dig的强大功能之一是模拟Recursive的运行流程来执行一次DNS查询,本文使用该功能分析DNS查询的流程以及NS记录,Glue record,Referral record等之间的关系和最终查询结果的关系。由此引出NSNXAttack和NRDelegationAttack两种攻击的分析。
查询
首先使用dig +trace获得整个查询的记录,以google.com为例:
~# dig +trace +additional google.com A @f.root-servers.net
; <<>> DiG 9.18.12-0ubuntu0.22.04.2-Ubuntu <<>> +trace +additional google.com A @f.root-servers.net
;; global options: +cmd
. 518400 IN NS d.root-servers.net.
. 518400 IN NS e.root-servers.net.
. 518400 IN NS a.root-servers.net.
. 518400 IN NS m.root-servers.net.
. 518400 IN NS l.root-servers.net.
. 518400 IN NS f.root-servers.net.
. 518400 IN NS g.root-servers.net.
. 518400 IN NS h.root-servers.net.
. 518400 IN NS b.root-servers.net.
. 518400 IN NS k.root-servers.net.
. 518400 IN NS j.root-servers.net.
. 518400 IN NS c.root-servers.net.
. 518400 IN NS i.root-servers.net.
. 518400 IN RRSIG NS 8 0 518400 20230913050000 20230831040000 11019 . sTegTb4O1m5gsG6/bNYMthI0KmGTq0sqyKzys6J9GjN05eew+r+hommx jkUk2k0SL8gFMvEOTCmObUw94Ln6qHK5FbyThvQFvxzF7TMBc+YIVEAU 9qYKNNcB+kXOdkrSYVUjFFKfIWbczm/4XhvAv8GkZqbNKEJwkgyKi9bH ippRdD67TNBWoaij+Q8XvlwnHXP3xfiptcTuxtsx8zSlBzVvKMb2GvlL W/Uf6QR+eL5QstjrqOv6TCMPz5UBtEQbuPBiZWArdsERT/3WH8Qir6Rq sFGpVbXijVDFykKxR3Cjby5zB/iQGlAdxFUY2uwJvvVu1dR/WE/G2IoG OUsTMw==
d.root-servers.net. 518400 IN A 199.7.91.13
d.root-servers.net. 518400 IN AAAA 2001:500:2d::d
e.root-servers.net. 518400 IN A 192.203.230.10
e.root-servers.net. 518400 IN AAAA 2001:500:a8::e
a.root-servers.net. 518400 IN A 198.41.0.4
a.root-servers.net. 518400 IN AAAA 2001:503:ba3e::2:30
m.root-servers.net. 518400 IN A 202.12.27.33
m.root-servers.net. 518400 IN AAAA 2001:dc3::35
l.root-servers.net. 518400 IN A 199.7.83.42
l.root-servers.net. 518400 IN AAAA 2001:500:9f::42
f.root-servers.net. 518400 IN A 192.5.5.241
f.root-servers.net. 518400 IN AAAA 2001:500:2f::f
g.root-servers.net. 518400 IN A 192.112.36.4
g.root-servers.net. 518400 IN AAAA 2001:500:12::d0d
h.root-servers.net. 518400 IN A 198.97.190.53
h.root-servers.net. 518400 IN AAAA 2001:500:1::53
b.root-servers.net. 518400 IN A 199.9.14.201
b.root-servers.net. 518400 IN AAAA 2001:500:200::b
k.root-servers.net. 518400 IN A 193.0.14.129
k.root-servers.net. 518400 IN AAAA 2001:7fd::1
j.root-servers.net. 518400 IN A 192.58.128.30
j.root-servers.net. 518400 IN AAAA 2001:503:c27::2:30
c.root-servers.net. 518400 IN A 192.33.4.12
c.root-servers.net. 518400 IN AAAA 2001:500:2::c
i.root-servers.net. 518400 IN A 192.36.148.17
i.root-servers.net. 518400 IN AAAA 2001:7fe::53
;; Received 1097 bytes from 192.5.5.241#53(f.root-servers.net) in 210 ms
com. 172800 IN NS i.gtld-servers.net.
com. 172800 IN NS e.gtld-servers.net.
com. 172800 IN NS a.gtld-servers.net.
com. 172800 IN NS d.gtld-servers.net.
com. 172800 IN NS j.gtld-servers.net.
com. 172800 IN NS f.gtld-servers.net.
