题目
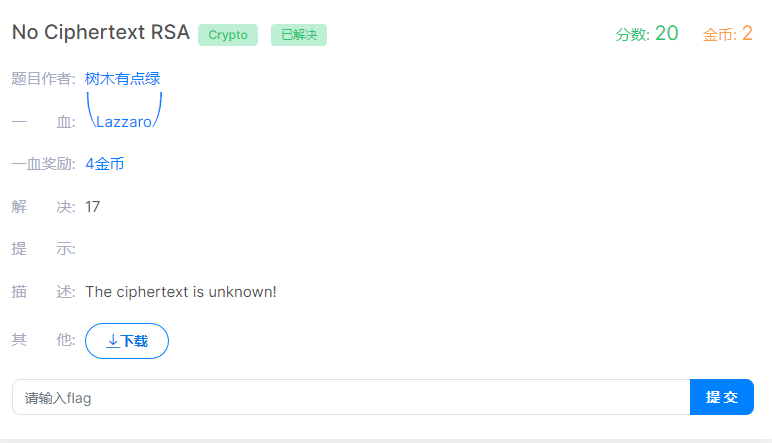
附件
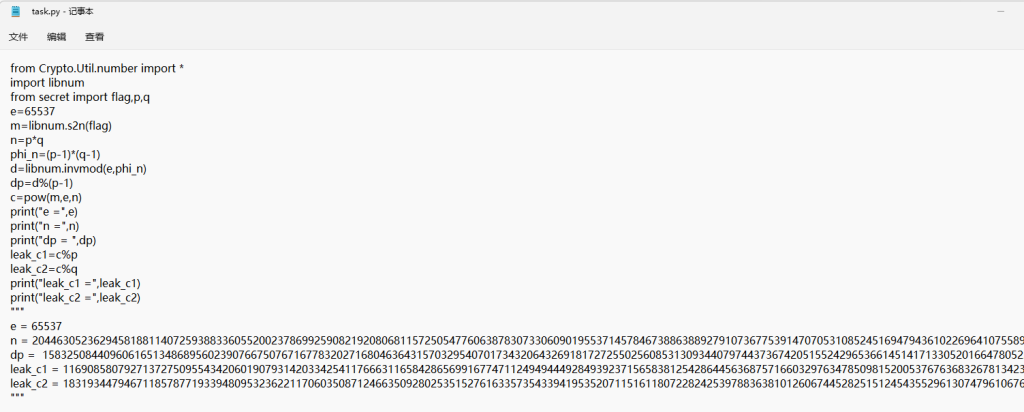
这里给了dp,可以根据dp爆破出p,q
n =
dp =
e = 65537
for x in range(1, e):
if(e*dp%x==1):
p=(e*dp-1)//x+1
if(n%p!=0):
continue
print('p=',p)
q = n//p
print('q=',q)现在来到了难点,c不知如何去求,这里给了leak_c1,leak_c2,应该就是用这个求了,最后实在没法了,看了一下作者的wp(传送门)
leak_c1=c%p
leak_c2=c%q这里我们用到了中国剩余定理(CRT),即p和q是互相独立的大素数,n为p*q,对于任意(m1, m2), (0<=m1< p, 0<=m2< p),这里把m1和m2替换成leak_c1和leak_c2,即可得到以下关系,我们发现这个关系完全符合以上定理
然后按照参考资料中的Using the CTR with RSA即可根据leak_c1和leak_c2求解出c了
import gmpy2
p =
q =
c_mod_p =
c_mod_q =
e = 65537
phi=(p-1)*(q-1)
d=gmpy2.invert(e,phi)
def CRT(aList, mList):
M = 1
for i in mList:
M = M * i
x = 0
for i in range(len(mList)):
Mi = M // mList[i]
Mi_inverse = gmpy2.invert(Mi, mList[i])
x += aList[i] * Mi * Mi_inverse
x = x % M
return x
if __name__ == "__main__":
cList = [c_mod_p,c_mod_q]
nList = [p,q]
c = CRT(cList, nList)
print(c)求出c后,p,q,e,c已知,直接跑代码
from Crypto.Util.number import *
import gmpy2 as gp
import binascii
p =
q =
e = 65537
c =
n = p*q
phi = (p-1)*(q-1)
d = gp.invert(e,phi)
m = pow(c,d,n)
##print(m)
print(bytes.fromhex(hex(m)[2:]))结果如下:
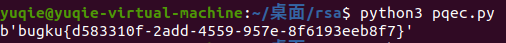
成功拿到flag!!























 2366
2366











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










