1.配置桥接并验证
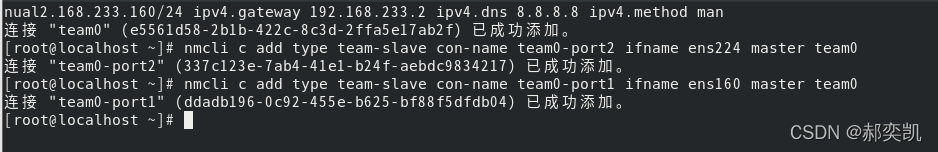
nmcli c add type team con-name team0 ifname team0 config '{"runner": {"name": "activebackup","hwaddr_policy": "by_active"}}' ipv4.addresses 192.168.233.160/24 ipv4.gateway 192.168.233.2 ipv4.dns 8.8.8.8 ipv4.method manual
nmcli c add type team-slave con-name team0-port2 ifname ens224 master team0
nmcli c add type team-slave con-name team0-port1 ifname ens160 master team0
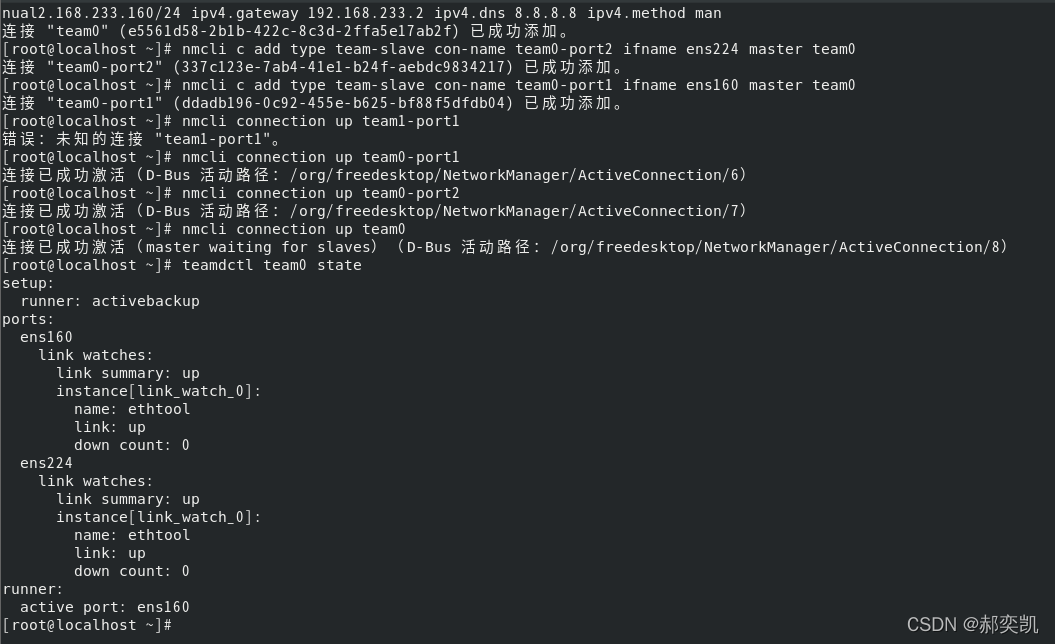
2.配置team多网卡绑定验证
nmcli connection add ifname team0 con-name team0 type team config '{"runner":"{"name":"active“}}'
nmcli connection add con-name team0-port1 type team-slave ifname ens38 master team
nmcli connection down team0-port1
nmcli connection down team-port2
nmcli connection up team0-port1
nmcli connection up team0-port2
nmcli connection modify team0 ipv4.addresses 192.168.234.155
nmcli connection modify team0 ipv4.method manual
nmcli connection down team0
nmcli connection up team0
3.配置ssh免密登录(基于公钥的认证)
[root@host ~]$ ssh-keygen <== 建立密钥对
Generating public/private rsa key pair.
Enter file in which to save the key (/root/.ssh/id_rsa): <== 按 Enter
Created directory '/root/.ssh'.
Enter passphrase (empty for no passphrase): <== 输入密钥锁码,或直接按 Enter 留空
Enter same passphrase again: <== 再输入一遍密钥锁码
Your identification has been saved in /root/.ssh/id_rsa. <== 私钥
Your public key has been saved in /root/.ssh/id_rsa.pub. <== 公钥
The key fingerprint is:
0f:d3:e7:1a:1c:bd:5c:03:f1:19:f1:22:df:9b:cc:08 root@host
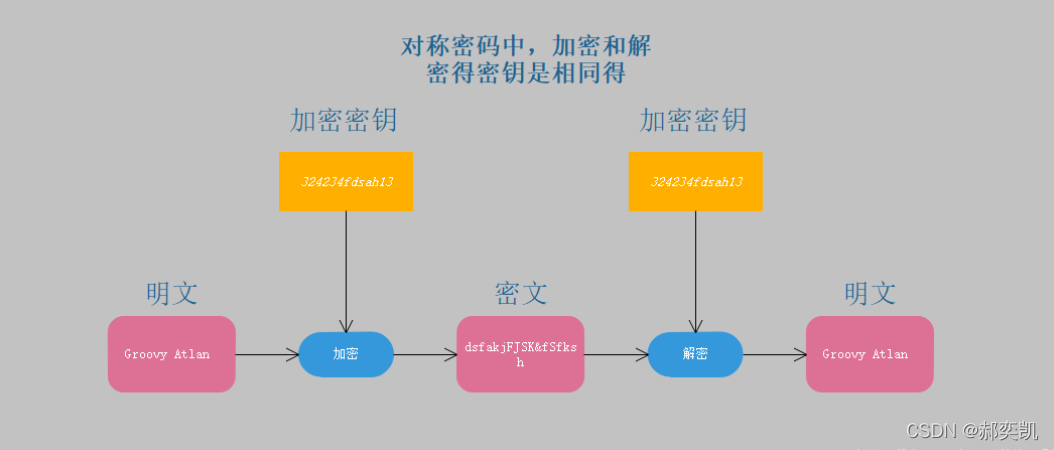
4.什么是对称加密,什么是非对称加密,以及对称加密和非对称加密存在的问题?
对称加密是一个秘钥,非对称加密是一对,两个秘钥 非对称加密比起对称加密更安全,因为不存在秘钥泄露问题,公钥即便被知道也没关系 由于使用非对称加密在计算上特别复杂,所以一般来说对称加密的加密解密的速度相对于非对称加密快很多 非对称秘钥还可以用于认证 由于以上第三条,所以在 https 中传输数据时不会使用非对称加密加密传输数据,传输数据时有可能数据本身很大,那样的话非对称加密更耗时了,所以传输数据时不会使用非对称加密的方式加密。






















 547
547











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