com. 172800 IN NS g.gtld-servers.net.
com. 172800 IN NS k.gtld-servers.net.
com. 172800 IN NS c.gtld-servers.net.
com. 172800 IN NS b.gtld-servers.net.
com. 172800 IN NS h.gtld-servers.net.
com. 172800 IN NS l.gtld-servers.net.
com. 172800 IN NS m.gtld-servers.net.
com. 86400 IN DS 30909 8 2 E2D3C916F6DEEAC73294E8268FB5885044A833FC5459588F4A9184CF C41A5766
com. 86400 IN RRSIG DS 8 1 86400 20230913050000 20230831040000 11019 . SDSqlwjZKrqNVP2SV+cRQEaiBBNvx8tIP8+tbNmNGyi9LqcDEKCWB5J8 3qfhueg/Wg31In3vFA7InAoeCciGeBXegT+iNdPNRt+/L2oXk5WYteQI YpQ9TvjilFBmvbfrfoJUxCe4yQsN7cMsvOB17e9OpWAdZxTdjra7qT+I GkHCzIhWJJ0y1LlpqGOSwPff2N3QABYzndPE5K/8Jn0kQaXS4yPSKN/G 6uGag6wrdb3e6wcLwg0iOe0B7cjBODKJF1OfnfIjdjd59w8uQfK8Zs9z 4etaabDHVcYrLCtVZeRU3uZ8jDYhw7O6EqjBQYgUZkEMe5TDIML7M+CT eP70VQ==
i.gtld-servers.net. 172800 IN A 192.43.172.30
i.gtld-servers.net. 172800 IN AAAA 2001:503:39c1::30
e.gtld-servers.net. 172800 IN A 192.12.94.30
e.gtld-servers.net. 172800 IN AAAA 2001:502:1ca1::30
a.gtld-servers.net. 172800 IN A 192.5.6.30
a.gtld-servers.net. 172800 IN AAAA 2001:503:a83e::2:30
d.gtld-servers.net. 172800 IN A 192.31.80.30
d.gtld-servers.net. 172800 IN AAAA 2001:500:856e::30
j.gtld-servers.net. 172800 IN A 192.48.79.30
j.gtld-servers.net. 172800 IN AAAA 2001:502:7094::30
f.gtld-servers.net. 172800 IN A 192.35.51.30
f.gtld-servers.net. 172800 IN AAAA 2001:503:d414::30
g.gtld-servers.net. 172800 IN A 192.42.93.30
g.gtld-servers.net. 172800 IN AAAA 2001:503:eea3::30
k.gtld-servers.net. 172800 IN A 192.52.178.30
k.gtld-servers.net. 172800 IN AAAA 2001:503:d2d::30
c.gtld-servers.net. 172800 IN A 192.26.92.30
c.gtld-servers.net. 172800 IN AAAA 2001:503:83eb::30
b.gtld-servers.net. 172800 IN A 192.33.14.30
b.gtld-servers.net. 172800 IN AAAA 2001:503:231d::2:30
h.gtld-servers.net. 172800 IN A 192.54.112.30
h.gtld-servers.net. 172800 IN AAAA 2001:502:8cc::30
l.gtld-servers.net. 172800 IN A 192.41.162.30
l.gtld-servers.net. 172800 IN AAAA 2001:500:d937::30
m.gtld-servers.net. 172800 IN A 192.55.83.30
m.gtld-servers.net. 172800 IN AAAA 2001:501:b1f9::30
;; Received 1170 bytes from 192.5.5.241#53(f.root-servers.net) in 210 ms
google.com. 172800 IN NS ns2.google.com.
google.com. 172800 IN NS ns1.google.com.
google.com. 172800 IN NS ns3.google.com.
google.com. 172800 IN NS ns4.google.com.
