Jwt Token(对称加密,主要用于鉴权)根据密钥生成,需要密钥解密验证。
// 生成一个JwtToken,包含uid
func CreatJwt(profileId string, key string) (string, error) {
at := jwt.NewWithClaims(jwt.SigningMethodHS256, jwt.MapClaims{
"uid": profileId,
"exp": time.Now().Add(time.Hour).Unix(),
})
token, err := at.SignedString([]byte(key))
if err != nil {
return "", err
}
return token, nil
}
// 从Jwt中解析Token
func ParseToken(token string, key string) (string, error) {
claim, err := jwt.Parse(token, func(token *jwt.Token) (interface{}, error) {
// Don't forget to validate the alg is what you expect:
if _, ok := token.Method.(*jwt.SigningMethodHMAC); !ok {
return nil, ErrTokenSigningMethod
}
return []byte(key), nil
})
if claims, ok := claim.Claims.(jwt.MapClaims); ok && claim.Valid {
return claims["uid"].(string), nil
//return claim.Claims.(jwt.MapClaims)["uid"].(string), nil
} else if ve, ok := err.(*jwt.ValidationError); ok {
if ve.Errors&jwt.ValidationErrorMalformed != 0 {
return "", ErrTokenMalformed
} else if ve.Errors&(jwt.ValidationErrorExpired|jwt.ValidationErrorNotValidYet) != 0 {
// Token is either expired or not active yet
return "", ErrTokenExpired
} else {
return "", ErrTokenHandle
}
} else {
return "", ErrTokenHandle
}
}
- 参考:https://godoc.org/github.com/dgrijalva/jwt-go#example-Parse–Hmac
- 参考: https://www.jianshu.com/p/e4d9dcda0558?from=singlemessage
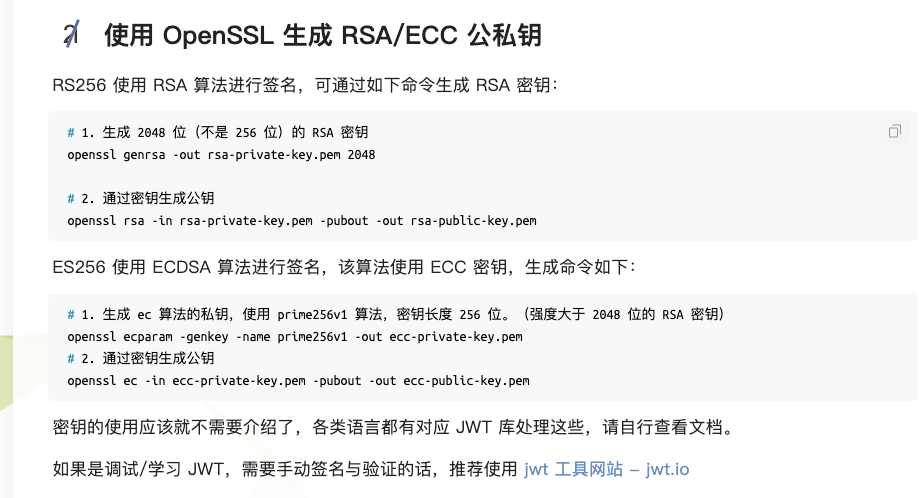
1、生成 2048 位(不是 256 位)的 RSA 密钥
openssl genrsa -out rsa-private-key.pem 2048
2、通过密钥生成公钥
openssl rsa -in rsa-private-key.pem -pubout -out rsa-public-key.pem
参考:https://www.cnblogs.com/kirito-c/p/12402066.html





















 433
433











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








