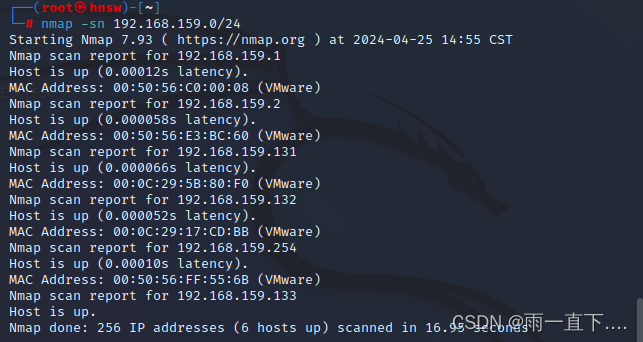
使用ARP协议进行主机发现
ARP活跃主机发现技术的原理:如果我们想要知道处在同一网段的IP
地址为0.0.0.0的主机是否为活跃主机,只需要构造一个ARP请求数据包,并广播出去,如果得到了回应,则说明该主机为活跃主机。
但是注意这种扫描方式仅能用于与Nmap所在主机在同一子网的目标,例如执行:
wireshark:

对单个主机的扫描:

指定端口扫描
除了所有前面讨论的扫描方法, Nmap提供选项说明那些端口被扫描以及扫描是随机还是顺序进行。 默认情况下,Nmap用指定的协议对端口1到1024以及nmap-services 文件中列出的更高的端口在扫描。
-p (只扫描指定的端口)
该选项指明您想扫描的端口,覆盖默认值。 单个端口和用连字符表示的端口范围(如 1-1023)都可以。 范围的开始以及/或者结束值可以被省略, 分别导致Nmap使用1和65535。所以您可以指定 -p-从端口1扫描到65535。 如果您特别指定,也可以扫描端口0。 对于IP协议扫描(-sO),该选项指定您希望扫描的协议号 (0-255)。
-sT (TCP connect()扫描)
扫描开放端口(这里的-p 是 21 号端口)

一次完整的握手 (红色为已经连接)
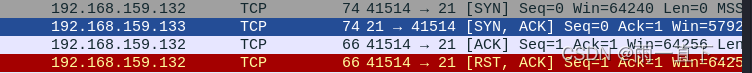
扫描关闭端口(这里的-p是20号端口)

![]()
-sS (TCP SYN扫描)
扫描开放端口(这里的-p 是 21 号端口)


扫描关闭端口(这里的-p是20号端口)

![]()
-sF (FIN扫描)
开放端口类型

![]()
关闭端口类型
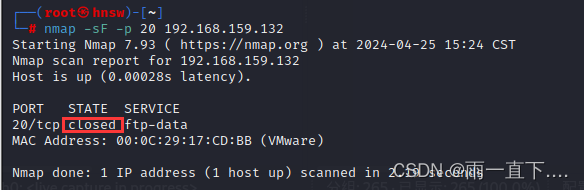
![]()
使用Nmap进行扫描目标操作系统
-O (启用操作系统检测)

