(一)、使不同vlan进行通信的方法
1.创建3层vlan接口
创建如图1所示的拓扑结构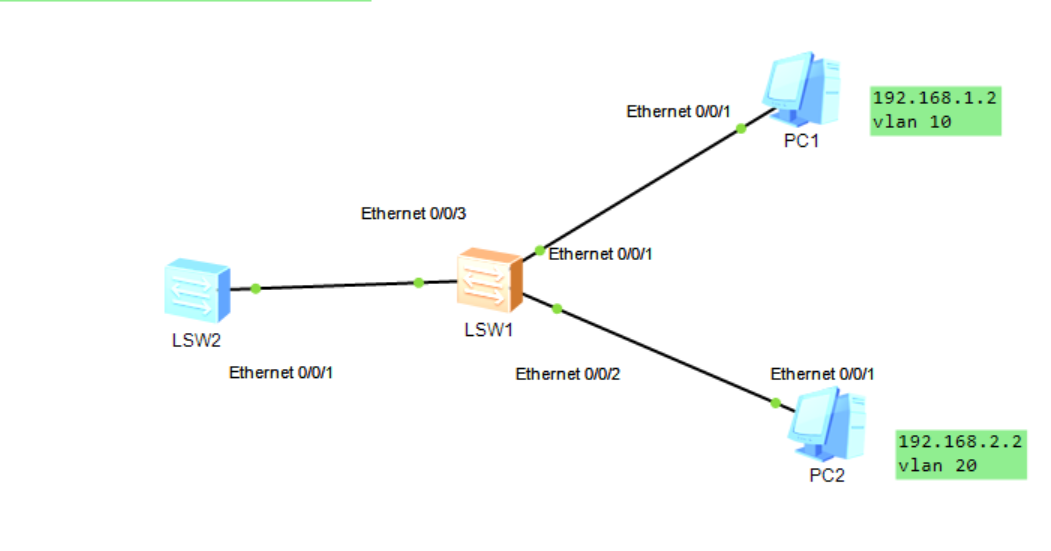
命令如下:
u t m
s y s //进入系统模式
s y s LSW1 //命名路由器
vlan batch 10 20 //划分vlan,分别为vlan 10和vlan 20
int e0/0/1 //进入1号口
port link-type access //vlan接口为access口
port default vlan 10 //将端口加入vlan 10中
int e0/0/2 //按照同样方法配置好2号口
port link-type access
port default vlan 20
此时已经划分好vlan,PC1和PC2无法ping通。我们需要配置三层vlanif接口来实现互通。
int e0/0/3
port link-type trunk //vlan接口为trunk口
port trunk allow-pass vlan 10 20 //允许vlan 10和vlan 20通过
在LSW2中:
u t m
s y s
s y s LSW2
vlan batch 10 20
int Vlanif 10 //进入vlan 10接口
ip address 192.168.1.1 255.255.255.0 //设置当前vlan的ip地址,前面是网关,后面是子网掩码
int Vlanif 20
ip address 192.168.2.1 255.255.255.0
(最后记得配置PC1和PC2的网关)
2.单臂路由:使用逻辑接口

还是按照同上的方法配置好vlan 10和vlan 20
之后开始配置单臂路由
u t m
sys
sys AR4
int g0/0/0.20 //配置单臂路由,逻辑接口最好与vlan一致
dot1q termination vid 20 //该接口在收到vlan tag(vlan 20)的报文时,将剥离tag进行三层转发;在发送报文时,会添加该接口对应的vlan tag(vlan 20)
ip address 192.168.2.1 255.255.255.0 //添加网关和子网掩码
arp broadcast enable
q
int g0/0/0.10
dot1q termination vid 10
ip address 192.168.1.1 255.255.255.0
arp broadcast enable //开启ARP广播
(我在CSDN上看到其他大佬写的比我好不知道怎么引用过来hhh,可以去收藏夹翻一翻有一个叫[华为路由器:单臂路由实验],写的很详细)
例1:拓扑结构如下所示,分别用三层vlanif接口和单臂路由实现不同vlan之间的通信

