接入正题:简易的动态js加密
-
首先hook到cookie:
// ==UserScript== // @name Hook Cookie // @namespace http://tampermonkey.net/ // @version 0.1 // @description pass // @author ayf // @run-at document-start // @match *://www.python-spider.com/* // @grant none // ==/UserScript== (function () { 'use strict'; Object.defineProperty(document, "cookie", { set:function(val){ console.log(11111) if(val.indexOf("m") != -1){ debugger; } return val; } }) })();
2.刷新网页打断点:
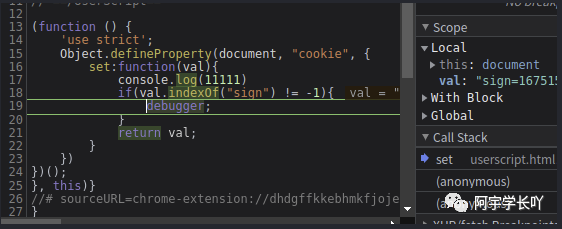
断点调试,进入下一层,找到sign位置:
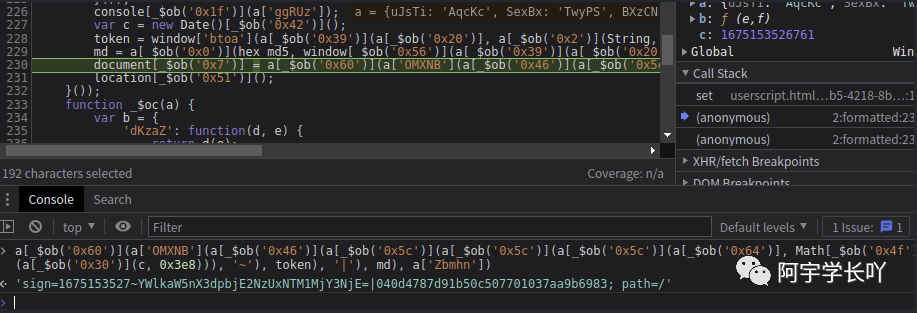
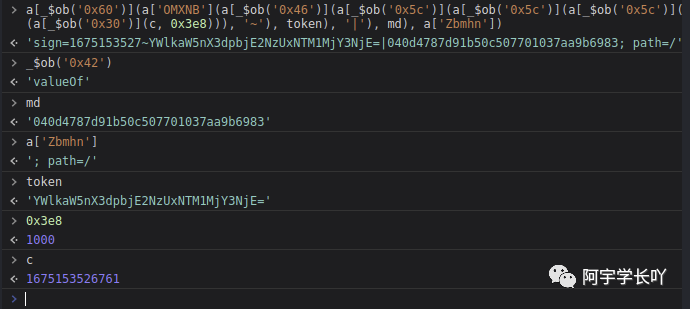
可以看到混淆后的代码:
var c = new Date()[_$ob('0x42')]();
token = window['btoa'](a[_$ob('0x39')](a[_$ob('0x20')], a[_$ob('0x2')](String, c)));
md = a[_$ob('0x0')](hex_md5, window[_$ob('0x56')](a[_$ob('0x39')](a[_$ob('0x20')], a[_$ob('0x0')](String, Math[_$ob('0x4f')](a[_$ob('0x36')](c, 0x3e8))))));
document[_$ob('0x7')] = a[_$ob('0x60')](a['OMXNB'](a[_$ob('0x46')](a[_$ob('0x5c')](a[_$ob('0x5c')](a[_$ob('0x5c')](a[_$ob('0x64')], Math[_$ob('0x4f')](a[_$ob('0x30')](c, 0x3e8))), '~'), token), '|'), md), a['Zbmhn']);然后一步步控制台输出还原:
var c = new Date()[_$ob('0x42')]();
var c = new Date()['valueOf']();然后一步步以此类推:就可以得到值
至此,结束!
凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!凑字数!

























 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








