0x01、实验环境
1、靶机:Metasploitable(192.168.97.140)
浏览器访问:http://192.168.97.140/dvwa
Username=admin
Password=password
2、攻击机:kali(192.168.97.129)
0x02、Httrack工具
1、Httrack:是一种专门针对Web服务器的一种工具
//其可以把站点下所有文件拷贝下来
2、httrack实战
例子1:
靶机:Metasploitable(192.168.97.140)
攻击机:kali(192.168.97.129)
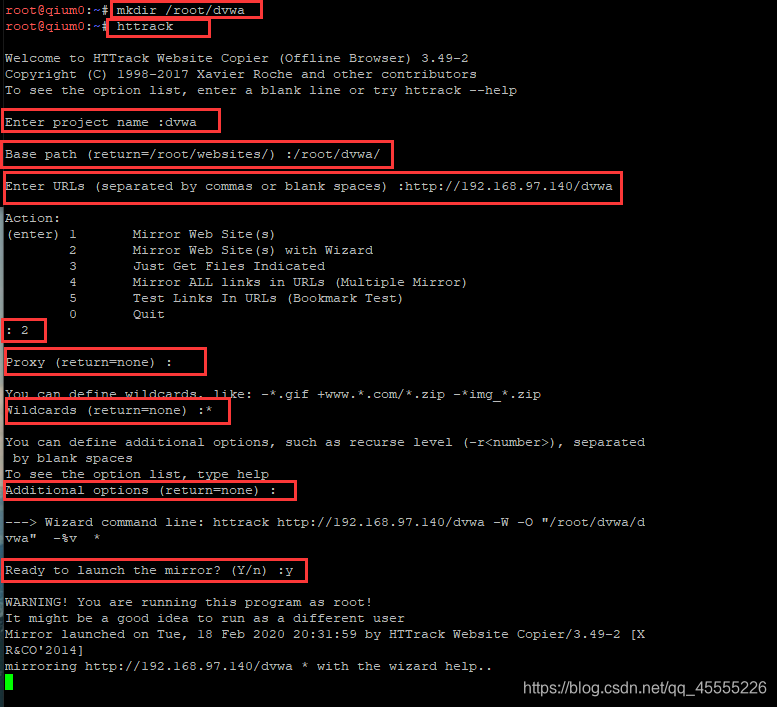
kali上:
mkdir /root/dvwa
#httrack
dvwa
http://192.168.97.140
2
回车
*
回车
y
如下图所示:

0x03、扫描工具Nikto
1、Nikto简介
①、Perl语言开发的开源web安全扫描器
②、用来搜索存在安全隐患的文件
③、扫描服务器配置漏洞
④、扫描Web Application层面的安全隐患
⑤、避免404误判:
很多服务器不遵守RFC标准,对于不存在的对象返回200响应码;
依据响应文件内容判断,不同扩展名的文件404响应内容不同;
去除时间信息后的内容取MD5值;
⑥、-no404:提高性能,但是存在误判;
2、nikto命令
man nikto //查看使用手册
nikto -list-plugins //查看插件
nikto //查看版本等信息
nikto -host //后可加url,可加ip、域名(d端口号)
nikto -evasion //使用LibWhisker中对IDS的躲避技术
①、随机URL编码(非UTF-8方式)
②、自选择路径
③、过早结束路径(/./)
④、优先考虑长随机字符串
⑤、参数欺骗
⑥、使用TAB作为命令的分隔符
⑦、使用变化的URL
⑧、使用Windows路径分隔符"\"
3、nikto实战
例子1:利用nikto扫描站点
靶机:Metasploitable(192.168.97.140:80)或(http://192.168.97.140/dvwa)
1、
# nikto -host http://192.168.97.140/dvwa
- Nikto v2.1.6
---------------------------------------------------------------------------
+ Target IP: 192.168.97.140
+ Target Hostname: 192.168.97.140
+ Target Port: 80
+ Start Time: 2020-02-18 20:42:42 (GMT8)
---------------------------------------------------------------------------
+ Server: Apache/2.2.8 (Ubuntu) DAV/2
+ Cookie PHPSESSID created without the httponly flag
+ Cookie security created without the httponly flag
+ Retrieved x-powered-by header: PHP/5.2.4-2ubuntu5.10
+ The anti-clickjacking X-Frame-Options header is not present.
+ The X-XSS-Protection header is not defined. This header can hint to the user agent to protect against some forms of XSS
+ The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type
+ Root page / redirects to: login.php
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ Server may leak inodes via ETags, header found with file /dvwa/robots.txt, inode: 93164, size: 26, mtime: Tue Mar 16 13:56:22 2010
+ Uncommon header 'tcn' found, with contents: list
+ Apache mod_negotiation is enabled with MultiViews, which allows attackers to easily brute force file names. See http://www.wisec.it/sectou.php?id=4698ebdc59d15. The following alternatives for 'index' were found: index.php
+ Apache/2.2.8 appears to be outdated (current is at least Apache/2.4.37). Apache 2.2.34 is the EOL for the 2.x branch.
+ Allowed HTTP Methods: GET, HEAD, POST, OPTIONS, TRACE
+ OSVDB-877: HTTP TRACE method is active, suggesting the host is vulnerable to XST
+ OSVDB-3268: /dvwa/config/: Directory indexing found.
+ /dvwa/config/: Configuration information may be available remotely.
+ OSVDB-12184: /dvwa/?=PHPB8B5F2A0-3C92-11d3-A3A9-4C7B08C10000: PHP reveals potentially sensitive information via certain HTTP requests that contain specific QUERY strings.
+ OSVDB-12184: /dvwa/?=PHPE9568F36-D428-11d2-A769-00AA001ACF42: PHP reveals potentially sensitive information via certain HTTP requests that contain specific QUERY strings.
+ OSVDB-12184: /dvwa/?=PHPE9568F34-D428-11d2-A769-00AA001ACF42: PHP reveals potentially sensitive information via certain HTTP requests that contain specific QUERY strings.
+ OSVDB-12184: /dvwa/?=PHPE9568F35-D428-11d2-A769-00AA001ACF42: PHP reveals potentially sensitive information via certain HTTP requests that contain specific QUERY strings.
+ OSVDB-3092: /dvwa/login/: This might be interesting...
+ OSVDB-3268: /dvwa/docs/: Directory indexing found.
+ OSVDB-3092: /dvwa/CHANGELOG.txt: A changelog was found.
+ /dvwa/login.php: Admin login page/section found.
+ /dvwa/?-s: PHP allows retrieval of the source code via the -s parameter, and may allow command execution. See http://www.kb.cert.org/vuls/id/520827
+ /dvwa/login.php?-s: PHP allows retrieval of the source code via the -s parameter, and may all







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 8807
8807











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