(二)、RSTP配置实现
在复杂的二次网络中,为了防止环路生成,可以在交换机上部署生成树协议(STP)。
为了解决STP收敛速度慢的问题,提出RSTP(rapid)。
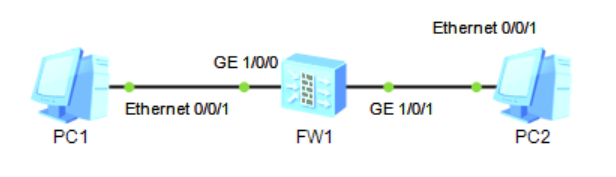
建立如下拓扑结构

不需要划分vlan,只要保证PC1和PC2能通就行。
对于LSW1:
stp enable //开始生成树的计算
stp mode rstp //配置设备工作模式
stp root primary //配置当前交换设备为指定生成树的根桥
查看生成树信息:
display stp brief
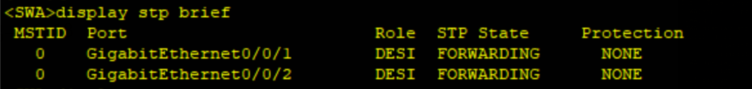
display stp

对于LSW2:
stp enable
stp mode rstp
stp bpdu-protection //开启BPDU保护功能,通过undo stp bpdu-protection取消
int g0/0/4
stp edged-port enable //配置的接口不参与生成树的计算,可以转发BPDU也可以接受BPDU
对于LSW3:
stp enable
stp mode rstp
stp bpdu-protection
int g0/0/4
stp edged-port enable
查看生成树信息:
display stp brief
(三)、MSTP配置实现
由于RSTP只能生成一棵树,有许多弊端,提出MSTP。
(四)、RIP
(五)、OSFP
1.多区域OSPF
建立如下拓扑结构图

先配置各路由器的ip地址
以AR1为例(路由器的标号是多少,就把对应ip地址设为多少,方便记忆)
int g0/0/0
ip address 10.1.12.1 24
int g0/0/1
ip address 10.1.13.1 24
其余的同理
注意lookback接口的配置
以AR5为例
int g0/0/2
ip address 10.1.35.5 24
int loo0
ip address 192.168.2.5 24
再配置OSPF协议
以AR1为例,剩下同理
ospf 1 router-id 1.1.1.1//router-id 几号交换机就命名为几
area 0//写明域
network 10.1.12.0 0.0.0.255//network连接的网段以及子网掩码的反码
network 10.1.13.0 0.0.0.255
注意AR2和AR3是区域边界路由器(ABR),需要进两个域分别network。
2.OSPF和RIP协议重发布

前面的配置和1相同。主要思路就是,分别配置好ospf和rip,在AR4分别进入ospf配置rip,以及在rip上配置ospf(因为AR4两个协议都有)
具体命令如下
ospf1
import-route rip
rip
import-route ospf
(六)网络安全隔离技术
1.ACL