CK0POJMG874LJREF7EFN8430QVIT8BSM.com. 86400 IN NSEC3 1 1 0 - CK0Q2D6NI4I7EQH8NA30NS61O48UL8G5 NS SOA RRSIG DNSKEY NSEC3PARAM
CK0POJMG874LJREF7EFN8430QVIT8BSM.com. 86400 IN RRSIG NSEC3 8 2 86400 20230907042432 20230831031432 4459 com. kfAa2AgL3x3C+IosF42yh93sqnQ7+rZxcAopsjOaXsD870wdt6cEDNeB e/3ssjbBsk0tn6mV095Q1LF1ca8c0rpH/fySsq251qNcNiMl6Pd8CUrj mDbXcxX0w8H+4yaARxywy4FDdcwRPtJcHcEQK6PElT0le0lPsQ/DekdS EpBdYJ196p6aN4KFDTuCs00wonokUDdxdImdbYZeVON0PQ==
S84BKCIBC38P58340AKVNFN5KR9O59QC.com. 86400 IN NSEC3 1 1 0 - S84BR9CIB2A20L3ETR1M2415ENPP99L8 NS DS RRSIG
S84BKCIBC38P58340AKVNFN5KR9O59QC.com. 86400 IN RRSIG NSEC3 8 2 86400 20230904050018 20230828035018 4459 com. CT/G8cz9O87WYOeCn9uyhPYbPaLja93Gtlu1zoxLJ4OlHiD4/fxE+Loo jP59N+xuxiYqzazMaDliDYIH3620QUfKSuO6wFY1E1vYT5ghzNogF9+D nQA7I1GLmNLsIAhxolGbG+W/fcb2ixLtgy2CM88k0VAkaLxsCkWBPNET 7iH8YFUx2FyTYQnfW6l328L58lUt7SSNyj/LMG0BZoNtxA==
ns2.google.com. 172800 IN AAAA 2001:4860:4802:34::a
ns2.google.com. 172800 IN A 216.239.34.10
ns1.google.com. 172800 IN AAAA 2001:4860:4802:32::a
ns1.google.com. 172800 IN A 216.239.32.10
ns3.google.com. 172800 IN AAAA 2001:4860:4802:36::a
ns3.google.com. 172800 IN A 216.239.36.10
ns4.google.com. 172800 IN AAAA 2001:4860:4802:38::a
ns4.google.com. 172800 IN A 216.239.38.10
;; Received 836 bytes from 192.33.14.30#53(b.gtld-servers.net) in 220 ms
google.com. 300 IN A 142.250.189.174
;; Received 55 bytes from 216.239.38.10#53(ns4.google.com) in 270 ms+trace选项使得dig以递归的方式查询,@f.root-servers.net指定向某个根发起请求,以获得完整的查询记录。+additional使得dig展示出additional段的内容,在后文中将解释additional内容的重要性。
根据Response中的信息可以分段分析。第一段是关于各个root的查询
. 518400 IN NS d.root-servers.net.
. 518400 IN NS e.root-servers.net.
. 518400 IN NS a.root-servers.net.
. 518400 IN NS m.root-servers.net.
. 518400 IN NS l.root-servers.net.
. 518400 IN NS f.root-servers.net.
. 518400 IN NS g.root-servers.net.
. 518400 IN NS h.root-servers.net.
. 518400 IN NS b.root-servers.net.
. 518400 IN NS k.root-servers.net.
. 518400 IN NS j.root-servers.net.
. 518400 IN NS c.root-servers.net.
. 518400 IN NS i.root-servers.net.
. 518400 IN RRSIG NS 8 0 518400 20230913050000 20230831040000 11019 . sTegTb4O1m5gsG6/bNYMthI0KmGTq0sqyKzys6J9GjN05eew+r+hommx jkUk2k0SL8gFMvEOTCmObUw94Ln6qHK5FbyThvQFvxzF7TMBc+YIVEAU 9qYKNNcB+kXOdkrSYVUjFFKfIWbczm/4XhvAv8GkZqbNKEJwkgyKi9bH ippRdD67TNBWoaij+Q8XvlwnHXP3xfiptcTuxtsx8zSlBzVvKMb2GvlL W/Uf6QR+eL5QstjrqOv6TCMPz5UBtEQbuPBiZWArdsERT/3WH8Qir6Rq sFGpVbXijVDFykKxR3Cjby5zB/iQGlAdxFUY2uwJvvVu1dR/WE/G2IoG OUsTMw==
d.root-servers.net. 518400 IN A 199.7.91.13
d.root-servers.net. 518400 IN AAAA 2001:500:2d::d
e.root-servers.net. 518400 IN A 192.203.230.10
e.root-servers.net. 518400 IN AAAA 2001:500:a8::e
a.root-servers.net. 518400 IN A 198.41.0.4
a.root-servers.net. 518400 IN AAAA 2001:503:ba3e::2:30
m.root-servers.net. 518400 IN A 202.12.27.33
m.root-servers.net. 518400 IN AAAA 2001:dc3::35
l.root-servers.net. 518400 IN A 199.7.83.42
l.root-servers.net. 518400 IN AAAA 2001:500:9f::42
f.root-servers.net. 518400 IN A 192.5.5.241
f.root-servers.net. 518400 IN AAAA 2001:500:2f::f
g.root-servers.net. 518400 IN A 192.112.36.4
g.root-servers.net. 518400 IN AAAA 2001:500:12::d0d
