Docker Remote API未授权访问漏洞,此API主要目的是取代命令行界面;
Dcoker swarm是docker下的分布化应用的本地集群,开放2375监听容器时,会调用这个API,方便的docker集群管理和扩展(绑定在0.0.0.0上,允许所有ip访问)
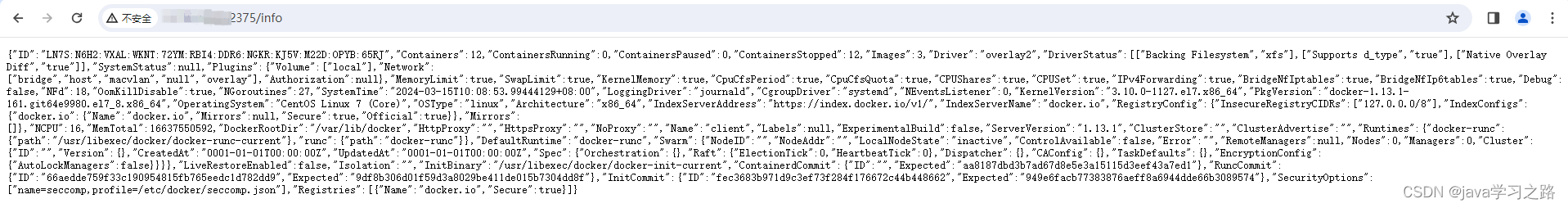
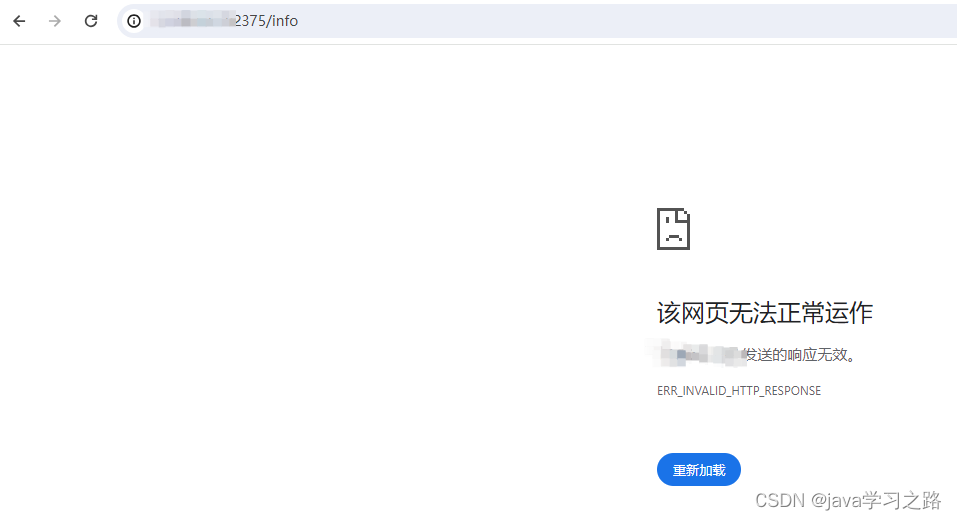
漏洞确认:可以通过浏览器访问http://ip:2375/
会返回404page not fount
会返回docker容器信息
漏洞的攻击过程大家可以网上找一下看看,这类信息网上很多,我就不多说了
漏洞防御方法有以下2种:
- 设置ACL,只允许信任的IP端口连接对应端口
- 开启TLS,使用生成的证书进行认证
今天主要说的是开启TLS认证方法
利用脚本自动生成证书,脚本(auto-tls-certs.sh)如下:
#!/bin/bash
#
# -------------------------------------------------------------
# 自动创建 Docker TLS 证书
# -------------------------------------------------------------
# 以下是配置信息
# --[BEGIN]------------------------------
IP="10.10.1.1"
PASSWORD="123456"
COUNTRY="CN"
STATE="BEIJING"
CITY="BEIJING"
ORGANIZATION="test"
ORGANIZATIONAL_UNIT="Dev"
COMMON_NAME="$IP"
EMAIL="test"
# --[END]--
# Generate CA key
openssl genrsa -aes256 -passout "pass:$PASSWORD" -out "ca-key.pem" 4096
# Generate CA
openssl req -new -x509 -days 365 -key "ca-key.pem" -sha256 -out "ca.pem" -passin "pass:$PASSWORD" -subj "/C=$COUNTRY/ST=$STATE/L=$CITY/O=$ORGANIZATION/OU=$ORGANIZATIONAL_UNIT/CN=$COMMON_NAME/emailAddress=$EMAIL"