AR1:
int g0/0/0
ip add 192.168.1.254 24
[AR1-GigabitEthernet0/0/0]int g0/0/1
[AR1-GigabitEthernet0/0/1]ip add 192.168.2.254 24 //注意这里的地址是网关地址
[AR1-GigabitEthernet0/0/1]int g0/0/2
[AR1-GigabitEthernet0/0/2]ip add 192.168.3.254 24
[AR1-GigabitEthernet0/0/2]int g6/0/0
[AR1-GigabitEthernet6/0/0]ip add 192.168.12.6 24 //两个路由器是直连的,只需给端口设置IP地址就行
//rip和OSPF都可以
[AR1]rip
[AR1-rip-1]version 2
[AR1-rip-1]network 192.168.1.0
[AR1-rip-1]network 192.168.2.0
[AR1-rip-1]network 192.168.3.0
[AR1-rip-1]network 192.168.12.0
AR2
[AR2]int g0/0/0
[AR2-GigabitEthernet0/0/0]ip add 192.168.12.2 24
[AR2-GigabitEthernet0/0/0]int g0/0/1
[AR2-GigabitEthernet0/0/1]ip add 192.168.4.254 24
[AR2-GigabitEthernet0/0/1]int g0/0/2
[AR2-GigabitEthernet0/0/2]ip add 192.168.23.2 24
[AR2]rip
[AR2-rip-1]version 2
[AR2-rip-1]network 192.168.12.0
[AR2-rip-1]network 192.168.5.0
[AR2-rip-1]network 192.168.23.0
AR3
[AR3]int g0/0/0
[AR3-GigabitEthernet0/0/0]ip add 192.168.23.3 24
[AR3-GigabitEthernet0/0/0]int g0/0/1
[AR3-GigabitEthernet0/0/1]ip add 192.168.5.254 24
[AR3-GigabitEthernet0/0/1]int g0/0/2
[AR3-GigabitEthernet0/0/2]ip add 192.168.6.254 24
配通以后,可以书写相应的ACL命令
2.NAT
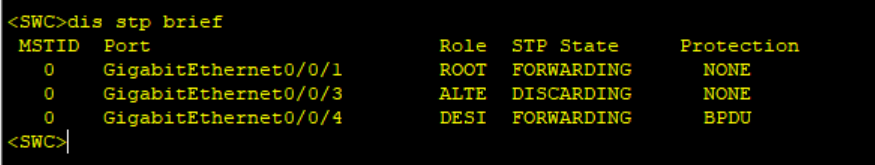
建立如图所示的拓扑结构

ISP
[ISP]int g0/0/0
[ISP-GigabitEthernet0/0/0]ip add 200.10.10.2 24 //还是配端口的ip地址
[ISP-GigabitEthernet0/0/0]int g0/0/1
[ISP-GigabitEthernet0/0/1]ip add 11.11.11.254 24 //同上
AR1
[AR1-GigabitEthernet0/0/0]ip add 200.10.10.3 24
[AR1-GigabitEthernet0/0/0]int g0/0/1
[AR1-GigabitEthernet0/0/1]ip add 192.168.1.254 24
[AR1-GigabitEthernet0/0/1]int g0/0/0
[AR1-GigabitEthernet0/0/0]nat server protocol tcp global 200.10.10.1 www inside
192.168.1.1 80 //在需要转接的端口配置nat
[AR1-GigabitEthernet0/0/0]q
[AR1]ip route-static 0.0.0.0 0.0.0.0 200.10.10.2
在AR1的1端口抓包,得到如下结果

可以看出,经过AR1的1号端口,数据包的源地址为192.168.1.1
在AR1的0端口抓包,得到如下结果

可以看出,在通信过程中,由AR1出去的数据包,地址已经变成200.10.10.1
3.防火墙
[FW]int g1/0/0
[FW-GigabitEthernet1/0/0]ip add 10.1.1.254 24
[FW-GigabitEthernet1/0/0]int g1/0/1
[FW-GigabitEthernet1/0/1]ip add 1.1.1.254 24
[FW]firewall zone trust
[FW-zone-trust]add int g1/0/0
[FW-zone-trust]firewall zone untrust
[FW-zone-untrust]add int g1/0/1
[FW-zone-untrust]q
[FW]security-policy
[FW-policy-security]rule name t_u
[FW-policy-security-rule-t_u]source-zone trust
[FW-policy-security-rule-t_u]destination-zone untrust
[FW-policy-security-rule-t_u]source-address 10.1.1.0 24
[FW-policy-security-rule-t_u]action permit
此时PC1 ping PC2能通,但是倒过来不能,还需要反着搞一下
4.在防火墙上配置源NAT

