temp, key);
p[i] = temp[0];
p[i + 1] = temp[1];
}
for (int i = 0; i < 8; i += 2)
{
temp[0] = p[i];
temp[1] = p[i + 1];
xteadecrypt(temp, key);
p[i] = temp[0];
p[i + 1] = temp[1];
}
btea(p, -8, key);
for (int i = 0; i < 8; i++)
{
for (int j = 0; j < sizeof(uint32_t) / sizeof(uint8_t); j++)
{
printf("%c", (p[i] >> (j * 8)) & 0xFF);
}
}






 文章描述了解密RE挑战中的三个问题,涉及字符串加密、加密函数分析、反调试技术以及使用VM和xtea/xxtea加密算法。主要内容包括加密逻辑、调试过程和解密策略,目标是找出关键的加密密钥。
文章描述了解密RE挑战中的三个问题,涉及字符串加密、加密函数分析、反调试技术以及使用VM和xtea/xxtea加密算法。主要内容包括加密逻辑、调试过程和解密策略,目标是找出关键的加密密钥。














 604
604

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








