一、文章来由
老师在期末的时候给出自愿 presentation 的任务,想接触一下这块,所以果断报名了。
Textbook 下载:
https://www.homeworkmarket.com/sites/default/files/corporate_computer_security_0.pdf
第5.6章
二、Textbook notes
1. Public Key Infrastructures
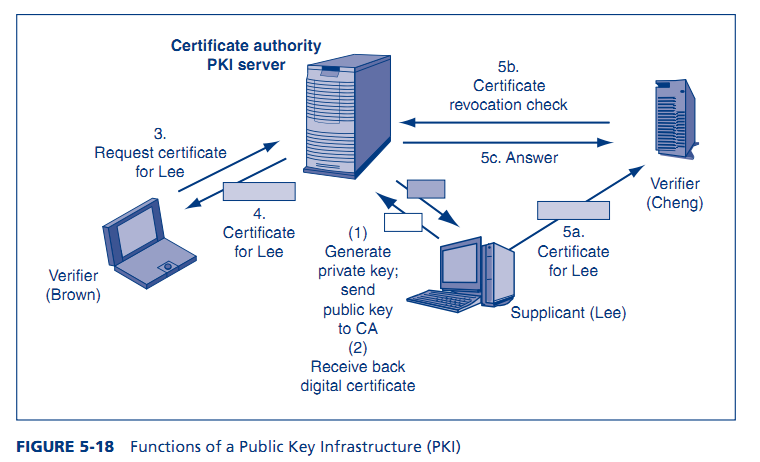
Using public key authentication with digital certificates requires the organization to establish a public key infrastructure (PKI) to create and manage public key–private key pairs and digital certificates. Figure 5-18 illustrates the functions of a PKI.
THE FIRM AS A CERTIFICATE AUTHORITY
As Chapter 3 noted, certificate authorities (CAs) manage digital certificates. The chapter also noted that CAs are not regulated, and this creates questions of trust. However, if firms act as their own CAs, they have control of trust in their entire public key infrastructure. On the negative side, being a certificate authority is quite expensive because of the labor involved.
2. CREATING PUBLIC KEY–PRIVATE KEY PAIRS
First, a PKI needs a way to generate public key–private key pairs for non-PKI servers and clients. This is typically done by the client or non-PKI server rather than by the PKI server. The client or server generates a private key–public key pair, and then sends the
public key to the CA. This transmission can be done in the clear because public keys are not secret. The private key, which is secret, is not transmitted at all.
3. ACCEPTING DIGITAL CERTIFICATES
The figure also shows that a supplicant can send the true party’s digital certificate to the verifier. This might seem suspicious, but recall that digital certificates have their own digital signatures signed (encrypted) by the private key of the PKI server. Digital signa-tures give message integrity as well as authentication. Consequently, an impostor cannot change the true party’s name and replace it with his or her own name.
It is safe to accept a digital certificate from a supplicant, even if the supplicant is an impostor. The digital certificate has its own digital signature, which gives integrity. This means that the sender cannot change it.






















 1215
1215

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