h.root-servers.net. 518400 IN A 198.97.190.53
h.root-servers.net. 518400 IN AAAA 2001:500:1::53
b.root-servers.net. 518400 IN A 199.9.14.201
b.root-servers.net. 518400 IN AAAA 2001:500:200::b
k.root-servers.net. 518400 IN A 193.0.14.129
k.root-servers.net. 518400 IN AAAA 2001:7fd::1
j.root-servers.net. 518400 IN A 192.58.128.30
j.root-servers.net. 518400 IN AAAA 2001:503:c27::2:30
c.root-servers.net. 518400 IN A 192.33.4.12
c.root-servers.net. 518400 IN AAAA 2001:500:2::c
i.root-servers.net. 518400 IN A 192.36.148.17
i.root-servers.net. 518400 IN AAAA 2001:7fe::53
;; Received 1097 bytes from 192.5.5.241#53(f.root-servers.net) in 210 ms本段向指定的root服务器请求了所有root的记录,root的IP地址一般比较固定,因此频繁查询是完全的浪费,实际的Recursive不会这样做。
第二部分是向指定的root对于".com"的查询,返回了一些Authoritative的结果
com. 172800 IN NS i.gtld-servers.net.
com. 172800 IN NS e.gtld-servers.net.
com. 172800 IN NS a.gtld-servers.net.
com. 172800 IN NS d.gtld-servers.net.
com. 172800 IN NS j.gtld-servers.net.
com. 172800 IN NS f.gtld-servers.net.
com. 172800 IN NS g.gtld-servers.net.
com. 172800 IN NS k.gtld-servers.net.
com. 172800 IN NS c.gtld-servers.net.
com. 172800 IN NS b.gtld-servers.net.
com. 172800 IN NS h.gtld-servers.net.
com. 172800 IN NS l.gtld-servers.net.
com. 172800 IN NS m.gtld-servers.net.
com. 86400 IN DS 30909 8 2 E2D3C916F6DEEAC73294E8268FB5885044A833FC5459588F4A9184CF C41A5766
com. 86400 IN RRSIG DS 8 1 86400 20230913050000 20230831040000 11019 . SDSqlwjZKrqNVP2SV+cRQEaiBBNvx8tIP8+tbNmNGyi9LqcDEKCWB5J8 3qfhueg/Wg31In3vFA7InAoeCciGeBXegT+iNdPNRt+/L2oXk5WYteQI YpQ9TvjilFBmvbfrfoJUxCe4yQsN7cMsvOB17e9OpWAdZxTdjra7qT+I GkHCzIhWJJ0y1LlpqGOSwPff2N3QABYzndPE5K/8Jn0kQaXS4yPSKN/G 6uGag6wrdb3e6wcLwg0iOe0B7cjBODKJF1OfnfIjdjd59w8uQfK8Zs9z 4etaabDHVcYrLCtVZeRU3uZ8jDYhw7O6EqjBQYgUZkEMe5TDIML7M+CT eP70VQ==
i.gtld-servers.net. 172800 IN A 192.43.172.30
i.gtld-servers.net. 172800 IN AAAA 2001:503:39c1::30
e.gtld-servers.net. 172800 IN A 192.12.94.30
e.gtld-servers.net. 172800 IN AAAA 2001:502:1ca1::30
a.gtld-servers.net. 172800 IN A 192.5.6.30
a.gtld-servers.net. 172800 IN AAAA 2001:503:a83e::2:30
d.gtld-servers.net. 172800 IN A 192.31.80.30
d.gtld-servers.net. 172800 IN AAAA 2001:500:856e::30
j.gtld-servers.net. 172800 IN A 192.48.79.30
j.gtld-servers.net. 172800 IN AAAA 2001:502:7094::30
f.gtld-servers.net. 172800 IN A 192.35.51.30
f.gtld-servers.net. 172800 IN AAAA 2001:503:d414::30
g.gtld-servers.net. 172800 IN A 192.42.93.30
g.gtld-servers.net. 172800 IN AAAA 2001:503:eea3::30
k.gtld-servers.net. 172800 IN A 192.52.178.30
k.gtld-servers.net. 172800 IN AAAA 2001:503:d2d::30
c.gtld-servers.net. 172800 IN A 192.26.92.30
c.gtld-servers.net. 172800 IN AAAA 2001:503:83eb::30
b.gtld-servers.net. 172800 IN A 192.33.14.30
b.gtld-servers.net. 172800 IN AAAA 2001:503:231d::2:30
h.gtld-servers.net. 172800 IN A 192.54.112.30
h.gtld-servers.net. 172800 IN AAAA 2001:502:8cc::30
l.gtld-servers.net. 172800 IN A 192.41.162.30
l.gtld-servers.net. 172800 IN AAAA 2001:500:d937::30
m.gtld-servers.net. 172800 IN A 192.55.83.30
m.gtld-servers.net. 172800 IN AAAA 2001:501:b1f9::30
;; Received 1170 bytes from 192.5.5.241#53(f.root-servers.net) in 210 ms使用dig再次单独重现这一步,可以得到更具体的结果。