也可以使用-A来同时启用操作系统检测和版本检测(这里的-A 扫描要4-5分钟)
这里是-A的全部信息
──(root㉿hnsw)-[~]
└─# nmap -A 192.168.159.132
Starting Nmap 7.93 ( https://nmap.org ) at 2024-04-25 15:31 CST
Stats: 0:01:11 elapsed; 0 hosts completed (1 up), 1 undergoing Service Scan
Service scan Timing: About 95.65% done; ETC: 15:32 (0:00:03 remaining)
Stats: 0:01:16 elapsed; 0 hosts completed (1 up), 1 undergoing Service Scan
Service scan Timing: About 95.65% done; ETC: 15:33 (0:00:03 remaining)
Nmap scan report for 192.168.159.132
Host is up (0.0013s latency).
Not shown: 977 closed tcp ports (reset)
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 2.3.4
| ftp-syst:
| STAT:
| FTP server status:
| Connected to 192.168.159.133
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| vsFTPd 2.3.4 - secure, fast, stable
|_End of status
|_ftp-anon: Anonymous FTP login allowed (FTP code 230)
22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1 (protocol 2.0)
| ssh-hostkey:
| 1024 600fcfe1c05f6a74d69024fac4d56ccd (DSA)
|_ 2048 5656240f211ddea72bae61b1243de8f3 (RSA)
23/tcp open telnet Linux telnetd
25/tcp open smtp Postfix smtpd
|_smtp-commands: metasploitable.localdomain, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN
|_ssl-date: 2024-04-25T07:34:35+00:00; +8s from scanner time.
53/tcp open domain ISC BIND 9.4.2
| dns-nsid:
|_ bind.version: 9.4.2
80/tcp open http Apache httpd 2.2.8 ((Ubuntu) DAV/2)
|_http-server-header: Apache/2.2.8 (Ubuntu) DAV/2
|_http-title: Metasploitable2 - Linux
111/tcp open rpcbind 2 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2 111/tcp rpcbind
| 100000 2 111/udp rpcbind
| 100003 2,3,4 2049/tcp nfs
| 100003 2,3,4 2049/udp nfs
| 100005 1,2,3 33716/udp mountd
| 100005 1,2,3 42031/tcp mountd
| 100021 1,3,4 34347/udp nlockmgr
| 100021 1,3,4 35589/tcp nlockmgr
| 100024 1 42550/tcp status
|_ 100024 1 49881/udp status
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 3.0.20-Debian (workgroup: WORKGROUP)
512/tcp open exec netkit-rsh rexecd
513/tcp open login?
514/tcp open shell?
1099/tcp open java-rmi GNU Classpath grmiregistry
1524/tcp open bindshell Metasploitable root shell
2049/tcp open nfs 2-4 (RPC #100003)
2121/tcp open ftp ProFTPD 1.3.1
3306/tcp open mysql MySQL 5.0.51a-3ubuntu5
| mysql-info:
| Protocol: 10
| Version: 5.0.51a-3ubuntu5
| Thread ID: 9
| Capabilities flags: 43564
| Some Capabilities: ConnectWithDatabase, SupportsTransactions, LongColumnFlag, Support41Auth, Speaks41ProtocolNew, SwitchToSSLAfterHandshake, SupportsCompression
| Status: Autocommit
|_ Salt: 3MlUHEdEmt~=QbxW*hO2
5432/tcp open postgresql PostgreSQL DB 8.3.0 - 8.3.7
| ssl-cert: Subject: commonName=ubuntu804-base.localdomain/organizationName=OCOSA/stateOrProvinceName=There is no such thing outside US/countryName=XX
| Not valid before: 2010-03-17T14:07:45
|_Not valid after: 2010-04-16T14:07:45
|_ssl-date: 2024-04-25T07:34:31+00:00; +8s from scanner time.
5900/tcp open vnc VNC (protocol 3.3)
| vnc-info:
| Protocol version: 3.3
| Security types:
|_ VNC Authentication (2)
6000/tcp open X11 (access denied)
6667/tcp open irc UnrealIRCd
| irc-info:
| users: 1
| servers: 1
| lusers: 1
| lservers: 0
| server: irc.Metasploitable.LAN
| version: Unreal3.2.8.1. irc.Metasploitable.LAN
| uptime: 0 days, 1:10:45
| source ident: nmap
| source host: C3536BBF.FE159842.FFFA6D49.IP
|_ error: Closing Link: zfrmeanay[192.168.159.133] (Quit: zfrmeanay)
8009/tcp open ajp13 Apache Jserv (Protocol v1.3)
|_ajp-methods: Failed to get a valid response for the OPTION request
8180/tcp open http Apache Tomcat/Coyote JSP engine 1.1
|_http-title: Apache Tomcat/5.5
|_http-favicon: Apache Tomcat
MAC Address: 00:0C:29:17:CD:BB (VMware)
Device type: general purpose
Running: Linux 2.6.X
OS CPE: cpe:/o:linux:linux_kernel:2.6
OS details: Linux 2.6.9 - 2.6.33
Network Distance: 1 hop
Service Info: Hosts: metasploitable.localdomain, irc.Metasploitable.LAN; OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_clock-skew: mean: 1h00m08s, deviation: 2h00m00s, median: 7s
| smb-security-mode:
| account_used: <blank>
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
|_nbstat: NetBIOS name: METASPLOITABLE, NetBIOS user: <unknown>, NetBIOS MAC: 000000000000 (Xerox)
| smb-os-discovery:
| OS: Unix (Samba 3.0.20-Debian)
| Computer name: metasploitable
| NetBIOS computer name:
| Domain name: localdomain
| FQDN: metasploitable.localdomain
|_ System time: 2024-04-25T03:33:59-04:00
|_smb2-time: Protocol negotiation failed (SMB2)
TRACEROUTE
HOP RTT ADDRESS
1 1.33 ms 192.168.159.132
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 190.95 seconds
如果想节约扫描时间,也可以用-sV参数粗略扫描























 8184
8184











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