# Generate Server key
openssl genrsa -out "server-key.pem" 4096
# Generate Server Certs.
openssl req -subj "/CN=$COMMON_NAME" -sha256 -new -key "server-key.pem" -out server.csr
echo "subjectAltName = IP:$IP,IP:127.0.0.1" >> extfile.cnf
echo "extendedKeyUsage = serverAuth" >> extfile.cnf
openssl x509 -req -days 365 -sha256 -in server.csr -passin "pass:$PASSWORD" -CA "ca.pem" -CAkey "ca-key.pem" -CAcreateserial -out "server-cert.pem" -extfile extfile.cnf
# Generate Client Certs.
rm -f extfile.cnf
openssl genrsa -out "key.pem" 4096
openssl req -subj '/CN=client' -new -key "key.pem" -out client.csr
echo extendedKeyUsage = clientAuth >> extfile.cnf
openssl x509 -req -days 365 -sha256 -in client.csr -passin "pass:$PASSWORD" -CA "ca.pem" -CAkey "ca-key.pem" -CAcreateserial -out "cert.pem" -extfile extfile.cnf
rm -vf client.csr server.csr
chmod -v 0400 "ca-key.pem" "key.pem" "server-key.pem"
chmod -v 0444 "ca.pem" "server-cert.pem" "cert.pem"
# 打包客户端证书
mkdir -p "tls-client-certs"
cp -f "ca.pem" "cert.pem" "key.pem" "tls-client-certs/"
cd "tls-client-certs"
tar zcf "tls-client-certs.tar.gz" *
mv "tls-client-certs.tar.gz" ../
cd ..
rm -rf "tls-client-certs"
# 拷贝服务端证书
mkdir -p /etc/docker/certs.d
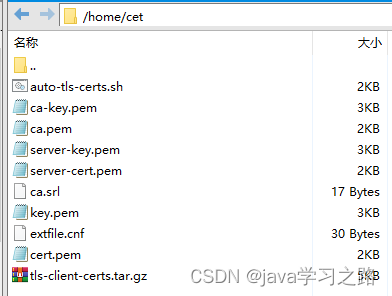
cp "ca.pem" "server-cert.pem" "server-key.pem" /etc/docker/certs.d/执行以上脚本会在
服务端的证书生成在: /etc/docker/certs.d
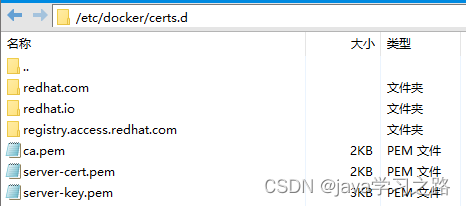
客户端证书自动打包为 tls-client-certs.tar.gz
服务端证书生成后,添加到docker.service中
我的docker.service目录在/usr/lib/systemd/system/
执行linux命令:
vi /usr/lib/systemd/system/docker.service
在ExecStart中添加