Huawei]sys AR!
[AR!]int g0/0/0
[AR!-GigabitEthernet0/0/0]ip add 1.1.1.254 24
[AR!-GigabitEthernet0/0/0]int g0/0/1
[AR!-GigabitEthernet0/0/1]ip add 11.11.11.1 24
[AR!-GigabitEthernet0/0/1]undo ip add 11.11.11.1 24
[AR!-GigabitEthernet0/0/1]ip add 11.11.11.254 24
[AR!-GigabitEthernet0/0/1]q
[AR!]ip route-static 1.1.1.10 255.255.255.255 1.1.1.1
[AR!]ip route-static 1.1.1.11 255.255.255.255 1.1.1.1
[USG6000V1]sys Fw1
[Fw1]int g1/0/1
[Fw1-GigabitEthernet1/0/1]ip add 10.1.1.254 24
[Fw1-GigabitEthernet1/0/1]int g1/0/2
[Fw1-GigabitEthernet1/0/2]ip add 1.1.1.1 24
[Fw1-GigabitEthernet1/0/2]q
[Fw1]firewall zone trust
[Fw1-zone-trust]add int g1/0/1
[Fw1-zone-trust]firewall zone untrust
[Fw1-zone-untrust]add int g1/0/2
[Fw1-zone-untrust]q
[Fw1]security-policy
[Fw1-policy-security]rule name t_u
[Fw1-policy-security-rule-t_u]source-zone trust
[Fw1-policy-security-rule-t_u]destination-zone untrust
[Fw1-policy-security-rule-t_u]source-address 10.1.1.0 24
[Fw1-policy-security-rule-t_u]action permit
[Fw1-policy-security-rule-t_u]q
[Fw1-policy-security]q
[Fw1]nat address-group addressgroup1
[Fw1-address-group-addressgroup1]section 0 1.1.1.10 1.1.1.11
[Fw1-address-group-addressgroup1]nat-policy
[Fw1-policy-nat]rule name policy_nat_1
[Fw1-policy-nat-rule-policy_nat_1]source trust
[Fw1-policy-nat-rule-policy_nat_1]undo source trust
[Fw1-policy-nat-rule-policy_nat_1]source-zone trust
[Fw1-policy-nat-rule-policy_nat_1]destination-zone untrust
[Fw1-policy-nat-rule-policy_nat_1]source-address 10.1.1.0 24
[Fw1-policy-nat-rule-policy_nat_1]action source-nat address-group addressgroup1
[Fw1-policy-nat-rule-policy_nat_1]q
[Fw1-policy-nat]ip route-static 0.0.0.0 0.0.0.0 1.1.1.254
[Fw1]ip route-static 1.1.1.10 255.255.255.255 NULL0
[Fw1]ip route-static 1.1.1.11 255.255.255.255 NULL0
GRE