~# dig +additional google.com @f.root-servers.net
; <<>> DiG 9.18.12-0ubuntu0.22.04.2-Ubuntu <<>> +additional google.com @f.root-servers.net
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 48964
;; flags: qr rd; QUERY: 1, ANSWER: 0, AUTHORITY: 13, ADDITIONAL: 27
;; WARNING: recursion requested but not available
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 1472
;; QUESTION SECTION:
;google.com. IN A
;; AUTHORITY SECTION:
com. 172800 IN NS i.gtld-servers.net.
com. 172800 IN NS e.gtld-servers.net.
com. 172800 IN NS a.gtld-servers.net.
com. 172800 IN NS d.gtld-servers.net.
com. 172800 IN NS j.gtld-servers.net.
com. 172800 IN NS f.gtld-servers.net.
com. 172800 IN NS g.gtld-servers.net.
com. 172800 IN NS k.gtld-servers.net.
com. 172800 IN NS c.gtld-servers.net.
com. 172800 IN NS b.gtld-servers.net.
com. 172800 IN NS h.gtld-servers.net.
com. 172800 IN NS l.gtld-servers.net.
com. 172800 IN NS m.gtld-servers.net.
;; ADDITIONAL SECTION:
i.gtld-servers.net. 172800 IN A 192.43.172.30
i.gtld-servers.net. 172800 IN AAAA 2001:503:39c1::30
e.gtld-servers.net. 172800 IN A 192.12.94.30
e.gtld-servers.net. 172800 IN AAAA 2001:502:1ca1::30
a.gtld-servers.net. 172800 IN A 192.5.6.30
a.gtld-servers.net. 172800 IN AAAA 2001:503:a83e::2:30
d.gtld-servers.net. 172800 IN A 192.31.80.30
d.gtld-servers.net. 172800 IN AAAA 2001:500:856e::30
j.gtld-servers.net. 172800 IN A 192.48.79.30
j.gtld-servers.net. 172800 IN AAAA 2001:502:7094::30
f.gtld-servers.net. 172800 IN A 192.35.51.30
f.gtld-servers.net. 172800 IN AAAA 2001:503:d414::30
g.gtld-servers.net. 172800 IN A 192.42.93.30
g.gtld-servers.net. 172800 IN AAAA 2001:503:eea3::30
k.gtld-servers.net. 172800 IN A 192.52.178.30
k.gtld-servers.net. 172800 IN AAAA 2001:503:d2d::30
c.gtld-servers.net. 172800 IN A 192.26.92.30
c.gtld-servers.net. 172800 IN AAAA 2001:503:83eb::30
b.gtld-servers.net. 172800 IN A 192.33.14.30
b.gtld-servers.net. 172800 IN AAAA 2001:503:231d::2:30
h.gtld-servers.net. 172800 IN A 192.54.112.30
h.gtld-servers.net. 172800 IN AAAA 2001:502:8cc::30
l.gtld-servers.net. 172800 IN A 192.41.162.30
l.gtld-servers.net. 172800 IN AAAA 2001:500:d937::30
m.gtld-servers.net. 172800 IN A 192.55.83.30
m.gtld-servers.net. 172800 IN AAAA 2001:501:b1f9::30
;; Query time: 210 msec
;; SERVER: 192.5.5.241#53(f.root-servers.net) (UDP)
;; WHEN: Thu Aug 31 05:06:26 EDT 2023
;; MSG SIZE rcvd: 835可以看到得到了13个AUTHORITY记录和27个ADDITIONAL记录(一个未展示),对于"google.com"的查询并未返回解析".com"的服务器地址而是返回了很多NS记录,这是root将查询委托到了这些gtld-server中,并在Additional区中附带了他们的A和AAAA记录,这就是Glue record。在此处直接返回Authoritative似乎也可行,在下面将介绍Glue record解决更为棘手问题的例子。
下一步是向某个gtld-server请求"google.com"的解析结果,同样返回了NS记录和Additional节中的Glue record,如下
~# dig +additional google.com @b.gtld-servers.net
; <<>> DiG 9.18.12-0ubuntu0.22.04.2-Ubuntu <<>> +additional google.com @b.gtld-servers.net
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 1013
;; flags: qr rd; QUERY: 1, ANSWER: 0, AUTHORITY: 4, ADDITIONAL: 9
;; WARNING: recursion requested but not available
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 4096
;; QUESTION SECTION:
;google.com. IN A
;; AUTHORITY SECTION:
google.com. 172800 IN NS ns2.google.com.