--tlsverify --tlscacert=/etc/docker/certs.d/ca.pem --tlscert=/etc/docker/certs.d/server-cert.pem --tlskey=/etc/docker/certs.d/server-key.pem \
这个地方路径不要错了,否者docker.service 启动不了
如图: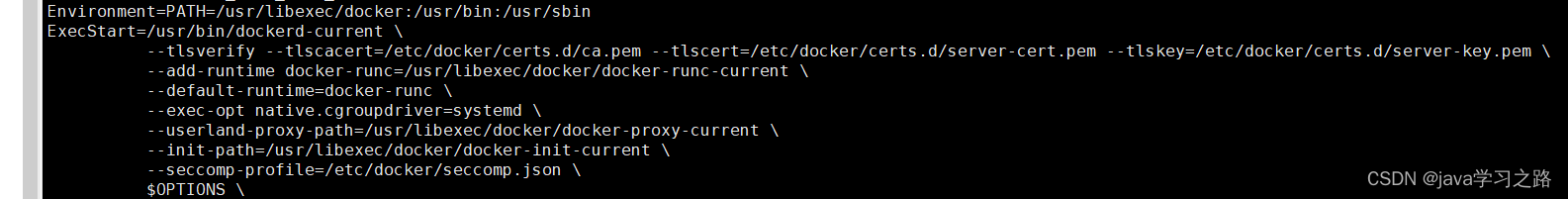
上面文件编辑保存后执行,以下命令重载配置重启服务:
systemctl daemon-reload
service docker restart
至此:docker API添加了证书认证
再访问http://ip:2375/info 就返回错误了
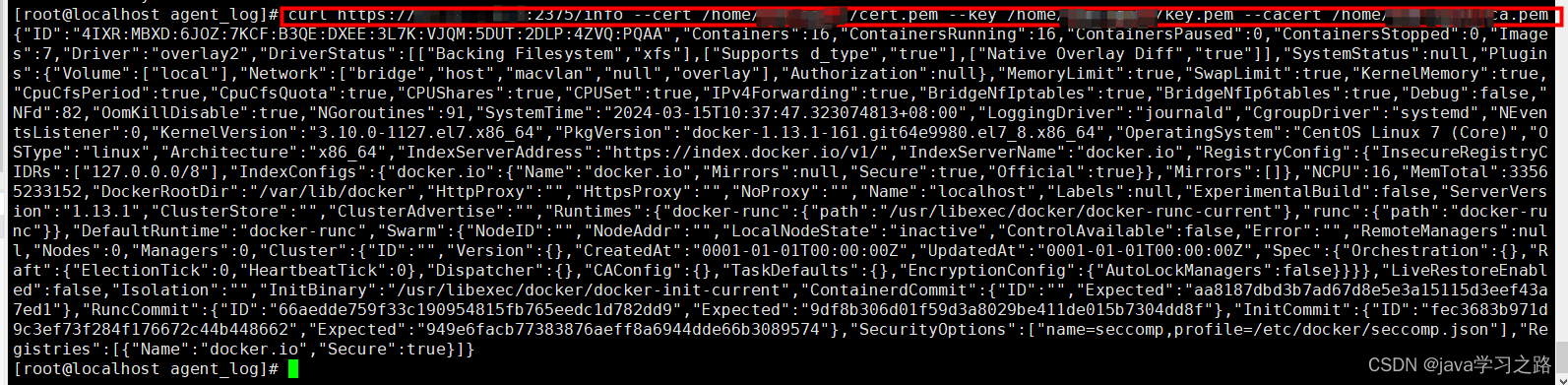
客户端通过TLS访问docker API
将tls-client-certs.tar.gz文件发送到客户端,解压到/home目录
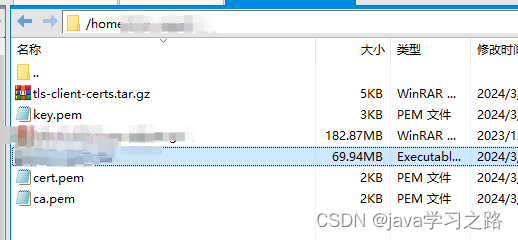
在客户端执行请求,参数携带客户端证书路径就可以返回容器信息了:
curl https://ip:2375/info --cert /home/cert.pem --key /home/key.pem --cacert /home/ca.pem
以上就是 Docker 开启TLS,使用生成的证书进行认证
另外记录一个java使用TLS调用docker远程api的方法:
@Bean
public DockerClient dockerClient() {
//本机ip
String localIp = "127.0.0.1";
com.github.dockerjava.core.DockerClientConfig config = null;
if (useTLS) {
config = DefaultDockerClientConfig.createDefaultConfigBuilder()
.withDockerHost("tcp://" + localIp + ":2375")
.withDockerTlsVerify(true)
.withDockerCertPath("/home/") //客户端证书在服务器上的位置
.build();
} else {
config = DefaultDockerClientConfig.createDefaultConfigBuilder()
.withDockerHost("tcp://" + localIp + ":2375")
.withDockerTlsVerify(false)
.build();
}
DockerHttpClient httpClient = new ApacheDockerHttpClient.Builder()
.dockerHost(config.getDockerHost())
.sslConfig(config.getSSLConfig())
.maxConnections(100)
.connectionTimeout(Duration.ofSeconds(30))
.responseTimeout(Duration.ofSeconds(45))
.build();
DockerClient dockerClient = DockerClientImpl.getInstance(config, httpClient);
return dockerClient;
}




















 107
107











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








