master1:kubeadm init --config=/etc/kubernetes/kubeadm-config.yaml --upload-certs
其余master:

0.阶段
只有master才需要证书,worker只需要kubelet<->api-server.
0.1 init
preflight Run pre-flight checks
certs Certificate generation
/ca Generate the self-signed Kubernetes CA to provision identities for other Kubernetes components
/apiserver Generate the certificate for serving the Kubernetes API
/apiserver-kubelet-client Generate the certificate for the API server to connect to kubelet
/front-proxy-ca Generate the self-signed CA to provision identities for front proxy
/front-proxy-client Generate the certificate for the front proxy client
/etcd-ca Generate the self-signed CA to provision identities for etcd
/etcd-server Generate the certificate for serving etcd
/etcd-peer Generate the certificate for etcd nodes to communicate with each other
/etcd-healthcheck-client Generate the certificate for liveness probes to healthcheck etcd
/apiserver-etcd-client Generate the certificate the apiserver uses to access etcd
/sa Generate a private key for signing service account tokens along with its public key
kubeconfig Generate all kubeconfig files necessary to establish the control plane and the admin kubeconfig file
/admin Generate a kubeconfig file for the admin to use and for kubeadm itself
/kubelet Generate a kubeconfig file for the kubelet to use *only* for cluster bootstrapping purposes
/controller-manager Generate a kubeconfig file for the controller manager to use
/scheduler Generate a kubeconfig file for the scheduler to use
kubelet-start Write kubelet settings and (re)start the kubelet
control-plane Generate all static Pod manifest files necessary to establish the control plane
/apiserver Generates the kube-apiserver static Pod manifest
/controller-manager Generates the kube-controller-manager static Pod manifest
/scheduler Generates the kube-scheduler static Pod manifest
etcd Generate static Pod manifest file for local etcd
/local Generate the static Pod manifest file for a local, single-node local etcd instance
upload-config Upload the kubeadm and kubelet configuration to a ConfigMap
/kubeadm Upload the kubeadm ClusterConfiguration to a ConfigMap
/kubelet Upload the kubelet component config to a ConfigMap
upload-certs Upload certificates to kubeadm-certs
mark-control-plane Mark a node as a control-plane
bootstrap-token Generates bootstrap tokens used to join a node to a cluster
kubelet-finalize Updates settings relevant to the kubelet after TLS bootstrap
/experimental-cert-rotation Enable kubelet client certificate rotation
addon Install required addons for passing Conformance tests
/coredns Install the CoreDNS addon to a Kubernetes cluster
/kube-proxy Install the kube-proxy addon to a Kubernetes cluster0.2 join
preflight Run join pre-flight checks
control-plane-prepare Prepare the machine for serving a control plane[仅针对master节点]
/download-certs [EXPERIMENTAL] Download certificates shared among control-plane nodes from the kubeadm-certs Secret
/certs Generate the certificates for the new control plane components
/kubeconfig Generate the kubeconfig for the new control plane components
/control-plane Generate the manifests for the new control plane components
kubelet-start Write kubelet settings, certificates and (re)start the kubelet
control-plane-join Join a machine as a control plane instance
/etcd Add a new local etcd member
/update-status Register the new control-plane node into the ClusterStatus maintained in the kubeadm-config ConfigMap
/mark-control-plane Mark a node as a control-plane1.证书
1.1 kubeadm init
| 证书名 | common Name | group |
|---|---|---|
| ca | kubernetes | 无 |
| apiserver | kube-apiserver makeAltNamesMutator(pkiutil.GetEtcdPeerAltNames), | 无 |
| apiserver-kubelet-client | kube-apiserver-kubelet-client | system:masters |
| front-proxy-ca | front-proxy-ca | 无 |
| front-proxy-client | front-proxy-client | 无 |
| etcd-ca | etcd-ca | 无 |
| etcd-server | makeAltNamesMutator(pkiutil.GetEtcdPeerAltNames), setCommonNameToNodeName(), | 无 |
| etcd-peer | makeAltNamesMutator(pkiutil.GetEtcdPeerAltNames), setCommonNameToNodeName(), | 无 |
| etcd-healthcheck-client | kube-etcd-healthcheck-client | system:masters |
| apiserver-etcd-client | apiserver-etcd-client | system:masters |
1.2 kubeadm join
1.2.1 针对master
control-plane-prepare Prepare the machine for serving a control plane
/download-certs [EXPERIMENTAL] Download certificates shared among control-plane nodes from the kubeadm-certs Secret
/certs Generate the certificates for the new control plane components
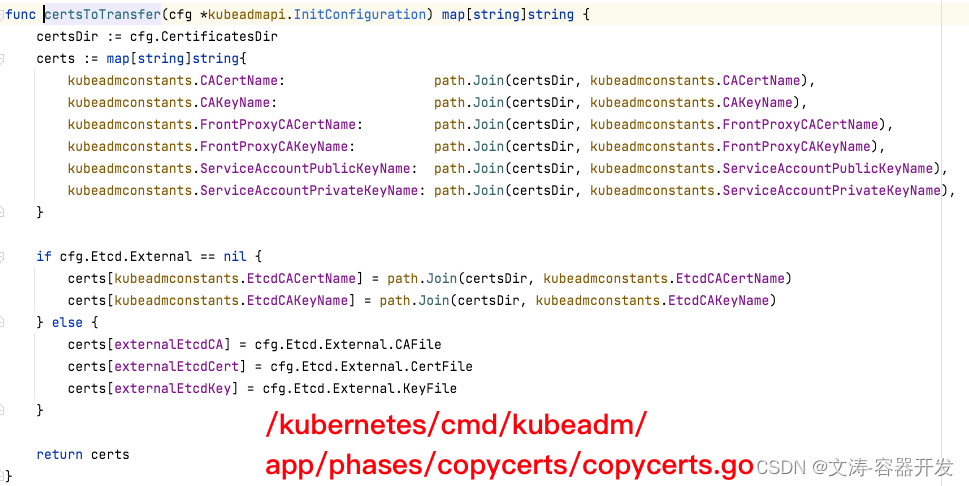
1)下载证书阶段
从kube-system的sercert"kubeadm-certs"中下载证书。
需要下载的证书:
2)certs阶段
1.创建未下载的证书。
2.创建serviceAccount使用的密钥。
1.2.2 针对worker节点
需要证书:kubelet访问api-server。
kubeadm未对上述证书进行操作。
kubedam启动时,根据--token参数生成"/etc/kubernetes/bootstrap-kubelet.conf"。
之后kubelet执行TLS Bootstrap,将"/etc/kubernetes/bootstrap-kubelet.conf"转化为"/etc/kubernetes/kubelet.conf".
1)/etc/kubernetes/bootstrap-kubelet.conf

2)/etc/kubernetes/kubelet.conf





















 9218
9218











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