google.com. 172800 IN NS ns1.google.com.
google.com. 172800 IN NS ns3.google.com.
google.com. 172800 IN NS ns4.google.com.
;; ADDITIONAL SECTION:
ns2.google.com. 172800 IN AAAA 2001:4860:4802:34::a
ns2.google.com. 172800 IN A 216.239.34.10
ns1.google.com. 172800 IN AAAA 2001:4860:4802:32::a
ns1.google.com. 172800 IN A 216.239.32.10
ns3.google.com. 172800 IN AAAA 2001:4860:4802:36::a
ns3.google.com. 172800 IN A 216.239.36.10
ns4.google.com. 172800 IN AAAA 2001:4860:4802:38::a
ns4.google.com. 172800 IN A 216.239.38.10
;; Query time: 220 msec
;; SERVER: 192.33.14.30#53(b.gtld-servers.net) (UDP)
;; WHEN: Thu Aug 31 05:37:36 EDT 2023
;; MSG SIZE rcvd: 287自上而下地看这是自然的,不过在此处发生了一个重要的变化,gtld-servers.net是注册局所有的,而查询结果中的ns[1-4].google.com是google自己所有的,google决定自己管理"google.com"子域下的所有域名,如www.google.com, scholar.google.com等等,而这一任务就由ns[1-4].google.com这4个IP来承担。从而google就需要向外界公布自家NS的域名和IP地址,假设google告知了管理".com"的域名管理机构".google.com"域由ns[1-4].google.com管理,并且告知了这4个IP,那么从Recursive的角度看就会进入以下的死循环:
假设Recursive请求"www.google.com"这一域名,请求首先到达root,然后root指向了某个gtld-server来解析".com"子域,然后这个gtld-server以NS记录的形式告诉recursive应该向ns1.google.com进一步查询。如果没有更多信息,recursive就需要再次请求ns1.google.com的地址,重复上述过程并再次得到ns1.google.com的NS记录,从而进入死循环。解决方法是在gtld-server的响应的Additional节中加入ns1.google.com的A/AAAA记录,避免解析之,这就是glue record。总而言之,glue record是存储在某个并不负责解析其所记录的域的authoritative中的记录。
最后一步中,recursive终于得到了他需要的google.com的A记录。