[FW1]int g1/0/1
[FW1-GigabitEthernet1/0/1]ip add 1.1.1.1 24
[FW1-GigabitEthernet1/0/1]int g1/0/0
[FW1-GigabitEthernet1/0/0]ip add 192.168.1.254 24
[FW1-GigabitEthernet1/0/0]q
[FW1]firewall zone trust
[FW1-zone-trust]add int g1/0/0
[FW1-zone-trust]firewall zone untrust
[FW1-zone-untrust]add int g1/0/1
[FW1-zone-untrust]q
[FW1]nat-policy
[FW1-policy-nat]rule name nat
[FW1-policy-nat-rule-nat]source-zone trust
[FW1-policy-nat-rule-nat]destination-zone untrust
[FW1-policy-nat-rule-nat]source-address 192.168.1.0 24
[FW1-policy-nat-rule-nat]action source-nat easy-ip
[FW1-policy-nat-rule-nat]q
[FW1-policy-nat]q
[FW1]ip route-static 0.0.0.0 0 1.1.1.2
[FW1]int Tunnel 1
[FW1-Tunnel1]tunnel-protocol gre
[FW1-Tunnel1]ip add 192.168.12.1 24
[FW1-Tunnel1]source 1.1.1.1
[FW1-Tunnel1]destination 5.5.5.5
[FW1-Tunnel1]q
[FW1]firewall zone untrust
[FW1-zone-untrust]add int tunnel1
[FW1-zone-untrust]dis th
[FW1]ip route-static 192.168.2.0 24 tunnel1
[FW1]security-policy
[FW1-policy-security]rule name t_u
[FW1-policy-security-rule-t_u]source-zone trust
[FW1-policy-security-rule-t_u]destination-zone untrust
[FW1-policy-security-rule-t_u]source-address 192.168.1.0 24
[FW1-policy-security-rule-t_u]action permit
[FW1-policy-security-rule-t_u]q
[FW1-policy-security]rule name u_t
[FW1-policy-security-rule-u_t]source-zone untrust
[FW1-policy-security-rule-u_t]destination-zone trust
[FW1-policy-security-rule-u_t]source-address 192.168.12.0 24
[FW1-policy-security-rule-u_t]action permit
[FW1-policy-security-rule-u_t]q
[FW1-policy-security]rule name gre
[FW1-policy-security-rule-gre]source-zone untrust
[FW1-policy-security-rule-gre]destination-zone local
[FW1-policy-security-rule-gre]service protocol 47
[FW1-policy-security-rule-gre]action permit
[AR1]int g0/0/0
[AR1-GigabitEthernet0/0/0]ip add 1.1.1.2 24
[AR1-GigabitEthernet0/0/0]int g0/0/1
[AR1-GigabitEthernet0/0/1]ip add 5.5.5.2 24
[AR1-GigabitEthernet0/0/1]int loo0
[AR1-LoopBack0]ip add 8.8.8.8 32
[FW2]int g1/0/1
[FW2-GigabitEthernet1/0/1]ip add 5.5.5.5 24
[FW2-GigabitEthernet1/0/1]int g1/0/0
[FW2-GigabitEthernet1/0/0]ip add 192.168.2.254 24
[FW2-GigabitEthernet1/0/0]q
[FW2]firewall zone trust
[FW2-zone-trust]add int g1/0/0
[FW2-zone-trust]firewall zone untrust
[FW2-zone-untrust]add int g1/0/1
[FW2-zone-untrust]q
[FW2]nat-policy
[FW2-policy-nat]rule name nat
[FW2-policy-nat-rule-nat]source-zone trust
[FW2-policy-nat-rule-nat]destination-zone untrust
[FW2-policy-nat-rule-nat]source-address 192.168.2.0 24
[FW2-policy-nat-rule-nat]action source-nat easy-ip
[FW2-policy-nat-rule-nat]q
[FW2-policy-nat]q
[FW2]ip route-static 0.0.0.0 0 5.5.5.2
[FW2]int tunnel1
[FW2-Tunnel1]tunnel-protocol gre
Warning: After this tunnel encapsulation protocol was configured, the MTU and ot
her parameter settings of the tunnel were deleted.
[FW2-Tunnel1]ip add 192.168.12.2 24
[FW2-Tunnel1]source 5.5.5.5
[FW2-Tunnel1]destination 1.1.1.1
[FW2-Tunnel1]q
[FW2]ip route-static 192.168.1.0 24 tunnel1
[FW2]security-policy
[FW2-policy-security]rule name t_u
[FW2-policy-security-rule-t_u]source-zone trust
[FW2-policy-security-rule-t_u]destination-zone untrust
[FW2-policy-security-rule-t_u]source-address 192.168.2.0 24
[FW2-policy-security-rule-t_u]action permit
[FW2-policy-security-rule-t_u]q
[FW2-policy-security]rule name u_t
[FW2-policy-security-rule-u_t]source-zone untrust
[FW2-policy-security-rule-u_t]destination-zone trust
[FW2-policy-security-rule-u_t]source-address 192.168.12.0 24
[FW2-policy-security-rule-u_t]action permit
[FW2-policy-security-rule-u_t]q
[FW2-policy-security]rule name gre
[FW2-policy-security-rule-gre]source-zone untrust
[FW2-policy-security-rule-gre]destination-zone local
[FW2-policy-security-rule-gre]service protocol 47
[FW2-policy-security-rule-gre]action permit
[FW2-policy-security-rule-gre]q
[FW2]ip route-static 192.168.1.0 24 tunnel1
[FW2]firewall zone untrust
[FW2-zone-untrust]add int tunnel1
[FW2-zone-untrust]q
























 6920
6920











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