google.com. 300 IN A 142.250.189.174
;; Received 55 bytes from 216.239.38.10#53(ns4.google.com) in 270 msNSNXAttack
在上述的解析过程中glue record并非必须的,仅当authoritative的委托对象在其查询的子域中时glue record才是必须的,假如r.gtld-servers.net在接收到"www.google.com"请求后打算将其委托到s.gtld-servers.net的话,则不需要glue record,这种委托将返回一个仅包含NS记录的Referral Response。
基于这种referral response的可行性,产生了一种放大攻击NSNXAttack,如下图
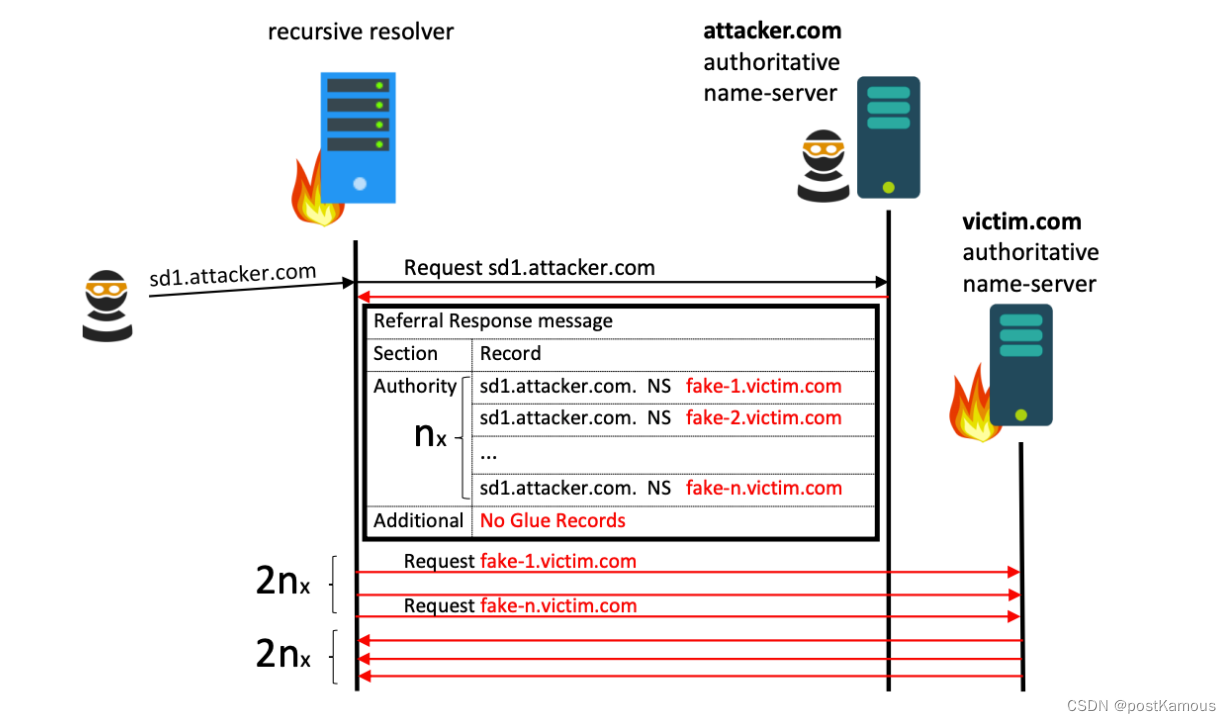
攻击者需要控制一个(若干个)客户端和一个authoritative服务器,利用前面提到的referral response向另外一个authoritative发起攻击。
以 sd1.attacker.com 的 DNS 解析过程为例
在攻击者触发向恶意的name-server进行对应域名解析的时候。
- 首先会由当前网络环境中的上层DNS服务器(服务器A)去检索 attacker.com 的 name-server 服务(服务器B)。
- 攻击者控制该 nameserver 服务器(服务器B)返回特制的响应包(该包的主要目的:通知接收服务器做NS转发查询)。
- 响应包中含有复数条记录。
- 每天记录都表述 sd1.attacker.com 需要转发到 {fake-n}.victim.com 的 dns name-server 服务器(服务器C)去做查询。
- 其中不含对应的IP地址。(确保查询的成立)
- (服务器A)接收到该特制的响应包后会逐一对响应包中的NS记录进行 dns 查询。
- 导致(服务器A)发送大量的请求包/(服务器C)接收大量的请求包导致拒绝服务。
参考NXNSAttack: DNS协议安全漏洞通告 - 360CERT 和原论文NXNSAttack - NXNSAttack by Lior Shafir, New DNS DDoS vulnerability
为了解决该漏洞,BIND,UNBOUND,KNOT等DNS实现引入了Referral Response Limit,限制了recursive在接收到referral response后单次发出的解析请求的数目k,即使referral response中的记录很多(例如1500),recursive也会每次只尝试解析k个NS记录,从而限制了放大系数,并且在k个记录均返回NXDomain时放弃此次客户的查询。然而这个机制引出了另一个漏洞的出现,在后面我们将介绍NRDelegationAttack





















 933
933











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








